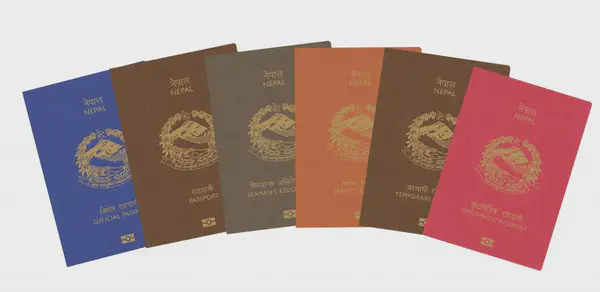
Overcoming Nepal's Passport Form Challenges with Cypress
When Nepal introduced the new E-Passport system, it promised a less stressful application process for everyone. The expectation was that individuals …
When Nepal introduced the new E-Passport system, it promised a less stressful application process for everyone. The expectation was that individuals …
Medusa is a lengthy machine from the platform HackMyVM despite being easy. The machine’s author is noname and I must pay respect to him for …

Kitty is a hard machine to root by avijneyam from the platform HackMyVM. The machine’s theme is cats as suggested by the name of the VM. To …

Arroutada is a medium-difficulty machine by RiJaba1 from the HackMyVM platform. Although the author has marked this machine as easy, I don’t …
Ephemeral is a difficult machine involving various tricks and techniques to get to the root shell. However, it took some time for me as one of the …

Moosage is an easy machine by sml from the platform HackMyVM. The machine features an insecure file upload vulnerability in a blog application. Then, …

Eighty is a difficult machine from sML on the platform HackMyVM. This machine uses various techniques like knocking the ports out, analyzing the …
HackMyVM has added a new medium-difficulty machine “Catland” by cromiphi. This machine features subdomain enumeration, local file …
Light is an easy machine from the platform HackMyVM by sML. This machine requires knowledge of basic Linux and penetration testing. It could be really …
By far, Troya is one of my favourite VMs from the HackMyVM platform. The creator of the machines is sML and he has categorized this as a medium …