In the previous post, we tried to identify the possible vulnerabilities of the target machine. In this post, we will be trying to exploit the system. Up to now, we have visited the IP address of the target machine in firefox which gave us two input fields.
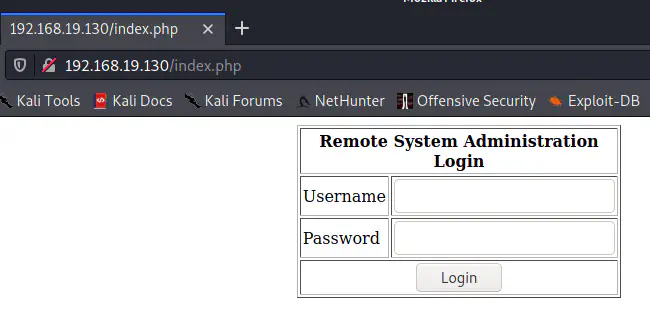
Now, if we try some random username and password, we cannot enter the system. However, there is an infamous vulnerability that a developer can introduce when he is not careful called SQL injection. In SQL injection, we can use input values that will modify the behaviour of the SQL commands on the website. Now, let’s write a SQL syntax.
SELECT * FROM users WHERE username = '$username' AND password='$password'
In the above query, a user has to supply a correct username and password to make it work. However, if we supply an input that can change the syntax to something else, that might get us access. In the place of username if you supply ' OR 1=1 #, then the syntax will be as follows.
SELECT * FROM users WHERE username = '' OR 1=1 #' AND password=''
Now, we can see that we joined an OR statement which will result in a true condition. Likewise, by the use of the comment, we removed the condition of the password. Also, this is a total valid SQL statement that will return all the records from the table users. Moreover, there are many ways to do this. You can use a – comment however if we did that we had to use the same value in the password field. If you want to learn the difference between these two types of comment, then visit this link.
In a similar way, there are many SQL injection input values. You can visit the following link to know about them.
https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/SQL%20Injection
Using SQL Injection in the target
Like we said earlier, we can try bypassing the authentication mechanism. Let’s use the input value ' OR 1=1 # and see what happens.
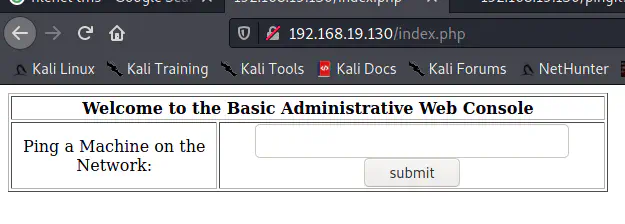
As in the screenshot above, we can now say that we have got an access to the system. Let’s try to use the website further by pinging the attacker IP address.
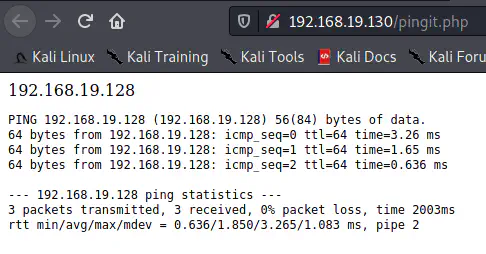
Yes, it works perfectly, and the output that we are seeing here looks like it is coming from the ping command of the target machine. Up to now, we gained he access to the website of the target machine. In the next post, we will be checking if we can exploit the ping feature of the website.